Data Breach Reports
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Event Transcript
The Walt Disney Company Q2 FY11 Earnings Conference Call MAY 10, 2011 Disney Speakers: Bob Iger President and Chief Executive Officer Jay Rasulo Senior Executive Vice President and Chief Financial Officer Moderated by, Lowell Singer Senior Vice President, Investor Relations PRESENTATION Operator Good day, ladies and gentlemen, and welcome to the second-quarter 2011 Walt Disney Company earnings conference call. My name is Stacy and I will be your conference moderator for today. At this time, all participants are in a listen-only mode. We will conduct a question- and-answer session towards the end of the conference. (Operator Instructions). As a reminder, this conference call is being recorded for replay purposes. Page 1 The Walt Disney Company Q2 FY11 Earnings May 10, 2011 Conference Call I would now like to turn the presentation over to your host for today, to Mr. Lowell Singer, Senior Vice President of Investor Relations. Please proceed. Lowell Singer – Senior Vice President, Investor Relations, The Walt Disney Company Okay. Thank you, and good afternoon, everyone. Welcome to The Walt Disney Company's second quarter earnings call. Our press release was issued almost an hour ago. It's now available on our website at www.Disney.com/investors. Today's call is also being webcast and the webcast will be on the website after the call. Finally, a replay and transcript of today's remarks will be available on the website as well. Joining me in Burbank for today's call are Bob Iger, Disney's President and Chief Executive Officer, and Jay Rasulo, Senior Executive Vice President and Chief Financial Officer. -

Innovation and Investment: Building Tomorrow’S Economy in the Bay Area
Innovation and Investment: Building Tomorrow’s Economy in the Bay Area Bay Area Economic Profile March 2012 Eighth in a Series Bay Area Council Economic Institute 201 California Street, Suite 1450, San Francisco, CA 94111 (415) 981-7117 Fax (415) 981-6408 www.bayareaeconomy.org [email protected] Innovation and Investment: Building Tomorrow’s Economy in the Bay Area Bay Area Economic Profile March 2012 Eighth in a Series Innovation and Investment: Building Tomorrow’s Economy in the Bay Area Introduction This report, the eighth in a series of biennial Bay Area Economic Profile reports produced by the Bay Area Council Economic Institute in partnership with McKinsey & Company, examines the evolution of the Bay Area’s econ- omy in the wake of the Great Recession that severely impacted the region from 2008 to 2010 and continues to be felt by many of our citizens and busi- nesses. As previous profile reports have done, it benchmarks the Bay Area’s economic performance against other knowledge-based economies in the United States and around the world, to assess the region’s national and global competitiveness. It also analyzes the economic and policy challenges that continue to confront the region and that must be addressed if the Bay Area wishes to maintain its current position of economic leadership. This year’s Bay Area Economic Profile report finds, as it has so often in the past, that the region has experienced a substantial economic recovery and remarkable economic growth based on its ability to innovate across a range of leading sectors. This strength in innovation continues to position it fa- vorably as both a partner and a competitor with leading economic regions throughout the world. -

A Closer Look at Third-Party OSN Applications: Are They Leaking Your Personal Information? Abdelberi Chaabane, Yuan Ding, Ratan Dey, Mohamed Ali Kaafar, Keith Ross
A Closer Look at Third-Party OSN Applications: Are They Leaking Your Personal Information? Abdelberi Chaabane, Yuan Ding, Ratan Dey, Mohamed Ali Kaafar, Keith Ross To cite this version: Abdelberi Chaabane, Yuan Ding, Ratan Dey, Mohamed Ali Kaafar, Keith Ross. A Closer Look at Third-Party OSN Applications: Are They Leaking Your Personal Information?. PAM 2014 - 15th International Conference on Passive and Active Measurement, Mar 2014, Los Angeles, United States. hal-00939175 HAL Id: hal-00939175 https://hal.inria.fr/hal-00939175 Submitted on 30 Jan 2014 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. A Closer Look at Third-Party OSN Applications: Are They Leaking Your Personal Information? Abdelberi Chaabane1, Yuan Ding2, Ratan Dey2, Mohamed Ali Kaafar1;3, Keith W. Ross2 1INRIA, France 2 Polytechnic Institute of NYU, USA 3 NICTA, Australia Abstract. We examine third-party Online Social Network (OSN) applica- tions for two major OSNs: Facebook and RenRen. These third-party applica- tions typically gather, from the OSN, user personal information. We develop a measurement platform to study the interaction between OSN applications and fourth parties. We use this platform to study the behavior of 997 Face- book applications and 377 RenRen applications. -

