IBM-IS-DCI-UR-Newsletter.Pdf
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Broadband/IP/Cloud Computing
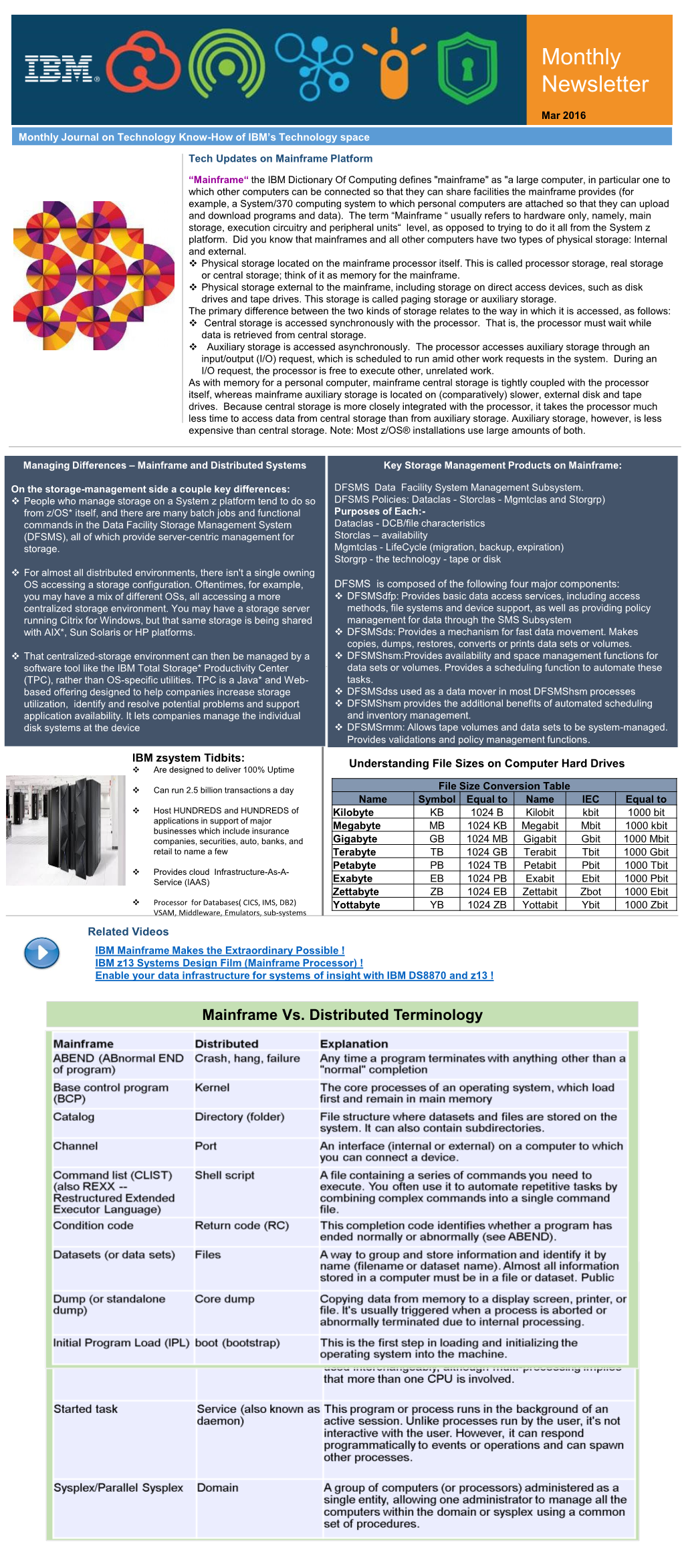
Broadband/IP/Cloud Computing Presentation to the Colorado Telecommunications Association www.cellstream.com (c) 2011 CellStream, Inc. 1 www.cellstream.com (c) 2011 CellStream, Inc. 2 www.cellstream.com (c) 2011 CellStream, Inc. 3 www.cellstream.com (c) 2011 CellStream, Inc. 4 www.cellstream.com (c) 2011 CellStream, Inc. 5 Past vs. Present The Past – 20th Century The Present – 21st Century • Peer-to-Peer with broadcast • Many-to-Many with multicast • Mix of Analog and Digital • All media is digital – single • Producers supply transport Consumers • All media is connected • Peer-to-Peer is 1:1 • Many-to-Many is M:N o Traditional Telephone • Producers and Consumers • Broadcast is 1:N do both o Newspaper o CNN takes reports from Twitter o TV/Radio o End users send pictures and reports www.cellstream.com (c) 2011 CellStream, Inc. 6 Where are we in Phone Evolution? PHONE 1.0 PHONE 2.0 PHONE 3.0 Soft phone Your Phone Number Your Phone Number Your Phone Number represents where you represents you represents an IP Address – are (e.g. 972-747- regardless of where you independent of location 0300 is home, 214- are. and appliance you are 405-3708 is work) using (e.g. IP Phone, Cell Phone, PDA, Computer, Television, etc.) www.cellstream.com (c) 2011 CellStream, Inc. 7 Phone 3.X • Examples of Phone 3.0 are Skype, Google Talk, others on a PC. • Phone 3.1 – Skype on an iTouch • Phone 3.2 – Android OS from Google – a phone Centric OS that runs on cellular appliances • Phone 3.3 – Android OS from Google that runs on a Phone Appliance www.cellstream.com (c) 2011 CellStream, Inc. -

Breaking Through the Myths to Reality: a Future-Proof View Of
Breaking Through the Myths to Reality A Future-Proof View of Fiber Optic Inspection and Cleaning Dear Viewer: As presented at BICSI® in February- 2018, this seminar has video and animations that Edward J. Forrest, Jr. are not available as a .pdf file. If you would like the RMS(RaceMarketingServices) original version, please contact BICSI or the author. Bringing Ideas Together Caution: This Presentation is going to be controversial! IT IS BASED ON 2,500 YEARS OF SCIENCE AND PRODUCT DEVELOPMENT 2 Fact OR FICTION of Fiber Optic Cleaning and Inspection This seminarWE WILL mayDISCUSS contradictAND currentDEFINE: trends ➢ There➢ Cleaningand are what OTHER you’ve is notWAYS been important…BESIDES taught. VIDEO ➢ ➢➢“Automatic99.9%Debris➢ ➢ExistingA “Reagent FiberonS Detection” CIENTIFICthe standards, Optic surface Grade” ConnectorR isEALITY of such“good Isopropanola fiber… as enough”.is optic a is IECconnector“Pass 61300Let’sanI NSPECTIONanythingeffective- Fail”separate- 3surface-35, is is bettereasy are Factsfiberto is “Best determine thantwoto from optic understand nothing!-dimensional Practice”Fiction cleaner What we’veTwoif the ( ALL-Dimensional connector) been taught/bought/soldand is Structure“clean” over the last 30+Myth yearsfrom may“diameter”. Scientific not be the same Reality thing! 3 Fact OR FICTION of Fiber Optic Cleaning and Inspection ➢ A Fiber Optic Connector is a Two-Dimensional Structure ➢ 99.9% “Reagent Grade” Isopropanol is an effective fiber optic cleaner ➢ Cleaning is not important… anything is better than nothing! ➢ There are OTHER WAYS BESIDES VIDEO INSPECTION to determine if the connector is “clean” ➢ Debris on the surface of a fiber optic connector surface is two-dimensional “diameter”. ➢ “Automatic Detection” is “good enough”. -

