Forest Quickstart Guide for Linguists
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

1 A) Login to the System B) Use the Appropriate Command to Determine Your Login Shell C) Use the /Etc/Passwd File to Verify the Result of Step B
CSE ([email protected] II-Sem) EXP-3 1 a) Login to the system b) Use the appropriate command to determine your login shell c) Use the /etc/passwd file to verify the result of step b. d) Use the ‘who’ command and redirect the result to a file called myfile1. Use the more command to see the contents of myfile1. e) Use the date and who commands in sequence (in one line) such that the output of date will display on the screen and the output of who will be redirected to a file called myfile2. Use the more command to check the contents of myfile2. 2 a) Write a “sed” command that deletes the first character in each line in a file. b) Write a “sed” command that deletes the character before the last character in each line in a file. c) Write a “sed” command that swaps the first and second words in each line in a file. a. Log into the system When we return on the system one screen will appear. In this we have to type 100.0.0.9 then we enter into editor. It asks our details such as Login : krishnasai password: Then we get log into the commands. bphanikrishna.wordpress.com FOSS-LAB Page 1 of 10 CSE ([email protected] II-Sem) EXP-3 b. use the appropriate command to determine your login shell Syntax: $ echo $SHELL Output: $ echo $SHELL /bin/bash Description:- What is "the shell"? Shell is a program that takes your commands from the keyboard and gives them to the operating system to perform. -

Windows Command Prompt Cheatsheet
Windows Command Prompt Cheatsheet - Command line interface (as opposed to a GUI - graphical user interface) - Used to execute programs - Commands are small programs that do something useful - There are many commands already included with Windows, but we will use a few. - A filepath is where you are in the filesystem • C: is the C drive • C:\user\Documents is the Documents folder • C:\user\Documents\hello.c is a file in the Documents folder Command What it Does Usage dir Displays a list of a folder’s files dir (shows current folder) and subfolders dir myfolder cd Displays the name of the current cd filepath chdir directory or changes the current chdir filepath folder. cd .. (goes one directory up) md Creates a folder (directory) md folder-name mkdir mkdir folder-name rm Deletes a folder (directory) rm folder-name rmdir rmdir folder-name rm /s folder-name rmdir /s folder-name Note: if the folder isn’t empty, you must add the /s. copy Copies a file from one location to copy filepath-from filepath-to another move Moves file from one folder to move folder1\file.txt folder2\ another ren Changes the name of a file ren file1 file2 rename del Deletes one or more files del filename exit Exits batch script or current exit command control echo Used to display a message or to echo message turn off/on messages in batch scripts type Displays contents of a text file type myfile.txt fc Compares two files and displays fc file1 file2 the difference between them cls Clears the screen cls help Provides more details about help (lists all commands) DOS/Command Prompt help command commands Source: https://technet.microsoft.com/en-us/library/cc754340.aspx. -
Disk Clone Industrial
Disk Clone Industrial USER MANUAL Ver. 1.0.0 Updated: 9 June 2020 | Contents | ii Contents Legal Statement............................................................................... 4 Introduction......................................................................................4 Cloning Data.................................................................................................................................... 4 Erasing Confidential Data..................................................................................................................5 Disk Clone Overview.......................................................................6 System Requirements....................................................................................................................... 7 Software Licensing........................................................................................................................... 7 Software Updates............................................................................................................................. 8 Getting Started.................................................................................9 Disk Clone Installation and Distribution.......................................................................................... 12 Launching and initial Configuration..................................................................................................12 Navigating Disk Clone.....................................................................................................................14 -

Don't Trust Traceroute (Completely)
Don’t Trust Traceroute (Completely) Pietro Marchetta, Valerio Persico, Ethan Katz-Bassett Antonio Pescapé University of Southern California, CA, USA University of Napoli Federico II, Italy [email protected] {pietro.marchetta,valerio.persico,pescape}@unina.it ABSTRACT In this work, we propose a methodology based on the alias resolu- tion process to demonstrate that the IP level view of the route pro- vided by traceroute may be a poor representation of the real router- level route followed by the traffic. More precisely, we show how the traceroute output can lead one to (i) inaccurately reconstruct the route by overestimating the load balancers along the paths toward the destination and (ii) erroneously infer routing changes. Categories and Subject Descriptors C.2.1 [Computer-communication networks]: Network Architec- ture and Design—Network topology (a) Traceroute reports two addresses at the 8-th hop. The common interpretation is that the 7-th hop is splitting the traffic along two Keywords different forwarding paths (case 1); another explanation is that the 8- th hop is an RFC compliant router using multiple interfaces to reply Internet topology; Traceroute; IP alias resolution; IP to Router to the source (case 2). mapping 1 1. INTRODUCTION 0.8 Operators and researchers rely on traceroute to measure routes and they assume that, if traceroute returns different IPs at a given 0.6 hop, it indicates different paths. However, this is not always the case. Although state-of-the-art implementations of traceroute al- 0.4 low to trace all the paths -

