TR 187 020 V1.1.1 (2011-05) Technical Report
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Iso 7010:2019
INTERNATIONAL ISO STANDARD 7010 Third edition 2019-07 Graphical symbols — Safety colours and safety signs — Registered safety signs Symboles graphiques — Couleurs de sécurité et signaux de sécurité — Signaux de sécurité enregistrés Reference number ISO 7010:2019(E) © ISO 2019 ISO 7010:2019(E) COPYRIGHT PROTECTED DOCUMENT © ISO 2019 All rights reserved. Unless otherwise specified, or required in the context of its implementation, no part of this publication may be reproduced or utilized otherwise in any form or by any means, electronic or mechanical, including photocopying, or posting on the internet or an intranet, without prior written permission. Permission can be requested from either ISO at the address below or ISO’s member body in the country of the requester. ISO copyright office CP 401 • Ch. de Blandonnet 8 CH-1214 Vernier, Geneva Phone: +41 22 749 01 11 Fax:Website: +41 22www.iso.org 749 09 47 Email: [email protected] iiPublished in Switzerland © ISO 2019 – All rights reserved ISO 7010:2019(E) Contents Page Foreword ........................................................................................................................................................................................................................................iv Introduction ................................................................................................................................................................................................................................vi 1 Scope ................................................................................................................................................................................................................................ -
Guidelines for Securing Radio Frequency Identification (RFID) Systems
Special Publication 800-98 Guidelines for Securing Radio Frequency Identification (RFID) Systems Recommendations of the National Institute of Standards and Technology Tom Karygiannis Bernard Eydt Greg Barber Lynn Bunn Ted Phillips NIST Special Publication 800-98 Guidelines for Securing Radio Frequency Identification (RFID) Systems Recommendations of the National Institute of Standards and Technology Tom Karygiannis Bernard Eydt Greg Barber Lynn Bunn Ted Phillips C O M P U T E R S E C U R I T Y Computer Security Division Information Technology Laboratory National Institute of Standards and Technology Gaithersburg, MD 20899-8930 April 2007 US Department of Commerce Carlos M. Gutierrez, Secretary Technology Administration Robert C. Cresanti, Under Secretary of Commerce for Technology National Institute of Standards and Technology William Jeffrey, Director GUIDELINES FOR SECURING RFID SYSTEMS Reports on Computer Systems Technology The Information Technology Laboratory (ITL) at the National Institute of Standards and Technology (NIST) promotes the US economy and public welfare by providing technical leadership for the nation’s measurement and standards infrastructure. ITL develops tests, test methods, reference data, proof of concept implementations, and technical analysis to advance the development and productive use of information technology. ITL’s responsibilities include the development of technical, physical, administrative, and management standards and guidelines for the cost-effective security and privacy of sensitive unclassified information in Federal computer systems. Special Publication 800-series documents report on ITL’s research, guidelines, and outreach efforts in computer security and its collaborative activities with industry, government, and academic organizations. National Institute of Standards and Technology Special Publication 800-98 Natl. -
Best Practices on Public Warning Systems for Climate-Induced
Best practices on Public Warning Systems for Climate-Induced Natural Hazards Abstract: This study presents an overview of the Public Warning System, focusing on approaches, technical standards and communication systems related to the generation and the public sharing of early warnings. The analysis focuses on the definition of a set of best practices and guidelines to implement an effective public warning system that can be deployed at multiple geographic scales, from local communities up to the national and also transboundary level. Finally, a set of recommendations are provided to support decision makers in upgrading the national Public Warning System and to help policy makers in outlining future directives. Authors: Claudio Rossi Giacomo Falcone Antonella Frisiello Fabrizio Dominici Version: 30 September 2018 Table of Contents List of Figures .................................................................................................................................. 2 List of Tables ................................................................................................................................... 4 Acronyms ........................................................................................................................................ 4 Core Definitions .............................................................................................................................. 7 1. Introduction ......................................................................................................................... -