The Impact of Corporate Newsroom Culture on News Workers & Community Reporting
Portland State University PDXScholar Dissertations and Theses Dissertations and Theses Spring 6-5-2018 News Work: the Impact of Corporate Newsroom Culture on News Workers & Community Reporting Carey Lynne Higgins-Dobney Portland State University Follow this and additional works at: https://pdxscholar.library.pdx.edu/open_access_etds Part of the Broadcast and Video Studies Commons, Journalism Studies Commons, and the Mass Communication Commons Let us know how access to this document benefits ou.y Recommended Citation Higgins-Dobney, Carey Lynne, "News Work: the Impact of Corporate Newsroom Culture on News Workers & Community Reporting" (2018). Dissertations and Theses. Paper 4410. https://doi.org/10.15760/etd.6307 This Dissertation is brought to you for free and open access. It has been accepted for inclusion in Dissertations and Theses by an authorized administrator of PDXScholar. Please contact us if we can make this document more accessible: [email protected]. News Work: The Impact of Corporate Newsroom Culture on News Workers & Community Reporting by Carey Lynne Higgins-Dobney A dissertation submitted in partial fulfillment of the requirements for the degree of Doctor of Philosophy in Urban Studies Dissertation Committee: Gerald Sussman, Chair Greg Schrock Priya Kapoor José Padín Portland State University 2018 © 2018 Carey Lynne Higgins-Dobney News Work i Abstract By virtue of their broadcast licenses, local television stations in the United States are bound to serve in the public interest of their community audiences. As federal regulations of those stations loosen and fewer owners increase their holdings across the country, however, local community needs are subjugated by corporate fiduciary responsibilities. Business practices reveal rampant consolidation of ownership, newsroom job description convergence, skilled human labor replaced by computer automation, and economically-driven downsizings, all in the name of profit. -
Spring Special 2017
www.newsandtech.com www.newsandtech.com Spring SPECIAL ISSUE 2017 The premier resource for insight, analysis and technology integration in newspaper, magazine, digital and hybrid production. ALEXA WHAT’S THE DAY’S NEWS? ALEXA WHAT’S AI? ALEXA WHAT’S OTT? ALEXA WHAT’S VR? Turn to page 37 for expanded industry coverage u 1 www.newsandtech.com — Let’s write the future with retrofit solutions that give your press another ten years of life. ABB’s retrofit solutions for newspaper presses will extend the productive life of your press, improve print quality, reduce waste and improve effi- ciency – for a fraction of the cost of a new press. Worried about the availability of spare parts for your existing controls? With an ABB retrofit you know that spares will be available worldwide for 10 to 15 years. Whether you are looking for replacement drives, new controls or a complete press reconfiguration, ABB has the right solution for you. The future of your printing business lies with ABB. abb.com/printing 2 t Spring SPECIAL ISSUE 2017 News & Tech www.newsandtech.com WSJ partners with Google, experiments with VR u BY KIRSTEN STAPLES CONTRIBUTING WRITER The Wall Street Journal is using new Photos: Courtesy of WSJ the power to put the viewer into the story technology to find better ways to connect like VR. By doing this you can literally cre- with readers using their virtual reality app ate empathy on a level that was previously on Google Daydream. This collaboration impossible.” with Google allows WSJ readers to experi- Readers can tune in to 360-video by ence 360-degree video news. -

