GNOME 2.0 Desktop for the Solaris Operating Environment Troubleshooting Guide
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Desktop Migration and Administration Guide
Red Hat Enterprise Linux 7 Desktop Migration and Administration Guide GNOME 3 desktop migration planning, deployment, configuration, and administration in RHEL 7 Last Updated: 2021-05-05 Red Hat Enterprise Linux 7 Desktop Migration and Administration Guide GNOME 3 desktop migration planning, deployment, configuration, and administration in RHEL 7 Marie Doleželová Red Hat Customer Content Services [email protected] Petr Kovář Red Hat Customer Content Services [email protected] Jana Heves Red Hat Customer Content Services Legal Notice Copyright © 2018 Red Hat, Inc. This document is licensed by Red Hat under the Creative Commons Attribution-ShareAlike 3.0 Unported License. If you distribute this document, or a modified version of it, you must provide attribution to Red Hat, Inc. and provide a link to the original. If the document is modified, all Red Hat trademarks must be removed. Red Hat, as the licensor of this document, waives the right to enforce, and agrees not to assert, Section 4d of CC-BY-SA to the fullest extent permitted by applicable law. Red Hat, Red Hat Enterprise Linux, the Shadowman logo, the Red Hat logo, JBoss, OpenShift, Fedora, the Infinity logo, and RHCE are trademarks of Red Hat, Inc., registered in the United States and other countries. Linux ® is the registered trademark of Linus Torvalds in the United States and other countries. Java ® is a registered trademark of Oracle and/or its affiliates. XFS ® is a trademark of Silicon Graphics International Corp. or its subsidiaries in the United States and/or other countries. MySQL ® is a registered trademark of MySQL AB in the United States, the European Union and other countries. -

B.Casselman,Mathematical Illustrations,A Manual Of
1 0 0 setrgbcolor newpath 0 0 1 0 360 arc stroke newpath Preface 1 0 1 0 360 arc stroke This book will show how to use PostScript for producing mathematical graphics, at several levels of sophistication. It includes also some discussion of the mathematics involved in computer graphics as well as a few remarks about good style in mathematical illustration. To explain mathematics well often requires good illustrations, and computers in our age have changed drastically the potential of graphical output for this purpose. There are many aspects to this change. The most apparent is that computers allow one to produce graphics output of sheer volume never before imagined. A less obvious one is that they have made it possible for amateurs to produce their own illustrations of professional quality. Possible, but not easy, and certainly not as easy as it is to produce their own mathematical writing with Donald Knuth’s program TEX. In spite of the advances in technology over the past 50 years, it is still not a trivial matter to come up routinely with figures that show exactly what you want them to show, exactly where you want them to show it. This is to some extent inevitable—pictures at their best contain a lot of information, and almost by definition this means that they are capable of wide variety. It is surely not possible to come up with a really simple tool that will let you create easily all the graphics you want to create—the range of possibilities is just too large. -
Nix on SHARCNET
Nix on SHARCNET Tyson Whitehead May 14, 2015 Nix Overview An enterprise approach to package management I a package is a specific piece of code compiled in a specific way I each package is entirely self contained and does not change I each users select what packages they want and gets a custom enviornment https://nixos.org/nix Ships with several thousand packages already created https://nixos.org/nixos/packages.html SHARCNET What this adds to SHARCNET I each user can have their own custom environments I environments should work everywhere (closed with no external dependencies) I several thousand new and newer packages Current issues (first is permanent, second will likely be resolved) I newer glibc requires kernel 2.6.32 so no requin I package can be used but not installed/removed on viz/vdi https: //sourceware.org/ml/libc-alpha/2014-01/msg00511.html Enabling Nix Nix is installed under /home/nixbld on SHARCNET. Enable for a single sessiong by running source /home/nixbld/profile.d/nix-profile.sh To always enable add this to the end of ~/.bash_profile echo source /home/nixbld/profile.d/nix-profile.sh \ >> ~/.bash_profile Reseting Nix A basic reset is done by removing all .nix* files from your home directory rm -fr ~/.nix* A complete reset done by remove your Nix per-user directories rm -fr /home/nixbld/var/nix/profile/per-user/$USER rm -fr /home/nixbld/var/nix/gcroots/per-user/$USER The nix-profile.sh script will re-create these with the defaults next time it runs. Environment The nix-env commands maintains your environments I query packages (available and installed) I create a new environment from current one by adding packages I create a new environment from current one by removing packages I switching between existing environments I delete unused environements Querying Packages The nix-env {--query | -q} .. -

