Agreement for International SMS Hubbing Services 7.0 12 March 2012
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
System/370 Model 145 Reference Summary
System/370 Model 145 Reference Summary S229-2239-1 IBM Corporation, Field Support Documentation, Dept 927, Rochester, Minnesota 55901 PREFACE This publication is primarily intended for customer engineers servicing System/370 Model 145. Second Edition (September 1972) This is a major revision of, and makes 8229-2239-0 obsolete. Address any comments concerning the contents of this publication to: IBM, Field Support Documentation, Dept 927, Rochester, Minnesota 55901 © International Business Machines Corporation 1972 CONTENTS Section 1 - Control Words Branch and Module Switch Word "O" . 1. 1 Branch Word . 1.2 GA Function Charts . 1.3 GA Function Charts . 1.4 GA Function Charts . 1.5 Branch and Link or Return Word . 1.6 Word Move Word Version"O" . 1. 7 Word Move Word Version "1" . 1.8 Storage Word, Non K-Addressable . 1.9 Storage Word, K-Addressable . 1.10 Arithmetic Word 10 Byte Version 1.11 Arithmetic Word, Fullword Version 1.12 Arithmetic Word, 11 Direct ByteVersion . 1.13 Arithmetic Word, 10/11 Indirect Byte Version . 1.14 ALU Entry Gating 1.15 Stat Set Symbols . 1.15 BranchSymbols . 1.15 Arithmetic Word Chart Selection 1.16 Address Formation Chart 1.16 Control Word Chart Selection 1.16 Section 2 - CPU 3145 CPU Data Flow . 2.1 I-Cycles Data Flow . 2.2 I-Cycles . 2.3 PSW Locations . 2.3 Expanded Local Storage . 2.3 I-Cycles . 2.3 I-Cycles Control Line Generation . 2.4 Control Word . 2.4 Control Register Decode . 2.4 iii ECCL Board Layout ............ 2.5 Data Bit Location Chart .......... 2.5 Common Test Points ........... -

Template Jurnal JAIC;
Journal of Applied Informatics and Computing (JAIC) Vol.2, No.1, Juli 2018, pp. 7~10 e-ISSN: 2548-6861 7 Simulation Strategic Positioning for Mobile Robot Roccer Wheels Mochamad Mobed Bachtiar1, Iwan Kurnianto Wibowo2, Rakhmat Faizal Ajie3 Teknik Komputer, Politeknik Elektronika Negeri Surabaya [email protected] 1, [email protected] 2, [email protected] 3 Article Info ABSTRACT Article history: Soccer robot is a combination of sports, robotics technology and multi agent system. The achieve goals in playing the ball, requires individual intelligence, and the ability Received 2018-04-30 of cooperation for individual skills. The success of a soccer robot team is influenced Revised 2018-06-01 by the success of the robot player to enter the ball into the opponent's goal. In Accepted 2018-07-01 entering the ball into the opponent's goal needed an appropriate position and strategic. This research makes the design in finding a strategic position at the time Keyword: of attack. The design divides the field into several small areas or the main grid, strategic position; attack where each region gives different action. The position is said to be strategic if the strategy; empty space; naïve robot passing success and has a fairly wide perspective against the goal. The bayes classifier strategic position is gained from the greatest opportunity of some of the decisive conditions. The calculation used is to use the Probability Naïve Bayes Classifier by taking the maximum value that serve as a strategic position. So this research resulted in a design in finding strategic position. Copyright © 2017 Journal of Applied Informatics and Computing. -
Report on the Most Appropriate Indicators Related to the Basic Concepts
D 4.1 – Report on the most appropriate indicators related to the basic concepts Report on the most appropriate indicators related to the basic concepts Deliverable D4.1 This project has received funding from the European Union’s Horizon 2020 research and innovation programme under grant agreement No. 870708 D 4.1 – Report on the most appropriate indicators related to the basic concepts Disclaimer: The contents of this deliverable are the sole responsibility of one or more Parties of the SmartCulTour consortium and can under no circumstances be regarded as reflecting the position of the Research Executive Agency and European Commission under the European Union’s Horizon 2020 programme. Copyright and Reprint Permissions “You may freely reproduce all or part of this paper for non-commercial purposes, provided that the following conditions are fulfilled: (i) to cite the authors, as the copyright owners (ii) to cite the SmartCulTour Project and mention that