Interactive Entertainment and Internet Segments Are Converging, Entertainment Shifting the Landscape of the Traditional Video Game Market
North America TMT Internet FITT Research Company Company 31 October 2010 Fundamental, Industry, Thematic, Thought Leading Deutsche Bank’s Research Product Interactive Committee has deemed this work F.I.T.T. for investors seeking differentiated ideas. The Interactive Entertainment and Internet segments are converging, Entertainment shifting the landscape of the traditional video game market. Digital, social and mobile gaming are emerging as the next major drivers of the interactive gaming space in the US over the next several years. The social and massively multi- player segments should also offer an attractive opportunity for monetization of Extending Game Play to the virtual goods, one of the fastest-growing segments in the space. Masses... beyond the console Fundamental: Growth Driven by Penetration of the Long Tail Global Markets Research Industry: We see Nearly a $30bn US Market Opportunity by 2014 Thematic: Digital, Social and Mobile are Key Emerging Themes Thought Leading: Adoption, Engagement, and Monetization Phases We Favor Activision Blizzard for Digital Position and Google for its Android Platform for Mobile Gaming Jeetil Patel Herman Leung Matt Chesler, CFA Research Analyst Research Analyst Research Analyst (+1) 415 617-4223 (+1) 415 617-3246 (+1) 212 250-6170 [email protected] [email protected] [email protected] Deutsche Bank Securities Inc. All prices are those current at the end of the previous trading session unless otherwise indicated. Prices are sourced from local exchanges via Reuters, Bloomberg and other vendors. Data is sourced from Deutsche Bank and subject companies. Deutsche Bank does and seeks to do business with companies covered in its research reports. -

The Video Games Industry
The video games industry: A responsible attitude towards parents and children October 2011 Executive Summary The Association for UK Interactive Entertainment (UKIE) is the trade association that represents a wide range of businesses and organisations involved in the video games industry. UKIE exists to ensure that our members have the right This document aims to set out what the video games and economic, political and social environment needed for this interactive entertainment is doing in the field of child safety. expanding industry to continue to thrive. UKIE’s membership The focus of this report is the following games consoles: includes games publishers, developers and the academic Nintendo Wii, Nintendo DS, Microsoft Xbox, Sony2 PlayStation institutions that support the industry. We represent the and Sony Playstation Portable. majority of the UK video games industry: in 2010 UKIE members were responsible for 97% of the games sold as physical products in the UK and UKIE is the only trade body Parental Controls on video games consoles in the UK to represent all the major console manufacturers (Nintendo, Microsoft and Sony). Tanya Byron’s Review of Progress (2010) urged internet- enabled device manufacturers to develop parental controls and include them on their devices. Similarly, the Bailey Introduction Review (2011) made the following recommendations regarding parents’ ability to block adult and age-restricted The video games and interactive entertainment industry material from the internet: is one of the fastest growing creative industries in the UK. With 1 in 3 people identifying as “gamers”, interactive “the internet industry must act decisively to develop entertainment is increasingly part of everyone’s everyday and introduce effective parental controls.” lives. -
Broadcast Actions 7/23/2014
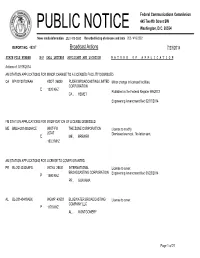
Federal Communications Commission 445 Twelfth Street SW PUBLIC NOTICE Washington, D.C. 20554 News media information 202 / 418-0500 Recorded listing of releases and texts 202 / 418-2222 REPORT NO. 48287 Broadcast Actions 7/23/2014 STATE FILE NUMBER E/P CALL LETTERS APPLICANT AND LOCATION N A T U R E O F A P P L I C A T I O N Actions of: 07/18/2014 AM STATION APPLICATIONS FOR MINOR CHANGE TO A LICENSED FACILITY DISMISSED CA BP-20130702AAA KSDT 36830 RUDEX BROADCASTING LIMITED Minor change in licensed facilities. CORPORATION E 1320 KHZ Published in the Federal Register 9/9/2013 CA , HEMET Engineering Amendment filed 02/07/2014 FM STATION APPLICATIONS FOR MODIFICATION OF LICENSE DISMISSED ME BMLH-20140529ACE WKIT-FM THE ZONE CORPORATION License to modify. 25747 Dismissed as moot. No letter sent. E ME ,BREWER 100.3 MHZ AM STATION APPLICATIONS FOR LICENSE TO COVER GRANTED PR BL-20140326AFG WGYA 25531 INTERNATIONAL License to cover. BROADCASTING CORPORATION Engineering Amendment filed 06/23/2014 P 1590 KHZ PR , GUAYAMA AL BL-20140418ABX WGMP 43633 BLUEWATER BROADCASTING License to cover. COMPANY LLC P 1170 KHZ AL , MONTGOMERY Page 1 of 21 Federal Communications Commission 445 Twelfth Street SW PUBLIC NOTICE Washington, D.C. 20554 News media information 202 / 418-0500 Recorded listing of releases and texts 202 / 418-2222 REPORT NO. 48287 Broadcast Actions 7/23/2014 STATE FILE NUMBER E/P CALL LETTERS APPLICANT AND LOCATION N A T U R E O F A P P L I C A T I O N Actions of: 07/18/2014 AM STATION APPLICATIONS FOR MODIFICATION OF LICENSE GRANTED MN BML-20131205BBX KOLM 50288 TOWNSQUARE MEDIA License to modify. -

