Chapter 2: Instructions How We Talk to the Computer
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Low-Power Microprocessor Based on Stack Architecture
Girish Aramanekoppa Subbarao Low-power Microprocessor based on Stack Architecture Stack on based Microprocessor Low-power Master’s Thesis Low-power Microprocessor based on Stack Architecture Girish Aramanekoppa Subbarao Series of Master’s theses Department of Electrical and Information Technology LU/LTH-EIT 2015-464 Department of Electrical and Information Technology, http://www.eit.lth.se Faculty of Engineering, LTH, Lund University, September 2015. Department of Electrical and Information Technology Master of Science Thesis Low-power Microprocessor based on Stack Architecture Supervisors: Author: Prof. Joachim Rodrigues Girish Aramanekoppa Subbarao Prof. Anders Ard¨o Lund 2015 © The Department of Electrical and Information Technology Lund University Box 118, S-221 00 LUND SWEDEN This thesis is set in Computer Modern 10pt, with the LATEX Documentation System ©Girish Aramanekoppa Subbarao 2015 Printed in E-huset Lund, Sweden. Sep. 2015 Abstract There are many applications of microprocessors in embedded applications, where power efficiency becomes a critical requirement, e.g. wearable or mobile devices in healthcare, space instrumentation and handheld devices. One of the methods of achieving low power operation is by simplifying the device architecture. RISC/CISC processors consume considerable power because of their complexity, which is due to their multiplexer system connecting the register file to the func- tional units and their instruction pipeline system. On the other hand, the Stack machines are comparatively less complex due to their implied addressing to the top two registers of the stack and smaller operation codes. This makes the instruction and the address decoder circuit simple by eliminating the multiplex switches for read and write ports of the register file. -

Mi!!Lxlosalamos SCIENTIFIC LABORATORY
LA=8902-MS C3b ClC-l 4 REPORT COLLECTION REPRODUCTION COPY VAXNMS Benchmarking 1-’ > .— u) 9 g .— mi!!lxLOS ALAMOS SCIENTIFIC LABORATORY Post Office Box 1663 Los Alamos. New Mexico 87545 — wAifiimative Action/Equal Opportunity Employer b . l)lS(”L,\l\ll K “Thisreport wm prcpmd J, an xcttunt ,,1”wurk ,pmwrd by an dgmcy d the tlnitwl SIdtcs (kvcm. mm:. Ncit her t hc llniml SIJIL.. ( Lwcrnmcm nor any .gcncy tlhmd. nor my 08”Ihcif cmployccs. makci my wur,nly. mprcss w mphd. or JwImL.s m> lcg.d Iululity ur rcspmuhdily ltw Ilw w.cur- acy. .vmplctcncs. w uscftthtc>. ttt”any ml’ormdt ml. dpprdl us. prudu.i. w proccw didowd. or rep. resent%Ihd IIS us wuukl not mfrm$e priwtcly mvnd rqdtts. Itcl”crmcti herein 10 my sp.xi!l tom. mrcial ptotlucr. prtxcm. or S.rvskc hy tdc mmw. Irdcnmrl.. nmu(a.lurm. or dwrwi~.. does nut mmwsuily mnstitutc or reply its mdursmwnt. rccummcnddton. or favorin: by the llniwd States (“mvcmment ormy qxncy thctcd. rhc V!C$VSmd opinmm d .mthor% qmxd herein do nut net’. UMrily r;~lt or died lhow. ol”the llnttcd SIJIL.S( ;ovwnnwnt or my ugcncy lhure of. UNITED STATES .. DEPARTMENT OF ENERGY CONTRACT W-7405 -ENG. 36 . ... LA-8902-MS UC-32 Issued: July 1981 G- . VAX/VMS Benchmarking Larry Creel —. I . .._- -- ----- ,. .- .-. .: .- ,.. .. ., ..,..: , .. .., . ... ..... - .-, ..:. .. *._–: - . VAX/VMS BENCHMARKING by Larry Creel ABSTRACT Primary emphasis in this report is on the perform- ance of three Digital Equipment Corporation VAX-11/780 computers at the Los Alamos National Laboratory. Programs used in the study are part of the Laboratory’s set of benchmark programs. -
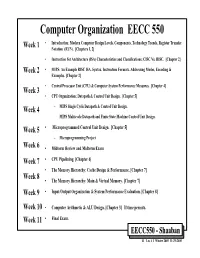
Computer Organization EECC 550 • Introduction: Modern Computer Design Levels, Components, Technology Trends, Register Transfer Week 1 Notation (RTN)
Computer Organization EECC 550 • Introduction: Modern Computer Design Levels, Components, Technology Trends, Register Transfer Week 1 Notation (RTN). [Chapters 1, 2] • Instruction Set Architecture (ISA) Characteristics and Classifications: CISC Vs. RISC. [Chapter 2] Week 2 • MIPS: An Example RISC ISA. Syntax, Instruction Formats, Addressing Modes, Encoding & Examples. [Chapter 2] • Central Processor Unit (CPU) & Computer System Performance Measures. [Chapter 4] Week 3 • CPU Organization: Datapath & Control Unit Design. [Chapter 5] Week 4 – MIPS Single Cycle Datapath & Control Unit Design. – MIPS Multicycle Datapath and Finite State Machine Control Unit Design. Week 5 • Microprogrammed Control Unit Design. [Chapter 5] – Microprogramming Project Week 6 • Midterm Review and Midterm Exam Week 7 • CPU Pipelining. [Chapter 6] • The Memory Hierarchy: Cache Design & Performance. [Chapter 7] Week 8 • The Memory Hierarchy: Main & Virtual Memory. [Chapter 7] Week 9 • Input/Output Organization & System Performance Evaluation. [Chapter 8] Week 10 • Computer Arithmetic & ALU Design. [Chapter 3] If time permits. Week 11 • Final Exam. EECC550 - Shaaban #1 Lec # 1 Winter 2005 11-29-2005 Computing System History/Trends + Instruction Set Architecture (ISA) Fundamentals • Computing Element Choices: – Computing Element Programmability – Spatial vs. Temporal Computing – Main Processor Types/Applications • General Purpose Processor Generations • The Von Neumann Computer Model • CPU Organization (Design) • Recent Trends in Computer Design/performance • Hierarchy -