the EC co-finances it, by means of including this statement “Smart Cultural Tourism as a Driver of Sustainable Development of European Regions - SmartCulTour Project no. H2020-870708 co financed by EC H2020 program” and (iii) not to alter the information.” _______________________________________________________________________________________ How to quote this document: Petrić, L., Mandić, A., Pivčević, S., Škrabić Perić, B., Hell, M., Šimundić, B., Muštra, V., Mikulić, D., & Grgić, J. (2020). Report on the most appropriate indicators related to the basic concepts. Deliverable 4.1 of the Horizon 2020 project SmartCulTour (GA number 870708), published on the project web site on September 2020: http://www.smartcultour.eu/deliverables/ D 4.1 – Report on the most appropriate indicators related to the basic concepts This project has received funding from the European Union’s Horizon 2020 research and innovation programme under grant agreement No. -

Nv9602 Nv9000 Control Panel
NV9602 NV9000 CONTROL PANEL User’s Guide VERSION 1.2 UG0040-02 2015-07-02 www.grassvalley.com Notices Copyright and Trademark Notice Copyright © 2015, Grass Valley USA, LLC. All rights reserved. Belden, Belden Sending All The Right Signals, and the Belden logo are trademarks or registered trademarks of Belden Inc. or its affiliated companies in the United States and other jurisdictions. Grass Valley USA, LLC, Miranda, NV9602, Kaleido, NVISION, iControl, and Densité are trademarks or registered trademarks of Grass Valley USA, LLC. Belden Inc., Grass Valley USA, LLC, and other parties may also have trademark rights in other terms used herein. Terms and Conditions Please read the following terms and conditions carefully. By using NVISION control panel documentation, you agree to the following terms and conditions. Grass Valley hereby grants permission and license to owners of NVISION control panels to use their product manuals for their own internal business use. Manuals for Grass Valley products may not be reproduced or transmitted in any form or by any means, electronic or mechanical, including photocopying and recording, for any purpose unless specifically authorized in writing by Grass Valley. A Grass Valley manual may have been revised to reflect changes made to the product during its manufacturing life. Thus, different versions of a manual may exist for any given product. Care should be taken to ensure that one obtains the proper manual version for a specific product serial number. Information in this document is subject to change without notice and does not represent a commitment on the part of Grass Valley. Warranty information is available in the Support section of the Grass Valley Web site (www.grassvalley.com). -
Decnet-Plusftam and Virtual Terminal Use and Management
VSI OpenVMS DECnet-Plus FTAM and Virtual Terminal Use and Management Document Number: DO-FTAMMG-01A Publication Date: June 2020 Revision Update Information: This is a new manual. Operating System and Version: VSI OpenVMS Integrity Version 8.4-2 VSI OpenVMS Alpha Version 8.4-2L1 VMS Software, Inc., (VSI) Bolton, Massachusetts, USA DECnet-PlusFTAM and Virtual Terminal Use and Management Copyright © 2020 VMS Software, Inc. (VSI), Bolton, Massachusetts, USA Legal Notice Confidential computer software. Valid license from VSI required for possession, use or copying. Consistent with FAR 12.211 and 12.212, Commercial Computer Software, Computer Software Documentation, and Technical Data for Commercial Items are licensed to the U.S. Government under vendor's standard commercial license. The information contained herein is subject to change without notice. The only warranties for VSI products and services are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional warranty. VSI shall not be liable for technical or editorial errors or omissions contained herein. HPE, HPE Integrity, HPE Alpha, and HPE Proliant are trademarks or registered trademarks of Hewlett Packard Enterprise. Intel, Itanium and IA-64 are trademarks or registered trademarks of Intel Corporation or its subsidiaries in the United States and other countries. UNIX is a registered trademark of The Open Group. The VSI OpenVMS documentation set is available on DVD. ii DECnet-PlusFTAM and Virtual -

VSI X.25 for Openvms Configuration Guide
