The Tragedy of Systemd
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
It's Complicated but It's Probably Already Booting Your Computer
FAQ SYSTEMD SYSTEMD It’s complicated but it’s probably already booting your computer. dynamically connect to your network, a runlevel of 1 for a single-user mode, GRAHAM MORRISON while syslogd pools all the system runlevel 3 for the same command messages together to create a log of prompt we described earlier, and Surely the ‘d’ in Systemd is everything important. Another daemon, runlevel 5 to launch a graphical a typo? though it lacks the ‘d’, is init – famous environment. Changing this for your No –it’s a form of Unix notation for being the first process that runs on next boot often involved editing the used to signify a daemon. your system. /etc/inittab file, and you’d soon get used to manually starting and stopping You mean like those little Isn’t init used to switch your own services simply by executing devils inhabiting Dante’s between the command-line the scripts you found. underworld? and the graphical desktop? There is a link in that Unix usage For many of us, yes. This was the You seem to be using the past of the term daemon supposedly main way of going from the tense for all this talk about the comes from Greek mythology, where desktop to a command line and back init daemon… daemons invisibly wove their magic again without trying to figure out which That’s because the and benign influence. The word is today processes to kill or start manually. aforementioned Systemd wants more commonly spelt ‘demon’, which Typing init 3 would typically close any to put init in the past. -
Getting to Grips with Unix and the Linux Family
Getting to grips with Unix and the Linux family David Chiappini, Giulio Pasqualetti, Tommaso Redaelli Torino, International Conference of Physics Students August 10, 2017 According to the booklet At this end of this session, you can expect: • To have an overview of the history of computer science • To understand the general functioning and similarities of Unix-like systems • To be able to distinguish the features of different Linux distributions • To be able to use basic Linux commands • To know how to build your own operating system • To hack the NSA • To produce the worst software bug EVER According to the booklet update At this end of this session, you can expect: • To have an overview of the history of computer science • To understand the general functioning and similarities of Unix-like systems • To be able to distinguish the features of different Linux distributions • To be able to use basic Linux commands • To know how to build your own operating system • To hack the NSA • To produce the worst software bug EVER A first data analysis with the shell, sed & awk an interactive workshop 1 at the beginning, there was UNIX... 2 ...then there was GNU 3 getting hands dirty common commands wait till you see piping 4 regular expressions 5 sed 6 awk 7 challenge time What's UNIX • Bell Labs was a really cool place to be in the 60s-70s • UNIX was a OS developed by Bell labs • they used C, which was also developed there • UNIX became the de facto standard on how to make an OS UNIX Philosophy • Write programs that do one thing and do it well. -

The GNOME Census: Who Writes GNOME?
The GNOME Census: Who writes GNOME? Dave Neary & Vanessa David, Neary Consulting © Neary Consulting 2010: Some rights reserved Table of Contents Introduction.........................................................................................3 What is GNOME?.............................................................................3 Project governance...........................................................................3 Why survey GNOME?.......................................................................4 Scope and methodology...................................................................5 Tools and Observations on Data Quality..........................................7 Results and analysis...........................................................................10 GNOME Project size.......................................................................10 The Long Tail..................................................................................11 Effects of commercialisation..........................................................14 Who does the work?.......................................................................15 Who maintains GNOME?................................................................17 Conclusions........................................................................................22 References.........................................................................................24 Appendix 1: Modules included in survey...........................................25 2 Introduction What -