Design and Construction of a PC-Based Stack Machine Simulator for Undergraduate Computer Science & Engineering Courses
Design and Construction of a PC-Based Stack Machine Simulator for Undergraduate Computer Science & Engineering Courses Fitratullah Khan and Sohail Anwar Department of Computer Science The University of Texas at Brownsville Brownsville, Texas 78520 Abstract - A senior level compiler design course in an top of the stack. The instructions pop operands from the stack undergraduate computer science and engineering program and push results back on to the stack. usually deals with teaching the students the basics of compiler The stack machine designed by the authors consists of a construction. A thorough understanding of the grammar of a code segment, a stack segment, an Arithmetic Logic Unit formal language and a compiler designed for it can only be (ALU), and four address registers. The code segment has the truly obtained by writing a working compiler for the language. program to be executed. The stack segment holds the A semester long feat of constructing the lexical, syntactic, intermediate data and addresses generated during program semantic, and code generation phases of a compiler exposes execution. A portion of the stack is set aside to store global the students to the inner workings of the compiler. The final data as well. The four address registers are pointers into the phase of testing the integrity and effectiveness of the code and stack segments: constructed compiler is both important and rewarding for a ! Instruction Pointer (IP) points to the next student. Furthermore, since the impetus of such an instruction to be executed, undergraduate course is to deal with the issues of compiler ! Stack Pointer (SP) points to the valid item on top construction rather than intricacies of different machines, it is of the stack, instructive to generate the code for a simple stack machine, ! Local Scope Pointer (LSP) points to the local incorporating a hardware stack, rather than dealing with a data declared within a procedure and the register-based machine such as a microcomputer. -

A Characterization of Processor Performance in the VAX-1 L/780
A Characterization of Processor Performance in the VAX-1 l/780 Joel S. Emer Douglas W. Clark Digital Equipment Corp. Digital Equipment Corp. 77 Reed Road 295 Foster Street Hudson, MA 01749 Littleton, MA 01460 ABSTRACT effect of many architectural and implementation features. This paper reports the results of a study of VAX- llR80 processor performance using a novel hardware Prior related work includes studies of opcode monitoring technique. A micro-PC histogram frequency and other features of instruction- monitor was buiit for these measurements. It kee s a processing [lo. 11,15,161; some studies report timing count of the number of microcode cycles execute z( at Information as well [l, 4,121. each microcode location. Measurement ex eriments were performed on live timesharing wor i loads as After describing our methods and workloads in well as on synthetic workloads of several types. The Section 2, we will re ort the frequencies of various histogram counts allow the calculation of the processor events in 5 ections 3 and 4. Section 5 frequency of various architectural events, such as the resents the complete, detailed timing results, and frequency of different types of opcodes and operand !!Iection 6 concludes the paper. specifiers, as well as the frequency of some im lementation-s ecific events, such as translation bu h er misses. ?phe measurement technique also yields the amount of processing time spent, in various 2. DEFINITIONS AND METHODS activities, such as ordinary microcode computation, memory management, and processor stalls of 2.1 VAX-l l/780 Structure different kinds. This paper reports in detail the amount of time the “average’ VAX instruction The llf780 processor is composed of two major spends in these activities. -