Tesi Definitiva
UNIVERSITA’ DEGLI STUDI DI TORINO FACOLTA’ DI ECONOMIA CORSO DI LAUREA IN ECONOMIA E DIREZIONE DELLE IMPRESE RELAZIONE DI LAUREA INNOVATIVI DISPOSITIVI TECNOLOGICI PER UNA MAGGIORE INFORMAZIONE DEL CONSUMATORE NEL SETTORE AGROALIMENTARE: UNO STUDIO AL SALONE DEL GUSTO 2010 Relatore: Prof. Giovanni Peira Correlatori: Prof. Luigi Bollani Dott. Sergio Arnoldi Candidato: Andrea Gino Sferrazza ANNO ACCADEMICO 2010/2011 Ringraziamenti Ringrazio per la stesura di questo lavoro: - il Prof. Giovanni Peira del Dipartimento di Scienze Merceologiche, per avermi seguito e aiutato durante questo lavoro, fornendomi parte del materiale di studio, indicandomi alcune persone cruciali per la buona riuscita della stesura e per la sua completa disponibilità durante quesi mesi di ricerche; - il Prof. Luigi Bollani, del Dipartimento di Statistica e Matematica applicata “Diego de Castro”, per il suo fondamentale contributo nell’impostazione e nell’elaborazione del questionario, proposto durante il Salone del Gusto 2010; - il Dott. Sergio Arnoldi, coordinatore dell’Area Promozione Agroalimentare della Camera di commercio di Torino, il quale ha messo a disposizione tempo e risorse preziose per questo progetto di ricerca, sempre con molta professionalità e competenza; - il Dott. Alessandro Bonadonna del Dipartimento di Scienze Merceologiche, per avermi fornito preziosi spunti per la trattazione; - tutti coloro che mi hanno supportato nella stesura ed elaborazione del questionario, rendendo possibile il raggiungimento degli obiettivi prefissati nei tempi prestabiliti. Ringraziamenti particolari Il primo ringraziamento va a mia madre, l’unica vera persona che mi ha accompagnato in ogni momento durante il mio percorso di studio. Senza di lei, non avrei potuto raggiungere questo importante traguardo. Questo risultato lo divido con te. -

TECHNICAL SPECIFICATION Grupa LOTOS S.A
Spec. No. TECHNICAL SPECIFICATION Grupa LOTOS S.A. General requirements for equipment 8100 subject to UDT/TDT/ZDT approval Contents 1 Subject of specification .......................................................................................................... 2 2 Scope of validity ..................................................................................................................... 2 2.1 Deviations .............................................................................................................................. 2 2.2 Order of Precedence............................................................................................................... 2 3 Definitions and designation .................................................................................................... 2 4 Types of technical inspection ................................................................................................. 3 4.1 Conformity assessment by NB .............................................................................................. 3 4.2 UDT inspection ...................................................................................................................... 3 4.3 TDT inspection ...................................................................................................................... 3 4.4 ZDT inspection ...................................................................................................................... 3 4.5 Requirements ........................................................................................................................ -

Watchpat 200 Operation Manual
WatchPAT™200 Operation Manual Itamar Medical REF OM2196330 Caution: Federal (U.S.) law restricts this device to sale by, or on the order of, a physician. Not for pediatric use. Copyright 2002-2016 By Itamar Medical Ltd. WatchPAT™ and PAT® are trademarks of Itamar Medical, Ltd. This manual and the information contained herein are confidential and are the sole property of Itamar Medical Ltd. Only Itamar Medical Ltd. or its licensees have the right to use this information. Any unauthorized use, disclosure or reproduction is a direct violation of Itamar Medical’s proprietary rights. DISCLAIMER Itamar Medical Ltd. shall not be held responsible in any manner for any bodily injury and/or property damage arising from operation or use of this WatchPAT™200 device other than that which adheres strictly to the instructions and safety precautions contained herein and in all supplements hereto and according to the terms of the warranty provided in the License Agreement in Appendix C. Itamar Medical Ltd. 9 Halamish St., P.O. Box 3579 Caesarea Ind. Park, 3088900, Israel Tel: International + 972-4-617-7000, US 1-888-7ITAMAR Fax + 972 4 627 5598 www.itamar-medical.com This product and/or method of use, is covered by one or more of the following US patents: 6319205, 6322515, 6461305, 6488633, 6916289, 6939304, 7374540, as well as any pending US patent applications and corresponding patents and/or applications filed in other countries. ISO 9001:2008 and EN ISO 13485:2012 See appendix D for contact information of the regulatory authorized representative WatchPAT™200 System i Operation Manual Record of Editions Edition Date Description Chapter Pages Resp. -
ITB Documents No Later Than (From the Bidders) the Date Indicated in the BDS
INVITATION TO BID Construction of Public Education Center in Gaziantep ITB No.: UNDP-TUR-ITB(MC3)-2019/10 Project: Turkey Resilience Project in Response to the Syria Crisis, MADAD C-3 Country: Turkey Issued on: 25 October 2019 1 Contents Section 1. Letter of Invitation ......................................................................................................................... 4 Section 2. Instruction to Bidders .................................................................................................................... 5 GENERAL PROVISIONS ................................ ................................ ................................ ................................ .............................. 6 1. Introduction ........................................................................................................................................................................ 6 2. Fraud & Corruption, Gifts and Hospitality ........................................................................................................................ 6 3. Eligibility .............................................................................................................................................................................. 6 4. Conflict of Interests ............................................................................................................................................................ 7 B. PREPARATION OF BIDS ................................ ................................ ............................... -

