FM 3-24.2. Tactics in Counterinsurgency
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

FRATERNITIES Carstens
m _ edseodestt whe sepas the letter @t Maysee flaith Bad pinsw0 *ie aft Us enm tsee UP&U bwad wima-&imips1 ed t 000ta by er ber at whnne *ate fad both,"1110r110119"M mudt without. do usht net bb h h la W Wesatm112,0am has e the "am ofterams esm- * 'Dd him come W she said, and then been Ons in 4 bte" a fee-Illmmme a 4bvn--ai Mgea Sone of the maids of he the at thimrtu ofs0 ase a t be 1T. "evhgo de isn- temporary bath led a m dU- wh See waS esat to each m 1er et the esb- went to gli the mesenger Into the lsser who ghter-h&* 'a wwa hs' blood. wof I usaw m of the two tents of festval she added. bath made o she is ToU-q0-- a , bm his- **m7~TheIlulmef aemin cemnib- "And where Is-the'ma r you." Ie a towar the MareemA, BathM 944Wo baentehodAM LaVIARSIXh et PyM,aw atdtismA ~mmn-y. Adigagoswh.gnot tuigase with a, It was Yvette who answered ber. who stood u whSS anTraR TheI to a 100110 s-m 4101 yeaw ag& Some n"4aa 'Do not hear?' she erled, clapping at-the anddea fduf&panm. Vri mosame be itramarred M' aamhabemPto 8m-I he of a you wRi the harbt t t" eamtr Maes, No. of ts and Is her hands with pleasurw "His people are boy, slay YoeIldn 2, Hity, wt He bringing him up In triumph. Do you hear And at the wonhe preciptated Mise rec"neftd as me at the most sette aGd leg. -

GREGORY the Natures of War FINAL May 2015
!1 The Natures of War Derek Gregory for Neil 1 In his too short life, Neil Smith had much to say about both nature and war: from his seminal discussion of ‘the production of nature’ in his first book, Uneven development, to his dissections of war in the twentieth and early twenty-first centuries in American Empire – where he identified the ends of the First and Second World Wars as crucial punctuations in the modern genealogy of globalisation – and its coda, The endgame of globalization, a critique of America’s wars conducted in the shadows of 9/11. 2 And yet, surprisingly, he never linked the two. He was of course aware of their connections. He always insisted that the capitalist production of nature, like that of space, was never – could not be – a purely domestic matter, and he emphasised that the modern projects of colonialism and imperialism depended upon often spectacular displays of military violence. But he did not explore those relations in any systematic or substantive fashion. He was not alone. The great Marxist critic Raymond Williams once famously identified ‘nature’ as ‘perhaps the most complex word in the [English] language.’ Since he wrote, countless commentators have elaborated on its complexities, but few of them 1 This is a revised and extended version of the first Neil Smith Lecture, delivered at the University of St Andrews – Neil’s alma mater – on 14 November 2013. I am grateful to Catriona Gold for research assistance on the Western Desert, to Paige Patchin for lively discussions about porno-tropicality and the Vietnam war, and to Noel Castree, Dan Clayton, Deb Cowen, Isla Forsyth, Gastón Gordillo, Jaimie Gregory, Craig Jones, Stephen Legg and the editorial collective of Antipode for radically improving my early drafts. -

The North Korean Nuclear Crisis: Past Failures, Present Solutions
Saint Louis University Law Journal Volume 50 Number 2 A Tribute to the Honorable Michael A. Article 16 Wolff (Winter 2006) 2006 The North Korean Nuclear Crisis: Past Failures, Present Solutions Morse Tan The University of Texas at Austin School of Law Follow this and additional works at: https://scholarship.law.slu.edu/lj Part of the Law Commons Recommended Citation Morse Tan, The North Korean Nuclear Crisis: Past Failures, Present Solutions, 50 St. Louis U. L.J. (2006). Available at: https://scholarship.law.slu.edu/lj/vol50/iss2/16 This Article is brought to you for free and open access by Scholarship Commons. It has been accepted for inclusion in Saint