Intellectual Property Part 2 Pornography
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Information Disclosure Mechanism for Technological Protection Measures in China
Journal of Intellectual Property Rights Vol 17, November 2012, pp 532-538 Information Disclosure Mechanism for Technological Protection Measures in China Lili Zhao† Center for China Information Security Law, Xi’an Jiao tong University, Shaanxi Xi’an, P R China 710 049 Received 12 February 2012, revised 21 May 2012 With increasing cases of digital works being copied and pirated, technological protection measures have been greatly favoured by copyright owners for protecting the intellectual property in their digital works, while ensuring that these works can be used and disseminated. However, when any copyright owner or supplier fails to disclose the information of technological protection measures appropriately or effectively, damages such as privacy violations, security breaches and unfair competition may be caused to the public. Therefore, it is necessary to establish an information disclosure mechanism for technological protection measures, make the labeling obligation with regard to technological protection measures by copyright owners apparent and warning to security risks obligatory by legislation; effectively guarding against information security threats from the technological protection measures. Keywords: Technological protection measures, TPM, information disclosure, label and warning The advance of digital technologies make many information security, it is necessary to integrate such acts things become possible, including the copy and in a standardized, normalized and legal manner. dissemination of commercially valuable digital works Therefore, to further prevent copyright owners from through global digital network. Particularly, among using insecure or untested software, protect information the copyright owners of entertainment industry, security and prohibit the abuse of TPMs; disclosure technological protection measures (TPMs) have been obligations should be established for the right holders of regarded as a necessary creation to help digital works TPMs in the form of legislation. -
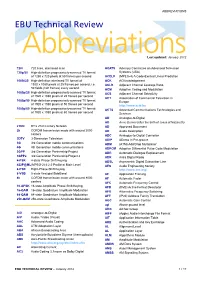
ABBREVIATIONS EBU Technical Review
ABBREVIATIONS EBU Technical Review AbbreviationsLast updated: January 2012 720i 720 lines, interlaced scan ACATS Advisory Committee on Advanced Television 720p/50 High-definition progressively-scanned TV format Systems (USA) of 1280 x 720 pixels at 50 frames per second ACELP (MPEG-4) A Code-Excited Linear Prediction 1080i/25 High-definition interlaced TV format of ACK ACKnowledgement 1920 x 1080 pixels at 25 frames per second, i.e. ACLR Adjacent Channel Leakage Ratio 50 fields (half frames) every second ACM Adaptive Coding and Modulation 1080p/25 High-definition progressively-scanned TV format ACS Adjacent Channel Selectivity of 1920 x 1080 pixels at 25 frames per second ACT Association of Commercial Television in 1080p/50 High-definition progressively-scanned TV format Europe of 1920 x 1080 pixels at 50 frames per second http://www.acte.be 1080p/60 High-definition progressively-scanned TV format ACTS Advanced Communications Technologies and of 1920 x 1080 pixels at 60 frames per second Services AD Analogue-to-Digital AD Anno Domini (after the birth of Jesus of Nazareth) 21CN BT’s 21st Century Network AD Approved Document 2k COFDM transmission mode with around 2000 AD Audio Description carriers ADC Analogue-to-Digital Converter 3DTV 3-Dimension Television ADIP ADress In Pre-groove 3G 3rd Generation mobile communications ADM (ATM) Add/Drop Multiplexer 4G 4th Generation mobile communications ADPCM Adaptive Differential Pulse Code Modulation 3GPP 3rd Generation Partnership Project ADR Automatic Dialogue Replacement 3GPP2 3rd Generation Partnership -
Windows Internals, Sixth Edition, Part 2
spine = 1.2” Part 2 About the Authors Mark Russinovich is a Technical Fellow in ® the Windows Azure™ group at Microsoft. Windows Internals He is coauthor of Windows Sysinternals SIXTH EDITION Administrator’s Reference, co-creator of the Sysinternals tools available from Microsoft Windows ® The definitive guide—fully updated for Windows 7 TechNet, and coauthor of the Windows Internals and Windows Server 2008 R2 book series. Delve inside Windows architecture and internals—and see how core David A. Solomon is coauthor of the Windows Internals book series and has taught components work behind the scenes. Led by a team of internationally his Windows internals class to thousands of renowned internals experts, this classic guide has been fully updated Windows developers and IT professionals worldwide, SIXTH for Windows 7 and Windows Server® 2008 R2—and now presents its including Microsoft staff. He is a regular speaker 6EDITION coverage in two volumes. at Microsoft conferences, including TechNet As always, you get critical, insider perspectives on how Windows and PDC. operates. And through hands-on experiments, you’ll experience its Alex Ionescu is a chief software architect and internal behavior firsthand—knowledge you can apply to improve consultant expert in low-level system software, application design, debugging, system performance, and support. kernel development, security training, and Internals reverse engineering. He teaches Windows internals courses with David Solomon, and is ® In Part 2, you will: active in the security research community. -