The Implementation of Prolog Via VAX 8600 Microcode ABSTRACT
The Implementation of Prolog via VAX 8600 Microcode Jeff Gee,Stephen W. Melvin, Yale N. Patt Computer Science Division University of California Berkeley, CA 94720 ABSTRACT VAX 8600 is a 32 bit computer designed with ECL macrocell arrays. Figure 1 shows a simplified block diagram of the 8600. We have implemented a high performance Prolog engine by The cycle time of the 8600 is 80 nanoseconds. directly executing in microcode the constructs of Warren’s Abstract Machine. The imulemention vehicle is the VAX 8600 computer. The VAX 8600 is a general purpose processor Vimal Address containing 8K words of writable control store. In our system, I each of the Warren Abstract Machine instructions is implemented as a VAX 8600 machine level instruction. Other Prolog built-ins are either implemented directly in microcode or executed by the general VAX instruction set. Initial results indicate that. our system is the fastest implementation of Prolog on a commercrally available general purpose processor. 1. Introduction Various models of execution have been investigated to attain the high performance execution of Prolog programs. Usually, Figure 1. Simplified Block Diagram of the VAX 8600 this involves compiling the Prolog program first into an intermediate form referred to as the Warren Abstract Machine (WAM) instruction set [l]. Execution of WAM instructions often follow one of two methods: they are executed directly by a The 8600 consists of six subprocessors: the EBOX. IBOX, special purpose processor, or they are software emulated via the FBOX. MBOX, Console. and UO adamer. Each of the seuarate machine language of a general purpose computer. -
VAX VMS at 20
1977–1997... and beyond Nothing Stops It! Of all the winning attributes of the OpenVMS operating system, perhaps its key success factor is its evolutionary spirit. Some would say OpenVMS was revolutionary. But I would prefer to call it evolutionary because its transition has been peaceful and constructive. Over a 20-year period, OpenVMS has experienced evolution in five arenas. First, it evolved from a system running on some 20 printed circuit boards to a single chip. Second, it evolved from being proprietary to open. Third, it evolved from running on CISC-based VAX to RISC-based Alpha systems. Fourth, VMS evolved from being primarily a technical oper- ating system, to a commercial operat- ing system, to a high availability mission-critical commercial operating system. And fifth, VMS evolved from time-sharing to a workstation environment, to a client/server computing style environment. The hardware has experienced a similar evolution. Just as the 16-bit PDP systems laid the groundwork for the VAX platform, VAX laid the groundwork for Alpha—the industry’s leading 64-bit systems. While the platforms have grown and changed, the success continues. Today, OpenVMS is the most flexible and adaptable operating system on the planet. What start- ed out as the concept of ‘Starlet’ in 1975 is moving into ‘Galaxy’ for the 21st century. And like the universe, there is no end in sight. —Jesse Lipcon Vice President of UNIX and OpenVMS Systems Business Unit TABLE OF CONTENTS CHAPTER I Changing the Face of Computing 4 CHAPTER II Setting the Stage 6 CHAPTER -