Metadata for Everyone a Simple, Low-Cost Methodology Timothy D
SAS Global Forum 2008 Data Integration Paper 138-2008 Metadata for Everyone A Simple, Low-Cost Methodology Timothy D. Brown, Altoona, IA ABSTRACT In the context of Base SAS® programming, this paper uses “hardcoded” values as an introduction to “metadata” and the reasons for using it. It then describes a low cost and simple methodology for maintaining any kind of metadata. INTRODUCTION This discussion will take an indirect approach to defining metadata. It’ll describe the metadata which might be included, or hard-coded, in a Base SAS program and propose alternatives to storing and using the metadata. Outside of programs “data” and “code” are distinct. However within programs, the distinction gets blurred when data values, called “hardcoded” data, are included within the code. Hardcoded values include, but are not limited to: • Text constants, literals • Names of companies, people, organizations and places • Directory paths and file names • Parameters on SAS procedures such as WHERE, KEEP, DROP, RENAME, VARS, BY etc • Numeric constants including dates* • Statistical constants • Period begin and end dates • Mixed text and numeric values • Expressions in IF and WHERE clauses • What-if scenarios (* excluding dates which are derived logically using a SAS functions such as TODAY(), DATETIME(), INTNX and NXTPD) In addition, many small conversion, cross-reference and look-up tables, which might be hardcoded as SAS formats or read into a program from many different sources, work well as metadata and fit into this framework. Obviously, some hardcoded values might never change in the life of a program. So it might be prudent to leave some hardcoded values in the code. -

Four Ways to Reorder Your Variables, Ranked by Elegance and Efficiency Louise S
Order, Order! Four Ways To Reorder Your Variables, Ranked by Elegance and Efficiency Louise S. Hadden, Abt Associates Inc. ABSTRACT SAS® practitioners are frequently required to present variables in an output data file in a particular order, or standards may require variables in a production data file to be in a particular order. This paper and presentation offer several methods for reordering variables in a data file, encompassing both DATA step and procedural methods. Relative efficiency and elegance of the solutions will be discussed. INTRODUCTION SAS provides us with numerous methods to control all types of SAS output, including SAS data files, data tables in other formats, and ODS output. This paper focuses solely on output SAS data files (which may then be used to generate SAS data files and other types of output from SAS processes), and specifically on DATA step and PROC SQL methods. This short paper and presentation is suitable for all SAS practitioners at all levels of expertise. Attendees will gain a greater understanding of the processes by which SAS assigns variable attributes, including variable/column order within a data file, and how to obtain information on variable attributes – and in the process, learn how to reorder variables within a SAS data file. KNOW THY DATA It is always important to understand fully and explore the inputs to SAS-created output. SAS has provided users with a variety of possibilities in terms of determining locations of variables or columns (and other important details comprising metadata). These possibilities include, but are not limited to: 1. The CONTENTS Procedure 2. -