File Organization and Management Com 214 Pdf
File organization and management com 214 pdf Continue 1 1 UNESCO-NIGERIA TECHNICAL - VOCATIONAL EDUCATION REVITALISATION PROJECT-PHASE II NATIONAL DIPLOMA IN COMPUTER TECHNOLOGY FILE Organization AND MANAGEMENT YEAR II- SE MESTER I THEORY Version 1: December 2 2 Content Table WEEK 1 File Concepts... 6 Bit:... 7 Binary figure... 8 Representation... 9 Transmission... 9 Storage... 9 Storage unit... 9 Abbreviation and symbol More than one bit, trit, dontcare, what? RfC on trivial bits Alternative Words WEEK 2 WEEK 3 Identification and File File System Aspects of File Systems File Names Metadata Hierarchical File Systems Means Secure Access WEEK 6 Types of File Systems Disk File Systems File Systems File Systems Transactional Systems File Systems Network File Systems Special Purpose File Systems 3 3 File Systems and Operating Systems Flat File Systems File Systems according to Unix-like Operating Systems File Systems according to Plan 9 from Bell Files under Microsoft Windows WEEK 7 File Storage Backup Files Purpose Storage Primary Storage Secondary Storage Third Storage Out Storage Features Storage Volatility Volatility UncertaintyAbility Availability Availability Performance Key Storage Technology Semiconductor Magnetic Paper Unusual Related Technology Connecting Network Connection Robotic Processing Robotic Processing File Processing Activity 4 4 Technology Execution Program interrupts secure mode and memory control mode Virtual Memory Operating Systems Linux and UNIX Microsoft Windows Mac OS X Special File Systems Journalized File Systems Graphic User Interfaces History Mainframes Microcomputers Microsoft Windows Plan Unix and Unix-like operating systems Mac OS X Real-time Operating Systems Built-in Core Development Hobby Systems Pre-Emptification 5 5 WEEK 1 THIS WEEK SPECIFIC LEARNING OUTCOMES To understand: The concept of the file in the computing concept, field, character, byte and bits in relation to File 5 6 6 Concept Files In this section, we will deal with the concepts of the file and their relationship. -

The 2016 SNIA Dictionary
A glossary of storage networking data, and information management terminology SNIA acknowledges and thanks its Voting Member Companies: Cisco Cryptsoft DDN Dell EMC Evaluator Group Fujitsu Hitachi HP Huawei IBM Intel Lenovo Macrosan Micron Microsoft NetApp Oracle Pure Storage Qlogic Samsung Toshiba Voting members as of 5.23.16 Storage Networking Industry Association Your Connection Is Here Welcome to the Storage Networking Industry Association (SNIA). Our mission is to lead the storage industry worldwide in developing and promoting standards, technologies, and educational services to empower organizations in the management of information. Made up of member companies spanning the global storage market, the SNIA connects the IT industry with end-to-end storage and information management solutions. From vendors, to channel partners, to end users, SNIA members are dedicated to providing the industry with a high level of knowledge exchange and thought leadership. An important part of our work is to deliver vendor-neutral and technology-agnostic information to the storage and data management industry to drive the advancement of IT technologies, standards, and education programs for all IT professionals. For more information visit: www.snia.org The Storage Networking Industry Association 4360 ArrowsWest Drive Colorado Springs, Colorado 80907, U.S.A. +1 719-694-1380 The 2016 SNIA Dictionary A glossary of storage networking, data, and information management terminology by the Storage Networking Industry Association The SNIA Dictionary contains terms and definitions related to storage and other information technologies, and is the storage networking industry's most comprehensive attempt to date to arrive at a common body of terminology for the technologies it represents. -

