IBM Z Systems Hardware - 2016 Technical Overview
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

IBM Z Systems Introduction May 2017
IBM z Systems Introduction May 2017 IBM z13s and IBM z13 Frequently Asked Questions Worldwide ZSQ03076-USEN-15 Table of Contents z13s Hardware .......................................................................................................................................................................... 3 z13 Hardware ........................................................................................................................................................................... 11 Performance ............................................................................................................................................................................ 19 z13 Warranty ............................................................................................................................................................................ 23 Hardware Management Console (HMC) ..................................................................................................................... 24 Power requirements (including High Voltage DC Power option) ..................................................................... 28 Overhead Cabling and Power ..........................................................................................................................................30 z13 Water cooling option .................................................................................................................................................... 31 Secure Service Container ................................................................................................................................................. -
The 32-Bit PA-RISC Run-Time Architecture Document, V. 1.0 for HP
The 32-bit PA-RISC Run-time Architecture Document HP-UX 11.0 Version 1.0 (c) Copyright 1997 HEWLETT-PACKARD COMPANY. The information contained in this document is subject to change without notice. HEWLETT-PACKARD MAKES NO WARRANTY OF ANY KIND WITH REGARD TO THIS MATERIAL, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. Hewlett-Packard shall not be liable for errors contained herein or for incidental or consequential damages in connection with furnishing, performance, or use of this material. Hewlett-Packard assumes no responsibility for the use or reliability of its software on equipment that is not furnished by Hewlett-Packard. This document contains proprietary information which is protected by copyright. All rights are reserved. No part of this document may be photocopied, reproduced, or translated to another language without the prior written consent of Hewlett-Packard Company. CSO/STG/STD/CLO Hewlett-Packard Company 11000 Wolfe Road Cupertino, California 95014 By The Run-time Architecture Team 32-bit PA-RISC RUN-TIME ARCHITECTURE DOCUMENT 11.0 version 1.0 -1 -2 CHAPTER 1 Introduction 7 1.1 Target Audiences 7 1.2 Overview of the PA-RISC Runtime Architecture Document 8 CHAPTER 2 Common Coding Conventions 9 2.1 Memory Model 9 2.1.1 Text Segment 9 2.1.2 Initialized and Uninitialized Data Segments 9 2.1.3 Shared Memory 10 2.1.4 Subspaces 10 2.2 Register Usage 10 2.2.1 Data Pointer (GR 27) 10 2.2.2 Linkage Table Register (GR 19) 10 2.2.3 Stack Pointer (GR 30) 11 2.2.4 Space -
Processor-103
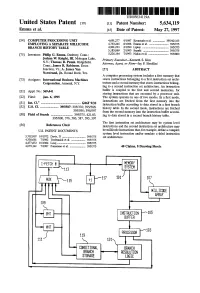
US005634119A United States Patent 19 11 Patent Number: 5,634,119 Emma et al. 45 Date of Patent: May 27, 1997 54) COMPUTER PROCESSING UNIT 4,691.277 9/1987 Kronstadt et al. ................. 395/421.03 EMPLOYING ASEPARATE MDLLCODE 4,763,245 8/1988 Emma et al. ........................... 395/375 BRANCH HISTORY TABLE 4,901.233 2/1990 Liptay ...... ... 395/375 5,185,869 2/1993 Suzuki ................................... 395/375 75) Inventors: Philip G. Emma, Danbury, Conn.; 5,226,164 7/1993 Nadas et al. ............................ 395/800 Joshua W. Knight, III, Mohegan Lake, Primary Examiner-Kenneth S. Kim N.Y.; Thomas R. Puzak. Ridgefield, Attorney, Agent, or Firm-Jay P. Sbrollini Conn.; James R. Robinson, Essex Junction, Vt.; A. James Wan 57 ABSTRACT Norstrand, Jr., Round Rock, Tex. A computer processing system includes a first memory that 73 Assignee: International Business Machines stores instructions belonging to a first instruction set archi Corporation, Armonk, N.Y. tecture and a second memory that stores instructions belong ing to a second instruction set architecture. An instruction (21) Appl. No.: 369,441 buffer is coupled to the first and second memories, for storing instructions that are executed by a processor unit. 22 Fied: Jan. 6, 1995 The system operates in one of two modes. In a first mode, instructions are fetched from the first memory into the 51 Int, C. m. G06F 9/32 instruction buffer according to data stored in a first branch 52 U.S. Cl. ....................... 395/587; 395/376; 395/586; history table. In the second mode, instructions are fetched 395/595; 395/597 from the second memory into the instruction buffer accord 58 Field of Search ........................... -
The 32-Bit PA-RISC Run- Time Architecture Document
The 32-bit PA-RISC Run- time Architecture Document HP-UX 10.20 Version 3.0 (c) Copyright 1985-1997 HEWLETT-PACKARD COMPANY. The information contained in this document is subject to change without notice. HEWLETT-PACKARD MAKES NO WARRANTY OF ANY KIND WITH REGARD TO THIS MATERIAL, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OFMERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. Hewlett-Packard shall not be liable for errors contained herein or for incidental or consequential damages in connection with furnishing, performance, or use of this material. Hewlett-Packard assumes no responsibility for the use or reliability of its software on equipment that is not furnished by Hewlett-Packard. This document contains proprietary information which is protected by copyright. All rights are reserved. No part of this document may be photocopied, reproduced, or translated to another language without the prior written consent of Hewlett- Packard Company. CSO/STG/STD/CLO Hewlett-Packard Company 11000 Wolfe Road Cupertino, California 95014 By The Run-time Architecture Team CHAPTER 1 Introduction This document describes the runtime architecture for PA-RISC systems running either the HP-UX or the MPE/iX operating system. Other operating systems running on PA-RISC may also use this runtime architecture or a variant of it. The runtime architecture defines all the conventions and formats necessary to compile, link, and execute a program on one of these operating systems. Its purpose is to ensure that object modules produced by many different compilers can be linked together into a single application, and to specify the interfaces between compilers and linker, and between linker and operating system. -