State of Linux Audio in 2009 Linux Plumbers Conference 2009
State of Linux Audio in 2009 Linux Plumbers Conference 2009 Lennart Poettering [email protected] September 2009 Lennart Poettering State of Linux Audio in 2009 Who Am I? Software Engineer at Red Hat, Inc. Developer of PulseAudio, Avahi and a few other Free Software projects http://0pointer.de/lennart/ [email protected] IRC: mezcalero Lennart Poettering State of Linux Audio in 2009 Perspective Lennart Poettering State of Linux Audio in 2009 So, what happened since last LPC? Lennart Poettering State of Linux Audio in 2009 RIP: EsounD is officially gone. Lennart Poettering State of Linux Audio in 2009 (at least on Fedora) RIP: OSS is officially gone. Lennart Poettering State of Linux Audio in 2009 RIP: OSS is officially gone. (at least on Fedora) Lennart Poettering State of Linux Audio in 2009 Audio API Guide http://0pointer.de/blog/projects/guide-to-sound-apis Lennart Poettering State of Linux Audio in 2009 We also make use of high-resolution timers on the desktop by default. We now use realtime scheduling on the desktop by default. Lennart Poettering State of Linux Audio in 2009 We now use realtime scheduling on the desktop by default. We also make use of high-resolution timers on the desktop by default. Lennart Poettering State of Linux Audio in 2009 2s Buffers Lennart Poettering State of Linux Audio in 2009 Mixer abstraction? Due to user-friendliness, i18n, meta data (icons, ...) We moved a couple of things into the audio server: Timer-based audio scheduling; mixing; flat volume/volume range and granularity extension; integration of volume sliders; mixer abstraction; monitoring Lennart Poettering State of Linux Audio in 2009 We moved a couple of things into the audio server: Timer-based audio scheduling; mixing; flat volume/volume range and granularity extension; integration of volume sliders; mixer abstraction; monitoring Mixer abstraction? Due to user-friendliness, i18n, meta data (icons, ...) Lennart Poettering State of Linux Audio in 2009 udev integration: meta data, by-path/by-id/.. -
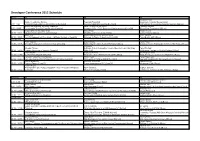
Developer Conference 2012 Schedule
Developer Conference 2012 Schedule Friday D1 D2 D3 Vlastimil Eliáš Jakub Hrozek, Jan Zeleny František Řezníček Centralized Identity Management 9:00 - 9:45 FreeIPA/SSSD + Intro to MIT Kerberos [Security] Towards Unified Messaging [CoreOS] And SSO for jboss.org Community Systems [JBoss] Alexander Bokovoy, Andreas Schneider Kamil Dudka, Ondřej Vašík Christian Sadilek 9:50 - 10:35 Cross-realm Trusts in FreeIPA v3.0 [Security] Common C/C++ Error Patterns & Static Analysis [CoreOS] JBoss Errai Framework [JBoss] Eduard Beneš, Miroslav Grepl Adam Tkáč Martin Kouba 10:40 - 11:25 SELinux News in Fedora 16 [Security] DNSSEC in Fedora 17 [CoreOS] CDI for Seam2 [JBoss] Dmitri Pal Marcela Maslanova, Jindrich Novy Peter Skopek 11:30 - 12:15 Identity Management Roadmap + MIT and Kerberos [Security] Dynamic Software Collections [CoreOS] PicketBox in AS7 [JBoss] Quick break Peter Vrabec Bryn Reeves Karel Piwko 12:30 - 13:15 Security Compliance Check in Fedora [Security] Supporting the Open Source Enterprise [Misc] Arquillian Drone Helping Ike Get Rid of the Bugs [JBoss] Jan Hutar Miloslav Trmac Software Robot Competition Around the World and Our Way Pavol Pitoňák 13:20 - 14:05 Concise Overview of Security [Security] [Misc, CZ] RichFaces: Testing on Mobile Devices [JBoss] Steve Grubb Stanislav Kozina Geoffrey De Smet 14:10 - 14:55 Government Security [Security] What Can Linux Learn from the Others [Misc] What Are Drools, Guvnor and Planner? [JBoss] Lennart Poettering, Kay Sievers Phil Knirsch Pavel Tisnovsky 15:00 - 15:45 Do's and Don'ts when Writing System -

If Data Is Confidential and Available but Altered Decryption of Altered Data Usually Gives Garbage Exception: Electronic-Codeboo
38 40 If Data is Confidential and Available but Altered Encryption • do not use ECB–Mode • use CBC– or CTR–mode (recommendation Schneier/Ferguson) • use AES or one of the finalists – Twofish (Schneier, Ferguson, Kelsey, Whiting, Wagner, Hall) decryption of altered data usually gives garbage – Serpent (Anderson, Biham, Knudsen) – MARS (Coppersmith et al., IBM) exception: electronic-codebook-mode (ECB) (uses independent blocks) – RC6 (Rivest, patented by RSA) 39 41 ECB-Mode Encrypted Penguin If Data is Non-Alterable and Confidential but not Available ,,Your message with authenticator 08931281763e1de003e5f930c449bf791c9f0db6 encryption is block by block has been received, but unfortunately the server is down. ❀ every block gets another color Your mail-service will never be accessible.” Example: lavabit.com, Snowden’s e-Mail-Provider 42 44 Authorization: Who is Allowed to Do All This? Problem: Person/Process/Role ⇐⇒ String (2) How to link a person to a string? • Person knows something (password, secret cryptographic key). • Person has something (token, USB–key, chipcard). Authorized entities only. • Person is something (biometrics, fingerprint etc.). Only Bob is allowed to enter here. We have to identify persons, processes and their roles. 43 45 Problem: Person/Process/Role ⇐⇒ String (1) Proof of Identity is Called Authentication Person identified by picture String identified by equality relation. 46 48 Proof of Identity: Links Person to a String Third party guarantees real identity. Has something: ID–card. 47 49 Proof of True Source is Called Authenticity -