NETSTAT Command
NETSTAT Command | NETSTAT Command | Use the NETSTAT command to display network status of the local host. | | ┌┐────────────── | 55──NETSTAT─────6─┤ Option ├─┴──┬────────────────────────────────── ┬ ─ ─ ─ ────────────────────────────────────────5% | │┌┐───────────────────── │ | └─(──SELect───6─┤ Select_String ├─┴ ─ ┘ | Option: | ┌┐─COnn────── (1, 2) ──────────────── | ├──┼─────────────────────────── ┼ ─ ──────────────────────────────────────────────────────────────────────────────┤ | ├─ALL───(2)──────────────────── ┤ | ├─ALLConn─────(1, 2) ────────────── ┤ | ├─ARp ipaddress───────────── ┤ | ├─CLients─────────────────── ┤ | ├─DEvlinks────────────────── ┤ | ├─Gate───(3)─────────────────── ┤ | ├─┬─Help─ ┬─ ───────────────── ┤ | │└┘─?──── │ | ├─HOme────────────────────── ┤ | │┌┐─2ð────── │ | ├─Interval─────(1, 2) ─┼───────── ┼─ ┤ | │└┘─seconds─ │ | ├─LEVel───────────────────── ┤ | ├─POOLsize────────────────── ┤ | ├─SOCKets─────────────────── ┤ | ├─TCp serverid───(1) ─────────── ┤ | ├─TELnet───(4)───────────────── ┤ | ├─Up──────────────────────── ┤ | └┘─┤ Command ├───(5)──────────── | Command: | ├──┬─CP cp_command───(6) ─ ┬ ────────────────────────────────────────────────────────────────────────────────────────┤ | ├─DELarp ipaddress─ ┤ | ├─DRop conn_num──── ┤ | └─RESETPool──────── ┘ | Select_String: | ├─ ─┬─ipaddress────(3) ┬ ─ ───────────────────────────────────────────────────────────────────────────────────────────┤ | ├─ldev_num─────(4) ┤ | └─userid────(2) ─── ┘ | Notes: | 1 Only ALLCON, CONN and TCP are valid with INTERVAL. | 2 The userid -
Introduction to Unix Shell
Introduction to Unix Shell François Serra, David Castillo, Marc A. Marti- Renom Genome Biology Group (CNAG) Structural Genomics Group (CRG) Run Store Programs Data Communicate Interact with each other with us The Unix Shell Introduction Interact with us Rewiring Telepathy Typewriter Speech WIMP The Unix Shell Introduction user logs in The Unix Shell Introduction user logs in user types command The Unix Shell Introduction user logs in user types command computer executes command and prints output The Unix Shell Introduction user logs in user types command computer executes command and prints output user types another command The Unix Shell Introduction user logs in user types command computer executes command and prints output user types another command computer executes command and prints output The Unix Shell Introduction user logs in user types command computer executes command and prints output user types another command computer executes command and prints output ⋮ user logs off The Unix Shell Introduction user logs in user types command computer executes command and prints output user types another command computer executes command and prints output ⋮ user logs off The Unix Shell Introduction user logs in user types command computer executes command and prints output user types another command computer executes command and prints output ⋮ user logs off shell The Unix Shell Introduction user logs in user types command computer executes command and prints output user types another command computer executes command and prints output -
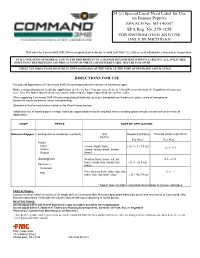
Command 3ME Banana Pepper Label
24 (c) Special Local Need Label for Use on Banana Peppers EPA SLN No. MI-140007 EPA Reg. No. 279-3158 FOR DISTRIBUTION AND USE ONLY IN MICHIGAN This label for Command® 3ME Microencapsulated Herbicide is valid until May 13, 2024 or until withdrawn, canceled or suspended. IT IS A VIOLATION OF FEDERAL LAW TO USE THIS PRODUCT IN A MANNER INCONSISTENT WITH ITS LABELING. ALL APPLICABLE DIRECTIONS, RESTRICTIONS AND PRECAUTIONS ON THE EPA REGISTERED LABEL MUST BE FOLLOWED. THESE USE DIRECTIONS MUST BE IN THE POSSESSION OF THE USER AT THE TIME OF PESTICIDE APPLICATION. DIRECTIONS FOR USE For ground application of Command 3ME Microencapsulated Herbicide on banana pepper. Make a single broadcast herbicide application at 10.7 to 42.7 fl oz per acre (0.25 to 1 lb ai/A) in a minimum of 10 gallons of water per acre. Use the lower specified rate on course soils and the higher specified rate on fine soils. When applying Command 3ME Microencapsulated Herbicide as a pre-transplant soil treatment, place roots of transplants below the chemical barrier when transplanting. Observe all buffer restrictions noted in the Restrictions section. Additional use of labeled post-emerge herbicide applications may be required where existing grass weeds are present at the time of application. CROP PESTS RATE OF APPLICATION Banana Pepper Lambsquarters (herbicide resistant) Soil Broadcast Rates Pounds Active Ingredient Texture Per Acre* Per Acre Foxtail- Giant, Coarse (light) Soils: (10.7 – 21.3 fl oz) 0.25 - 0.5 Green (sand, loamy sand, sandy Robust loam) Goosegrass Medium Soils: (loam, silt, silt 0.5 – 0.75 loam, sandy clay, sandy clay (21.3 - 32 fl oz) Panicum – loam) Common Fine (heavy) Soils: (silty clay, clay 0.75 - 1 Fall loam, silty clay loam, clay) (32 – 42.7 fl oz) * Select lower to higher rates based on lighter to heavier soil types. -