Vincent M. Weaver Sally A. Mckee
Optimizing for Size: Exploring the Limits of Code Density Sally A. McKee Vincent M. Weaver ASPLOS XIV Poster Session, 8 March 2009 Cornell University Chalmers University of Technology Abstract Hand-Optimized Assembly Results Architectural Size Correlations 0.9020 Minimum possible instruction size Reductions in instruction count can improve cache and bandwidth utiliza- 0.8652 Number of integer registers tion, lower power consumption, and increase overall performance. Nonethe- Total Size of Executable VLIW 2560 RISC less, code density is often overlooked when studying processor architectures. 2048 CISC 0.6623 Architecture has a zero register embedded 1536 8/16-bit 0.5845 Bit-width bytes 1024 We hand-optimize an embedded benchmark for size in assembly language -0.4366 Hardware divide in ALU on 20 different instruction set architectures and investigate the architectural 512 features that contribute most heavily to code density. 0 0.4385 Number of operands in each instruction arm ppc vax sh3 z80 ia64 6502 mips s390 i386 alphaparisc sparc m88k m68k thumb avr32 -0.3356 Unaligned load/store available x86_64 crisv32pdp-11 0.2773 Year the architecture was introduced 256 Size of LZSS Decompression Code VLIW -0.2597 Auto-incrementing addressing scheme Background RISC CISC 192 embedded -0.2597 Hardware status flags (zero/overflow/etc.) 128 8/16-bit bytes -0.1252 Little or Big endian 64 The 20 architectures investigated can be broadly broken into 5 categories: -0.0487 Branch delay slot 0 -0.0079 Maximum possible instruction size Instr Length Opcode arm ppc vax z80 sh3 ia64 mips s390 6502 i386 Type Represented Architectures alpha parisc sparc m88k m68kthumb avr32 (bytes) Args pdp-11 x86_64crisv32 VLIW ia64 16/3 3 Size of String-Search Code VLIW Other Considerations alpha, arm, m88k, mips 256 RISC RISC 4 3 CISC pa-risc, ppc, sparc 192 embedded 128 8/16-bit System libraries and compiler overhead can overshadow the effects of size bytes CISC m68k, s390, vax, x86, x86 64 1-54 2 64 optimization, increasing memory footprint by several orders of magnitude. -

In Using the GNU Compiler Collection (GCC)
Using the GNU Compiler Collection For gcc version 6.1.0 (GCC) Richard M. Stallman and the GCC Developer Community Published by: GNU Press Website: http://www.gnupress.org a division of the General: [email protected] Free Software Foundation Orders: [email protected] 51 Franklin Street, Fifth Floor Tel 617-542-5942 Boston, MA 02110-1301 USA Fax 617-542-2652 Last printed October 2003 for GCC 3.3.1. Printed copies are available for $45 each. Copyright c 1988-2016 Free Software Foundation, Inc. Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.3 or any later version published by the Free Software Foundation; with the Invariant Sections being \Funding Free Software", the Front-Cover Texts being (a) (see below), and with the Back-Cover Texts being (b) (see below). A copy of the license is included in the section entitled \GNU Free Documentation License". (a) The FSF's Front-Cover Text is: A GNU Manual (b) The FSF's Back-Cover Text is: You have freedom to copy and modify this GNU Manual, like GNU software. Copies published by the Free Software Foundation raise funds for GNU development. i Short Contents Introduction ::::::::::::::::::::::::::::::::::::::::::::: 1 1 Programming Languages Supported by GCC ::::::::::::::: 3 2 Language Standards Supported by GCC :::::::::::::::::: 5 3 GCC Command Options ::::::::::::::::::::::::::::::: 9 4 C Implementation-Defined Behavior :::::::::::::::::::: 373 5 C++ Implementation-Defined Behavior ::::::::::::::::: 381 6 Extensions to -

