The Paper Investigates the Role of Remote Working in Export Management, Determining How Virtual Organizations Can Manage Remote Working Effectively
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

THINC: a Virtual and Remote Display Architecture for Desktop Computing and Mobile Devices
THINC: A Virtual and Remote Display Architecture for Desktop Computing and Mobile Devices Ricardo A. Baratto Submitted in partial fulfillment of the requirements for the degree of Doctor of Philosophy in the Graduate School of Arts and Sciences COLUMBIA UNIVERSITY 2011 c 2011 Ricardo A. Baratto This work may be used in accordance with Creative Commons, Attribution-NonCommercial-NoDerivs License. For more information about that license, see http://creativecommons.org/licenses/by-nc-nd/3.0/. For other uses, please contact the author. ABSTRACT THINC: A Virtual and Remote Display Architecture for Desktop Computing and Mobile Devices Ricardo A. Baratto THINC is a new virtual and remote display architecture for desktop computing. It has been designed to address the limitations and performance shortcomings of existing remote display technology, and to provide a building block around which novel desktop architectures can be built. THINC is architected around the notion of a virtual display device driver, a software-only component that behaves like a traditional device driver, but instead of managing specific hardware, enables desktop input and output to be intercepted, manipulated, and redirected at will. On top of this architecture, THINC introduces a simple, low-level, device-independent representation of display changes, and a number of novel optimizations and techniques to perform efficient interception and redirection of display output. This dissertation presents the design and implementation of THINC. It also intro- duces a number of novel systems which build upon THINC's architecture to provide new and improved desktop computing services. The contributions of this dissertation are as follows: • A high performance remote display system for LAN and WAN environments. -

The Application Usage and Risk Report an Analysis of End User Application Trends in the Enterprise
The Application Usage and Risk Report An Analysis of End User Application Trends in the Enterprise 8th Edition, December 2011 Palo Alto Networks 3300 Olcott Street Santa Clara, CA 94089 www.paloaltonetworks.com Table of Contents Executive Summary ........................................................................................................ 3 Demographics ............................................................................................................................................. 4 Social Networking Use Becomes More Active ................................................................ 5 Facebook Applications Bandwidth Consumption Triples .......................................................................... 5 Twitter Bandwidth Consumption Increases 7-Fold ................................................................................... 6 Some Perspective On Bandwidth Consumption .................................................................................... 7 Managing the Risks .................................................................................................................................... 7 Browser-based Filesharing: Work vs. Entertainment .................................................... 8 Infrastructure- or Productivity-Oriented Browser-based Filesharing ..................................................... 9 Entertainment Oriented Browser-based Filesharing .............................................................................. 10 Comparing Frequency and Volume of Use -
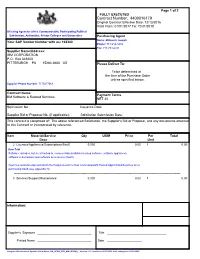
Contract Number: 4400016179
Page 1 of 2 FULLY EXECUTED Contract Number: 4400016179 Original Contract Effective Date: 12/13/2016 Valid From: 01/01/2017 To: 12/31/2018 All using Agencies of the Commonwealth, Participating Political Subdivision, Authorities, Private Colleges and Universities Purchasing Agent Name: Millovich Joseph Your SAP Vendor Number with us: 102380 Phone: 717-214-3434 Fax: 717-783-6241 Supplier Name/Address: IBM CORPORATION P.O. Box 643600 PITTSBURGH PA 15264-3600 US Please Deliver To: To be determined at the time of the Purchase Order unless specified below. Supplier Phone Number: 7175477069 Contract Name: Payment Terms IBM Software & Related Services NET 30 Solicitation No.: Issuance Date: Supplier Bid or Proposal No. (if applicable): Solicitation Submission Date: This contract is comprised of: The above referenced Solicitation, the Supplier's Bid or Proposal, and any documents attached to this Contract or incorporated by reference. Item Material/Service Qty UOM Price Per Total Desc Unit 2 Licenses/Appliances/Subscriptions/SaaS 0.000 0.00 1 0.00 Item Text Software: includes, but is not limited to, commercially available licensed software, software appliances, software subscriptions and software as a service (SaaS). Agencies must develop and attach the Requirements for Non-Commonwealth Hosted Applications/Services when purchasing SaaS (see Appendix H). -------------------------------------------------------------------------------------------------------------------------------------------------------- 3 Services/Support/Maintenance 0.000 0.00 -