Infrastructural Requirements for a Privacy Preserving Internet
Infrastructural Requirements for a Privacy Preserving Internet Brad Rosen Fall 2003 Professor Feigenbaum Sensitive Information in the Wired World Abstract With much gusto, firms routinely sell “privacy enhancing technology” to enrich the web experience of typical consumers. Standards bodies have thrown in their hats, and even large organizations such as AT&T and IBM have gotten involved. Still, it seems no one has asked the question, “Are we trying to save a sinking ship?” “Are our ultimate goals actually achievable given the current framework?” This paper tries to examine the necessary infrastructure to support the goals of privacy enhancing technologies and the reasoning behind them. Contents 1 Introduction 2 2 Definition of Terms 3 2.1 User-Centric Terms . 3 2.2 Technical Terms . 4 2.3 Hypothetical Terms . 5 3 Privacy and Annoyances 5 3.1 Outflows – Encroachment . 6 3.2 Inflows – Annoyances . 6 3.3 Relevance . 7 4 Privacy Preserving vs. Privacy Enhancing 7 1 5 Current Infrastructure 8 5.1 Overview . 8 5.2 DNS Request . 8 5.3 Routing . 9 5.4 Website Navigation . 9 5.5 Sensitive Data-Handling . 9 5.6 Infrastructural Details . 10 5.6.1 IPv4 . 10 5.6.2 Java/ECMA Script . 10 5.6.3 Applets/ActiveX . 10 5.6.4 (E)SMTP . 10 6 Next-Generation Infrastructure 11 6.1 Overview . 11 6.2 DNS Request . 11 6.3 Routing . 12 6.4 Website Navigation . 12 6.5 Sensitive Data-Handling . 12 6.6 Infrastructural Details . 13 6.6.1 IPv6 . 13 6.6.2 Java/ECMA Script . 13 6.6.3 Applets/ActiveX . -
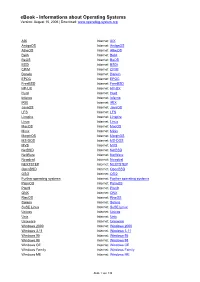
Ebook - Informations About Operating Systems Version: August 15, 2006 | Download
eBook - Informations about Operating Systems Version: August 15, 2006 | Download: www.operating-system.org AIX Internet: AIX AmigaOS Internet: AmigaOS AtheOS Internet: AtheOS BeIA Internet: BeIA BeOS Internet: BeOS BSDi Internet: BSDi CP/M Internet: CP/M Darwin Internet: Darwin EPOC Internet: EPOC FreeBSD Internet: FreeBSD HP-UX Internet: HP-UX Hurd Internet: Hurd Inferno Internet: Inferno IRIX Internet: IRIX JavaOS Internet: JavaOS LFS Internet: LFS Linspire Internet: Linspire Linux Internet: Linux MacOS Internet: MacOS Minix Internet: Minix MorphOS Internet: MorphOS MS-DOS Internet: MS-DOS MVS Internet: MVS NetBSD Internet: NetBSD NetWare Internet: NetWare Newdeal Internet: Newdeal NEXTSTEP Internet: NEXTSTEP OpenBSD Internet: OpenBSD OS/2 Internet: OS/2 Further operating systems Internet: Further operating systems PalmOS Internet: PalmOS Plan9 Internet: Plan9 QNX Internet: QNX RiscOS Internet: RiscOS Solaris Internet: Solaris SuSE Linux Internet: SuSE Linux Unicos Internet: Unicos Unix Internet: Unix Unixware Internet: Unixware Windows 2000 Internet: Windows 2000 Windows 3.11 Internet: Windows 3.11 Windows 95 Internet: Windows 95 Windows 98 Internet: Windows 98 Windows CE Internet: Windows CE Windows Family Internet: Windows Family Windows ME Internet: Windows ME Seite 1 von 138 eBook - Informations about Operating Systems Version: August 15, 2006 | Download: www.operating-system.org Windows NT 3.1 Internet: Windows NT 3.1 Windows NT 4.0 Internet: Windows NT 4.0 Windows Server 2003 Internet: Windows Server 2003 Windows Vista Internet: Windows Vista Windows XP Internet: Windows XP Apple - Company Internet: Apple - Company AT&T - Company Internet: AT&T - Company Be Inc. - Company Internet: Be Inc. - Company BSD Family Internet: BSD Family Cray Inc. -