VSI OpenVMS VSI X.25 for OpenVMS Configuration Guide Document Number: DO-DX25CG-01A Publication Date: August 2018 Revision Update Information: This is a new manual. Operating System and Version: VSI OpenVMS Integrity Version 8.4-2 VSI OpenVMS Alpha Version 8.4-2L1 Software Version: VSI X.25 for OpenVMS Version 2.1 VMS Software, Inc. (VSI) Burlington, Massachusetts, USA VSI X.25 for OpenVMS Configuration Guide Copyright © 2018 VMS Software, Inc. (VSI), Burlington, Massachusetts, USA Legal Notice Confidential computer software. Valid license from VSI required for possession, use or copying. Consistent with FAR 12.211 and 12.212, Commercial Computer Software, Computer Software Documentation, and Technical Data for Commercial Items are licensed to the U.S. Government under vendor's standard commercial license. The information contained herein is subject to change without notice. The only warranties for VSI products and services are set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional warranty. VSI shall not be liable for technical or editorial errors or omissions contained herein. HPE, HPE Integrity, HPE Alpha, and HPE Proliant are trademarks or registered trademarks of Hewlett Packard Enterprise. Intel and Itanium are trademarks or registered trademarks of Intel Corporation or its subsidiaries in the United States and other countries. Oracle is a registered trademark of Oracle and/or its affiliates. The VSI OpenVMS documentation set is available -

Towards Coordinated, Network-Wide Traffic
Towards Coordinated, Network-Wide Traffic Monitoring for Early Detection of DDoS Flooding Attacks by Saman Taghavi Zargar B.Sc., Computer Engineering (Software Engineering), Azad University of Mashhad, 2004 M.Sc., Computer Engineering (Software Engineering), Ferdowsi University of Mashhad, 2007 Submitted to the Graduate Faculty of the School of Information Sciences in partial fulfillment of the requirements for the degree of Doctor of Philosophy University of Pittsburgh 2014 UNIVERSITY OF PITTSBURGH SCHOOL OF INFORMATION SCIENCES This dissertation was presented by Saman Taghavi Zargar It was defended on June 3, 2014 and approved by James Joshi, Ph.D., Associate Professor, School of Information Sciences David Tipper, Ph.D., Associate Professor, School of Information Sciences Prashant Krishnamurthy, Ph.D., Associate Professor, School of Information Sciences Konstantinos Pelechrinis, Ph.D., Assistant Professor, School of Information Sciences Yi Qian, Ph.D., Associate Professor, College of Engineering, Dissertation Advisors: James Joshi, Ph.D., Associate Professor, School of Information Sciences, David Tipper, Ph.D., Associate Professor, School of Information Sciences ii Copyright c by Saman Taghavi Zargar 2014 iii Towards Coordinated, Network-Wide Traffic Monitoring for Early Detection of DDoS Flooding Attacks Saman Taghavi Zargar, PhD University of Pittsburgh, 2014 DDoS flooding attacks are one of the biggest concerns for security professionals and they are typically explicit attempts to disrupt legitimate users' access to services. Developing a com- prehensive defense mechanism against such attacks requires a comprehensive understanding of the problem and the techniques that have been used thus far in preventing, detecting, and responding to various such attacks. In this thesis, we dig into the problem of DDoS flooding attacks from four directions: (1) We study the origin of these attacks, their variations, and various existing defense mecha- nisms against them. -
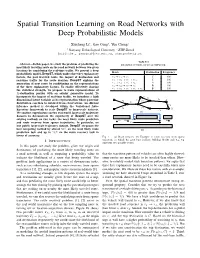
Spatial Transition Learning on Road Networks with Deep Probabilistic Models
Spatial Transition Learning on Road Networks with Deep Probabilistic Models Xiucheng Liy, Gao Congy, Yun Chengz y Nanyang Technological Univeristy, z ETH Zurich fxli055@e., [email protected], [email protected] TABLE I Abstract—In this paper, we study the problem of predicting the EXAMPLE OF TRIPS ON ROAD NETWORK. most likely traveling route on the road network between two given locations by considering the real-time traffic. We present a deep Route Destination Frequency probabilistic model–DeepST–which unifies three key explanatory factors, the past traveled route, the impact of destination and r3 ! r2 ! r4 C 400 real-time traffic for the route decision. DeepST explains the r3 ! r2 ! r5 ! r10 C 100 generation of next route by conditioning on the representations r1 ! r2 ! r5 ! r6 A 100 of the three explanatory factors. To enable effectively sharing r1 ! r2 ! r7 ! r8 B 100 r ! r ! r ! r ! r