Design of the RISC-V Instruction Set Architecture
Design of the RISC-V Instruction Set Architecture Andrew Waterman Electrical Engineering and Computer Sciences University of California at Berkeley Technical Report No. UCB/EECS-2016-1 http://www.eecs.berkeley.edu/Pubs/TechRpts/2016/EECS-2016-1.html January 3, 2016 Copyright © 2016, by the author(s). All rights reserved. Permission to make digital or hard copies of all or part of this work for personal or classroom use is granted without fee provided that copies are not made or distributed for profit or commercial advantage and that copies bear this notice and the full citation on the first page. To copy otherwise, to republish, to post on servers or to redistribute to lists, requires prior specific permission. Design of the RISC-V Instruction Set Architecture by Andrew Shell Waterman A dissertation submitted in partial satisfaction of the requirements for the degree of Doctor of Philosophy in Computer Science in the Graduate Division of the University of California, Berkeley Committee in charge: Professor David Patterson, Chair Professor Krste Asanovi´c Associate Professor Per-Olof Persson Spring 2016 Design of the RISC-V Instruction Set Architecture Copyright 2016 by Andrew Shell Waterman 1 Abstract Design of the RISC-V Instruction Set Architecture by Andrew Shell Waterman Doctor of Philosophy in Computer Science University of California, Berkeley Professor David Patterson, Chair The hardware-software interface, embodied in the instruction set architecture (ISA), is arguably the most important interface in a computer system. Yet, in contrast to nearly all other interfaces in a modern computer system, all commercially popular ISAs are proprietary. -

