Computer Organisation PC Maintenance & Troubleshooting
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Broadwell Skylake Next Gen* NEW Intel NEW Intel NEW Intel Microarchitecture Microarchitecture Microarchitecture
15 лет доступности IOTG is extending the product availability for IOTG roadmap products from a minimum of 7 years to a minimum of 15 years when both processor and chipset are on 22nm and newer process technologies. - Xeon Scalable (w/ chipsets) - E3-12xx/15xx v5 and later (w/ chipsets) - 6th gen Core and later (w/ chipsets) - Bay Trail (E3800) and later products (Braswell, N3xxx) - Atom C2xxx (Rangeley) and later - Не включает в себя Xeon-D (7 лет) и E5-26xx v4 (7 лет) 2 IOTG Product Availability Life-Cycle 15 year product availability will start with the following products: Product Discontinuance • Intel® Xeon® Processor Scalable Family codenamed Skylake-SP and later with associated chipsets Notification (PDN)† • Intel® Xeon® E3-12xx/15xx v5 series (Skylake) and later with associated chipsets • 6th Gen Intel® Core™ processor family (Skylake) and later (includes Intel® Pentium® and Celeron® processors) with PDNs will typically be issued no later associated chipsets than 13.5 years after component • Intel Pentium processor N3700 (Braswell) and later and Intel Celeron processors N3xxx (Braswell) and J1900/N2xxx family introduction date. PDNs are (Bay Trail) and later published at https://qdms.intel.com/ • Intel® Atom® processor C2xxx (Rangeley) and E3800 family (Bay Trail) and late Last 7 year product availability Time Last Last Order Ship Last 15 year product availability Time Last Last Order Ship L-1 L L+1 L+2 L+3 L+4 L+5 L+6 L+7 L+8 L+9 L+10 L+11 L+12 L+13 L+14 L+15 Years Introduction of component family † Intel may support this extended manufacturing using reasonably Last Time Order/Ship Periods Component family introduction dates are feasible means deemed by Intel to be appropriate. -
Intel® E7501 Chipset for Embedded Computing
Product Brief Intel® E7501 Chipset for Embedded Computing Product Overview The Intel® E7501 chipset represents the next step in high-performance chipset technology, supporting single- and dual-processor platforms optimized for the Intel® Xeon™ processor and Low Voltage Intel® Xeon™ processor. It also supports uni-processor platforms optimized for the Intel® Pentium® M processor. The design delivers maximized system bus, memory, and I/O bandwidth to enhance performance, scalability, and end-user productivity while providing a smooth transition to next-generation technologies. Features that Maximize Performance of an Intel® E7501 Chipset-based Platform I Dual Intel Xeon processors and a 400/533 MHz I Single or dual DDR266 memory channels system bus provide up to 4.3 GB/s of available provide up to 4.3 GB/s of memory bandwidth bandwidth I Three hub interface 2.0 connections provide Intel in I Intel Pentium M processors and a 400 MHz multiple high-bandwidth I/O configuration Communications system bus provide up to 3.2 GB/s of available options, yielding up to 3.2 GB/s of I/O bandwidth bandwidth Features Benefits Supports one or two Intel® Xeon™ processors I Intel® NetBurst™ microarchitecture and the Hyper-Threading Technology of or Low Voltage Intel® Xeon™ processors the Intel Xeon processor combine to deliver world-class performance. Supports one Intel® Pentium® M processor I New microarchitecture supports low power and high performance. 400/533 MHz system bus capability I Up to 4.3 GB/s system bus bandwidth for increased memory and I/O throughput. Intel hub architecture 2.0 connection I Point-to-point connection between the MCH and up to three P64H2 hub to the Memory Controller Hub (MCH) devices provides up to 3.2 GB/s of bandwidth. -

C:\Andrzej\PDF\ABC Nagrywania P³yt CD\1 Strona.Cdr