The Walt Disney Company: a Corporate Strategy Analysis
The Walt Disney Company: A Corporate Strategy Analysis November 2012 Written by Carlos Carillo, Jeremy Crumley, Kendree Thieringer and Jeffrey S. Harrison at the Robins School of Business, University of Richmond. Copyright © Jeffrey S. Harrison. This case was written for the purpose of classroom discussion. It is not to be duplicated or cited in any form without the copyright holder’s express permission. For permission to reproduce or cite this case, contact Jeff Harrison at [email protected]. In your message, state your name, affiliation and the intended use of the case. Permission for classroom use will be granted free of charge. Other cases are available at: http://robins.richmond.edu/centers/case-network.html "Walt was never afraid to dream. That song from Pinocchio, 'When You Wish Upon a Star,' is the perfect summary of Walt's approach to life: dream big dreams, even hopelessly impossible dreams, because they really can come true. Sure, it takes work, focus and perseverance. But anything is possible. Walt proved it with the impossible things he accomplished."1 It is well documented that Walt Disney had big dreams and made several large gambles to propel his visions. From the creation of Steamboat Willie in 1928 to the first color feature film, “Snow White and the Seven Dwarves” in 1937, and the creation of Disneyland in Anaheim, CA during the 1950’s, Disney risked his personal assets as well as his studio to build a reality from his dreams. While Walt Disney passed away in the mid 1960’s, his quote, “If you can dream it, you can do it,”2 still resonates in the corporate world and operations of The Walt Disney Company. -

Apiw / Privacy Panel =
EVERYONE’S NIGHTMARE PRIVACY AND DATA BREACH RISKS MAY 2014 EDITION This edition is updated as of May 2014. To obtain a copy of this edition by email or to be placed on the mailing list for future editions, please email [email protected]. To learn more about our firm, or our Privacy and Data Protection Practice, please visit edwardswildman.com. BOSTON ♦ CHICAGO ♦ HARTFORD ♦ HONG KONG ♦ ISTANBUL ♦ LONDON ♦ LOS ANGELES ♦ MIAMI ♦ MORRISTOWN NEW YORK ♦ ORANGE COUNTY ♦ PROVIDENCE ♦ STAMFORD ♦ TOKYO ♦ WASHINGTON DC ♦ WEST PALM BEACH This white paper is for guidance only and is not intended to be a substitute for specific legal advice. If you would like further information, please contact the Edwards Wildman Palmer LLP lawyer responsible for your matters. This white paper is published by Edwards Wildman Palmer for the benefit of clients, friends and fellow professionals on matters of interest. The information contained herein is not to be construed as legal advice or opinion. We provide such advice or opinion only after being engaged to do so with respect to particular facts and circumstances. The firm is not authorized under the UK Financial Services and Markets Act 2000 to offer UK investment services to clients. In certain circumstances, as members of the Law Society of England and Wales, we are able to provide these investment services if they are an incidental part of the professional services we have been engaged to provide. Please note that your contact details, which may have been used to provide this bulletin to you, will be used for communications with you only. -