Safety Guide for the Americas
Safety Guide for the Americas Six steps to a safe machine Contents Six steps to a safe machine Six steps to a safe machine Contents Six steps to a safe machine Laws, directives, standards, liability g §-1 • Regulatory requirements g §-1 • European directives g §-4 • Obligations of the machine manufacturer g §-5 • Standards g §-9 § • International/European standards g §-11 • Nationally recognized testing labs g §-14 • Test bodies, insurance providers, and authorities g §-15 Risk assessment g 1-1 • The risk assessment process g 1-1 • Functions of the machine g 1-3 • Identification of tasks and hazards g 1-4 1 • Risk estimation and risk evaluation g 1-5 • Documentation g 1-6 Safe design g 2-3 • Mechanical design g 2-3 • Operating and maintenance concept g 2-4 • Electrical installation g 2-5 • Enclosure ratings g 2-8 • Lock-out/tag-out g 2-10 2 • Stop functions g 2-11 g • Electromagnetic compatibility (EMC) 2-12 2-1 • Fluid technology g 2-14 g g • Use in potentially explosive atmospheres 2-15 c Design of the safety function g 3-1 Technical protective measures • Development of the safety concept g 3-13 g • Selection of the protective devices g 3-18 a Definition of the safety functions 3-2 g b Determination of the required g 3-9 • Positioning and dimensioning of 3-44 safety level protective devices • Integration of protective devices into g 3-65 3 the control system Implementation of the safety functions • Product overview for safeguarding g 3-76 d Verification of the safety function g 3-79 e Validation of all safety functions g 3-95 Risk reduction -

Isoupdate May 2019
ISO Update Supplement to ISOfocus May 2019 International Standards in process ISO/CD Agricultural machinery and tractors — Re- 22172-2 pair and maintenance information — Part 2: An International Standard is the result of an agreement between Diagnostics the member bodies of ISO. A first important step towards an Interna- ISO/CD 23130 Milking and cooling machine installa- tional Standard takes the form of a committee draft (CD) - this is cir- tions — Monitoring device for cooling tanks culated for study within an ISO technical committee. When consensus — Requirements has been reached within the technical committee, the document is ISO/CD 11839 Machinery for forestry — Glazing and panel sent to the Central Secretariat for processing as a draft International materials used in operator enclosures for Standard (DIS). The DIS requires approval by at least 75 % of the protection against thrown sawteeth — Test member bodies casting a vote. A confirmation vote is subsequently method and performance criteria carried out on a final draft International Standard (FDIS), the approval criteria remaining the same. ISO/CD Agricultural and forestry machinery — Safety 11806-1 requirements and testing for portable, hand- held, powered brush-cutters and grass-trim- mers — Part 1: Machines fitted with an integral combustion engine ISO/CD Agricultural and forestry machinery — Safety 11806-2 requirements and testing for portable, hand- held, powered brush-cutters and grass- trimmers — Part 2: Machines for use with CD registered back-pack power unit TC 31 Tyres, rims and valves ISO/CD 3739-1 Industrial tyres and rims — Part 1: Pneumatic Period from 01 April to 30 April 2019 tyres (metric series) on 5 degrees tapered or flat base rims — Designation, dimensions and These documents are currently under consideration in the technical marking committee. -
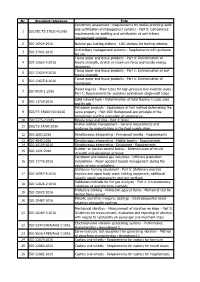
Nr. Standard Reference Title 1 ISO/IEC TS 17021-9:2016
Nr. Standard reference Title Conformity assessment - Requirements for bodies providing audit and certification of management systems - Part 9: Competence 1 ISO/IEC TS 17021-9:2016 requirements for auditing and certification of anti-bribery management systems 2 ISO 16924:2016 Natural gas fuelling stations - LNG stations for fuelling vehicles Anti-bribery management systems - Requirements with guidance 3 ISO 37001:2016 for use Tissue paper and tissue products - Part 4: Determination of 4 ISO 12625-4:2016 tensile strength, stretch at maximum force and tensile energy absorption Tissue paper and tissue products - Part 5: Determination of wet 5 ISO 12625-5:2016 tensile strength Tissue paper and tissue products - Part 6: Determination of 6 ISO 12625-6:2016 grammage Diesel engines - Steel tubes for high-pressure fuel injection pipes - 7 ISO 8535-1:2016 Part 1: Requirements for seamless cold-drawn single-wall tubes Solid mineral fuels - Determination of total fluorine in coal, coke 8 ISO 11724:2016 and fly ash Petroleum products - Equivalency of test method determining the 9 ISO/TR 19686-100:2016 same property - Part 100: Background and principle of the comparison and the evaluation of equivalency 10 ISO 5775-2:2015 Bicycle tyres and rims - Part 2: Rims Animal welfare management - General requirements and 11 ISO/TS 34700:2016 guidance for organizations in the food supply chain 12 ISO 2603:2016 Simultaneous interpreting - Permanent booths - Requirements 13 ISO 4043:2016 Simultaneous interpreting - Mobile booths - Requirements 14 ISO 20109:2016 Simultaneous -