IDZ DO PRZYK£ADOWY ROZDZIA£ SPIS TREFCI Wielka encyklopedia komputerów KATALOG KSI¥¯EK Autor: Alan Freedman KATALOG ONLINE T³umaczenie: Micha³ Dadan, Pawe³ Gonera, Pawe³ Koronkiewicz, Rados³aw Meryk, Piotr Pilch ZAMÓW DRUKOWANY KATALOG ISBN: 83-7361-136-3 Tytu³ orygina³u: ComputerDesktop Encyclopedia Format: B5, stron: 1118 TWÓJ KOSZYK DODAJ DO KOSZYKA Wspó³czesna informatyka to nie tylko komputery i oprogramowanie. To setki technologii, narzêdzi i urz¹dzeñ umo¿liwiaj¹cych wykorzystywanie komputerów CENNIK I INFORMACJE w ró¿nych dziedzinach ¿ycia, jak: poligrafia, projektowanie, tworzenie aplikacji, sieci komputerowe, gry, kinowe efekty specjalne i wiele innych. Rozwój technologii ZAMÓW INFORMACJE komputerowych, trwaj¹cy stosunkowo krótko, wniós³ do naszego ¿ycia wiele nowych O NOWOFCIACH mo¿liwoYci. „Wielka encyklopedia komputerów” to kompletne kompendium wiedzy na temat ZAMÓW CENNIK wspó³czesnej informatyki. Jest lektur¹ obowi¹zkow¹ dla ka¿dego, kto chce rozumieæ dynamiczny rozwój elektroniki i technologii informatycznych. Opisuje wszystkie zagadnienia zwi¹zane ze wspó³czesn¹ informatyk¹; przedstawia zarówno jej historiê, CZYTELNIA jak i trendy rozwoju. Zawiera informacje o firmach, których produkty zrewolucjonizowa³y FRAGMENTY KSI¥¯EK ONLINE wspó³czesny Ywiat, oraz opisy technologii, sprzêtu i oprogramowania. Ka¿dy, niezale¿nie od stopnia zaawansowania swojej wiedzy, znajdzie w niej wyczerpuj¹ce wyjaYnienia interesuj¹cych go terminów z ró¿nych bran¿ dzisiejszej informatyki. • Komunikacja pomiêdzy systemami informatycznymi i sieci komputerowe • Grafika komputerowa i technologie multimedialne • Internet, WWW, poczta elektroniczna, grupy dyskusyjne • Komputery osobiste — PC i Macintosh • Komputery typu mainframe i stacje robocze • Tworzenie oprogramowania i systemów komputerowych • Poligrafia i reklama • Komputerowe wspomaganie projektowania • Wirusy komputerowe Wydawnictwo Helion JeYli szukasz ]ród³a informacji o technologiach informatycznych, chcesz poznaæ ul. -
VIA Apollo P4X400 Chipset Enabling Total System Performance
VIA Apollo P4X400 Chipset White Paper VIA Apollo P4X400 Chipset Enabling Total System Performance High performance DDR400 chipset platform for the Intel® Pentium® 4 processor Page 1 VIA Apollo P4X400 Chipset White Paper Introduction The VIA Apollo P4X400 is a core logic chipset solution that makes Total System Performance a reality in Intel® Pentium® 4 processor based systems . Fusing the unequalled bandwidth of DDR400 with the Intel® Pentium® 4 processor, the VIA Apollo P4X400 with 533MHz processor bus, AGP 8X, ATA-133, USB 2.0 and 8X V-Link chip interconnect, brings an unmatched suite of new memory, system and I/O technologies to a single platform. In combination these technologies enable Intel® Pentium® 4 systems and servers to achieve heights of performance never scaled before. In the past, advances in one area of system performance have frequently been held back by I/O and connectivity bottlenecks, but with the advent of the VIA Apollo P4X400, every aspect of performance is addressed, delivering end user experiences that meet the high expectations of today’s consumers. The VT8235, with USB 2.0 integrated into a chipset for the first time, enables peripheral devices to send and receive data at 480 Mbps, 40 times faster than the previous USB standard. This data can then be sent to the North Bridge through the new 8X V-Link chip interconnect which offers 533MB/s of bandwidth, twice as much as Intel Hub Architecture, making sure the ultra fast processor and DDR333 memory subsystem is supplied with all the data it needs minimizing system delays and offering the smoothest system performance you will ever have experienced. -

Computer Hardware and Servicing
GOVERNMENT OF TAMILNADU DIRECTORATE OF TECHNICAL EDUCATION CHENNAI – 600 025 STATE PROJECT COORDINATION UNIT Diploma in Computer Engineering Course Code: 1052 M – Scheme e-TEXTBOOK on Computer Hardware and Servicing for VI Semester Diploma in Computer Engineering Convener for Computer Engineering Discipline: Tmt.A.Ghousia Jabeen Principal TPEVR Government Polytechnic College Vellore- 632202 Team Members for Computer Hardware and Servicing: Mr. M. Suresh Babu HOD / Computer Engineering, N.P.A. Centenary Polytechnic College, Kotagiri – 643217 Mr. H.Ganesh Lecturer (SG) / Computer Engineering, N.P.A. Centenary Polytechnic College, Kotagiri – 643217 Dr. S.Sharmila HOD / IT P.S.G. Polytechnic College, Coimbatore – 641001. Validated by Dr. S. Brindha HOD/Computer Networks, PSG Polytechnic College, Coimbatore – 641001. CONTENTS Unit No. Name of the Unit Page No. 1 MOTHERBOARD COMPONENTS 1 2 MEMORY AND I/O DEVICES 33 3 DISPLAY, POWER SUPPLY AND BIOS 91 4 MAINTENANCE AND TROUBLE SHOOTING OF 114 DESKTOP & LAPTOP COMPUTERS 5 MOBILE PHONE SERVICING 178 Unit-1 