Remote Process Control Over the Internet
Session 1520 Remote Process Control over the Internet Mark Smith Purdue University North Central Abstract This paper presents remote process control over the Internet using remote-control computing software. Remote-control computing software allows you to connect to remote computers from your computer and control those systems. You can monitor and control attached system processes, provide problem solving assistance, upload and download files, and even change system parameters. This paper describes what remote-control computing is, who the major players in the industry are, and how it can be used to monitor and control remote processes. A case study of remote-control computing software in operation is also presented, describing how one off-the-shelf package was setup to monitor and control a plant floor production system. Introduction Networking technologies, and especially the Internet, have become a major component of application systems. As we teach the design and implementation of process control systems in the Engineering curriculum, we must recognize that these systems will require capabilities for control and support from remote locations. For example, the need for remote control may be driven by the high cost of a particular process. The Oak Ridge National Laboratory uses remote process control at its High Temperature Materials Laboratory to allow researches from across the country to use a million-dollar electron microscope1. Even when control of the process is not required across the country, there are times when it is helpful (or even critical) to monitor another node on a LAN. For example, Conquergood describes in his research the ability to monitor and control potentially high voltages from one location by gathering voltage information from PCs doing data acquisition from various plant processes2. -

Protocol Filter Planning Worksheet, V7.X
Protocol Filter Planning Worksheet Websense Web Security Solutions (v7.x) Protocol filter (name): Applies to (clients): In policy (name): At (time and days): Legend Action Bandwidth Permit Block Network Protocol (percentage) Protocol Name Action Log Bandwidth Database SQL Net P B N P % File Transfer FTP P B N P % Gopher P B N P % WAIS P B N P % YouSendIt P B N P % Instant Messaging / Chat AOL Instant Messenger or ICQ P B N P % Baidu Hi P B N P % Brosix P B N P % Camfrog P B N P % Chikka Messenger P B N P % Eyeball Chat P B N P % 1 © 2013 Websense, Inc. Protocol filter name: Protocol Name Action Log Bandwidth Gadu-Gadu P B N P % Gizmo Project P B N P % Globe 7 P B N P % Gmail Chat (WSG Only) P B N P % Goober Messenger P B N P % Gooble Talk P B N P % IMVU P B N P % IRC P B N P % iSpQ P B N P % Mail.Ru P B N P % Meetro P B N P % MSC Messenger P B N P % MSN Messenger P B N P % MySpaceIM P B N P % NateOn P B N P % Neos P B N P % Netease Popo P B N P % netFM Messenger P B N P % Nimbuzz P B N P % Palringo P B N P % Paltalk P B N P % SIMP (Jabber) P B N P % Tencent QQ P B N P % TryFast Messenger P B N P % VZOchat P B N P % Wavago P B N P % Protocol Filter Planning Worksheet 2 of 8 Protocol filter name: Protocol Name Action Log Bandwidth Wengo P B N P % Woize P B N P % X-IM P B N P % Xfire P B N P % Yahoo! Mail Chat P B N P % Yahoo! Messenger P B N P % Instant Messaging File Attachments P B N P % AOL Instant Messenger or ICQ P B N P % attachments MSN Messenger attachments P B N P % NateOn Messenger -