SVENSK STANDARD SS-ISO 3864-3:2016 Fastställd/Approved: 2016-03-14 Publicerad/Published: 2016-03-17 Utgåva/Edition: 1 Språk/Language: Engelska/English ICS: 01.080.01
SVENSK STANDARD SS-ISO 3864-3:2016 Fastställd/Approved: 2016-03-14 Publicerad/Published: 2016-03-17 Utgåva/Edition: 1 Språk/Language: engelska/English ICS: 01.080.01 Grafiska symboler – Varselmärkning och varselskyltar – Del 3: Utformning av grafiska symboler för användning av säkerhetsskyltar (ISO 3864-3:2012, IDT) Graphical symbols – Safety colours and safety signs – Part 3: Design principles for graphical symbols for use in safety signs (ISO 3864-3:2012, IDT) This preview is downloaded from www.sis.se. Buy the entire standard via https://www.sis.se/std-8019463 This preview is downloaded from www.sis.se. Buy the entire standard via https://www.sis.se/std-8019463 Standarder får världen att fungera SIS (Swedish Standards Institute) är en fristående ideell förening med medlemmar från både privat och offentlig sektor. Vi är en del av det europeiska och globala nätverk som utarbetar internationella standarder. Standarder är dokumenterad kunskap utvecklad av framstående aktörer inom industri, näringsliv och samhälle och befrämjar handel över gränser, bidrar till att processer och produkter blir säkrare samt effektiviserar din verksamhet. Delta och påverka Som medlem i SIS har du möjlighet att påverka framtida standarder inom ditt område på nationell, europeisk och global nivå. Du får samtidigt tillgång till tidig information om utvecklingen inom din bransch. Ta del av det färdiga arbetet Vi erbjuder våra kunder allt som rör standarder och deras tillämpning. Hos oss kan du köpa alla publikationer du behöver – allt från enskilda standarder, tekniska rapporter och standard- paket till handböcker och onlinetjänster. Genom vår webbtjänst e-nav får du tillgång till ett lättnavigerat bibliotek där alla standarder som är aktuella för ditt företag finns tillgängliga. -

3 Security Threats for RFID Systems
FIDIS Future of Identity in the Information Society Title: “D3.7 A Structured Collection on Information and Literature on Technological and Usability Aspects of Radio Frequency Identification (RFID)” Author: WP3 Editors: Martin Meints (ICPP) Reviewers: Jozef Vyskoc (VaF) Sandra Steinbrecher (TUD) Identifier: D3.7 Type: [Template] Version: 1.0 Date: Monday, 04 June 2007 Status: [Deliverable] Class: [Public] File: fidis-wp3-del3.7.literature_RFID.doc Summary In this deliverable the physical properties of RFID, types of RFID systems basing on the physical properties and operational aspects of RFID systems are introduced and described. An overview on currently know security threats for RFID systems, countermeasures and related cost aspects is given. This is followed by a brief overview on current areas of application for RFID. To put a light on status quo and trends of development in the private sector in the context of RFID, the results of a study carried out in 2004 and 2005 in Germany are summarised. This is followed by an overview on relevant standards in the context of RFID. This deliverable also includes a bibliography containing relevant literature in the context of RFID. This is published in the bibliographic system at http://www.fidis.net/interactive/rfid-bibliography/ Copyright © 2004-07 by the FIDIS consortium - EC Contract No. 507512 The FIDIS NoE receives research funding from the Community’s Sixth Framework Program FIDIS D3.7 Future of Identity in the Information Society (No. 507512) Copyright Notice: This document may not be copied, reproduced, or modified in whole or in part for any purpose without written permission from the FIDIS Consortium.