Code Breaking in the Pacific
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

How I Learned to Stop Worrying and Love the Bombe: Machine Research and Development and Bletchley Park
View metadata, citation and similar papers at core.ac.uk brought to you by CORE provided by CURVE/open How I learned to stop worrying and love the Bombe: Machine Research and Development and Bletchley Park Smith, C Author post-print (accepted) deposited by Coventry University’s Repository Original citation & hyperlink: Smith, C 2014, 'How I learned to stop worrying and love the Bombe: Machine Research and Development and Bletchley Park' History of Science, vol 52, no. 2, pp. 200-222 https://dx.doi.org/10.1177/0073275314529861 DOI 10.1177/0073275314529861 ISSN 0073-2753 ESSN 1753-8564 Publisher: Sage Publications Copyright © and Moral Rights are retained by the author(s) and/ or other copyright owners. A copy can be downloaded for personal non-commercial research or study, without prior permission or charge. This item cannot be reproduced or quoted extensively from without first obtaining permission in writing from the copyright holder(s). The content must not be changed in any way or sold commercially in any format or medium without the formal permission of the copyright holders. This document is the author’s post-print version, incorporating any revisions agreed during the peer-review process. Some differences between the published version and this version may remain and you are advised to consult the published version if you wish to cite from it. Mechanising the Information War – Machine Research and Development and Bletchley Park Christopher Smith Abstract The Bombe machine was a key device in the cryptanalysis of the ciphers created by the machine system widely employed by the Axis powers during the Second World War – Enigma. -
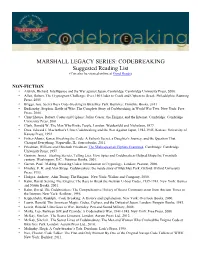
CODEBREAKING Suggested Reading List (Can Also Be Viewed Online at Good Reads)
MARSHALL LEGACY SERIES: CODEBREAKING Suggested Reading List (Can also be viewed online at Good Reads) NON-FICTION • Aldrich, Richard. Intelligence and the War against Japan. Cambridge: Cambridge University Press, 2000. • Allen, Robert. The Cryptogram Challenge: Over 150 Codes to Crack and Ciphers to Break. Philadelphia: Running Press, 2005 • Briggs, Asa. Secret Days Code-breaking in Bletchley Park. Barnsley: Frontline Books, 2011 • Budiansky, Stephen. Battle of Wits: The Complete Story of Codebreaking in World War Two. New York: Free Press, 2000. • Churchhouse, Robert. Codes and Ciphers: Julius Caesar, the Enigma, and the Internet. Cambridge: Cambridge University Press, 2001. • Clark, Ronald W. The Man Who Broke Purple. London: Weidenfeld and Nicholson, 1977. • Drea, Edward J. MacArthur's Ultra: Codebreaking and the War Against Japan, 1942-1945. Kansas: University of Kansas Press, 1992. • Fisher-Alaniz, Karen. Breaking the Code: A Father's Secret, a Daughter's Journey, and the Question That Changed Everything. Naperville, IL: Sourcebooks, 2011. • Friedman, William and Elizebeth Friedman. The Shakespearian Ciphers Examined. Cambridge: Cambridge University Press, 1957. • Gannon, James. Stealing Secrets, Telling Lies: How Spies and Codebreakers Helped Shape the Twentieth century. Washington, D.C.: Potomac Books, 2001. • Garrett, Paul. Making, Breaking Codes: Introduction to Cryptology. London: Pearson, 2000. • Hinsley, F. H. and Alan Stripp. Codebreakers: the inside story of Bletchley Park. Oxford: Oxford University Press, 1993. • Hodges, Andrew. Alan Turing: The Enigma. New York: Walker and Company, 2000. • Kahn, David. Seizing The Enigma: The Race to Break the German U-boat Codes, 1939-1943. New York: Barnes and Noble Books, 2001. • Kahn, David. The Codebreakers: The Comprehensive History of Secret Communication from Ancient Times to the Internet. -