B 100 the statistical strength, we propose to learn representations of 1 2 5 6 9 K-destination proxies with an adjoint generative model. To incorporate the impact of real-time traffic, we introduce a high C r<latexit sha1_base64="(null)">(null)</latexit> 10 r<latexit sha1_base64="(null)">(null)</latexit> dimensional latent variable as its representation whose posterior r<latexit sha1_base64="(null)">(null)</latexit> 4 6 A r<latexit sha1_base64="lQIphb3ZxX5RFxPPJ2+0wE0HOKM=">AAAB6nicbZBNS8NAEIYn9avWr6hHL4tF8FQSEfRY9OKxov2ANpTNdtMu3WzC7kQooT/BiwdFvPqLvPlv3LY5aOsLCw/vzLAzb5hKYdDzvp3S2vrG5lZ5u7Kzu7d/4B4etUySacabLJGJ7oTUcCkUb6JAyTup5jQOJW+H49tZvf3EtRGJesRJyoOYDpWIBKNorQfd9/tu1at5c5FV8AuoQqFG3/3qDRKWxVwhk9SYru+lGORUo2CSTyu9zPCUsjEd8q5FRWNugny+6pScWWdAokTbp5DM3d8TOY2NmcSh7YwpjsxybWb+V+tmGF0HuVBphlyxxUdRJgkmZHY3GQjNGcqJBcq0sLsSNqKaMrTpVGwI/vLJq9C6qPmW7y+r9ZsijjKcwCmcgw9XUIc7aEATGAzhGV7hzZHOi/PufCxaS04xcwx/5Hz+AAKOjZo=</latexit> -

Does Migration Destination Affect the Mortality Advantage of Mexican Immigrants? a Comparison of Traditional, New, and Emerging Destinations
Does Migration Destination Affect the Mortality Advantage of Mexican Immigrants? A comparison of Traditional, New, and Emerging Destinations Andrew Fenelon1 1National Center for Health Statistics, 3311 Toledo Road, Hyattsville, MD 20782 Abstract Health declines for immigrants with greater exposure to the United States, but the specific characteristics of the migration and assimilation processes that contribute to this pattern are less clear. As the Mexican population in the US has grown, it has expanded outside traditional gateways in California and Texas to new destinations throughout the US. This study examines the mortality of Mexican immigrants in Traditional versus New and Emerging destinations in the US. Using National Health Interview Survey data between 1989 and 2009 the analysis finds that Mexican immigrants in New and Emerging destinations have a significant survival advantage over their counterparts in traditional established destinations. This advantage may reflect selective migration to new destinations, superior employment prospects, or slower behavioral assimilation. US-born Mexicans do not benefit from this advantage. The results suggest that the spatial characteristics of the assimilation process are important when considering the health of immigrants. Introduction The Hispanic mortality advantage refers to the finding that the Hispanic-origin population in the United States experiences lower adult mortality rates than the non-Hispanic white population, despite lower average socioeconomic status among Hispanics. The “Hispanic Paradox” calls attention to the fact that Hispanics resemble African-Americans in terms of socioeconomic indicators but non-Hispanic whites in health and mortality indicators (Hummer, et al., 2000, Markides and Eschbach, 2011). In many studies, Hispanics exhibit higher life expectancy than non-Hispanic whites, as well as more favorable profiles with respect to non-fatal conditions such as cancer incidence and severity, heart disease, and hypertension (Eschbach, et al., 2005, Singh and Siahpush, 2002). -

IEEE Paper Template in A4 (V1)
INTERNATIONAL JOURNAL OF INFORMATION AND COMPUTING SCIENCE ISSN NO: 0972-1347 Performance of Bidirectional Diagonal Mesh Topology with modified Q routing for Network on Chip Architecture P. P. Papalkar1, M. A. Gaikwad2 1Electronics and Telecommunication, Ramrao Adik Institute of Technology, Navi - Mumbai, India [email protected] 2 Electronics and Telecommunication, G. H. Raisoni college of Engineering, Nagpur, India [email protected] Abstract— Many routing architectures and routing algorithms have been developed to alleviate traffic congestion over the network. Bidirectional Diagonal Mesh NoC architecture is used to reduce the load distribution across the network by reducing the diameter of the network, which ultimately reduces routing cost. Q routing searches least congested path available in the network from source to destination. It is highly adaptive and flexible algorithm. Bidirectional Diagonal Mesh topology is combined with modified Q routing, which estimates the alternative routes with priority given to diagonal path using Q Table. Significant improvement over the traditional Mesh topology is achieved by the proposed approach. Keywords: Network on Chip, Bidirectional Diagonal Mesh Topology, Q Routing, Modified Q Routing, throughput and latency 1. INTRODUCTION As the size of a transistor reduces to submicron level, more transistors will be integrated on a single chip that can be clocked faster. According to Moore’s law, the density of a transistor in an integrated circuit would double every 18 to 24 months that leading to the implementation of System on chip (SoC). SoC is complex and heterogeneous components such as programmable processors, memories, input /output interface, custom hardware, peripherals, external interface IP (INTELLECTUAL property) blocks can be in integrated on-chip communication architecture that serves to interconnect these components. -