External Commands
5/22/2018 External commands External commands Previous | Content | Next External commands are known as Disk residence commands. Because they can be store with DOS directory or any disk which is used for getting these commands. Theses commands help to perform some specific task. These are stored in a secondary storage device. Some important external commands are given below- MORE MOVE FIND DOSKEY MEM FC DISKCOPY FORMAT SYS CHKDSK ATTRIB XCOPY SORT LABEL 1. MORE:-Using TYPE command we can see the content of any file. But if length of file is greater than 25 lines then remaining lines will scroll up. To overcome through this problem we uses MORE command. Using this command we can pause the display after each 25 lines. Syntax:- C:\> TYPE <File name> | MORE C:\> TYPE ROSE.TXT | MORE or C: \> DIR | MORE 2. MEM:-This command displays free and used amount of memory in the computer. Syntax:- C:\> MEM the computer will display the amount of memory. 3. SYS:- This command is used for copy system files to any disk. The disk having system files are known as Bootable Disk, which are used for booting the computer. Syntax:- C:\> SYS [Drive name] C:\> SYS A: System files transferred This command will transfer the three main system files COMMAND.COM, IO.SYS, MSDOS.SYS to the floppy disk. 4. XCOPY:- When we need to copy a directory instant of a file from one location to another the we uses xcopy command. This command is much faster than copy command. Syntax:- C:\> XCOPY < Source dirname > <Target dirname> C:\> XCOPY TC TURBOC 5. -

Linux Terminal Commands Man Pwd Ls Cd Olmo S
Python Olmo S. Zavala Romero Welcome Computers File system Super basics of Linux terminal Commands man pwd ls cd Olmo S. Zavala Romero mkdir touch Center of Atmospheric Sciences, UNAM rm mv Ex1 August 9, 2017 Regular expres- sions grep Ex2 More Python Olmo S. 1 Welcome Zavala Romero 2 Computers Welcome 3 File system Computers File system 4 Commands Commands man man pwd pwd ls ls cd mkdir cd touch mkdir rm touch mv Ex1 rm Regular mv expres- sions Ex1 grep Regular expressions Ex2 More grep Ex2 More Welcome to this course! Python Olmo S. Zavala Romero Welcome Computers File system Commands 1 Who am I? man pwd 2 Syllabus ls cd 3 Intro survey https://goo.gl/forms/SD6BM6KHKRlDOpZx1 mkdir 4 touch Homework 1 due this Sunday. rm mv Ex1 Regular expres- sions grep Ex2 More How does a computer works? Python Olmo S. Zavala Romero Welcome Computers File system Commands man pwd ls cd mkdir touch rm mv Ex1 Regular 1 CPU Central Processing Unit. All the computations happen there. expres- sions 2 HD Hard Drive. Stores persistent information in binary format. grep 3 RAM Random Access Memory. Faster memory, closer to the CPU, not persistent. Ex2 More 4 GPU Graphics Processing Unit. Used to process graphics. https://teentechdaily.files.wordpress.com/2015/06/computer-parts-diagram.jpg What is a file? Python Olmo S. Zavala Romero Welcome Computers File system Commands man pwd ls cd mkdir touch rm mv Section inside the HD with 0’s and 1’s. Ex1 Regular File extension is used to identify the meaning of those 0’s and 1’s. -

SAS Programming Tips
TUESDAY TIPS – SAS PROGRAMMING Weekly Tip for Nov. 3, 2020 Your data dictionary contains some variables that can iterate - for example, the unknown # of COVID tests for an unknown # of infants. How do you manage documentation? A data dictionary for a file based on Electronic Medical Records (EMR) contains variables which represent an unknown number of COVID tests for an unknown number of infants – there is no way to know in advance how many iterations of this variable will exist in the actual data file. In addition, variables in this file may exist for three different groups (pregnant women, postpartum women, and infants), with PR, PP and IN prefixes, respectively. This Tuesday Tip demonstrates how to process such variables in a data dictionary to drive label (and value label) description creation for iterated (and other) labels using SAS functions, as well as other utilities. Using PROC CONTENTS and ODS OUTPUT on an imported data dictionary (example shown above) and a data file from a health care entity, the position ODS OUTPUT object is created, and the column variable is standardized using the UPCASE function. ************************************************************; *** Import Personal Data Dictionary one tab at a time ***; ************************************************************; %macro imptabs(tabn=1, tabnm=identifiers, intab=Identifiers, startrow=10, endcol=H); proc import dbms=xlsx out = temp datafile = " \file.xlsx" replace; RANGE="&intab.$A&startrow.:&endcol.999"; getnames=YES; run; . data labels&tabn.; length label