EECS 470 Lecture 2 Instruction Set Architecture
© Wenisch 2007 -- Portions © Austin, Brehob, Falsafi, Hill, Hoe, Lipasti, Martin, Roth, Shen, Smith, Sohi, Tyson, Vijaykumar EECS 470 Lecture 2 Instruction Set Architecture Fall 2007 Prof. Thomas Wenisch http://www.eecs.umich.edu/courses/eecs470/ Slides developed in part by Profs. Austin, Brehob, Falsafi, Hill, Hoe, Lipasti, Shen, Smith, Sohi, Tyson, Vijaykumar, and Wenisch of Carnegie Mellon University, Purdue University, University of Michigan, and University of Wisconsin. Lecture 2 EECS 470 Slide 1 © Wenisch 2007 -- Portions © Austin, Brehob, Falsafi, Hill, Hoe, Lipasti, Martin, Roth, Shen, Smith, Sohi, Tyson, Vijaykumar Announcements Reminders: HW # 1 due Friday 9/14 Hand in at start of discussion Programming assignment #1 due Friday 9/14 Electronic hand‐in by midnight Lecture 2 EECS 470 Slide 2 © Wenisch 2007 -- Portions © Austin, Brehob, Falsafi, Hill, Hoe, Lipasti, Martin, Roth, Shen, Smith, Sohi, Tyson, Vijaykumar Readings For today: Task of the Referee. A.J. Smith H & P Chapter 1 H & P Appendix B For Wednesday: Cramming More Components onto ICs. GEG.E. Moore H & P Chapter A.1‐A.6 Lecture 2 EECS 470 Slide 3 © Wenisch 2007 -- Portions © Austin, Brehob, Falsafi, Hill, Hoe, Lipasti, Martin, Roth, Shen, Smith, Sohi, Tyson, Vijaykumar Performance – Key Points Amdahl’s law Soverall = 1 / ( (1-f)+ f/S ) Iron law Time Instructions Cycles Time = × × Program Program Instruction Cycle AiThiAveraging Techniques Arithmetic Harmonic Geometric Time Rates Ratios n n 1 n n 1 n ∑i=1Timei ∏Ratio i ∑i=1 n i =1 Rate i Lecture 2 EECS 470 Slide 4 © Wenisch 2007 -- Portions © Austin, Brehob, Falsafi, Hill, Hoe, Lipasti, Martin, Roth, Shen, Smith, Sohi, Tyson, Vijaykumar Digital System Cost Cost is also a key design constraint Architecture is about trade‐offs Cost plays a major role Huge difference between Cost & Price E.g., Higher Price Æ Lower Volume Æ Higher Cost Æ Higher Price Direct Cost Gross Margin List vs. -

GCC for Embedded Systems
GCC for Embedded Systems Ayal Zaks IBM Haifa Research Lab [email protected] http://www.haifa.il.ibm.com/dept/svt/code_compiler.html IBM Haifa Research Lab IBM Haifa Research Lab GCC for Embedded Systems – Talk Goals GCC for Embedded Systems – why GCC? What (R&D) are we doing in GCC? Where can you learn more? 2 IBM Haifa Research Lab GCC for Embedded Systems - Talk Layout 1. GCC – development: open community product of FSF 2. GCC – recent contributions from IBM Haifa Vectorization (GCC 4.0) Modulo scheduling (GCC 4.0) Inter-Procedural constant propagation (GCC 4.1) Data-layout optimizations (GCC 4.3) 3. GCC – performance for embedded: EEMBC 4. GCC – research: HiPEAC 3 IBM Haifa Research Lab GCC development – Mission Statement (from http://gcc.gnu.org/gccmission.html) GCC development is a part of the GNU Project , aiming to improve the compiler used in the GNU system including the GNU/Linux® variant. The GCC development effort uses an open development environment and supports many other platforms in order to foster a world-class optimizing compiler , to attract a larger team of developers, to ensure that GCC and the GNU system work on multiple architectures and diverse environments , and to more thoroughly test and extend the features of GCC. 4 IBM Haifa Research Lab GNU Compiler Collection Advantages Consistent across large number of targets (target is architecture plus operating system) Very good warnings aid porting to new targets Free software project: licenses protect GCC as free software while allowing users to build proprietary -

Code Generation for a Stack Machine •
CS 410 Lecture Outline Code Generation for a Stack Machine • a simple language • activation trees again • a simple implementation model: the stack machine • stack machine implementation of the simple • language – design of activation records – code generation Note: these lecture notes are by Alex Aiken for his compiler class at UC Berkeley with minor modifications made for local use. 1 CS 410 A Small Language A language with integers and integer operations: • P D; P D → | D def id(ARGS)=E; → ARGS id, ARGS id → | E int id if E = E then E else E → | | 1 2 3 4 | E1 + E2 E1 E2 id(E1,...,En) | − | The first function definition f is the “main” routine. • Running the program on input i means compute f(i). • Computing the ith Fibonacci number: • def fib(x) = if x = 1 then 0 else if x = 2 then 1 else fib(x-1) + fib(x-2) 2 CS 410 Review: Activation Trees The activation tree for a run of a program is a graph • of the function calls. For fib(4), the activation tree is: • fib(4) fib(3) fib(2) fib(2) fib(1) Activation records are managed using a runtime stack. • At any point during execution, the activation stack • describes some path starting from the root of the ac- tivation tree. 3 CS 410 A Stack Machine A stack machine evaluates one expression at a time. • The value of an expression is stored in a • distinguished register called the accumulator (or acc). A stack is used to hold intermediate results. • To evaluate an expression op(e ,...,e ): • 1 n 1.