VISIT to BLETCHLEY PARK
REPORT of STAR GROUP – VISIT to BLETCHLEY PARK It was 8-30 on the damp drizzly Monday morning of 5th October when our intrepid group of bleary-eyed third-agers left Keyworth to visit the former codebreaking and cipher centre at Bletchley Park. As we progressed south along the M1 motorway the weather started to clear and by the time we arrived in Milton Keynes the rain and drizzle had stopped. For me the first stop was a cup of coffee in the Block C Visitor Centre. We moved out of the Visitor Centre and towards the lake. We were told that many a wartime romantic coupling around this beautiful lake had led to marriage. The beautiful Bletchley Park Lake So… Moving on. We visited the Mansion House with it’s curious variety of styles of architecture. The original owners of the estate had travelled abroad extensively and each time they returned home they added an extension in the styles that they visited on their travels. The Mansion House At the Mansion we saw the sets that had been designed for the Film “The Imitation Game.” The attention to detail led one to feel that you were back there in the dark days of WWII. History of The Mansion Captain Ridley's Shooting Party The arrival of ‘Captain Ridley's Shooting Party’ at a mansion house in the Buckinghamshire countryside in late August 1938 was to set the scene for one of the most remarkable stories of World War Two. They had an air of friends enjoying a relaxed weekend together at a country house. -

9 Purple 18/2
THE CONCORD REVIEW 223 A VERY PURPLE-XING CODE Michael Cohen Groups cannot work together without communication between them. In wartime, it is critical that correspondence between the groups, or nations in the case of World War II, be concealed from the eyes of the enemy. This necessity leads nations to develop codes to hide their messages’ meanings from unwanted recipients. Among the many codes used in World War II, none has achieved a higher level of fame than Japan’s Purple code, or rather the code that Japan’s Purple machine produced. The breaking of this code helped the Allied forces to defeat their enemies in World War II in the Pacific by providing them with critical information. The code was more intricate than any other coding system invented before modern computers. Using codebreaking strategy from previous war codes, the U.S. was able to crack the Purple code. Unfortunately, the U.S. could not use its newfound knowl- edge to prevent the attack at Pearl Harbor. It took a Herculean feat of American intellect to break Purple. It was dramatically intro- duced to Congress in the Congressional hearing into the Pearl Harbor disaster.1 In the ensuing years, it was discovered that the deciphering of the Purple Code affected the course of the Pacific war in more ways than one. For instance, it turned out that before the Americans had dropped nuclear bombs on Japan, Purple Michael Cohen is a Senior at the Commonwealth School in Boston, Massachusetts, where he wrote this paper for Tom Harsanyi’s United States History course in the 2006/2007 academic year. -

LGBTQ Guam and Hospitality of the Guamanian People
An LGBTQ Guide to Guam Håfa Adai, Welcome! As Lieutenant Governor of Guam and proud member of the LGBTQ community, I am grateful that Guam’s residents have given me the opportunity to help direct the island’s future. Also, Guam has just elected its first female Governor, and now holds the record for the largest women majority in U.S. history. Guam’s diverse political leadership is a direct reflection JOSHUA TENORIO, of the broadening views within our island community. THE HONORABLE LT. GOVERNOR I will advocate for policy that is fair and equal for all and will positively impact LGBTQ rights. I applaud the Guam Visitors Bureau’s efforts in developing the Guam travel industry to better serve LGBTQ travelers and give my full support to their ongoing efforts. We look forward to your visit and providing you with the adventure of a lifetime! Si Yu’os Ma’åse’ 23 Håfa Adai! (Greetings!) Contents The Guam Visitors Bureau (GVB) finds great joy in welcoming LGBTQ travelers to our beautiful island. 02 Welcome As you read this guide, we hope that it inspires you to visit our home and experience the warmth 04 LGBTQ Guam and hospitality of the Guamanian people. 06 LGBTQ Resources 16 Guam strongly supports the LGBTQ community, paving 08 Visiting Guam PILAR LAGUAÑA, the way for equality, celebrating diversity, and promoting With Other LGBTQ PRESIDENT & CEO, inclusivity. The Bureau is a proud member of the Destinations 12 Things to do International Gay and Lesbian Travel Association (IGLTA), GUAM VISITORS 09 Guam + Japan 12 Outdoors BUREAU where we continue our efforts to be a reliable resource for, and to better serve the needs of, all of our visitors. -