Chapter 1: Data Storage
Chapter 1: Data Storage 1.1 Bits and Their Storage 1.2 Main Memory 1.3 Mass Storage 1.4 Representing Information as Bit Patterns 1.5 The Binary System 1.6 Storing Integers 1.7 Storing Fractions 1.8 Data Compression 1.9 Communication Errors 1 Computer == 0 and 1 ? Hmm…every movie says so…. Chapter 2 2 Why I can’t see any 0 and 1 when opening up a computer?? Chapter 2 3 What’s really in the computer With the help of an oscilloscope (示波器) Chapter 2 4 HIGH Bits LOW Bit Binary Digit The basic unit of information in a computer A symbol whose meaning depends on the application at hand. Numeric value (1 or 0) Boolean value (true or false) Voltage (high or low) For TTL, high=5V, low=0V 5 More bits? kilobit (kbit) 103 210 megabit (Mbit) 106 220 gigabit (Gbit) 109 230 terabit (Tbit) 1012 240 petabit (Pbit) 1015 250 exabit (Ebit) 1018 260 zettabit (Zbit) 1021 270 6 Bit Patterns All data stored in a computer are represented by patterns of bits: Numbers Text characters Images Sound Anything else… 7 Now you know what’s a ‘bit’, and then? How to ‘compute’ bits? How to ‘implement’ it ? How to ‘store’ bit in a computer? Chapter 2 8 How to do computation on Bits? Chapter 2 9 Boolean Operations Boolean operation any operation that manipulates one or more true/false values (e.g. 0=true, 1=false) Can be used to operate on bits Specific operations AND OR XOR NOT 10 AND, OR, XOR 11 Implement the Boolean operation on a computer Chapter 2 12 Gates Gates devices that produce the outputs of Boolean operations when given -
Engilab Units 2018 V2.2
EngiLab Units 2021 v3.1 (v3.1.7864) User Manual www.engilab.com This page intentionally left blank. EngiLab Units 2021 v3.1 User Manual (c) 2021 EngiLab PC All rights reserved. No parts of this work may be reproduced in any form or by any means - graphic, electronic, or mechanical, including photocopying, recording, taping, or information storage and retrieval systems - without the written permission of the publisher. Products that are referred to in this document may be either trademarks and/or registered trademarks of the respective owners. The publisher and the author make no claim to these trademarks. While every precaution has been taken in the preparation of this document, the publisher and the author assume no responsibility for errors or omissions, or for damages resulting from the use of information contained in this document or from the use of programs and source code that may accompany it. In no event shall the publisher and the author be liable for any loss of profit or any other commercial damage caused or alleged to have been caused directly or indirectly by this document. "There are two possible outcomes: if the result confirms the Publisher hypothesis, then you've made a measurement. If the result is EngiLab PC contrary to the hypothesis, then you've made a discovery." Document type Enrico Fermi User Manual Program name EngiLab Units Program version v3.1.7864 Document version v1.0 Document release date July 13, 2021 This page intentionally left blank. Table of Contents V Table of Contents Chapter 1 Introduction to EngiLab Units 1 1 Overview .................................................................................................................................. -