Motherboard Components UNIT -1 MOTHERBOARD COMPONENTS Learning Objectives: Learner should be able to ➢ Acquire the skills of motherboard and its components ➢ Explain the basic concepts of processor. ➢ Differentiate the types of processor technology ➢ Describe the concepts of chipsets ➢ Differentiate the features of PCI,AGP, USB and processor bus Introduction: To troubleshoot the PC effectively, a student must be familiar about the components and its features. This chapter focuses the motherboard and its components. Motherboard is an important component of the PC. The architecture and the construction of the motherboard are described. This chapter deals the various types of processors and its features. -

Comptia A+ Certification Exam Prep
Course 445 CompTIA A+ Certification Exam Prep 445/CN/H.3/709/H.2 Acknowledgments The author would like to thank the following people for their valuable help with this course: Teresa Shinn Carl Waldron Tim Watts Esteban Delgado Dave O’Neal Shirley Auguste Alicia Richardson © Learning Tree International, Inc. All rights reserved. Not to be reproduced without prior written consent. © LEARNING TREE INTERNATIONAL, INC. All rights reserved. All trademarked product and company names are the property of their respective trademark holders. No part of this publication may be reproduced, stored in a retrieval system, or transmitted in any form or by any means, electronic, mechanical, photocopying, recording or otherwise, or translated into any language, without the prior written permission of the publisher. Copying software used in this course is prohibited without the express permission of Learning Tree International, Inc. Making unauthorized copies of such software violates federal copyright law, which includes both civil and criminal penalties. Introduction and Overview Course Objectives The main objective of this course is to Prepare you to pass the CompTIA A+ 220-901 and 220-902 exams To accomplish this goal, you will learn how to Safely disassemble and reassemble a complete PC system Install and configure common PC motherboards and adapter cards Use an organized strategy to identify and troubleshoot common PC problems Select and install the correct type of RAM memory needed to upgrade a PC system Install and configure data storage systems, including hard disks, solid state drives (SSD), CD, and DVD-ROM drives Identify fundamental components of laptops and mobile devices and describe how to troubleshoot common problems © Learning Tree International, Inc. -
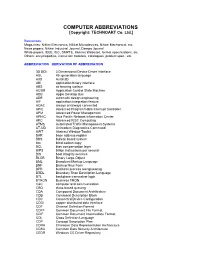
COMPUTER ABBREVIATIONS [Copyright: TECHNOART Co
COMPUTER ABBREVIATIONS [Copyright: TECHNOART Co. Ltd.] References: Magazines: Nikkei Electronics, Nikkei Microdevices, Nikkei Mechanical, etc. News papers: Nikkei Industrial Journal, Dempa Journal White papers: IEEE, IEC, SMPTE, Internet Websites, format specifications, etc. Others: encyclopedias, instruction booklets, catalogues, product spec., etc. ABBREVIATION DERIVATION OF ABBREVIATION 3D DDI 3 Dimensional Device Driver Interface 4GL 4th generation language A3D Aural 3D ABI application binary interface ABS air bearing surface ACSM Application Control State Machine ADB Apple Desktop Bus ADE automatic design engineering AIF application integration feature AOAC always on/always connected APIC Advanced Programmable Interrupt Controller APM Advanced Power Management APNIC Asia Pacific Network Information Center ARC Advanced RISC Computing ATMS Automated Traffic Management Systems AT-UD Unimodem Diagnostics Command AWT Abstract Window Toolkit BAR base address register BBS bulletin board system bcc blind carbon copy BCL bias compensation layer BIPS billion instructions per second BIS boot integrity services BLOB Binary Large Object BML Broadcast Markup Language BNF Backup Naur Form BPR business process reengineering BSDL Boundary Scan Description Language BTL backplane transceiver logic BTRON Business TRON C&C computer and communication CBQ class-based queuing CDA Compound Document Architecture CDB Command Description Block CDC Connected Device Configuration CDDI copper distributed data interface CDF Channel Definition Format CDFF Common -

OVERVIEW Intel Corporation Is an American Multinational Corporation