Breaking Japanese Diplomatic Codes David Sissons and D Special Section During the Second World War
Breaking Japanese Diplomatic Codes David Sissons and D Special Section during the Second World War Breaking Japanese Diplomatic Codes David Sissons and D Special Section during the Second World War Edited by Desmond Ball and Keiko Tamura ASIAN STUDIES SERIES MONOGRAPH 4 Published by ANU E Press The Australian National University Canberra ACT 0200, Australia Email: [email protected] This title is also available online at http://epress.anu.edu.au National Library of Australia Cataloguing-in-Publication entry Title: Breaking Japanese diplomatic codes : David Sissons and D Special Section during the Second World War / edited by Desmond Ball and Keiko Tamura. ISBN: 9781925021073 (paperback) 9781925021080 (ebook) Subjects: Sissons, D. C. S. (David Carlisle Stanley), 1925-2006. Allied Forces. Southwest Pacific Area. Allied Intelligence Bureau World War, 1939-1945--Cryptography. World War, 1939-1945--Secret service--Australia. World War, 1939-1945--Electronic intelligence--Australia. World War, 1939-1945--Military intelligence--Australia. World War, 1939-1945--Japan. Cryptography--Australia--History. Military intelligence--Australia--History--20th century. Other Authors/Contributors: Ball, Desmond, 1947- editor. Tamura, Keiko, editor. Dewey Number: 940.548694 All rights reserved. No part of this publication may be reproduced, stored in a retrieval system or transmitted in any form or by any means, electronic, mechanical, photocopying or otherwise, without the prior permission of the publisher. Cover design and layout by ANU E Press Cover image: David Sissons about 18 years old before joining the Army in 1944. Photo courtesy of Mrs Bronwen Sissons. Printed by Griffin Press This edition © 2013 ANU E Press Contents Preface . ix Acknowledgements . xi Acronyms and Abbreviations . -

Considering the Creation of a Domestic Intelligence Agency in the United States
HOMELAND SECURITY PROGRAM and the INTELLIGENCE POLICY CENTER THE ARTS This PDF document was made available CHILD POLICY from www.rand.org as a public service of CIVIL JUSTICE the RAND Corporation. EDUCATION ENERGY AND ENVIRONMENT Jump down to document6 HEALTH AND HEALTH CARE INTERNATIONAL AFFAIRS The RAND Corporation is a nonprofit NATIONAL SECURITY research organization providing POPULATION AND AGING PUBLIC SAFETY objective analysis and effective SCIENCE AND TECHNOLOGY solutions that address the challenges SUBSTANCE ABUSE facing the public and private sectors TERRORISM AND HOMELAND SECURITY around the world. TRANSPORTATION AND INFRASTRUCTURE Support RAND WORKFORCE AND WORKPLACE Purchase this document Browse Books & Publications Make a charitable contribution For More Information Visit RAND at www.rand.org Explore the RAND Homeland Security Program RAND Intelligence Policy Center View document details Limited Electronic Distribution Rights This document and trademark(s) contained herein are protected by law as indicated in a notice appearing later in this work. This electronic representation of RAND intellectual property is provided for non-commercial use only. Unauthorized posting of RAND PDFs to a non-RAND Web site is prohibited. RAND PDFs are protected under copyright law. Permission is required from RAND to reproduce, or reuse in another form, any of our research documents for commercial use. For information on reprint and linking permissions, please see RAND Permissions. This product is part of the RAND Corporation monograph series. RAND monographs present major research findings that address the challenges facing the public and private sectors. All RAND mono- graphs undergo rigorous peer review to ensure high standards for research quality and objectivity. -
Certain Aspects of "Magic" in the Cryptological Background of the Various Official Investigations Into the Attack on P
REF ID:A485355 OF 'l'.BE V.AltIOUS OFFICIAL INVEmGATIONS mo 'l!BE A'.t'.J!ACK ON PEA.BL MRBOR ··. •· . ' I-.- REF ID:A485355 --;-~·;-:;-.:- ... -~.... , ""'-·I';"~-""",~-·;,'~;~~~-~~.\,-::):t~<.""',. -.~\~=---:~-.,,-1f~': ------== ,,.--.., "t-,-.\;' .,-~,-. Certain As;pects of 1tMsgie 11 in the Ct;r:ttol~eaJ.. De.ck.ground of the V{'J."':touc; Offic!.&.1. Invest1@(1ons into the Atttlck on Pearl Harbor INDEX Section l. Introduction • • • • • • • • • • • • • • • • • • • 2. The Real Essence of the Problem • • • • • • • • • 11 A Ziev Look a.t the Revisionists Allegations of Conspiracy to Keep K:l.mmel and S'bort in the Da:rk • • • • • • • • • • • • • • • • • • • • • 18 4. Was MtlGIC Withheld from Kimmel and Short and, if so, ~ ••••••• ,, •••••••• • • 35 1 The tiWinds Code Message:B ' . ~ . .. 49 The Question of Sabota.g~f! • • • ti ~ • • • • • • • 53 Conclusions ....... ",., ....... 65 8. Epilogtte • • .. • • • • ' • ' It • Ill • • • • • • • • 60 11 11 APPENDIX 1: Pearl H&'bor in Pernpective1 by Dr. Louis Morton, Uni:ted States Na.val Institute Proceedi!!is,, Vo1. 81, No. 4, April 1955; P-.kl. 461'.:468 APPlitWIX 2: !lpea.rl Ra.rhor and the Revlsionists, 11 by Prof'. Robert H. Ferrc:Ll.. The Historian, Vol. XVII, No. 2, SprinS 19551 :Pl~· 215·233 REF ID:A485355 1. nmOD"OCTION More than 15 yea.rs have passed. since the Japanese, with unparalleled good luck, good luck that nov seem:s astoundinS, and vith a degree of skill unanticipated by the United, :3tates, executed their surprise attack on Pearl Harbor during the morning hours of 7 December 1941. It was an attack that constituted a. momentou::; disaster for the United States; it ma.de our Navy's Pacific Pleet, for all practica.l purposes, hors de combat for m.a.ny months. -