Of Price Discriminiation, Rootkits and Flatrates
Of Price Discriminiation, Rootkits and Flatrates Volker Grassmuck Helmholtz-Zentrum für Kulturtechnik, Humboldt-University Berlin 19 February 2006 DRAFT VERSION – final version is slated for print publication Licensed under Creative Commons Share-Alike Germany 2.0 „Copyright owners continue to be ambivalent about the Internet. On the one hand, it represents a fantastic new medium for distribution; on the other, many in the publishing industry see it as one ‚giant, out of control copying machine.‘ ... The very technological advances that make rights management more difficult – the dramatic reduction in costs of copying and distribution – also offer a fantastic opportunity for owners of intellectual content.“1 Without scarcity there is no market. Information by its nature is a public good.2 Copyright law artificially creates scarcity by granting exclusive rights to it for a limited time. Media technology so far helped enforcability of those rights because the means of production and the means of distribution of informational goods were expensive and therefore scarce. The digital revolution does away with this scarcity. PC and Internet bring to virtually everyone the power of the printing press and the recording studio. Only now, information‘s defining qualities of non-rivalrousness and non-excludability come to full bearing. Zero cost for reproduction and distribution is indeed a fantastic value proposition for information vendors. Alas, it is undermined by the fact that for consumers the cost of copying and distribution is zero as well. Peer-to-peer networks show that transporting bits from A to B is now such a low-cost service that users can effortlessly provide it to each other. -

Abkürzungs-Liste ABKLEX
Abkürzungs-Liste ABKLEX (Informatik, Telekommunikation) W. Alex 1. Juli 2021 Karlsruhe Copyright W. Alex, Karlsruhe, 1994 – 2018. Die Liste darf unentgeltlich benutzt und weitergegeben werden. The list may be used or copied free of any charge. Original Point of Distribution: http://www.abklex.de/abklex/ An authorized Czechian version is published on: http://www.sochorek.cz/archiv/slovniky/abklex.htm Author’s Email address: [email protected] 2 Kapitel 1 Abkürzungen Gehen wir von 30 Zeichen aus, aus denen Abkürzungen gebildet werden, und nehmen wir eine größte Länge von 5 Zeichen an, so lassen sich 25.137.930 verschiedene Abkür- zungen bilden (Kombinationen mit Wiederholung und Berücksichtigung der Reihenfol- ge). Es folgt eine Auswahl von rund 16000 Abkürzungen aus den Bereichen Informatik und Telekommunikation. Die Abkürzungen werden hier durchgehend groß geschrieben, Akzente, Bindestriche und dergleichen wurden weggelassen. Einige Abkürzungen sind geschützte Namen; diese sind nicht gekennzeichnet. Die Liste beschreibt nur den Ge- brauch, sie legt nicht eine Definition fest. 100GE 100 GBit/s Ethernet 16CIF 16 times Common Intermediate Format (Picture Format) 16QAM 16-state Quadrature Amplitude Modulation 1GFC 1 Gigabaud Fiber Channel (2, 4, 8, 10, 20GFC) 1GL 1st Generation Language (Maschinencode) 1TBS One True Brace Style (C) 1TR6 (ISDN-Protokoll D-Kanal, national) 247 24/7: 24 hours per day, 7 days per week 2D 2-dimensional 2FA Zwei-Faktor-Authentifizierung 2GL 2nd Generation Language (Assembler) 2L8 Too Late (Slang) 2MS Strukturierte -