A Lisp Oriented Architecture by John W.F
A Lisp Oriented Architecture by John W.F. McClain Submitted to the Department of Electrical Engineering and Computer Science in partial fulfillment of the requirements for the degrees of Master of Science in Electrical Engineering and Computer Science and Bachelor of Science in Electrical Engineering at the MASSACHUSETTS INSTITUTE OF TECHNOLOGY September 1994 © John W.F. McClain, 1994 The author hereby grants to MIT permission to reproduce and to distribute copies of this thesis document in whole or in part. Signature of Author ...... ;......................... .............. Department of Electrical Engineering and Computer Science August 5th, 1994 Certified by....... ......... ... ...... Th nas F. Knight Jr. Principal Research Scientist 1,,IA £ . Thesis Supervisor Accepted by ....................... 3Frederic R. Morgenthaler Chairman, Depattee, on Graduate Students J 'FROM e ;; "N MfLIT oARIES ..- A Lisp Oriented Architecture by John W.F. McClain Submitted to the Department of Electrical Engineering and Computer Science on August 5th, 1994, in partial fulfillment of the requirements for the degrees of Master of Science in Electrical Engineering and Computer Science and Bachelor of Science in Electrical Engineering Abstract In this thesis I describe LOOP, a new architecture for the efficient execution of pro- grams written in Lisp like languages. LOOP allows Lisp programs to run at high speed without sacrificing safety or ease of programming. LOOP is a 64 bit, long in- struction word architecture with support for generic arithmetic, 64 bit tagged IEEE floats, low cost fine grained read and write barriers, and fast traps. I make estimates for how much these Lisp specific features cost and how much they may speed up the execution of programs written in Lisp. -

IBM Z13 Server Technology
Introducing the IBM® z13™ Server Platform Structure and Performance Monte Bauman Enterprise Server Technical Support IBM Columbus [email protected] January 2015 IBM z Systems Agenda § Design Imperatives § The IBM z Systems z13 Server § The z13 Big Data Server 2 © 2015 IBM Corporation IBM z Systems Design Imperatives IBM z Systems Business Imperatives The Mobile Moment The Odds are High … Business Management is interested in... Enterprise § Promoting High Retention Rates and Capturing Class Competitive share through mobile interactions Cloud § Driving integrated/smart transactions that improve the Client Experience (e.g. Next Best Action) Business- Critical § Growing and Improving the IT services consumer Analytics experience within Existing Environmental Envelope Smart Transactions 4 © 2015 IBM Corporation IBM z Systems IBM z13 Design Primitives The IBM z13 Server was developed with the intent to: § Capture transaction growth through mobile enablement of existing systems § Drive integrated analytics at the time of the transaction § Deliver higher levels of Capacity and Performance within the Existing Environmental Envelope Enclave-Encapsulated Systems of Engagement Systems of Record Systems of Insight 5 © 2015 IBM Corporation IBM z Systems The IBM z13 Server 6 © 2015 IBM Corporation IBMIBM z Systems z13 platform positioning Platform Core Capabilities: Transaction Processing • The world’s premier transaction and data engine now enabled for Data Serving the mobile generation Mixed Workloads Operational Efficiency • The integrated transaction -

Brief History of Microprogramming
Microprogramming History -- Mark Smotherman A Brief History of Microprogramming Mark Smotherman Last updated: October 2012 Summary: Microprogramming is a technique to implement the control logic necessary to execute instructions within a processor. It relies on fetching low-level microinstructions from a control store and deriving the appropriate control signals as well as microprogram sequencing information from each microinstruction. Definitions and Example Although loose usage has sometimes equated the term "microprogramming" with the idea of "programming a microcomputer", this is not the standard definition. Rather, microprogramming is a systematic technique for implementing the control logic of a computer's central processing unit. It is a form of stored-program logic that substitutes for hardwired control circuitry. The central processing unit in a computer system is composed of a data path and a control unit. The data path includes registers, function units such as shifters and ALUs (arithmetic and logic units), internal processor busses and paths, and interface units for main memory and I/O busses. The control unit governs the series of steps taken by the data path during the execution of a user- visible instruction, or macroinstruction (e.g., load, add, store). Each action of the datapath is called a register transfer and involves the transfer of information within the data path, possibly including the transformation of data, address, or instruction bits by the function units. A register transfer is accomplished by gating out (sending) register contents onto internal processor busses, selecting the operation of ALUs, shifters, etc., through which that information might pass, and gating in (receiving) new values for one or more registers. -