The First Americans the 1941 US Codebreaking Mission to Bletchley Park
United States Cryptologic History The First Americans The 1941 US Codebreaking Mission to Bletchley Park Special series | Volume 12 | 2016 Center for Cryptologic History David J. Sherman is Associate Director for Policy and Records at the National Security Agency. A graduate of Duke University, he holds a doctorate in Slavic Studies from Cornell University, where he taught for three years. He also is a graduate of the CAPSTONE General/Flag Officer Course at the National Defense University, the Intelligence Community Senior Leadership Program, and the Alexander S. Pushkin Institute of the Russian Language in Moscow. He has served as Associate Dean for Academic Programs at the National War College and while there taught courses on strategy, inter- national relations, and intelligence. Among his other government assignments include ones as NSA’s representative to the Office of the Secretary of Defense, as Director for Intelligence Programs at the National Security Council, and on the staff of the National Economic Council. This publication presents a historical perspective for informational and educational purposes, is the result of independent research, and does not necessarily reflect a position of NSA/CSS or any other US government entity. This publication is distributed free by the National Security Agency. If you would like additional copies, please email [email protected] or write to: Center for Cryptologic History National Security Agency 9800 Savage Road, Suite 6886 Fort George G. Meade, MD 20755 Cover: (Top) Navy Department building, with Washington Monument in center distance, 1918 or 1919; (bottom) Bletchley Park mansion, headquarters of UK codebreaking, 1939 UNITED STATES CRYPTOLOGIC HISTORY The First Americans The 1941 US Codebreaking Mission to Bletchley Park David Sherman National Security Agency Center for Cryptologic History 2016 Second Printing Contents Foreword ................................................................................ -