Alarms Toolbar
Iris Alarms Version 7.13.2 NOTE The content in this document is a subset of the Iris online help and user guides. Not all links within the document are active. Refer to the Iris online help and user guides for access to complete information about a feature. Tektronix Communications | For Licensed Users Only | Unauthorized Duplication and Distribution Prohibited Copyright Copyright Tektronix Communications, Inc. All rights reserved. Printed in the USA. Tektronix products are covered by U.S. and foreign patents, issued and pending. Information in this publication supersedes that in all previously published material. Specification and price change privileges reserved. TEKTRONIX and TEK are registered trademarks of Tektronix, Inc. All other trade names referenced are the trademarks of the service marks, trademarks, or registered trademarks of their respective companies. No portion of this document may be copied, photocopied, reproduced, translated, or reduced to any electronic medium or machine form without prior consent in writing from Tektronix, Inc. The information in this document is subject to change without notice and does not represent a commitment on the part of Tektronix, Inc. Tektronix Communications 3033 W President George Bush Highway Plano, TX 75075 USA +1 469-330-4000 (voice) www.tekcomms.com 992-0472-08-001-140228 The products and specifications, configurations, and other technical information regarding the services described or referenced in this document are subject to change without notice. All statements, technical information, and recommendations contained in this document are believed to be accurate and reliable but are presented "as is" without warranty of any kind, express or implied. -

Strategic Communication in Tourism
STRATEGIC COMMUNICATION IN TOURISM DEPARTMENT OF DESIGN AND COMMUNICATION CENTRE FOR TOURISM, INNOVATION AND CULTURE (TIC) Bodil Stilling Blichfeldt Strategic Communication in Tourism Background, conceptualizations, introduction to analysis and relations to sustainable tourism and tourism innovation TIC TALKS no. 5, September 2017 1 Author info Associate Professor, Ph.D. Bodil Stilling Blichfeldt, TIC and Department of Design and Communication, University of Southern Denmark. Email: [email protected] Place of publication TIC is University of Southern Denmark’s multidisciplinary research center in tourism, innovation and culture. The center is located at the Kolding campus. TIC strives to transform the university to an engaged, collaborative institution where academics and students pursue an unrelenting examination of knowledge, its sources and its uses. TIC defines the university as a center for higher order knowledge creation and for collaboration with, and for, society at large. We do this through research-based education, education-based research and collaborative engagement with society. We aim to charter new territory in international academe, as well as in multi-level collaboration based on interdisciplinary research with a strong foundation in the Humanities. TIC engages in research dialogues through both a traditional peer-review publication strategy and through involvement in securing free access to knowledge. Supplementing traditional journal articles, TIC TALKS is one of TIC’s contributions to open access sharing and collaborative development of knowledge. TIC TALKS are provided by Centre for Tourism, Innovation and Culture, University of Southern Denmark Universitetsparken 1, Kolding, DK-6000 http://www.sdu.dk/en/Om_SDU/Institutter_centre/C_Tik.aspx The present manuscript qualifies as unfinished work-in-progress and the reader should bear in mind that the manuscript is quite likely to contain a series of errors, flaws and weaknesses.