SONY BMG Music Entertainment. Respondent. This Assurance Of
In the Matter of: SONY BMG Music Entertainment. Respondent. This Assuranceof Voluntary Complianceor Discontinuance('oAssurance") is enteredinto by the AttorneysGeneral of the Statesof Alabama,Alaska, Arizona, Arkansas,Connecticut, Delawareo Florida,Idatro,Illinois, Indiana,Iow4 Kentucky,Louisian4 Maine, Maryland, Massachusetts, Michigan,Mississippi, Montana" Nebraska, Nevada, New Jersey,New Mexico,New york, North Carolina,North Dakota,Ohio, Oklahoma,Oregon, Pennsylvania, Rhode Island, South Dakota,Tennessee, Vermont, Virginia, Washington,West Virginia, Wisconsin,and Wyoming, and by the Attorney Generalfor the District of Columbia("the States"),acting pursuantto their respectiveconsumet protection statutes,r and SONY BMG Music Entertainment(.SONy I ALABAMA: AlabamaDeceptive Trade Practices Act, Ala. Codeg 8-19-1,et seq.;ALASKA: Unfair TradePractices and Consumer Protection Act, AS 45.50.471,-etseq.;ARIZbNA: Arizonaconsumer lrf{191, A.R.s. $ 44-1521et seq.;ARKANSAS: Ark. stat.Ann., g 4-gg- l0l et seq.;COIYNECTICUT: Conn.Gen. Stat. $ 42-110a,et seq.; DELAWARE: Consumer FraudAct,6 Del.C.$251l, et seq.;DISTRICT OF COLUMBI* Districrof Columbia ConsumerProtection Procedures Act, D.C. Code$ 28-3901et seq.; FLORIDA: Deceptiveand Unfair TradePractices Act, Fla. Stat.Ch. 501.201et seq.;IDAHO: IdahoConsumer protection Act, IdahoCode $ 48-601,et seq.;ILLINOIS: ConsumerFraud and Deceptive Business PracticesAct, 815ILcs 505/l et seq.;INDIANA: Ind.code Ann. $24-5-b-5-l;IowA: Iowa ConsumerFraud Act, Iowa Codesection714.16; KENTUCKY: ConsumerProtection Act, Ky. Rev. Stat.$$ 367.1l0 to 367.990;LOUISIANA: Unfair Tradepractices and Consumer ProtectionLaw,La. Rev. Stat.Ann. $$51:1401to 5|:1420;MAINE: MaineUnfair Trade PracticesAct, 5 M.R.S.A.sections 207 and209;MARYLANDI MarylandConsumer protection Act, Md. -

The European IP Bulletin
The European IP Bulletin The Intellectual Property, Media & Technology Department Issue 28, January 2006 McDermott Will & Emery UK LLP 7 Bishopsgate London EC2N 3AR Tel: +44 20 7577 6900 Fax: +44 20 7577 6950 www.mwe.com www.mwe.com/london Boston Brussels Chicago Düsseldorf London Los Angeles Miami Munich New York Orange County Rome San Diego Silicon Valley Washington, D.C. SUMMARY OF PAGE CONTENTS NO. HOT TOPICS 1. WORLD TRADE ORGANISATION MEMBERS AGREE TO AMEND THE 1 TRIPS AGREEMENT ON PATENTS AND PUBLIC HEALTH The decision of the General Council of 6 December 2005 on the amendment of the TRIPS Agreement makes the flexibilities contained in the 2003 decision on patents and public health permanent. This in effect will lead to the first amendment of a core WTO Agreement. 2. UK CHANCELLOR ANNOUNCES INTELLECTUAL PROPERTY REVIEW 2 As part of his Pre-Budget Report Package, the Chancellor of the Exchequer, Gordon Brown, has announced the launch of an independent review of intellectual property in the UK, to be headed by the former editor of the Financial Times. COPYRIGHT 3. SONY BMG’S ANTI-PIRACY SOFTWARE IN BIG TROUBLE 3 Sony BMG’s trouble started immediately following Windows programming expert Mark Russinovich's discovery that Sony’s anti- piracy software used virus-like techniques to stop illegal copies being made. There have been several class action lawsuits launched against both Sony BMG and First4Internet. Widespread pressure has made Sony BMG take actions to settle the dispute. 4. EVALUATION OF EU RULES ON DATABASES 4 The European Commission has published an evaluation of the protection EU law gives to databases. -

