VSI Openvms VAX MACRO and Instruction Set Reference Manual
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
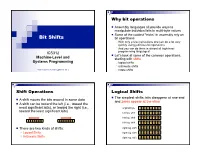
Bit Shifts Bit Operations, Logical Shifts, Arithmetic Shifts, Rotate Shifts
Why bit operations Assembly languages all provide ways to manipulate individual bits in multi-byte values Some of the coolest “tricks” in assembly rely on Bit Shifts bit operations With only a few instructions one can do a lot very quickly using judicious bit operations And you can do them in almost all high-level ICS312 programming languages! Let’s look at some of the common operations, Machine-Level and starting with shifts Systems Programming logical shifts arithmetic shifts Henri Casanova ([email protected]) rotate shifts Shift Operations Logical Shifts The simplest shifts: bits disappear at one end A shift moves the bits around in some data and zeros appear at the other A shift can be toward the left (i.e., toward the most significant bits), or toward the right (i.e., original byte 1 0 1 1 0 1 0 1 toward the least significant bits) left log. shift 0 1 1 0 1 0 1 0 left log. shift 1 1 0 1 0 1 0 0 left log. shift 1 0 1 0 1 0 0 0 There are two kinds of shifts: right log. shift 0 1 0 1 0 1 0 0 Logical Shifts right log. shift 0 0 1 0 1 0 1 0 Arithmetic Shifts right log. shift 0 0 0 1 0 1 0 1 Logical Shift Instructions Shifts and Numbers Two instructions: shl and shr The common use for shifts: quickly multiply and divide by powers of 2 One specifies by how many bits the data is shifted In decimal, for instance: multiplying 0013 by 10 amounts to doing one left shift to obtain 0130 Either by just passing a constant to the instruction multiplying by 100=102 amounts to doing two left shifts to obtain 1300 Or by using whatever -

VAX MACRO and Instruction Set Reference Manual
VAX MACRO and Instruction Set Reference Manual Order Number: AA-LA89A-TE April 1988 This document describes the features of the VAX MACRO instruction set and assembler. It includes a detailed description of MACRO directives and instructions, as well as information about MACRO source program syntax. Revision/Update Information: This manual supersedes the VAX MACRO and Instruction Set Reference Manual, Version 4.0. Software Version: VMS Version 5.0 digital equipment corporation maynard, massachusetts April 1988 The information in this document is subject to change without notice and should not be construed as a commitment by Digital Equipment Corporation. Digital Equipment Corporation assumes no responsibility for any errors that may appear in this document. The software described in this document is furnished under a license and may be used or copied only in accordance with the terms of such license. No responsibility is assumed for the use or reliability of software on equipment that is not supplied by Digital Equipment Corporation or its affiliated companies. Copyright © 1988 by Digital Equipment Corporation All Rights Reserved. Printed in U.S.A. The postpaid READER'S COMMENTS form on the last page of this document requests the user's critical evaluation to assist in preparing future documentation. The following are trademarks of Digital Equipment Corporation: DEC DIBOL UNIBUS DEC/CMS EduSystem VAX DEC/MMS IAS VAXcluster DECnet MASSBUS VMS DECsystem-10 PDP VT DECSYSTEM-20 PDT DECUS RSTS DECwriter RSX t:JD~DD5lD TM ZK4515 HOW TO ORDER ADDITIONAL DOCUMENTATION DIRECT MAIL ORDERS USA 8t PUERTO Rico* CANADA INTERNATIONAL Digital Equipment Corporation Digital Equipment Digital Equipment Corporation P.O. -

Multi-Method Dispatch Using Single-Receiver Projections
Multi-Method Dispatch Using Single-Receiver Projections Wade Holst Duane Szafron Candy Pang Yuri Leontiev g fwade,duane,candy,yuri @cs.ualberta.ca Department of Computing Science University of Alberta Edmonton, Canada Abstract A new technique for multi-method dispatch, called Single-Receiver Projections and abbre- viated SRP, is presented. It operates by performing projections onto single-receiver dispatch tables, and thus benefits from existing research into single-receiver dispatch techniques. It pro- k vides method dispatch in O(k ), where is the arity of the method. Unlike existing multi-method dispatch techniques, it also maintains the set of all applicable methods. This extra information allows SRP to support languages like CLOS that use next-method. SRP is also highly incremen- tal in nature, so it is well-suited for languages that require separate compilation and languages that allow methods and classes to be added at run-time. SRP uses less data-structure memory than all existing multi-method techniques and has the second fastest dispatch time. Furthermore, if the other techniques are extended to support all applicable methods, SRP becomes the fastest dispatch techniques. RESEARCH PAPER Subject Areas: language design and implementation, programming environments Keywords: multi-method, dispatch, object-oriented, implementation, compiler Word Count: 8722 Contact Author: Duane Szafron Department of Computing Science University of Alberta Edmonton, Canada, T6G 2H1 Phone: (780) 492-5468 Fax: (780) 492-1071 Email: [email protected] 1 1 Introduction In object-oriented languages, the method to invoke is determined not only by the method (selector) name, but also by the dynamic types of its arguments. -