Louis University Law Journal by an authorized editor of Scholarship Commons. For more information, please contact Susie Lee. SAINT LOUIS UNIVERSITY SCHOOL OF LAW THE NORTH KOREAN NUCLEAR CRISIS: PAST FAILURES, PRESENT SOLUTIONS MORSE TAN* ABSTRACT North Korea has recently announced that it has developed nuclear weapons and has pulled out of the six-party talks. These events do not emerge out of a vacuum, and this Article lends perspective through an interdisciplinary lens that seeks to grapple with the complexities and provide constructive approaches based on this well-researched understanding. This Article analyzes political, military, historical, legal and other angles of this international crisis. Past dealings with North Korea have been unfruitful because other nations do not recognize the ties between North Korean acts and its ideology and objectives. For a satisfactory resolution to the current crisis, South Korea and the United States must maintain sufficient deterrence, focus on multi-lateral and international avenues, and increase the negative and later positive incentives for North Korean compliance with its international obligations. -
Airpower in Three Wars
AIRPOWER IN THREE WARS GENERAL WILLIAM W. MOMYER USAF, RET. Reprint Edition EDITORS: MANAGING EDITOR - LT COL A. J. C. LAVALLE, MS TEXTUAL EDITOR - MAJOR JAMES C. GASTON, PHD ILLUSTRATED BY: LT COL A. J. C. LAVALLE Air University Press Maxwell Air Force Base, Alabama April 2003 Air University Library Cataloging Data Momyer, William W. Airpower in three wars / William W. Momyer ; managing editor, A. J. C. Lavalle ; textual editor, James C. Gaston ; illustrated by A. J. C. Lavalle–– Reprinted. p. ; cm. With a new preface. Includes bibliographical references and index. ISBN 1-58566-116-3 1. Airpower. 2. World War, 1939–1945––Aerial operations. 3. Korean War. 1950–1953––Aerial operations. 4. Vietnamese Conflict, 1961–1975––Aerial oper- ations. 5. Momyer, William W. 6. Aeronautics, Military––United States. I. Title. II. Lavalle, A. J. C. (Arthur J. C.), 1940– III. Gaston, James C. 358.4/009/04––dc21 Disclaimer Opinions, conclusions, and recommendations expressed or implied within are solely those of the author and do not necessarily represent the views of Air University, the United States Air Force, the Department of Defense, or any other US government agency. Cleared for public release. Air University Press 131 West Shumacher Avenue Maxwell AFB AL 36112-6615 http://aupress.maxwell.af.mil ii TO . all those brave airmen who fought their battles in the skies for command of the air in World War II, Korea, and Vietnam. iii THIS PAGE INTENTIONALLY LEFT BLANK PREFACE 2003 When I received the request to update my 1978 foreword to this book, I thought it might be useful to give my perspective of some aspects on the employment of airpower in the Persian Gulf War, the Air War over Serbia (Operation Allied Force), and the war in Afghanistan (Operation Enduring Freedom). -

Vietnam War US Army Video Log Michael Momparler Born
Video Log Michael Momparler Vietnam War U.S. Army Born: 03/05/1947 Interviewed on 11/20/2012 Interviewed by: George Jones 00:00:00 Introduction 00:00:23 Michael Momparler’s highest rank was 1st Lieutenant. 00:00:35 Momparler served in III Corps in Vietnam 00:00:45 Momparler was living in College Point, NY when he enlisted in the Army on 4/18/1966. He joined because he was a wild teenager with legal problems and few other options 00:01:45 Momparler discusses first days in the U.S. Army and his thoughts about the experience and the military experiences of other family members; specifically a cousin who suffered the loss of six fellow Marines. 00:03:23 Momparler discusses basic training experiences like using monkey bars, the mile run, and KP. 00:04:40 Momparler discusses being selected for Officer Candidate School - OCS. Mentions the testing and that he was encouraged to tell the interviewing officer that the war in Vietnam should be escalated. Entered OCS at age 19. 