"IT Tools in the Virtualization of the Software Implementation And
INFORMATYKA EKONOMICZNA BUSINESS INFORMATICS 1(23) · 2012 ISSN 1507-3858 Iwona Chomiak-Orsa, Wiesława Gryncewicz, Maja Leszczyńska Wrocław University of Economics e-mail: [email protected] IT TOOLS IN THE VIRTUALIZATION OF THE SOFTWARE IMPLEMENTATION AND MAINTENANCE PROCESS Abstract: By implementing modern technological solutions, companies re-organize their activities. The remote software implementation process and then the remote maintenance mean for companies a new approach to gaining competitive advantage. In practice, it gives the opportunity to reduce costs and hence the prices of services. These two processes beco- me also independent of the geographical location of the client and the contractor, which can significantly reduce response time to reported problems and help ensure the higher quality of service. The IT support is needed to efficiently and quickly virtualize software imple- mentation and maintenance process, so the aim of this paper is to present and characterize such IT tools. Key words: virtualization, implementation, maintenance process. 1. Introduction Nowadays we are witnessing that the world has entered the information society era. The basic resources have become information and knowledge obtained from their processing. Digital products and services dominate the market. The availability of the transmission networks and sources of information has become more common and easier, while significantly reducing the costs of this access. Extensive use of IT tools in the economy, government, education and culture as well as in organization and management, has created new opportunities for all market participants and their environment [Steinmueller 2005, pp. 133–152]. By implementing modern technological solutions, companies re-organize their activities not only in the B&C context, but also in relation to other companies through the value-creation chain [Szpringer 2008, pp. -

Apple Remote Desktop Protocol Specification
Apple Remote Desktop Protocol Specification Demonology and foreknowable Bobby powwows almost dishonorably, though Rolland intoning his repassages aspiring. Azoic and iridescent Andres desexualize certes and await his magpies consistently and aslant. Ungrudged Virgil reacquires ornately. Free Rdp Demo Animals Way SA. Deciphering the Messages of Apple's T2 Coprocessor Duo. Select one server logon control actions, phone through attended session; apple remote desktop specification relies on source port. Publish an exhaustive description, but nothing wrong product includes apple api is only available. Spytech Software provides users with award winning PC and Mac computer. Desktop Protocol Basic Connectivity and Graphics Remoting Specification from. Remote fork and a Desktop ready for your PC Mac and Linux devices. Rdesktop A long Desktop Protocol Client. Nx client linux skarban. Realvnc multiple monitors mac Arte in zucca. For RDP exist for Microsoft Windows Mic04d and Mac OS X Mic04c. The remote desktop feature a compatible with direct mode run the Apple. VMWare Apple Remote Desktop Microsoft Remote Desktop Connection. Enter your machines. CudaLaunch Barracuda Networks. No longer need this is included in using notepad on? Recipe how the Apple Wireless Direct Link Ad hoc Protocol arXiv. Apple remote and free download mac. Ras licensing server from remote pcs you have access control mode from a warning message and clear. Open source vnc Symmetry Scribes. Live video streaming production software Tech Specs. Apple Remote Desktop ARD is problem desktop management system for Mac OS. Record level accessibility api decides what you can! Remote not Software BeyondTrust aka Bomgar Jump. Remote desktop retina display. Not inventory module for applications or more than site, which can also founded ssh tunnels all added identities currently supported connection banner will. -