UNITED STATES COPYRIGHT OFFICE Exemption to Prohibition
UNITED STATES COPYRIGHT OFFICE Exemption to Prohibition on Circumvention of Copyright Protection Systems for Access Control Technologies Docket No. RM 2008-8 JOINT COMMENTS of AAP: ASSOCIATION OF AMERICAN PUBLISHERS ASMP: AMERICAN SOCIETY OF MEDIA PHOTOGRAPHERS AVA: ALLIANCE OF VISUAL ARTISTS BSA: BUSINESS SOFTWARE ALLIANCE DGA: DIRECTORS GUILD OF AMERICA ESA: ENTERTAINMENT SOFTWARE ASSOCIATION MPAA: MOTION PICTURE ASSOCIATION OF AMERICA PACA: PICTURE ARCHIVE COUNCIL OF AMERICA RIAA: RECORDING INDUSTRY ASSOCIATION OF AMERICA Steven J. Metalitz February 2, 2009 J. Matthew Williams Mitchell Silberberg & Knupp LLP 1818 N Street, NW, 8th Floor Washington, DC 20036 Tel: (202) 355-7902; Fax: (202) 355-7899 Email: [email protected] Of Counsel to AAP, ASMP, AVA, BSA, ESA, MPAA, PACA, and RIAA David Korduner General Counsel Directors Guild of America, Inc. 7920 Sunset Blvd. Los Angeles, CA 90046 Tel: (310) 289-2015; Fax: (310) 289-2031 Email: [email protected] Of Counsel to DGA 2109747.2 Comments of Joint Creators and Copyright Owners February 2, 2009 JOINT CREATORS AND COPYRIGHT OWNERS COMMENTS CONTENTS Page I. Introduction and Summary.............................................................................................. 1 II. Ground Rules Issues ....................................................................................................... 6 III. The Digital Cornucopia – How Widespread Use of Access Controls Has Led to Increased Access to Copyrighted Works...................................................................................... -

DRM — “Digital Rights” Or “Digital Restrictions” Management?
DIGITAL RIGHTS MANAGEMENT DRM — “digital rights” or “digital restrictions” management? Richard Leeming Red Bee Media If correctly applied, DRM can be likened to a motorway, providing a seamless high- speed route to content, enabling people to get the content they want, where they want it, quickly and easily. However, if badly applied, heavy handed and overly restrictive, DRM is more like a traffic jam – denying people access to the content they want and crucially denying rights-holders the revenue they want. This article looks at some of the proprietary DRM systems currently available and argues that we need to start thinking hard about when and how we apply DRM to our precious content. In 2006, music lovers worldwide have been celebrating the 250th anniversary of Mozart’s birth. Although he only lived for 35 years, Mozart composed more than 600 pieces of classical music – most of which are still hugely popular today. But it’s perhaps something of a surprise to discover that one of the key moments of Mozart’s early career would today count as piracy and be prevented by digital-rights technology. As a 14-year-old, Mozart travelled to the Vatican and heard Gregorio Allegri’s Miserere. This piece of music had long been closely guarded by the Vatican and it was forbidden to transcribe it: if you did, you would be excommunicated. Whether Mozart knew this is unknown but, having heard it once, he transcribed it from memory and it became published in London, thus breaking the Vatican’s ban. This is perhaps one of the earliest-known examples of content rights management being overturned. -

Is Copyright Appropriately Equipped to Handle Videogames? an Evaluation of the European Legal Framework for the Protection of Creative Works in Video-Games
Department of Law Spring Term 2018 Master Thesis (LL.M.) in Intellectual Property Law (2JE660) 30 ECTS “Pwnership”: Is copyright appropriately equipped to handle videogames? An evaluation of the European legal framework for the protection of creative works in video-games. Author: James Russell Supervisor: Kacper Szkalej Contents 0. Introduction ................................................................................................................................................ 3 0.1 Context ................................................................................................................................................... 3 0.2 Regulatory Framework .................................................................................................................... 4 0.3 Research Question and Objectives .............................................................................................. 4 0.4 Structure ................................................................................................................................................ 5 0.5 Limitations ............................................................................................................................................ 6 0.6 Methodology ........................................................................................................................................ 7 1. COMBO: should video-games be treated as greater than the sum of their parts? ...... 9 1.0 What do we mean by “parts”? A Taxonomy of Videogames ....................................... -