An Introduction to the X Window System Introduction to X's Anatomy
An Introduction to the X Window System Robert Lupton This is a limited and partisan introduction to ‘The X Window System’, which is widely but improperly known as X-windows, specifically to version 11 (‘X11’). The intention of the X-project has been to provide ‘tools not rules’, which allows their basic system to appear in a very large number of confusing guises. This document assumes that you are using the configuration that I set up at Peyton Hall † There are helpful manual entries under X and Xserver, as well as for individual utilities such as xterm. You may need to add /usr/princeton/X11/man to your MANPATH to read the X manpages. This is the first draft of this document, so I’d be very grateful for any comments or criticisms. Introduction to X’s Anatomy X consists of three parts: The server The part that knows about the hardware and how to draw lines and write characters. The Clients Such things as terminal emulators, dvi previewers, and clocks and The Window Manager A programme which handles negotiations between the different clients as they fight for screen space, colours, and sunlight. Another fundamental X-concept is that of resources, which is how X describes any- thing that a client might want to specify; common examples would be fonts, colours (both foreground and background), and position on the screen. Keys X can, and usually does, use a number of special keys. You are familiar with the way that <shift>a and <ctrl>a are different from a; in X this sensitivity extends to things like mouse buttons that you might not normally think of as case-sensitive. -

Optical Character Recognition - a Combined ANN/HMM Approach
Optical Character Recognition - A Combined ANN/HMM Approach Dissertation submitted to the Department of Computer Science Technical University of Kaiserslautern for the fulfillment of the requirements for the doctoral degree Doctor of Engineering (Dr.-Ing.) by Sheikh Faisal Rashid Dean: Prof. Dr. Klaus Schneider Thesis supervisors: Prof. Dr. Thomas Breuel, TU Kaiserslautern Prof. Dr. Andreas Dengel, TU Kaiserslautern Chair of supervisory committee: Prof. Dr. Karsten Berns, TU Kaiserslautern Kaiserslautern, 11 July, 2014 D 386 Abstract Optical character recognition (OCR) of machine printed text is ubiquitously considered as a solved problem. However, error free OCR of degraded (broken and merged) and noisy text is still challenging for modern OCR systems. OCR of degraded text with high accuracy is very important due to many applications in business, industry and large scale document digitization projects. This thesis presents a new OCR method for degraded text recognition by introducing a combined ANN/HMM OCR approach. The approach provides significantly better performance in comparison with state-of-the-art HMM based OCR methods and existing open source OCR systems. In addition, the thesis introduces novel applications of ANNs and HMMs for document image preprocessing and recognition of low resolution text. Furthermore, the thesis provides psychophysical experiments to determine the effect of letter permutation in visual word recognition of Latin and Cursive script languages. HMMs and ANNs are widely employed pattern recognition paradigms and have been used in numerous pattern classification problems. This work presents a simple and novel method for combining the HMMs and ANNs in application to segmentation free OCR of degraded text. HMMs and ANNs are powerful pattern recognition strategies and their combination is interesting to improve current state-of-the-art research in OCR. -

Font HOWTO Font HOWTO
Font HOWTO Font HOWTO Table of Contents Font HOWTO......................................................................................................................................................1 Donovan Rebbechi, elflord@panix.com..................................................................................................1 1.Introduction...........................................................................................................................................1 2.Fonts 101 −− A Quick Introduction to Fonts........................................................................................1 3.Fonts 102 −− Typography.....................................................................................................................1 4.Making Fonts Available To X..............................................................................................................1 5.Making Fonts Available To Ghostscript...............................................................................................1 6.True Type to Type1 Conversion...........................................................................................................2 7.WYSIWYG Publishing and Fonts........................................................................................................2 8.TeX / LaTeX.........................................................................................................................................2 9.Getting Fonts For Linux.......................................................................................................................2 -

The Linux Command Line
The Linux Command Line Fifth Internet Edition William Shotts A LinuxCommand.org Book Copyright ©2008-2019, William E. Shotts, Jr. This work is licensed under the Creative Commons Attribution-Noncommercial-No De- rivative Works 3.0 United States License. To view a copy of this license, visit the link above or send a letter to Creative Commons, PO Box 1866, Mountain View, CA 94042. A version of this book is also available in printed form, published by No Starch Press. Copies may be purchased wherever fine books are sold. No Starch Press also offers elec- tronic formats for popular e-readers. They can be reached at: https://www.nostarch.com. Linux® is the registered trademark of Linus Torvalds. All other trademarks belong to their respective owners. This book is part of the LinuxCommand.org project, a site for Linux education and advo- cacy devoted to helping users of legacy operating systems migrate into the future. You may contact the LinuxCommand.org project at http://linuxcommand.org. Release History Version Date Description 19.01A January 28, 2019 Fifth Internet Edition (Corrected TOC) 19.01 January 17, 2019 Fifth Internet Edition. 17.10 October 19, 2017 Fourth Internet Edition. 16.07 July 28, 2016 Third Internet Edition. 13.07 July 6, 2013 Second Internet Edition. 09.12 December 14, 2009 First Internet Edition. Table of Contents Introduction....................................................................................................xvi Why Use the Command Line?......................................................................................xvi -