Attacks on Quantum Key Distribution Protocols That Employ Non
Attacks on quantum key distribution protocols that employ non‐ITS authentication Christoph Pacher, Aysajan Abidin, Thomas Lorünser, Momtchil Peev, Rupert Ursin, Anton Zeilinger and Jan-Åke Larsson The self-archived postprint version of this journal article is available at Linköping University Institutional Repository (DiVA): http://urn.kb.se/resolve?urn=urn:nbn:se:liu:diva-91260 N.B.: When citing this work, cite the original publication. The original publication is available at www.springerlink.com: Pacher, C., Abidin, A., Lorünser, T., Peev, M., Ursin, R., Zeilinger, A., Larsson, J., (2016), Attacks on quantum key distribution protocols that employ non-ITS authentication, Quantum Information Processing, 15(1), 327-362. https://doi.org/10.1007/s11128-015-1160-4 Original publication available at: https://doi.org/10.1007/s11128-015-1160-4 Copyright: Springer Verlag (Germany) http://www.springerlink.com/?MUD=MP Attacks on quantum key distribution protocols that employ non-ITS authentication C Pacher1 · A Abidin2 · T Lor¨unser1 · M Peev1 · R Ursin3 · A Zeilinger3;4 · J-A˚ Larsson2 the date of receipt and acceptance should be inserted later Abstract We demonstrate how adversaries with large computing resources can break Quantum Key Distribution (QKD) protocols which employ a par- ticular message authentication code suggested previously. This authentication code, featuring low key consumption, is not Information-Theoretically Secure (ITS) since for each message the eavesdropper has intercepted she is able to send a different message from a set of messages that she can calculate by finding collisions of a cryptographic hash function. However, when this authentication code was introduced it was shown to prevent straightforward Man-In-The- Middle (MITM) attacks against QKD protocols. -
Data Storage
Chapter 1: Data Storage 1.1 Bits and Their Storage 1.2 Main Memory 1.3 Mass Storage 1.4 Representing Information as Bit Patterns 1.5 The Binary System 1.6 Storing Integers 1.7 Storing Fractions 1.8 Data Compression 1.9 Communication Errors 1 HIGH Bits LOW Bit Binary Digit A symbol whose meaning depends on the application at hand. Numeric value (1 or 0) Boolean value (true or false) Voltage (high or low) For TTL, high=5V, low=0V 2 More bits? kilobit (kbit) 103 210 megabit (Mbit) 106 220 gigabit (Gbit) 109 230 terabit (Tbit) 1012 240 petabit (Pbit) 1015 250 exabit (Ebit) 1018 260 zettabit (Zbit) 1021 270 3 Bit Patterns All data stored in a computer are represented by patterns of bits: Numbers Text characters Images Sound Anything else… 4 Boolean Operations Boolean operation any operation that manipulates one or more true/false values Can be used to operate on bits Specific operations AND OR XOR NOT 5 AND, OR, XOR 6 Gates Gates devices that produce the outputs of Boolean operations when given the operations‟ input values Often implemented as electronic circuits Provide the building blocks from which computers are constructed 7 AND, OR, XOR, NOT Gates Chapter 2 8 INPUT OUTPUT A B A NAND B NAND 0 0 1 0 1 1 1 0 1 NOR 1 1 0 XNOR 9 10 Store the bit What do we mean by „storing‟ the data? Bits in the computer at the i th second = Bits in the computer at the (i + 1) th second For example If the current state of the bit is „1‟, it should be still „1‟ at the next second 11 Flip-Flops Flip-Flop a circuit built from gates that can store one bit of data Two input lines One input line sets its stored value to 1 Another input line sets its stored value to 0 When both input lines are 0, the most recently stored value is preserved 12 Flip-Flops Illustrated X Y Z X Z 0 0 -- 0 1 0 Flip-Flop 1 0 1 Y 1 1 * 13 A Simple Flip-Flop Circuit 14 Setting to 1 – Step a. -

