Label Formatting Commands
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Disk Clone Industrial
Disk Clone Industrial USER MANUAL Ver. 1.0.0 Updated: 9 June 2020 | Contents | ii Contents Legal Statement............................................................................... 4 Introduction......................................................................................4 Cloning Data.................................................................................................................................... 4 Erasing Confidential Data..................................................................................................................5 Disk Clone Overview.......................................................................6 System Requirements....................................................................................................................... 7 Software Licensing........................................................................................................................... 7 Software Updates............................................................................................................................. 8 Getting Started.................................................................................9 Disk Clone Installation and Distribution.......................................................................................... 12 Launching and initial Configuration..................................................................................................12 Navigating Disk Clone.....................................................................................................................14 -

(PI-Net): Facial Image Obfuscation with Manipulable Semantics
Perceptual Indistinguishability-Net (PI-Net): Facial Image Obfuscation with Manipulable Semantics Jia-Wei Chen1,3 Li-Ju Chen3 Chia-Mu Yu2 Chun-Shien Lu1,3 1Institute of Information Science, Academia Sinica 2National Yang Ming Chiao Tung University 3Research Center for Information Technology Innovation, Academia Sinica Abstract Deepfakes [45], if used to replace sensitive semantics, can also mitigate privacy risks for identity disclosure [3, 15]. With the growing use of camera devices, the industry However, all of the above methods share a common has many image datasets that provide more opportunities weakness of syntactic anonymity, or say, lack of formal for collaboration between the machine learning commu- privacy guarantee. Recent studies report that obfuscated nity and industry. However, the sensitive information in faces can be re-identified through machine learning tech- the datasets discourages data owners from releasing these niques [33, 19, 35]. Even worse, the above methods are datasets. Despite recent research devoted to removing sen- not guaranteed to reach the analytical conclusions consis- sitive information from images, they provide neither mean- tent with the one derived from original images, after manip- ingful privacy-utility trade-off nor provable privacy guar- ulating semantics. To overcome the above two weaknesses, antees. In this study, with the consideration of the percep- one might resort to differential privacy (DP) [9], a rigorous tual similarity, we propose perceptual indistinguishability privacy notion with utility preservation. In particular, DP- (PI) as a formal privacy notion particularly for images. We GANs [1, 6, 23, 46] shows a promising solution for both also propose PI-Net, a privacy-preserving mechanism that the provable privacy and perceptual similarity of synthetic achieves image obfuscation with PI guarantee. -

Forest Quickstart Guide for Linguists
Forest Quickstart Guide for Linguists Guido Vanden Wyngaerd [email protected] June 28, 2020 Contents 1 Introduction 1 2 Loading Forest 2 3 Basic Usage 2 4 Adjusting node spacing 4 5 Triangles 7 6 Unlabelled nodes 9 7 Horizontal alignment of terminals 10 8 Arrows 11 9 Highlighting 14 1 Introduction Forest is a package for drawing linguistic (and other) tree diagrams de- veloped by Sašo Živanović. This manual provides a quickstart guide for linguists with just the essential things that you need to get started. More 1 extensive documentation is available from the CTAN-archive. Forest is based on the TikZ package; more information about its commands, in par- ticular those controlling the appearance of the nodes, the arrows, and the highlighting can be found in the TikZ documentation. 2 Loading Forest In your preamble, put \usepackage[linguistics]{forest} The linguistics option makes for nice trees, in which the branches meet above the two nodes that they join; it will also align the example number (provided by linguex) with the top of the tree: (1) CP C IP I VP V NP 3 Basic Usage Forest uses a familiar labelled brackets syntax. The code below will out- put the tree in (1) above (\ex. requires the linguex package and provides the example number): \ex. \begin{forest} [CP[C][IP[I][VP[V][NP]]]] \end{forest} Forest will parse the above code without problem, but you are likely to soon get lost in your labelled brackets with more complicated trees if you write the code this way. The better alternative is to arrange the nodes over multiple lines: 2 \ex. -