MIPS SDE 6.X Programmers' Guide
TECHNOLOGIES MIPS® SDE 6.x Programmers’ Guide Document Number: MD00428 Revision 1.17 April 4, 2007 MIPS Technologies, Inc 1225 Charleston Road Mountain View,CA94043-1353 Copyright © 1995-2007 MIPS Technologies, Inc. All rights reserved. Copyright © 1995-2007 MIPS Technologies, Inc. All rights reserved. Unpublished rights (if any) reserved under the copyright laws of the United States of America and other countries. This document contains information that is proprietary to MIPS Technologies, Inc. (‘‘MIPS Technologies’’). Any copying, reproducing, modifying or use of this information (in whole or in part) that is not expressly permitted in writing by MIPS Technologies or an authorized third party is strictly prohibited. At a minimum, this information is protected under unfair competition and copyright laws. Violations thereof may result in criminal penalties and fines. Anydocument provided in source format (i.e., in a modifiable form such as in FrameMaker or Microsoft Word format) is subject to use and distribution restrictions that are independent of and supplemental to anyand all confidentiality restrictions. UNDER NO CIRCUMSTANCES MAYADOCUMENT PROVIDED IN SOURCE FORMATBEDISTRIBUTED TOATHIRD PARTY IN SOURCE FORMATWITHOUT THE EXPRESS WRITTEN PERMISSION OF MIPS TECHNOLOGIES, INC. MIPS Technologies reserves the right to change the information contained in this document to improve function, design or otherwise. MIPS Technologies does not assume anyliability arising out of the application or use of this information, or of anyerror or omission in such information. Anywarranties, whether express, statutory,implied or otherwise, including but not limited to the implied warranties of merchantability or fitness for a particular purpose, are excluded. Except as expressly provided in anywritten license agreement from MIPS Technologies or an authorized third party,the furnishing of this document does not give recipient anylicense to anyintellectual property rights, including anypatent rights, that coverthe information in this document. -

A Cross-Platform Programmer's Calculator
– Independent Work Report Fall, 2015 – A Cross-Platform Programmer’s Calculator Brian Rosenfeld Advisor: Robert Dondero Abstract This paper details the development of the first cross-platform programmer’s calculator. As users of programmer’s calculators, we wanted to address limitations of existing, platform-specific options in order to make a new, better calculator for us and others. And rather than develop for only one- platform, we wanted to make an application that could run on multiple ones, maximizing its reach and utility. From the start, we emphasized software-engineering and human-computer-interaction best practices, prioritizing portability, robustness, and usability. In this paper, we explain the decision to build a Google Chrome Application and illustrate how using the developer-preview Chrome Apps for Mobile Toolchain enabled us to build an application that could also run as native iOS and Android applications [18]. We discuss how we achieved support of signed and unsigned 8, 16, 32, and 64-bit integral types in JavaScript, a language with only one numerical type [15], and we demonstrate how we adapted the user interface for different devices. Lastly, we describe our usability testing and explain how we addressed learnability concerns in a second version. The end result is a user-friendly and versatile calculator that offers value to programmers, students, and educators alike. 1. Introduction This project originated from a conversation with Dr. Dondero in which I expressed an interest in software engineering, and he mentioned a need for a good programmer’s calculator. Dr. Dondero uses a programmer’s calculator while teaching Introduction to Programming Systems at Princeton (COS 217), and he had found that the pre-installed Mac OS X calculator did not handle all of his use cases. -
VAX VMS at 20
1977–1997... and beyond Nothing Stops It! Of all the winning attributes of the OpenVMS operating system, perhaps its key success factor is its evolutionary spirit. Some would say OpenVMS was revolutionary. But I would prefer to call it evolutionary because its transition has been peaceful and constructive. Over a 20-year period, OpenVMS has experienced evolution in five arenas. First, it evolved from a system running on some 20 printed circuit boards to a single chip. Second, it evolved from being proprietary to open. Third, it evolved from running on CISC-based VAX to RISC-based Alpha systems. Fourth, VMS evolved from being primarily a technical oper- ating system, to a commercial operat- ing system, to a high availability mission-critical commercial operating system. And fifth, VMS evolved from time-sharing to a workstation environment, to a client/server computing style environment. The hardware has experienced a similar evolution. Just as the 16-bit PDP systems laid the groundwork for the VAX platform, VAX laid the groundwork for Alpha—the industry’s leading 64-bit systems. While the platforms have grown and changed, the success continues. Today, OpenVMS is the most flexible and adaptable operating system on the planet. What start- ed out as the concept of ‘Starlet’ in 1975 is moving into ‘Galaxy’ for the 21st century. And like the universe, there is no end in sight. —Jesse Lipcon Vice President of UNIX and OpenVMS Systems Business Unit TABLE OF CONTENTS CHAPTER I Changing the Face of Computing 4 CHAPTER II Setting the Stage 6 CHAPTER -
Readthedocs-Breathe Documentation Release 1.0.0
ReadTheDocs-Breathe Documentation Release 1.0.0 Thomas Edvalson Feb 06, 2019 Contents 1 Going to 11: Amping Up the Programming-Language Run-Time Foundation3 2 Solid Compilation Foundation and Language Support5 2.1 Quick Start Guide............................................5 2.1.1 Current Release Notes.....................................5 2.1.2 Installation Guide........................................5 2.1.3 Programming Guide......................................6 2.1.4 ROCm GPU Tunning Guides..................................7 2.1.5 GCN ISA Manuals.......................................7 2.1.6 ROCm API References.....................................7 2.1.7 ROCm Tools..........................................8 2.1.8 ROCm Libraries........................................9 2.1.9 ROCm Compiler SDK..................................... 10 2.1.10 ROCm System Management.................................. 10 2.1.11 ROCm Virtualization & Containers.............................. 10 2.1.12 Remote Device Programming................................. 11 2.1.13 Deep Learning on ROCm.................................... 11 2.1.14 System Level Debug...................................... 11 2.1.15 Tutorial............................................. 11 2.1.16 ROCm Glossary......................................... 12 2.2 Current Release Notes.......................................... 12 2.2.1 New features and enhancements in ROCm 2.1......................... 12 2.2.1.1 RocTracer v1.0 preview release – ‘rocprof’ HSA runtime tracing and statistics sup- port -