File Organization & Management
1 UNESCO -NIGERIA TECHNICAL & VOCATIONAL EDUCATION REVITALISATION PROJECT -PHASE II NATIONAL DIPLOMA IN COMPUTER TECHNOLOGY File Organization and Management YEAR II- SE MESTER I THEORY Version 1: December 2008 1 2 Table of Contents WEEK 1 File Concepts .................................................................................................................................6 Bit: . .................................................................................................................................................7 Binary digit .....................................................................................................................................8 Representation ...............................................................................................................................9 Transmission ..................................................................................................................................9 Storage ............................................................................................................................................9 Storage Unit .....................................................................................................................................9 Abbreviation and symbol ............................................................................................................ 10 More than one bit ......................................................................................................................... 11 Bit, trit, -

Gigabit Networking
GIGABIT NETWORKING Office of the Manager National Communications System February 1999 Communication Technologies, Inc. 503 Carlisle Drive, Suite 200 Herndon, Virginia 20170 703-318-7212 (Voice) 703-318-7214 (Fax) Web: www.comtechnologies.com GIGABIT NETWORKING Abstract Gigabit networking is expected to grow rapidly in popularity over the next several years. It is anticipated that as the communications infrastructure evolves to support gigabit speeds, new applications such as telemedicine, desktop videoconferencing, scientific modeling, and interactive telecollaboration will evolve to become important commonplace capabilities. These and many other bandwidth intensive applications have great potential to improve National Security/Emergency Preparedness (NS/EP) communications and event management activities. This report examines existing and emerging gigabit networking technologies, addresses issues associated with their applications, and discusses their applicability to NS/EP environments. 3 Table of Contents 1 INTRODUCTION......................................................................................................................... 7 1.1 NS/EP Event Characteristics................................................................................ 7 2 BACKGROUND ........................................................................................................................... 9 3 GIGABIT NETWORKING TECHNOLOGIES .........................................................................11 3.1 Fibre Channel ................................................................................................... -