January 2019 Edition
Tunkhannock Area High School Tunkhannock, Pennsylvania The Prowler January 2019 Volume XIV, Issue XLVII Local Subst itute Teacher in Trouble Former TAHS substitute teacher, Zachary Migliori, faces multiple charges. By MADISON NESTOR Former substitute teacher Wyoming County Chief out, that she did not report it originally set for December at Tunkhannock Area High Detective David Ide, started to anyone. 18 was moved to March 18. School, Zachary Migliori, on October 11 when the When Detective Ide asked If he is convicted, he will was charged with three felony parents of a 15-year old Migliori if he knew that one face community service, and counts of distributing obscene student found pornographic of the girls he sent explicit mandatory counseling. material, three misdemeanor images and sexual texts messages to was a 15-year- Tunkhannock Area High counts of open lewdness, and on their daughter’s phone. old, he explained that he School took action right away three misdemeanor counts of The parent then contacted thought she was 18-years-old to ensure students’ safety, unlawful contact with minors. Detective Ide, who found because she hung out with and offers counseling to any This comes after the results after investigating that the many seniors. After being students who need it. of an investigation suspecting substitute teacher was using informed of one victim being Sources:WNEP, lewd contact with students a Snapchat account with the 15-years-old, Migliori said he WCExaminer, CitizensVoice proved to be true. According name ‘Zach Miggs.’ was disgusted with himself. to court documents, Migliori Two 17-year old females Judge Plummer set used Facebook Messenger also came forward, one of Migliori’s bail at $50,000. -

Metadata for Everyone a Simple, Low-Cost Methodology Timothy D
SAS Global Forum 2008 Data Integration Paper 138-2008 Metadata for Everyone A Simple, Low-Cost Methodology Timothy D. Brown, Altoona, IA ABSTRACT In the context of Base SAS® programming, this paper uses “hardcoded” values as an introduction to “metadata” and the reasons for using it. It then describes a low cost and simple methodology for maintaining any kind of metadata. INTRODUCTION This discussion will take an indirect approach to defining metadata. It’ll describe the metadata which might be included, or hard-coded, in a Base SAS program and propose alternatives to storing and using the metadata. Outside of programs “data” and “code” are distinct. However within programs, the distinction gets blurred when data values, called “hardcoded” data, are included within the code. Hardcoded values include, but are not limited to: • Text constants, literals • Names of companies, people, organizations and places • Directory paths and file names • Parameters on SAS procedures such as WHERE, KEEP, DROP, RENAME, VARS, BY etc • Numeric constants including dates* • Statistical constants • Period begin and end dates • Mixed text and numeric values • Expressions in IF and WHERE clauses • What-if scenarios (* excluding dates which are derived logically using a SAS functions such as TODAY(), DATETIME(), INTNX and NXTPD) In addition, many small conversion, cross-reference and look-up tables, which might be hardcoded as SAS formats or read into a program from many different sources, work well as metadata and fit into this framework. Obviously, some hardcoded values might never change in the life of a program. So it might be prudent to leave some hardcoded values in the code. -

Four Ways to Reorder Your Variables, Ranked by Elegance and Efficiency Louise S
Order, Order! Four Ways To Reorder Your Variables, Ranked by Elegance and Efficiency Louise S. Hadden, Abt Associates Inc. ABSTRACT SAS® practitioners are frequently required to present variables in an output data file in a particular order, or standards may require variables in a production data file to be in a particular order. This paper and presentation offer several methods for reordering variables in a data file, encompassing both DATA step and procedural methods. Relative efficiency and elegance of the solutions will be discussed. INTRODUCTION SAS provides us with numerous methods to control all types of SAS output, including SAS data files, data tables in other formats, and ODS output. This paper focuses solely on output SAS data files (which may then be used to generate SAS data files and other types of output from SAS processes), and specifically on DATA step and PROC SQL methods. This short paper and presentation is suitable for all SAS practitioners at all levels of expertise. Attendees will gain a greater understanding of the processes by which SAS assigns variable attributes, including variable/column order within a data file, and how to obtain information on variable attributes – and in the process, learn how to reorder variables within a SAS data file. KNOW THY DATA It is always important to understand fully and explore the inputs to SAS-created output. SAS has provided users with a variety of possibilities in terms of determining locations of variables or columns (and other important details comprising metadata). These possibilities include, but are not limited to: 1. The CONTENTS Procedure 2. -

S.Ha.R.K. Installation Howto Tools Knoppix Live CD Linux Fdisk HD
S.Ha.R.K. Installation Tools HowTo • Linux fdisk utility • A copy of Linux installation CD • A copy of Windows® installation CD Tullio Facchinetti University of Pavia - Italy • Some FreeDOS utilities • A copy of S.Ha.R.K. S.Ha.R.K. Workshop S.Ha.R.K. Workshop Knoppix live CD Linux fdisk Command action a toggle a bootable flag Download ISO from b edit bsd disklabel c toggle the dos compatibility flag d delete a partition http://www.knoppix.org l list known partition types m print this menu n add a new partition o create a new empty DOS partition table p print the partition table q quit without saving changes • boot from CD s create a new empty Sun disklabel t change a partition's system id • open a command shell u change display/entry units v verify the partition table • type “su” (become root ), password is empty w write table to disk and exit x extra functionality (experts only) • start fdisk (ex. fdisk /dev/hda ) Command (m for help): S.Ha.R.K. Workshop S.Ha.R.K. Workshop HD partitioning HD partitioning 1st FreeDOS FAT32 FreeDOS must be installed Primary 2nd Windows® FAT32 into the first partition of your HD or it may not boot 3rd Linux / extX Data 1 FAT32 format data partitions as ... Extended FAT32, so that you can share Data n FAT32 your data between Linux, last Linux swap swap Windows® and FreeDOS S.Ha.R.K. Workshop S.Ha.R.K. Workshop 1 HD partitioning Windows ® installation FAT32 Windows® partition type Install Windows®.. -