00:05:50 Momparler transition from basic training to advanced infrantry training to OCS. 00:06:24 Momparler discusses experiences with the M-14, M-15, and M-16 rifles. 00:07:00 Momparler discusses the experience of Officer Candidate School. 00:10:32 Momparler mentions that one of his commanding officers was in the Bay of Pigs invasion. Discusses the amount of combat experience, or Vietnam experience of his commanding officers at OCS. 00:11:00 Momparler discusses how OCS candidates used the OCS experience to limit their amount of time in the Army or avoid having to serve in Vietnam. -
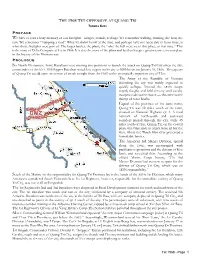
Tet 1968 Draft 2
THOMAS KJOS We have at least a hazy memory of our firefights - images, sounds, feelings. We remember walking, running, the heat, the rain. We remember “humping a load.” What we didn’t know at the time, and perhaps have not been able to learn since, is what those firefights were part of. The larger battles, the plans, the “why the hell were we in that place, at that time.” This is the story of Delta Company at Tet in 1968. It is also the story of the plans and battles that give greater context to our place in the history of the Vietnam war. Six North Vietnamese Army Battalions were moving into positions to launch the attack on Quang Tri City when the elite commandos of the NVA 10th Sapper Battalion struck key targets in the city at 0200 hours on January 31, 1968. The capture of Quang Tri would open an avenue of attack straight from the DMZ to the strategically important city of Hue. The Army of the Republic of Vietnam defending the city was widely expected to quickly collapse. Instead, the ARVN troops stayed, fought, and held the city until cavalry troopers rode to the rescue — this time to the thump of rotor blades. Capital of the province of the same name, Quang Tri was 12 miles south of the DMZ, situated on National Highway QL 1. A road network of north-south and east-west corridors passed through the city. Only 45 miles north of Hue, Quang Tri, on the coastal plain, was vulnerable to attack from all but the west, where the Thach Han river presented a formidable barrier. -

DUE 43 Cover
M4 SHERMAN TYPE 97 CHI-HA The Pacific 1945 STEVEN J. ZALOGA © Osprey Publishing • www.ospreypublishing.com M4 SHERMAN TYPE 97 CHI-HA The Pacific 1945 STEVEN J. ZALOGA © Osprey Publishing • www.ospreypublishing.com CONTENTS Introduction 4 Chronology 8 Design and Development 10 Technical Specifications 21 The Combatants 30 The Strategic Situation 41 Combat 47 Statistics and Analysis 74 Bibliography 78 Index 80 © Osprey Publishing • www.ospreypublishing.com INTRODUCTION Most titles in the Duel series deal with weapons of similar combat effectiveness. But what happens when the weapons of one side are dramatically inferior to those of the other? Could the technological imbalance be overcome by innovative tactics? This title examines such a contest, the US Army’s M4A3 Sherman medium tank against the Japanese Type 97-kai Shinhoto Chi-Ha in the Philippines in 1945. Tank combat in the Pacific War of 1941–45 is not widely discussed. There has long been a presumption that the terrain conditions in many areas, especially the mountainous tropical jungles of the Southwest Pacific and Burma, were not well suited to tank use. Yet the terrain of the Pacific battlefields varied enormously, from the fetid jungles of New Guinea to the rocky coral atolls of the Central Pacific. In many of the critical campaigns of 1944–45, the terrain was suitable for tank use and they became a critical ingredient in the outcome of the fighting. This book examines the largest single armored clash of the Pacific War – on Luzon in the Philippines in January–February 1945. This was the only time that the Imperial Japanese Army (IJA) committed an entire armored division against American or British forces. -