A+ Guide to Managing & Maintaining Your PC, 8Th Edition
A+ Guide to Managing & Maintaining Your PC, 8th Edition Chapter 4 All About Motherboards Objectives • Learn about the different types and features of motherboards • Learn how to use setup BIOS and physical jumpers to configure a motherboard • Learn how to maintain a motherboard • Learn how to select, install, and replace a motherboard A+ Guide to Managing & Maintaining 2 Your PC, 8th Edition © Cengage Learning 2014 Part 2 Buses and Expansion Slots • Bus – System of pathways used for communication • Carried by bus: – Power, control signals, memory addresses, data • Data and instructions exist in binary – Only two states: on and off • Data path size: width of a data bus – Examples: 8-bit bus has eight wire (lines) to transmit A+ Guide to Managing & Maintaining 3 Your PC, 8th Edition © Cengage Learning 2014 •Bit: A bit is the basic unit of information in computing and digital communications. A bit can have only one of two values, and may therefore be physically implemented with a two-state device. The most common representation of these values are 0 and 1. The term bit is a contraction of binary digit. •Byte: A byte is a unit of digital information in computing and telecommunications that most commonly consists of eight bits. •bps: bit rate, bit per seconds •Hz: (Hertz): It is defined as the number of cycles per second of a periodic phenomenon. The hertz is equivalent to cycles per second. •Radio frequency radiation is usually measured in kilohertz (kHz), megahertz (MHz), or gigahertz (GHz) A+ Guide to Managing & Maintaining 4 Your PC, 8th -
Evolving TDM to IP
Evolving the Network to IP Services Andrew Walding, CellStream, Inc. www.cellstream.com ©2010 CellStream, Inc. All Rights Reserved 1 December 21, 1956 - February 9, 2010 ©2010 CellStream, Inc. All Rights Reserved 2 What will the Customer Demand? “Mobility” “Bandwidth” Performance Do they get the speed they are paying for? Do the games and video work? Is the phone better than the cell phone? This means “convergence” of voice, video, data with “Quality of Service” Need to define who the customer is ©2010 CellStream, Inc. All Rights Reserved 3 Connectivity Today - 2010 Does a POTS (Plain Old Telephone Service) Line mean: “truly connected”? 21st Century connectivity requires more than a POTS line -- requires a “pipe” to the information and services offered by the Internet Cloud The Internet ©2010 CellStream, Inc. All Rights Reserved 4 Past vs. Present The Past – 20th Century The Present – 21st Century Peer-to-Peer with broadcast Many-to-Many with multicast Mix of Analog and Digital All media is digital – single transport Producers supply Consumers All media is connected Peer-to-Peer is 1:1 Many-to-Many is M:N Traditional Telephone Producers and Consumers do Broadcast is 1:N both Newspaper CNN takes reports from TV/Radio Twitter End users send pictures and reports ©2010 CellStream, Inc. All Rights Reserved 5 “Take-Rate” The rate at which users adopt broadband Availa- bility to users ©2010 CellStream, Inc. All Rights Reserved 6 Broadband Adoption Rate Data Percentage Year Source Data Methodology 63% 2009 Pew Internet and Phone Survey of American American Life households and adults 64% 2009 Pike & Fischer Subscriber counts from industry reported information 63% 2008 Forrester Mail survey of American and Research Canadian households and adults 67% 2008 Nielsen Phone surveys Sources shown ©2010 CellStream, Inc.