Bitwise Operators
Logical operations ANDORNOTXORAND,OR,NOT,XOR •Loggpical operations are the o perations that have its result as a true or false. • The logical operations can be: • Unary operations that has only one operand (NOT) • ex. NOT operand • Binary operations that has two operands (AND,OR,XOR) • ex. operand 1 AND operand 2 operand 1 OR operand 2 operand 1 XOR operand 2 1 Dr.AbuArqoub Logical operations ANDORNOTXORAND,OR,NOT,XOR • Operands of logical operations can be: - operands that have values true or false - operands that have binary digits 0 or 1. (in this case the operations called bitwise operations). • In computer programming ,a bitwise operation operates on one or two bit patterns or binary numerals at the level of their individual bits. 2 Dr.AbuArqoub Truth tables • The following tables (truth tables ) that shows the result of logical operations that operates on values true, false. x y Z=x AND y x y Z=x OR y F F F F F F F T F F T T T F F T F T T T T T T T x y Z=x XOR y x NOT X F F F F T F T T T F T F T T T F 3 Dr.AbuArqoub Bitwise Operations • In computer programming ,a bitwise operation operates on one or two bit patterns or binary numerals at the level of their individual bits. • Bitwise operators • NOT • The bitwise NOT, or complement, is an unary operation that performs logical negation on each bit, forming the ones' complement of the given binary value. -
Bits, Bytes, and Integers Today: Bits, Bytes, and Integers
Bits, Bytes, and Integers Today: Bits, Bytes, and Integers Representing information as bits Bit-level manipulations Integers . Representation: unsigned and signed . Conversion, casting . Expanding, truncating . Addition, negation, multiplication, shifting . Summary Representations in memory, pointers, strings Everything is bits Each bit is 0 or 1 By encoding/interpreting sets of bits in various ways . Computers determine what to do (instructions) . … and represent and manipulate numbers, sets, strings, etc… Why bits? Electronic Implementation . Easy to store with bistable elements . Reliably transmitted on noisy and inaccurate wires 0 1 0 1.1V 0.9V 0.2V 0.0V For example, can count in binary Base 2 Number Representation . Represent 1521310 as 111011011011012 . Represent 1.2010 as 1.0011001100110011[0011]…2 4 13 . Represent 1.5213 X 10 as 1.11011011011012 X 2 Encoding Byte Values Byte = 8 bits . Binary 000000002 to 111111112 0 0 0000 . Decimal: 010 to 25510 1 1 0001 2 2 0010 . Hexadecimal 0016 to FF16 3 3 0011 . 4 4 0100 Base 16 number representation 5 5 0101 . Use characters ‘0’ to ‘9’ and ‘A’ to ‘F’ 6 6 0110 7 7 0111 . Write FA1D37B16 in C as 8 8 1000 – 0xFA1D37B 9 9 1001 A 10 1010 – 0xfa1d37b B 11 1011 C 12 1100 D 13 1101 E 14 1110 F 15 1111 Example Data Representations C Data Type Typical 32-bit Typical 64-bit x86-64 char 1 1 1 short 2 2 2 int 4 4 4 long 4 8 8 float 4 4 4 double 8 8 8 long double − − 10/16 pointer 4 8 8 Today: Bits, Bytes, and Integers Representing information as bits Bit-level manipulations Integers . -
Integer Arithmetic and Undefined Behavior in C Brad Karp UCL Computer Science
Carnegie Mellon Integer Arithmetic and Undefined Behavior in C Brad Karp UCL Computer Science CS 3007 23rd January 2018 (lecture notes derived from material from Eddie Kohler, John Regehr, Phil Gibbons, Randy Bryant, and Dave O’Hallaron) 1 Carnegie Mellon Outline: Integer Arithmetic and Undefined Behavior in C ¢ C primitive data types ¢ C integer arithmetic § Unsigned and signed (two’s complement) representations § Maximum and minimum values; conversions and casts § Perils of C integer arithmetic, unsigned and especially signed ¢ Undefined behavior (UB) in C § As defined in the C99 language standard § Consequences for program behavior § Consequences for compiler and optimizer behavior § Examples § Prevalence of UB in real-world Linux application-level code ¢ Recommendations for defensive programming in C 2 Carnegie Mellon Example Data Representations C Data Type Typical 32-bit Typical 64-bit x86-64 char 1 1 1 signed short (default) 2 2 2 and int 4 4 4 unsigned variants long 4 8 8 float 4 4 4 double 8 8 8 pointer 4 8 8 3 Carnegie Mellon Portable C types with Fixed Sizes C Data Type all archs {u}int8_t 1 {u}int16_t 2 {u}int32_t 4 {u}int64_t 8 uintptr_t 4 or 8 Type definitions available in #include <stdint.h> 4 Carnegie Mellon Shift Operations ¢ Left Shift: x << y Argument x 01100010 § Shift bit-vector x left y positions << 3 00010000 – Throw away extra bits on left Log. >> 2 00011000 § Fill with 0’s on right Arith. >> 2 00011000 ¢ Right Shift: x >> y § Shift bit-vector x right y positions Argument 10100010 § Throw away extra bits on right x § Logical shift << 3 00010000 § Fill with 0’s on left Log. -