A Reference Guide to Selected Historical Documents Relating to the National Security Agency/Central Security Service (NSA/CSS) 1931-1985
Description of document: A Reference Guide to Selected Historical Documents Relating to the National Security Agency/Central Security Service (NSA/CSS) 1931-1985 Requested date: 15-June-2009 Released date: 03-February-2010 Posted date: 15-February-2010 Source of document: National Security Agency Attn: FOIA/PA Office (DJP4) 9800 Savage Road, Suite 6248 Ft. George G. Meade, MD 20755-6248 Fax: 443-479-3612 Online form: Here The governmentattic.org web site (“the site”) is noncommercial and free to the public. The site and materials made available on the site, such as this file, are for reference only. The governmentattic.org web site and its principals have made every effort to make this information as complete and as accurate as possible, however, there may be mistakes and omissions, both typographical and in content. The governmentattic.org web site and its principals shall have neither liability nor responsibility to any person or entity with respect to any loss or damage caused, or alleged to have been caused, directly or indirectly, by the information provided on the governmentattic.org web site or in this file. The public records published on the site were obtained from government agencies using proper legal channels. Each document is identified as to the source. Any concerns about the contents of the site should be directed to the agency originating the document in question. GovernmentAttic.org is not responsible for the contents of documents published on the website. A REFERENCE GUIDE TO SELECTED HISTORICAL DOCUMENTS RELATING TO THE NATIONAL SECURITY AGENCY/CENTRAL SECURITY SERVICE 1931-1985 (U) SOURCE DOCUMENTS IN Compiled by: CRYPTOLOGIC HISTORY Gerald K. -

Bentley, Caitlin Accepted Thesis 12-04-15 Fa 15.Pdf
Read all instructions first and then perform each step in this order. 1. Select File/Save As menu options to save this document (name it: Last, First MM-DD-YY) to your computer disk. 2. Open Word and this file. The file opens in Protected Mode. Type title above in the gray box as instructed and tab to next field (see instructions in each gray field and in the status bar). Tab and answer all questions until you return back to the title above. 3. Please scroll to and read Chapter 1 to learn how to unprotect this document. Once the document is unprotected the gray fields will continue to display on the screen, but will not print or convert to the PDF file. Fields can then also be modified if needed. 4. Once the document is Unprotected, scroll to Chapter 2 to read about the automatic Table of Contents, Heading Styles, Tables, Figures, References, and Appendices. 5. To remove this box, click it, point to outer gray hash marks until you see the Move icon, click to select, and press Delete key. Linking Communications: the Philippine Regional Section of the Allied Intelligence Bureau's Operations in the Occupied Islands,1942-1945 A thesis presented to the faculty of the College of Arts and Sciences of Ohio University In partial fulfillment of the requirements for the degree Master of Arts Caitlin T. Bentley December 2015 © 2015 Caitlin T. Bentley. All Rights Reserved. 2 This thesis titled Linking Communications: The Philippine Regional Section of the Allied Intelligence Bureau's Operations in the Occupied Islands,1942-1945 by CAITLIN T. -

Quiet Heroes Cover.Qxd
UNITED STATES CRYPTOLOGIC HISTORY Series IV World War II Volume 7 The Quiet Heroes of the Southwest Pacific Theater: An Oral History of the Men and Women of CBB and FRUMEL Sharon A. Maneki CENTER FOR CRYPTOLOGIC HISTORY NATIONAL SECURITY AGENCY Reprinted 2007 This monograph is a product of the National Security Agency history program. Its contents and conclusions are those of the author, based on original research, and do not necessarily represent the official views of the National Security Agency. Please address divergent opinion or additional detail to the Center for Cryptologic History (EC). Page ii Table of Contents Foreword . v Preface . vii Acknowledgments . xii An Introduction to the Central Bureau Story . .1 Chapter 1: The Challenge of Reaching Australia . .3 Escaping from the Philippines: A View from the Navy . .3 Escaping from the Philippines: A View from the Army . .5 Traveling from Stateside . .7 Chapter 2: Challenges at Central Bureau Field Sections . .11 Mastering Japanese Intercept . .12 The Paradox of Life at a Field Site . .13 On the Move in New Guinea . .16 An American Perspective on Traffic Analysis . .18 Chapter 3: Cryptanalysts at Work in Central Bureau . .23 The Key to Success Was Teamwork . .25 The Joy of Discovery . .30 Putting Our Cryptanalytic Skills to the Test at Central Bureau 1942-1945 .34 Developing the Clues to Solve the Cryptanalytic Puzzle . .37 Chapter 4: Central Bureau: A Complete Signals Intelligence Agency . .39 The Trials and Tribulations of an IBM Operator . .39 Supporting Central Bureau’s Information Needs . .41 A Central Bureau J-Boy . .42 A Bizarre Experiment .