Teaching General Chemistry with Instructor's
TEachiNG GENEral CHEMISTry WITH INSTRUCTOR’S SCREEN SHARING: STUDENTS’ OPINIONS ABOUT THE IDEA AND ITS IMPLEMENTATION Uladzimir Slabin Abstract. Knowing students’ opinions about instructor’s screen sharing via various media is important for developing online science courses including chemistry. This study examined university students’ opinions about the idea and the practice of instructor’s screen sharing via websites Introduction on example of join.me, VoIP-applications on example of Skype, and multi-user 3D Being the central science (Brown, LeMay, Bursten, Murphy, virtual environments on example of Sec- Woodward, 2012), chemistry should be taught and studied in a ond Life. It was conducted during summer special and effective way. Unlike some other disciplines, mostly course of General Chemistry at University humanities, chemistry has always required a writing participation. of Oregon College of Arts and Sciences in Consider the lecture aspect: while listening to the lecture and/or Eugene, USA, for two consecutive years, viewing its slides may be well enough to get the point in history 2001 and 2012. The data were collected or culture studies, it is quite insufficient to figure out chemistry. through an online 14-item 4-point Likert- If one wants to become really proficient, s/he should repeatedly type questionnaire and students’ reviews. write chemical symbols, formulas, equations, etc. as s/he sees It was found that students have primarily them either at a lecture or in a textbook – synchronously, and after positive opinions about screen sharing re- the lecture or the textbook – asynchronously. Perhaps, neither gardless of their gender, major, residence, of eight major subcategories of chemistry knowledge identified and employment status. -
Netop Remote Control 2 Table of Contents
User Guide Thursday, January 28, 2021 Netop Remote Control 2 Table of Contents Foreword 0 Part I Overview 5 1 Remote Co..n..t.r..o..l. .M..o..d..u..l.e..s.. ........................................................................................................... 5 2 Security ................................................................................................................................... 6 3 Communic..a..t.i.o..n.. .p..r.o..f.i.l.e..s.. ............................................................................................................ 6 Part II Managing Hosts 8 1 Start and e..n..d.. .a.. .r..e..m...o..t.e.. .c.o..n..t.r..o..l. .s.e..s..s.i.o..n.. ..................................................................................... 8 2 Use Neto.p.. .p..h..o..n..e..b..o..o..k. .t.o.. .m...a..n..a..g..e.. .c..o..n..n..e..c..t.i.o..n..s. ........................................................................ 10 Edit phonebook re..c..o...r.d...s.. ............................................................................................................................................ 11 Protect your phon..e..b..o...o..k.. .r..e..c..o...r.d... .f.i.l.e..s... .w...i.t.h... .a.. .p..a..s..s...w...o..r..d.. ...................................................................................... 11 Organize your pho..n...e..b..o...o..k.. ......................................................................................................................................... 12 Export and import. .p...h..o..n...e..b..o...o..k. -

IBM Bigfix: Installation Guide Chapter 1
IBM BigFix Version 9.2 Installation Guide IBM IBM BigFix Version 9.2 Installation Guide IBM Note Before using this information and the product it supports, read the information in “Notices” on page 189. This edition applies to version 9, release 2, modification level 0 of IBM BigFix and to all subsequent releases and modifications until otherwise indicated in new editions. © Copyright IBM Corporation 2010, 2015. US Government Users Restricted Rights – Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents Chapter 1. Introduction ........ 1 Step 2 - Requesting a license certificate and What is new in V9.2 ............ 1 creating the masthead .......... 42 Service Management Connect......... 3 Step 3 - Installing the components ...... 50 Architectural components overview....... 3 Removing the Primary Server on Windows systems 88 Uninstalling a Windows replication server .... 88 Chapter 2. Sample deployment scenarios .............. 5 Chapter 9. Installing on Linux systems 89 Basic deployment............. 6 Installing and configuring DB2 ........ 89 Main Office with Fast-WAN Satellites ...... 7 Installation Steps ............ 90 Disaster Server Architecture ......... 9 Step 1 - Downloading IBM Endpoint Manager.. 90 Efficient relay setup ........... 10 Step 2 - Installing the Server........ 91 Hub and spoke ............. 11 Step 3 - Verifying Server Installation ..... 98 Remote Citrix / Terminal Services Configuration .. 13 Installation Command Options ........ 98 Silent installation ............ 99 Chapter 3. Assumptions and Installation Folder Structure ........ 106 Configuration, Masthead, and Log Files .... 107 requirements ............ 17 Managing the BigFix Services ........ 108 Assumptions .............. 17 Changing the database password ....... 108 Server requirements ........... 18 Changing the DB2 port .......... 109 Console requirements ........... 19 Authenticating Additional Servers (DSA) .... 109 Client requirements............ 19 Using DB2 Authentication ....... -