Modern Guerrilla Tactics
Guerrilla Tactics Guerrilla Tactics The Use of Decoy Rockets and Missiles Fire decoy missiles and rockets at the enemy in order to overwhelm their anti-missile systems (Patriot, Iron Dome, etc.). Decoy missiles and rockets can be fired first, then followed up by the real missiles and rockets or the decoys can be mixed in with the real. The objective is to get the enemy to shoot down the decoys and possibly run out of missiles. The decoys are, on the other hand, cheap and inexpensive rockets or perhaps some could be specialized missiles that disrupt enemy radar, etc. Perhaps hundreds of balloons with thin strips of aluminum attached to them are sent up to confuse enemy radar or balloons made of thin foil like material. Done to confuse enemy radar during a missile or rocket barrage. Decoy rockets positioned on the ground. Perhaps fake ground crews "hiding" nearby. Not too well hidden. Used to draw enemy fire away from real rockets and soldiers. Used to waste enemy munitions on false targets. Common Guerrilla Tactics The guerrillas can draw enemy forces out of major population areas and into remote border sanctuaries where supply and escape can be facilitated. This helps undermine enemy pacification efforts on the civilian population and disperses his forces. The enemy cannot send large amounts of soldiers to occupy every city, town, village, block, building, etc. The enemy cannot be strong everywhere. If the enemy is strong in one area, he will be weak in another. Attack the enemy where he is weak, not where he is strong. -

Livret De Regles ______1
COMBAT COMMANDER : PACIFIQUEPACIFIQUE–––– LIVRET DE REGLES ______________________________________________________ 1 LIVRET DE REGLES Un Jeu de Chad Jensen TABLE DES MATIERES COMBAT COMMANDER : PACIFIQUEPACIFIQUE–––– LIVRET DE REGLES ______________________________________________________ 2 INTRODUCTION TABLE DES MATIERES « C’était une sorte de combat rusé et sournois CC : E—CC : P Différences ..................................................................................... 3 qui n’a jamais ressemblé aux opérations Matériel ..................................................................................................................... 4 massives et orageuses d’Europe, où des Echelle du Jeu ........................................................................................................... 4 bataillons de chars étaient lancés contre Glossaire.................................................................................................................... 4 d’autres bataillons de chars et des armées de la taille de la population d’une ville Règles de Base—Matériel ........................................................................................ 5 bougeaient et manoeuvraient lourdement. Le 1 Cartes Destin................................................................................................... 5 Pacifique était une guerre différente. » 2 Cartes .............................................................................................................. 6 —Général Robert L. Eichelberger 3 Unités ............................................................................................................. -
COMBAT Security...J
t e engine• r • WINTER 1973 VOLUME 2 NUMBER4 2 Pipeline/News Item s 4 Stop-16/ L eiters to the EditOl' 5 Engineer In terview/ CP T George W . Gipe 8 Foul' Other Faces of Camoufuuie/ LT John S. H O?·n er 12 Tou gh Row to Plow/ En gin eer Staff 15 Color Me Camoufuuie/ L 'I'C E . N . J on es 16 The H elph d W ido w/Engineer Staff 18 The Role of the Erutimeer in Combat Security/ Engin ee?' Staff 21 Camoufuuie, Carnoufuuie, Wherefore A rt. Thou, Ca/moufuuie?