POWER4 System Microarchitecture
by J. M. Tendler J. S. Dodson POWER4 J. S. Fields, Jr. H. Le system B. Sinharoy microarchitecture The IBM POWER4 is a new microprocessor commonplace. The RS64 and its follow-on organized in a system structure that includes microprocessors, the RS64-II [6], RS64-III [7], and RS64- new technology to form systems. The name IV [8], were optimized for commercial applications. The POWER4 as used in this context refers not RS64 initially appeared in systems operating at 125 MHz. only to a chip, but also to the structure used Most recently, the RS64-IV has been shipping in systems to interconnect chips to form systems. operating at up to 750 MHz. The POWER3 and its follow- In this paper we describe the processor on, the POWER3-II [9], were optimized for technical microarchitecture as well as the interconnection applications. Initially introduced at 200 MHz, most recent architecture employed to form systems up to systems using the POWER3-II have been operating at a 32-way symmetric multiprocessor. 450 MHz. The RS64 microprocessor and its follow-ons were also used in AS/400* systems (the predecessor Introduction to today’s eServer iSeries*). IBM announced the RISC System/6000* (RS/6000*, the POWER4 was designed to address both commercial and predecessor of today’s IBM eServer pSeries*) family of technical requirements. It implements and extends in a processors in 1990. The initial models ranged in frequency compatible manner the 64-bit PowerPC Architecture [10]. from 20 MHz to 30 MHz [1] and achieved performance First used in pSeries systems, it will be staged into the levels exceeding those of many of their contemporaries iSeries at a later date. -

The RISC-V Instruction Set Manual Volume I: User-Level ISA Document Version 2.2
The RISC-V Instruction Set Manual Volume I: User-Level ISA Document Version 2.2 Editors: Andrew Waterman1, Krste Asanovi´c1;2 1SiFive Inc., 2CS Division, EECS Department, University of California, Berkeley [email protected], [email protected] May 7, 2017 Contributors to all versions of the spec in alphabetical order (please contact editors to suggest corrections): Krste Asanovi´c,Rimas Aviˇzienis,Jacob Bachmeyer, Christopher F. Batten, Allen J. Baum, Alex Bradbury, Scott Beamer, Preston Briggs, Christopher Celio, David Chisnall, Paul Clayton, Palmer Dabbelt, Stefan Freudenberger, Jan Gray, Michael Hamburg, John Hauser, David Horner, Olof Johansson, Ben Keller, Yunsup Lee, Joseph Myers, Rishiyur Nikhil, Stefan O'Rear, Albert Ou, John Ousterhout, David Patterson, Colin Schmidt, Michael Taylor, Wesley Terpstra, Matt Thomas, Tommy Thorn, Ray VanDeWalker, Megan Wachs, Andrew Waterman, Robert Wat- son, and Reinoud Zandijk. This document is released under a Creative Commons Attribution 4.0 International License. This document is a derivative of \The RISC-V Instruction Set Manual, Volume I: User-Level ISA Version 2.1" released under the following license: c 2010{2017 Andrew Waterman, Yunsup Lee, David Patterson, Krste Asanovi´c. Creative Commons Attribution 4.0 International License. Please cite as: \The RISC-V Instruction Set Manual, Volume I: User-Level ISA, Document Version 2.2", Editors Andrew Waterman and Krste Asanovi´c,RISC-V Foundation, May 2017. Preface This is version 2.2 of the document describing the RISC-V user-level architecture. The document contains the following versions of the RISC-V ISA modules: Base Version Frozen? RV32I 2.0 Y RV32E 1.9 N RV64I 2.0 Y RV128I 1.7 N Extension Version Frozen? M 2.0 Y A 2.0 Y F 2.0 Y D 2.0 Y Q 2.0 Y L 0.0 N C 2.0 Y B 0.0 N J 0.0 N T 0.0 N P 0.1 N V 0.2 N N 1.1 N To date, no parts of the standard have been officially ratified by the RISC-V Foundation, but the components labeled \frozen" above are not expected to change during the ratification process beyond resolving ambiguities and holes in the specification. -