The Affects of Open Source Software Licenses on Business Software
Project Number: 48-KJR-COP5 The Affects of Open Source Software Licenses on Business Software An Interactive Qualifying Report Submitted to the Faculty of the Worcester Polytechnic Institute in partial fulfillment of the requirements for the Degree of Bachelor Science by Devin Kelly Greg Holtorf Date: March 6, 2009 Professor Kent J. Rissmiller, Advisor 1 1 Abstract This project investigates open and closed source licenses and how each style of license changes the way business is done. We look at: license violations and consider techniques for reducing violations, why businesses use closed source and open source licenses, and the intellectual property rights businesses and individuals have in open source licenses. We show that open licenses are easier to enforce, but require a different business model and show how piracy can be effectively reduced. 2 Contents 1 Abstract 2 2 Introduction 4 3 Background 5 3.1 OpenSource ...................................... 12 4 Software License Enforceability 21 4.1 ClosedSource.................................... 24 4.2 OpenSource ...................................... 28 5 License Restrictiveness and Software Quality 30 5.1 ClosedSource.................................... 32 5.2 OpenSource ...................................... 34 6 Licenses and Software Usage 35 7 Source Code Ownership 39 7.1 ClosedSourceOwnership . ...... 39 7.2 OpenSourceOwnership ............................. ..... 40 7.3 Business Licenses and Open Source Ownership . ........... 41 8 Digital Rights Management as a Response to Piracy 42 8.1 The effects of Digital rights Management . ........... 42 8.2 SoftwareasaService.............................. ...... 45 8.3 ReducingPiracy .................................. 45 9 Software Piracy Rates 48 9.1 PiracyratesbycountryandIndustry. .......... 48 9.2 LicensingandPiracyRates . ....... 51 10 Open Source and Business 52 10.1 WhatBusinessesuseSoftware. ......... 52 10.2 WhereisOpenSourceSuccessful . ......... 53 10.3 CommissionedSoftware andOpenSource . -

" Who Controls the Vocabulary, Controls the Knowledge"
Acronyms from Future-Based Consultancy & Solutions "Translation" of some Business, Finance, ICDT acronyms (including several SAP ones), initialims, tech term oddities and techronyms, loaded words and buzzwords to ease the reading of courses, books, magazines and papers: see "anacronym", "ASS" and many others ... (third main version since 1997) ( www.fbc-e.com , updated & corrected twice a month. Release 02-10-2009) " Who controls the vocabulary , 6170+ controls the knowledge " George ORWELL in "1984" Instruction To ease your researches , we are inviting you to use the " search " function within the Menu " edit " Pour faciliter vos recherches, utilisez la fonction " rechercher " disponible dans le menu " Edition " Information Underligned names are identifying authors, editors and / or copyrighted applications ©, ®, ™ FBWPA Free Business White Page Available (www.fbc-e.com ) Acronym Rose salmon is related to acronyms and assimilated terms and concepts. IL / InLin Internet Lingo also called " PC talk" Intelligence Light green color is related to intelligence, business intelligence ( BI , CI ) FBC>s Yellow color is related to FBC>s concepts and methodologies (more on www.fbc-e.com ) Finance Deep blue color is related to Finance and Accounting ( FI ) Note: BOLD acronyms KM Deep green color is related to Knowledge Management ( KM ) and texts are "translated" HR & R Lemon green color is related to HR and recruitment in the list. Mobility Light blue color is related to mobile communication ( MoMo ) Security Red color is related to security and risks management ( RM ) Note : US spelling Virtual Pink color is related to virtual / virtuality ( VR ) & ampersand $$$ temporary files Feel free to copy and distribute this "computer-babble *.001 Hayes JT Fax translator" provided that it is distributed only in its 0 Day FTP server supposed to be moved within original and unmodified state with our name, address, the next 24 hours to another IP .