NETSTAT Command
NETSTAT Command | NETSTAT Command | Use the NETSTAT command to display network status of the local host. | | ┌┐────────────── | 55──NETSTAT─────6─┤ Option ├─┴──┬────────────────────────────────── ┬ ─ ─ ─ ────────────────────────────────────────5% | │┌┐───────────────────── │ | └─(──SELect───6─┤ Select_String ├─┴ ─ ┘ | Option: | ┌┐─COnn────── (1, 2) ──────────────── | ├──┼─────────────────────────── ┼ ─ ──────────────────────────────────────────────────────────────────────────────┤ | ├─ALL───(2)──────────────────── ┤ | ├─ALLConn─────(1, 2) ────────────── ┤ | ├─ARp ipaddress───────────── ┤ | ├─CLients─────────────────── ┤ | ├─DEvlinks────────────────── ┤ | ├─Gate───(3)─────────────────── ┤ | ├─┬─Help─ ┬─ ───────────────── ┤ | │└┘─?──── │ | ├─HOme────────────────────── ┤ | │┌┐─2ð────── │ | ├─Interval─────(1, 2) ─┼───────── ┼─ ┤ | │└┘─seconds─ │ | ├─LEVel───────────────────── ┤ | ├─POOLsize────────────────── ┤ | ├─SOCKets─────────────────── ┤ | ├─TCp serverid───(1) ─────────── ┤ | ├─TELnet───(4)───────────────── ┤ | ├─Up──────────────────────── ┤ | └┘─┤ Command ├───(5)──────────── | Command: | ├──┬─CP cp_command───(6) ─ ┬ ────────────────────────────────────────────────────────────────────────────────────────┤ | ├─DELarp ipaddress─ ┤ | ├─DRop conn_num──── ┤ | └─RESETPool──────── ┘ | Select_String: | ├─ ─┬─ipaddress────(3) ┬ ─ ───────────────────────────────────────────────────────────────────────────────────────────┤ | ├─ldev_num─────(4) ┤ | └─userid────(2) ─── ┘ | Notes: | 1 Only ALLCON, CONN and TCP are valid with INTERVAL. | 2 The userid -

JES3 Commands
z/OS Version 2 Release 3 JES3 Commands IBM SA32-1008-30 Note Before using this information and the product it supports, read the information in “Notices” on page 431. This edition applies to Version 2 Release 3 of z/OS (5650-ZOS) and to all subsequent releases and modifications until otherwise indicated in new editions. Last updated: 2019-02-16 © Copyright International Business Machines Corporation 1997, 2017. US Government Users Restricted Rights – Use, duplication or disclosure restricted by GSA ADP Schedule Contract with IBM Corp. Contents List of Figures....................................................................................................... ix List of Tables........................................................................................................ xi About this document...........................................................................................xiii Who should use this document.................................................................................................................xiii Where to find more information................................................................................................................ xiii How to send your comments to IBM......................................................................xv If you have a technical problem.................................................................................................................xv Summary of changes...........................................................................................xvi -