OVERVIEW ⌂ Introduced April 1, 1974. ⌂ Intel Corporation is an American multinational corporation headquartered in ⌂ 10 times faster than 8008. Santa Clara, California. ⌂ Used in the Altair 8800, Traffic light controller, cruise missile. ⌂ It is the inventor of the x86 series of microprocessors, the processors found in ⌂ Characteristics most personal computers. • 6 mm process ⌂ Intel Corporation, founded on July 18, 1968, is a portmanteau of • 4500 transistors Integrated Electronics (the fact that "intel" is the term for intelligence • 2 MHz information also made the name appropriate). • 8-bit word size ⌂ Intel sells its products and solutions to original equipment manufacturers • 40-pin DIP package (OEMs) and original design manufacturers (ODMs). Intel 8086/8088 ⌂ The 80486 architecture, for example, supports clock rates of from 33 to 66 ⌂ A 16 bit processors Introduced June 8, 1978(8086) and Introduced June 1, MHz. 1979(8088). ⌂ Because Intel discovered that it couldn't trademark its CPU numbers, it shifted ⌂ First used in the Compaq Deskpro IBM PC-compatible computers. Later used to a naming scheme, starting with the Pentium processors. Intel's sixth- in portable computing, and in the IBM PS/2 Model 25 and Model 30. Also generation chip is called the Pentium Pro. used in the AT&T PC6300 / Olivetti M24, a popular IBM PC-compatible HISTORY (predating the IBM PS/2 line). ⌂ Intel was originally founded in Mountain View, California in 1968 by Gordon E. ⌂ NASA used original 8086 CPUs on equipment for ground-based maintenance Moore, Robert Noyce, Arthur Rock and Max Palevsky. of the Space Shuttle Discovery until the end of the space shuttle program in ⌂ Intel's third employee was Andy Grove, a chemical engineer, who later ran the 2011. -

Multi-Core Programming
Digital Edition Digital Editions of selected Intel Press books are in addition to and complement the printed books. Click the icon to access information on other essential books for Developers and IT Professionals Visit our website at www.intel.com/intelpress Multi-Core Programming Increasing Performance through Software Multi-threading Shameem Akhter Jason Roberts Intel PRESS Copyright © 2006 Intel Corporation. All rights reserved. ISBN 0-9764832-4-6 This publication is designed to provide accurate and authoritative information in regard to the subject matter covered. It is sold with the understanding that the publisher is not engaged in professional services. If professional advice or other expert assistance is required, the services of a competent professional person should be sought. Intel Corporation may have patents or pending patent applications, trademarks, copyrights, or other intellectual property rights that relate to the presented subject matter. The furnishing of documents and other materials and information does not provide any license, express or implied, by estoppel or otherwise, to any such patents, trademarks, copyrights, or other intellectual property rights. Intel may make changes to specifications, product descriptions, and plans at any time, without notice. Fictitious names of companies, products, people, characters, and/or data mentioned herein are not intended to represent any real individual, company, product, or event. Intel products are not intended for use in medical, life saving, life sustaining, critical control or safety systems, or in nuclear facility applications. Intel, the Intel logo, Celeron, Intel Centrino, Intel NetBurst, Intel Xeon, Itanium, Pentium, MMX, and VTune are trademarks or registered trademarks of Intel Corporation or its subsidiaries in the United States and other countries. -

CS170-Q370/C246/H310 Mini-ITX Industrial Motherboard User’S Manual CS170-Q370/C246/H310