Kernel Boot Process Kernel Booting Process. Part 1
Kernel Boot Process This chapter describes the linux kernel boot process. Here you will see a series of posts which describes the full cycle of the kernel loading process: • From the bootloader to kernel - describes all stages from turning on the computer to running the first instruction of the kernel. • First steps in the kernel setup code - describes first steps in the kernel setup code. You will see heap initialization, query of different parameters like EDD, IST and etc. • Video mode initialization and transition to protected mode - describes video mode initialization in the kernel setup code and transition to protected mode. • Transition to 64-bit mode - describes preparation for transition into 64-bit mode and details of transition. • Kernel Decompression - describes preparation before kernel decompression and details of direct decompression. • Kernel random address randomization - describes randomization of the Linux kernel load address. Kernel booting process. Part 1. From the bootloader to the kernel If you have been reading my previous blog posts, then you can see that, for some time now, I have been starting to get involved with low-level programming. I have written some posts about assembly programming for x86_64 Linux and, at the same time, I have also started to dive into the Linux kernel source code. I have a great interest in understanding how low-level things work, how programs run on my computer, how they are located in memory, how the kernel manages processes and memory, how the network stack works at a low level, and many many other things. So, I have decided to write yet another series of posts about the Linux kernel for the x86_64 architecture. -

Episode 7.03 – Coding Bitwise Operations
Episode 7.03 – Coding Bitwise Operations Welcome to the Geek Author series on Computer Organization and Design Fundamentals. I’m David Tarnoff, and in this series, we are working our way through the topics of Computer Organization, Computer Architecture, Digital Design, and Embedded System Design. If you’re interested in the inner workings of a computer, then you’re in the right place. The only background you’ll need for this series is an understanding of integer math, and if possible, a little experience with a programming language such as Java. And one more thing. This episode has direct consequences for our code. You can find coding examples on the episode worksheet, a link to which can be found on the transcript page at intermation.com. Way back in Episode 2.2 – Unsigned Binary Conversion, we introduced three operators that allow us to manipulate integers at the bit level: the logical shift left (represented with two adjacent less-than operators, <<), the arithmetic shift right (represented with two adjacent greater-than operators, >>), and the logical shift right (represented with three adjacent greater-than operators, >>>). These special operators allow us to take all of the bits in a binary integer and move them left or right by a specified number of bit positions. The syntax of all three of these operators is to place the integer we wish to shift on the left side of the operator and the number of bits we wish to shift it by on the right side of the operator. In that episode, we introduced these operators to show how bit shifts could take the place of multiplication or division by powers of two.