System Analysis and Tuning Guide System Analysis and Tuning Guide SUSE Linux Enterprise Server 15 SP1
SUSE Linux Enterprise Server 15 SP1 System Analysis and Tuning Guide System Analysis and Tuning Guide SUSE Linux Enterprise Server 15 SP1 An administrator's guide for problem detection, resolution and optimization. Find how to inspect and optimize your system by means of monitoring tools and how to eciently manage resources. Also contains an overview of common problems and solutions and of additional help and documentation resources. Publication Date: September 24, 2021 SUSE LLC 1800 South Novell Place Provo, UT 84606 USA https://documentation.suse.com Copyright © 2006– 2021 SUSE LLC and contributors. All rights reserved. Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or (at your option) version 1.3; with the Invariant Section being this copyright notice and license. A copy of the license version 1.2 is included in the section entitled “GNU Free Documentation License”. For SUSE trademarks, see https://www.suse.com/company/legal/ . All other third-party trademarks are the property of their respective owners. Trademark symbols (®, ™ etc.) denote trademarks of SUSE and its aliates. Asterisks (*) denote third-party trademarks. All information found in this book has been compiled with utmost attention to detail. However, this does not guarantee complete accuracy. Neither SUSE LLC, its aliates, the authors nor the translators shall be held liable for possible errors or the consequences thereof. Contents About This Guide xii 1 Available Documentation xiii -
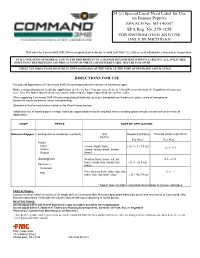
Command 3ME Banana Pepper Label
24 (c) Special Local Need Label for Use on Banana Peppers EPA SLN No. MI-140007 EPA Reg. No. 279-3158 FOR DISTRIBUTION AND USE ONLY IN MICHIGAN This label for Command® 3ME Microencapsulated Herbicide is valid until May 13, 2024 or until withdrawn, canceled or suspended. IT IS A VIOLATION OF FEDERAL LAW TO USE THIS PRODUCT IN A MANNER INCONSISTENT WITH ITS LABELING. ALL APPLICABLE DIRECTIONS, RESTRICTIONS AND PRECAUTIONS ON THE EPA REGISTERED LABEL MUST BE FOLLOWED. THESE USE DIRECTIONS MUST BE IN THE POSSESSION OF THE USER AT THE TIME OF PESTICIDE APPLICATION. DIRECTIONS FOR USE For ground application of Command 3ME Microencapsulated Herbicide on banana pepper. Make a single broadcast herbicide application at 10.7 to 42.7 fl oz per acre (0.25 to 1 lb ai/A) in a minimum of 10 gallons of water per acre. Use the lower specified rate on course soils and the higher specified rate on fine soils. When applying Command 3ME Microencapsulated Herbicide as a pre-transplant soil treatment, place roots of transplants below the chemical barrier when transplanting. Observe all buffer restrictions noted in the Restrictions section. Additional use of labeled post-emerge herbicide applications may be required where existing grass weeds are present at the time of application. CROP PESTS RATE OF APPLICATION Banana Pepper Lambsquarters (herbicide resistant) Soil Broadcast Rates Pounds Active Ingredient Texture Per Acre* Per Acre Foxtail- Giant, Coarse (light) Soils: (10.7 – 21.3 fl oz) 0.25 - 0.5 Green (sand, loamy sand, sandy Robust loam) Goosegrass Medium Soils: (loam, silt, silt 0.5 – 0.75 loam, sandy clay, sandy clay (21.3 - 32 fl oz) Panicum – loam) Common Fine (heavy) Soils: (silty clay, clay 0.75 - 1 Fall loam, silty clay loam, clay) (32 – 42.7 fl oz) * Select lower to higher rates based on lighter to heavier soil types. -
Chronos® Bone Void Filler Beta-Tricalcium Phosphate (B-TCP) Bone Graft Substitute Chronos® Bone Void Filler
chronOS® BONE VOID FILLER Beta-Tricalcium Phosphate (b-TCP) bone graft substitute chronOS® BONE VOID FILLER OSTEOCONDUCTIVE • RESORBABLE • SYNTHETIC chronOS® Granules and Preforms are synthetic, porous, osteoconductive, resorbable calcium phosphate bone substitutes, which can replace autogenous bone. chronOS Bone Graft Substitute eliminates the need for autologous bone harvesting, thus reducing overall patient morbidity. chronOS Granules and Preforms are manufactured in a clean-room environment from a biocompatible, radiopaque material, beta-tricalcium phosphate (b-TCP). This material contains two of the main mineral constituents of bone, calcium and phosphorous. chronOS Bone Graft Substitute has been clinically used in Europe for more than 20 years under the name CEROS 82. Replaced with bone in 6 to 18 months, chronOS Bone Graft Substitute is suitable for many bone void filler applications. Due to its synthetic manufacturing process, chronOS Beta-Tricalcium Phosphate shows reliable and standardized biomechanical properties. The compressive strength of chronOS Beta-Tricalcium Phosphate averages ~5 MPa, and is similar to that of human cancellous bone. Postoperative, 6 weeks Postoperative, 12 months High tibial osteotomy treated with a proximal tibial plate and chronOS Preforms (Dr. Wymengy, Nijmegen, Netherlands) DePuy Synthes Trauma chronOS Bone Void Filler INDICATIONS AND CONTRAINDICATIONS Indications chronOS is indicated for use in bony voids or gaps that are not intrinsic to the stability of the bony structure. chronOS is indicated for use in the treatment of bony defects created surgically or through traumatic injury. chronOS is intended to be gently packed or placed into bony voids or gaps of the skeletal system (i.e., the extremities, spine, and pelvis) and may be combined with autogenous blood and/or bone marrow.