Linux on IBM Z13:Performance Aspects of New Technology And
Linux on IBM z13: Performance Aspects of New Technology and Features Mario Held ([email protected]) Linux on z Systems Performance Analyst IBM Corporation Session 17772 August 13, 2015 Trademarks The following are trademarks of the International Business Machines Corporation in the United States and/or other countries. BlueMix ECKD IBM* Maximo* Smarter Cities* WebSphere* z Systems BigInsights FICON* Ibm.com MQSeries* Smarter Analytics XIV* z/VSE* Cognos* FileNet* IBM (logo)* Performance Toolkit for VM SPSS* z13 z/VM* DB2* FlashSystem IMS POWER* Storwize* zEnterprise* DB2 Connect GDPS* Informix* Quickr* System Storage* z/OS* Domino* GPFS InfoSphere Rational* Tivoli* DS8000* Sametime* * Registered trademarks of IBM Corporation The following are trademarks or registered trademarks of other companies. Adobe, the Adobe logo, PostScript, and the PostScript logo are either registered trademarks or trademarks of Adobe Systems Incorporated in the United States, and/or other countries. IT Infrastructure Library is a registered trademark of the Central Computer and Telecommunications Agency which is now part of the Office of Government Commerce. Intel, Intel logo, Intel Inside, Intel Inside logo, Intel Centrino, Intel Centrino logo, Celeron, Intel Xeon, Intel SpeedStep, Itanium, and Pentium are trademarks or registered trademarks of Intel Corporation or its subsidiaries in the United States and other countries. Linux is a registered trademark of Linus Torvalds in the United States, other countries, or both. Microsoft, Windows, Windows NT, and the Windows logo are trademarks of Microsoft Corporation in the United States, other countries, or both. Windows Server and the Windows logo are trademarks of the Microsoft group of countries. ITIL is a registered trademark, and a registered community trademark of the Office of Government Commerce, and is registered in the U.S. -

Enhancing the RISC-V Instruction Set Architecture
Enhancing the RISC-V Instruction Set Architecture Plamen Petrov MInf Project (Part 1) Report Master of Informatics School of Informatics University of Edinburgh 2019 3 Abstract Since its emergence, RISC-V has offered a license-free alternative to proprietary in- struction sets designed by ARM and Intel by providing a stable base to researchers and small companies. This makes it possible for small companies and researchers to design new cores without incurring exorbitant costs. In our two-part project we explore RISC- V’s performance compared to the commercial ARM and X86 architectures. Most of the first part focuses on static code size, where we find that RISC-V performs very rea- sonably, but is behind Thumb2. For this reason, we propose improvements to RISC-V which constitute of new prologue and epilogue instructions that almost fully bridge this gap. We give ideas for other possible enhancements and plan to extend the project to cover dynamic measures in the second part. Overall, we conclude that RISC-V per- forms very well given the resources invested in it and open instruction sets, in general, deserve to be developed further for the better of the computer architecture field as a whole. 4 Acknowledgements I would like to express my gratitude to my supervisor Professor Nigel Topham for supporting me with the project throughout the year. Table of Contents 1 Introduction 7 1.1 Overview . 7 1.2 Aims . 9 1.3 Contributions . 10 1.4 Outline . 10 2 Background 11 2.1 Abbreviations . 11 2.2 Binary File . 11 2.3 SPEC2006 .