Disney Interactive
Terms of Use Last Updated: July 10, 2014 Disney Interactive is pleased to provide to you its sites, software, applications, content, products and services (“Disney Services”), which may be branded Disney, ABC, ESPN, Marvel, Lucasfilm, Club Penguin, Playdom or another brand owned or licensed by The Walt Disney Company. These terms govern your use and our provision of the Disney Services on which these terms are posted, as well as Disney Services we make available on third-party sites and platforms if these terms are disclosed to you in connection with your use of the Disney Services. PLEASE READ THESE TERMS CAREFULLY BEFORE USING THE DISNEY SERVICES. ANY DISPUTE BETWEEN YOU AND US MUST BE RESOLVED BY INDIVIDUAL BINDING ARBITRATION. PLEASE READ THE ARBITRATION PROVISION IN THESE TERMS AS IT AFFECTS YOUR RIGHTS UNDER THIS CONTRACT. NOTHING IN THESE TERMS IS INTENDED TO AFFECT YOUR RIGHTS UNDER THE LAW IN YOUR USUAL PLACE OF RESIDENCE. IF THERE IS A CONFLICT BETWEEN THOSE RIGHTS AND THESE TERMS, YOUR RIGHTS UNDER APPLICABLE LOCAL LAW WILL PREVAIL. 1. Contract between You and Us This is a contract between you and Disney Interactive, a California corporation located at 500 South Buena Vista Street, Burbank, California 91521, USA, or between you and any different service provider identified for a particular Disney Service. You must read and agree to these terms before using the Disney Services. If you do not agree, you may not use the Disney Services. These terms describe the limited basis on which the Disney Services are available and supersede prior agreements or arrangements. -

Make Hunger History Awards
Second harvest food Bank of SANTA CLARA and SAN Mateo CouNTieS Make Hunger History Awards Celebrating your efforts to end local hunger welcoMe PRogRAM Welcome to Second Harvest Food Bank’s Second HarveSt Food Bank’S Make Hunger History Awards! 22nd recognition event Although the reasons for hunger are complicated, feeding a Annual family in need is not. Because of your help and generosity, last year we were able to provide 41 million meals to children, seniors and hard-working adults who had nowhere else to turn. We served nearly a quarter of a million people every month last year. Make Hunger History it’s staggering to know that one in every 10 people in Silicon Valley and on the Peninsula received at least some of their food from the Food Bank. Awards Nationally, 70 billion pounds of food is wasted every year, far more than is needed by the 49 million people who struggle with tHurSday, april 4, 2013 hunger. You don’t have to be a “numbers person” to figure out 6:00 pm that there is enough food available to COCKTAIL reception feed our hungry neighbors. Hunger is a solvable problem. 7:00 pm AWARDS program The solution to hunger is connectivity. we are striving to make hunger history by Kathy Jackson, Ceo, Second Harvest Food Bank supplementing our highly efficient physical distribution of food by adopting new technology, orchestrating win-win collaborations and connecting more people to 2012 Holiday Food & Fund drive c o-cHairS: food that would otherwise be wasted. Tonight we’ll even meet Kate to see how the Dan Campbell, Coo, Backup and Recovery Systems, eMC Corporation Food Bank is connecting local families with the food they need to thrive.