CS170-Q370/C246/H310 Mini-ITX Industrial Motherboard User’s Manual CS170-Q370/C246/H310 www.dfi.com Copyright FCC and DOC Statement on Class B This publication contains information that is protected by copyright. No part of it may be re- This equipment has been tested and found to comply with the limits for a Class B digital produced in any form or by any means or used to make any transformation/adaptation without device, pursuant to Part 15 of the FCC rules. These limits are designed to provide reason- the prior written permission from the copyright holders. able protection against harmful interference when the equipment is operated in a residential installation. This equipment generates, uses and can radiate radio frequency energy and, if not This publication is provided for informational purposes only. The manufacturer makes no installed and used in accordance with the instruction manual, may cause harmful interference representations or warranties with respect to the contents or use of this manual and specifi- to radio communications. However, there is no guarantee that interference will not occur in a cally disclaims any express or implied warranties of merchantability or fitness for any particular particular installation. If this equipment does cause harmful interference to radio or television purpose. The user will assume the entire risk of the use or the results of the use of this docu- reception, which can be determined by turning the equipment off and on, the user is encour- ment. Further, the manufacturer reserves the right to revise this publication and make changes aged to try to correct the interference by one or more of the following measures: to its contents at any time, without obligation to notify any person or entity of such revisions or changes. -

Z390 AORUS MASTER (Rev
Z390 AORUS MASTER (rev. 1.0) Key Features Specification Support News & Awards Learn more Buy CPU 1. Support for 9th and 8th Generation Intel® Core™ i9 processors/ Intel® Core™ i7 processors/ Intel® Core™ i5 processors/ Intel® Core™ i3 processors/ Intel® Pentium® processors/ Intel® Celeron® processors in the LGA1151 package 2. L3 cache varies with CPU (Please refer to "CPU Support List" for more information.) Chipset 1. Intel® Z390 Express Chipset Memory 1. 4 x DDR4 DIMM sockets supporting up to 64 GB of system memory 2. Dual channel memory architecture 3. Support for DDR4 4333(O.C.) / 4266(O.C.) / 4133(O.C.) / 4000(O.C.) / 3866(O.C.) / 3800(O.C.) / 3733(O.C.) / 3666(O.C.) / 3600(O.C.) / 3466(O.C.) / 3400(O.C.) / 3333(O.C.) / 3300(O.C.) / 3200(O.C.) / 3000(O.C.) / 2800(O.C.) / 2666 / 2400 / 2133 MHz memory modules 4. Support for ECC Un-buffered DIMM 1Rx8/2Rx8 memory modules (operate in non-ECC mode) 5. Support for non-ECC Un-buffered DIMM 1Rx8/2Rx8/1Rx16 memory modules 6. Support for Extreme Memory Profile (XMP) memory modules (Please refer to "Memory Support List" for more information.) Onboard Graphics Integrated Graphics Processor-Intel® HD Graphics support: 1. 1 x HDMI port, supporting a maximum resolution of 4096x2160@30 Hz * Support for HDMI 1.4 version and HDCP 2.2. Maximum shared memory of 1 GB Audio 1. Realtek® ALC1220-VB codec * The front panel line out jack supports DSD audio. 2. ESS SABRE 9118 DAC 3. High Definition Audio 4. 2/4/5.1/7.1-channel 5. -
Introduction to Operating Systems and Data Communication
IN2140: Introduction to Operating Systems and Data Communication Operating Systems: Introduction Pål Halvorsen Sunday, 3 February 19 Overview § Basic execution environment – an Intel example (why do you need an operating system (OS), or need to know anything about it) § What is an OS? § OS components and services (extended in later lectures) § Interrupts and system calls § Booting, protection, kernel organization University of Oslo INF2140, Pål Halvorsen Hardware § Central Processing Units (CPUs) § Memory (cache(s), RAM, ROM, Flash, …) § I/O Devices (network cards, disks, CD, keyboard, mouse, …) § Links (interconnects, busses, …) University of Oslo INF2140, Pål Halvorsen An easy, old example: Intel Hub Architecture (850 Chipset) Intel D850MD Motherboard: Source: Intel® Desktop Board D850MD/D850MV Technical Product Specification University of Oslo INF2140, Pål Halvorsen An easy, old example: Intel Hub Architecture i7 motherboard mouse, keyboard, parallel, serial, Intel D850MD Motherboard: network and USB connectors Source: Intel® Desktop Board D850MD/D850MV Technical Product Specification Video PCI Connectors (slots) Memory Controller Hub AGP slot Pentium 4 socket I/O Controller Hub RDRAM PCI interface bus RAMBUS RDRAM – 2 banks (4 slots) Firmware Hub – including BIOS Power connector Speaker Diskette connector Battery IDE drive connectors University of Oslo INF2140, Pål Halvorsen An easy, old example: Intel Hub Architecture application Pentium 4 Processor file system registers cache(s) system bus disk (64-bit, 400/533 MHz !~24-32 Gbps)