Ghostscript and Mupdf Status Openprinting Summit April 2016
Ghostscript and MuPDF Status OpenPrinting Summit April 2016 Michael Vrhel, Ph.D. Artifex Software Inc. San Rafael CA Outline Ghostscript overview What is new with Ghostscript MuPDF overview What is new with MuPDF MuPDF vs Ghostscript MuJS, GSView The Basics Ghostscript is a document conversion and rendering engine. Written in C ANSI 1989 standard (ANS X3.159-1989) Essential component of the Linux printing pipeline. Dual AGPL/Proprietary licensed. Artifex owns the copyright. Source and documentation available at www.ghostscript.com Graphical Overview PostScript PCL5e/c with PDF 1.7 XPS Level 3 GL/2 and RTL PCLXL Ghostscript Graphics Library High level Printer drivers: Raster output API: Output drivers: Inkjet TIFF PSwrite PDFwrite Laser JPEG XPSwrite Custom etc. CUPS Devices Understanding devices is a major key to understanding Ghostscript. Devices can have high-level functionality. e.g. pdfwrite can handle text, images, patterns, shading, fills, strokes and transparency directly. Graphics library has “default” operations. e.g. text turns into bitmaps, images decomposed into rectangles. In embedded environments, calls into hardware can be made. Raster devices require the graphics library to do all the rendering. Relevant Changes to GS since last meeting…. A substantial revision of the build system and GhostPDL directory structure (9.18) GhostPCL and GhostXPS "products" are now built by the Ghostscript build system "proper" rather than having their own builds (9.18) New method of internally inserting devices into the device chain developed. Allows easier implementation of “filter” devices (9.18) Implementation of "-dFirstPage"/"-dLastPage" with all input languages (9.18) Relevant Changes to GS since last meeting…. -

License Agreement
TAGARNO MOVE, FHD PRESTIGE/TREND/UNO License Agreement Version 2021.08.19 Table of Contents Table of Contents License Agreement ................................................................................................................................................ 4 Open Source & 3rd-party Licenses, MOVE ............................................................................................................ 4 Open Source & 3rd-party Licenses, PRESTIGE/TREND/UNO ................................................................................. 4 atk ...................................................................................................................................................................... 5 base-files ............................................................................................................................................................ 5 base-passwd ...................................................................................................................................................... 5 BSP (Board Support Package) ............................................................................................................................ 5 busybox.............................................................................................................................................................. 5 bzip2 ................................................................................................................................................................. -

Bienvenue Sur L'aide En Ligne Du Simulateur Affranchigo
AIDE EN LIGNE DU SIMULATEUR Bienvenue sur l’aide en ligne du simulateur AFFRANCHIGO A. Aide à la navigation Le développement de ce site s'efforce de respecter au mieux les critères d'accessibilité de façon à faciliter la consultation du site pour tous. Si malgré nos efforts, vous rencontrez des difficultés à consulter certaines informations, n'hésitez pas à nous en faire part. 1. Logo du haut de page Le logo La Poste du haut de page permet d’accéder à l’espace «Solutions Business» pour affranchir votre courrier entreprise sur le portail www.laposte.fr. 2. Présentation du contenu-Téléchargement La plus grande partie du contenu est disponible en format HTML. Vous trouverez des documents téléchargeables au format RTF. Ce format est lisible par tous les sites bureautiques. Vous trouverez également des documents téléchargeables au format PDF. Si vous n'avez pas Acrobat Reader, vous pouvez le télécharger sur le site d'Adobe : télécharger Acrobat Reader. Ou alors, vous pouvez transformer les PDF en format HTML classique en utilisant le moteur de conversion en ligne d'Adobe. Pour cela, copier l'adresse du lien vers le fichier en PDF et collez-la dans le champ prévu à cet effet sur l'outil de conversion en ligne d'Adobe. 3. Raccourcis claviers Par ailleurs, des raccourcis claviers ont été programmés sur la totalité du site : − «s» vous amène sur le bouton «suivant» − «p» vous amène sur le bouton «précédent» Les combinaisons de touches pour valider ces raccourcis diffèrent selon les navigateurs, c'est pourquoi nous listons ci-dessous les procédures