/ CPT Georae VV . Gipe 25 The In stan t Obstacle/Robert B. Bockiiruj 28 Dinuumic Trainin g/ En gin eer Staff 30 The Engineers R ole in Defensive Operaticms/ MAJ L eToy A . Sch/m ult 34 Caesar's Etunneere/Ci'T James M. Sm ith 36 BTidgin g The Gap /Career Notes DEPARTMENTS: Chief's Briei e/Pipelin e/ Stop-I s Dynamic Tl·aining/ BTidging The Gap U.S. Army Eng ineer Schoo l Fort Be lvo ir, Virg inia Commandant MG Robert R. Ploger Assistant Commandant CHIEF'S BRIEFS ..... BG Richa rd l. Ha rris Deputy A ssista nt Colonel Jonathan Williams, the U.S. Army's sixth Chief E ngineer, Comma nda nt and the first Superintend ent of the U.S. Military Academy at West COLCharles A. Mcleod Point, was born at Boston , Massachusetts on May 20, 1750. He was Secreta ry a grand-nephew of Benjam in Franklin, and acted as his private secretary LTC Robert l. -

High-Altitude ISR
March 2013/$5 High-Altitude ISR The Syria Question Vets Courts Iraqi Freedom March 2013, Vol. 96, No. 3 Publisher Craig R. McKinley Editor in Chief Adam J. Hebert Editorial [email protected] Editor Suzann Chapman Executive Editors Michael C. Sirak John A. Tirpak Senior Editors Amy McCullough Marc V. Schanz Associate Editor Aaron M. U. Church Contributors Walter J. Boyne, John T. Correll, Robert 38 S. Dudney, Rebecca Grant, Peter Grier, Otto Kreisher, Anna Mulrine FEATURES Production [email protected] 4 Editorial: Leaving No One Behind Managing Editor By Adam J. Hebert Juliette Kelsey Chagnon Identifying Keller and Meroney was extraordinary—and typical. Assistant Managing Editor Frances McKenney 26 The Syria Question By John A. Tirpak Editorial Associate June Lee 46 An air war would likely be tougher than what the US saw in Serbia or Senior Designer Libya. Heather Lewis 32 Spy Eyes in the Sky Designer By Marc V. Schanz Darcy N. Lewis The long-term futures for the U-2 and Global Hawk are uncertain, but for Photo Editor now their unique capabilities remain Zaur Eylanbekov in high demand. Production Manager 38 Iraqi Freedom and the Air Force Eric Chang Lee By Rebecca Grant The Iraq War changed the Air Force Media Research Editor in ways large and small. Chequita Wood 46 Strike Eagle Rescue Advertising [email protected] By Otto Kreisher The airmen were on the ground Director of Advertising in Libya, somewhere between the William Turner warring loyalists and the friendly 1501 Lee Highway resistance. Arlington, Va. 22209-1198 Tel: 703/247-5820 52 Remote and Ready at Kunsan Telefax: 703/247-5855 Photography by Jim Haseltine About the cover: U-2 instructor pilots at North Korea is but a short flight away. -
Excerpts from the Memoir of Trần Văn Thủy
Wayne Karlin Excerpts from the Memoir of Trần Văn Thủy n 2013, a memoir by the well-known documentary filmmaker Trần Văn Thủy was published in Vietnam, with the title Chuyện Nghề của Thủy: rendered in English as The Life and Adventures of Trần Văn Thủy: the Story of a Filmmaker. IThe memoir, co-written by Thuy and his friend Lê Thanh Dũng was snatched off the book store shelves by Vietnamese readers (both book store shelves and readers still being widespread and extant in Vietnam) and became a run-away best seller. Trần Văn Thủy is known for making films which are startlingly original and unblinkingly honest in their portrayal of both the strengths and problems of Vietnamese society, and his memoir was equally honest in recounting his own life and struggles. A good part of that life and the filmmaker’s vision was formed by the experience of war. Born in 1940, in the Northern city of Nam Dinh, Thuy and his family had to flee to a small farming village when French soldiers destroyed their house. That village only proved to be a temporary refuge: it was also attacked by the French, who shot and killed Thuy’s 14 year old brother in the process. The family finally ended up in Hanoi, where Thuy grew up. In 1965, after some perfunctory training, young Thuy was handed a Bolex camera and assigned as a People’s Army cameraman, tasked to film whatever he could of the war with the Americans. He was sent to the battlefields of South Vietnam, infiltrating down the Ho Chi Minh Trails to Quang Nam Province.