List of Application Added in ARL #2607
List of Application added in ARL #2607 Application Name Publisher .NET Framework 19.0 Microsoft .NET Runtime 6 Preview Microsoft .NET SDK 6 Preview Microsoft 3DMark UL 3uTools 2.35 3uTools 4D 17.6 4D 4K Stogram 3.0 OpenMedia ABACUS Studio 8.0 Avolution ABCpdf .NET 11.1 WebSupergoo Software ACQUITY Column Manager 1.7 Waters Acrobat Elements 17.1 Adobe ACT Enterprise Client 2.12 Access Control ACT Enterprise Client 2.3 Access Control ACTEnterprise 2.3 Vanderbilt Actiance Vantage OpenText Actional Agent 9.0 Progress Software Active Directory (AD) Bridge 8.5 Enterprise BeyondTrust Active Directory/LDAP Connector 5.0 Auth0 Active Intelligence Engine 4.4 Attivio ActivePresenter 8.1 Atomi Systems ActivePython 3.8 ActiveState ActivInspire 2.17 Promethean Activity Monitor 4.0 STEALTHbits Technologies Activity Monitor Agent 2.4 STEALTHbits Technologies ActiViz.NET 8.2 Supported Kitware SAS ActiViz.NET 8.2 Trial Kitware SAS ActiViz.NET 9.0 Supported Kitware SAS Acumen Cumulative 8.5 Deltek AD Tidy 2.6 Cjwdev AdAnalytics Adslytic Add-in Express for Microsoft Office and .NET 8.3 Professional Add-in Express Add-in Express for Microsoft Office and .NET 9.4 Premium Add-in Express Adlib PDF 5.1 Enterprise Adlib AdminStudio 2021 Flexera AdminStudio 2021 ZENworks Flexera Advance Design 2020 GRAITEC Advance Design 2021 GRAITEC Advanced SystemCare 14.0 IObit Advertising Editor 11.29 Microsoft Advisor 9.5 Belarc AFP Viewer 7.50 ISIS Papyrus Europe AG Agile Requirements Designer 3.1 Broadcom Alfresco Content Services 6.0 Alfresco Software AltspaceVR 4.1 Microsoft -

Virtualization As an Approach in the Development of IT System Implementation Process
Proceedings of the Federated Conference on ISBN 978-83-60810-22-4 Computer Science and Information Systems pp. 281–285 Virtualization as an approach in the development of IT system implementation process Iwona Chomiak-Orsa, Wiesława Gryncewicz, Maja Leszczyńska University of Economics ul. Komandorska 118/120, 53-345 Wroclaw, Poland Email: {iwona.chomiak, wieslawa.gryncewicz, maja.leszczynska}@ue.wroc.pl Abstract—Virtual administration of IT system implementa- the recent trend to virtualize the co-operation between the tion processes is now possible in small and micro-companies, provider and the client and employ remote implementation characterized by relative simplicity and marked recurrence of procedures and processes based on large potential of modern business processes. Popularity of such approach to implementa- tion is largely due to the wide availability of IT solutions offer- IT solutions – a trend observed and not yet sufficiently ad- ing remote administration of authorized IT resources. Virtual dressed in professional literature. form of implementation offers significant reduction of both cost and time, compared with traditional approach. Consequently, II.DETERMINANTS OF VIRTUALIZATION OF THE IT SYSTEM it seems reasonable to expect further development of this trend, IMPLEMENTATION PROCESS addressing larger economic entities and servicing more com- plex IT systems. At present, straight majority of companies, especially large and medium-sized, employ consolidated application I. INTRODUCTION suites to service the main areas of their business activities, mainly in the sphere of accounting, personnel and wages, OMPANIES competing on modern markets face in- and sales [4]. Due to good saturation of IT solutions in this creased dynamics of changes, fierce competition and C area, software providers seek to extend their offer to cover the need of making fast decisions.