Beyond Init: Systemd Linux Plumbers Conference 2010
Beyond Init: systemd Linux Plumbers Conference 2010 Kay Sievers Lennart Poettering November 2010 Kay Sievers, Lennart Poettering Beyond Init: systemd Triggers: Boot, Socket, Bus, Device, Path, Timers, More Kay Sievers, Lennart Poettering Beyond Init: systemd Kay Sievers, Lennart Poettering Beyond Init: systemd Substantial coverage of basic OS boot-up tasks, including fsck, mount, quota, hwclock, readahead, tmpfiles, random-seed, console, static module loading, early syslog, plymouth, shutdown, kexec, SELinux, initrd+initrd-less boots. Status: almost made Fedora 14. Kay Sievers, Lennart Poettering Beyond Init: systemd including fsck, mount, quota, hwclock, readahead, tmpfiles, random-seed, console, static module loading, early syslog, plymouth, shutdown, kexec, SELinux, initrd+initrd-less boots. Status: almost made Fedora 14. Substantial coverage of basic OS boot-up tasks, Kay Sievers, Lennart Poettering Beyond Init: systemd mount, quota, hwclock, readahead, tmpfiles, random-seed, console, static module loading, early syslog, plymouth, shutdown, kexec, SELinux, initrd+initrd-less boots. Status: almost made Fedora 14. Substantial coverage of basic OS boot-up tasks, including fsck, Kay Sievers, Lennart Poettering Beyond Init: systemd quota, hwclock, readahead, tmpfiles, random-seed, console, static module loading, early syslog, plymouth, shutdown, kexec, SELinux, initrd+initrd-less boots. Status: almost made Fedora 14. Substantial coverage of basic OS boot-up tasks, including fsck, mount, Kay Sievers, Lennart Poettering Beyond Init: systemd hwclock, readahead, tmpfiles, random-seed, console, static module loading, early syslog, plymouth, shutdown, kexec, SELinux, initrd+initrd-less boots. Status: almost made Fedora 14. Substantial coverage of basic OS boot-up tasks, including fsck, mount, quota, Kay Sievers, Lennart Poettering Beyond Init: systemd readahead, tmpfiles, random-seed, console, static module loading, early syslog, plymouth, shutdown, kexec, SELinux, initrd+initrd-less boots. -

Introduction to Unix Shell (Part I)
Introduction to Unix shell (part I) Evgeny Stambulchik Faculty of Physics, Weizmann Institute of Science, Rehovot 7610001, Israel Joint ICTP-IAEA School on Atomic Processes in Plasmas February 27 – March 3, 2017 Trieste, Italy Contrary to popular belief, Unix is user friendly. It just happens to be very selective about who it decides to make friends with. Unknown Initially used at Bell Labs, but soon licensed to academy (notably, U. of California, Berkeley) and commercial vendors (IBM, Sun, etc). There are two major products that came out of Berkeley: LSD and Unix. We don’t believe this to be a coincidence. Jeremy S. Anderson, Unix systems administrator Historical overview (kind of) Unix is a family of multiuser, multitasking operating systems stemming from the original Unix developed in the 1970’s at Bell Labs by Ken Thompson, Dennis Ritchie1, and others. Some consider Unix to be the second most important invention to come out of AT&T Bell Labs after the transistor. Dennis Ritchie 1Also famous for creating the C programming language. Historical overview (kind of) Unix is a family of multiuser, multitasking operating systems stemming from the original Unix developed in the 1970’s at Bell Labs by Ken Thompson, Dennis Ritchie1, and others. Some consider Unix to be the second most important invention to come out of AT&T Bell Labs after the transistor. Dennis Ritchie Initially used at Bell Labs, but soon licensed to academy (notably, U. of California, Berkeley) and commercial vendors (IBM, Sun, etc). There are two major products that came out of Berkeley: LSD and Unix. -
Beyond Init: Systemd Linux.Conf.Au 2011
Beyond Init: systemd linux.conf.au 2011 Lennart Poettering January 2011 Lennart Poettering Beyond Init: systemd compatible with SysV and LSB init scripts. systemd provides aggressive parallelization capabilities, uses socket and D-Bus activation for starting services, offers on-demand starting of daemons, keeps track of processes using Linux cgroups, supports snapshotting and restoring of the system state, maintains mount and automount points and implements an elaborate transactional dependency-based service control logic. It can work as a drop-in replacement for sysvinit." \systemd is a system and session manager for Linux, Lennart Poettering Beyond Init: systemd systemd provides aggressive parallelization capabilities, uses socket and D-Bus activation for starting services, offers on-demand starting of daemons, keeps track of processes using Linux cgroups, supports snapshotting and restoring of the system state, maintains mount and automount points and implements an elaborate transactional dependency-based service control logic. It can work as a drop-in replacement for sysvinit." \systemd is a system and session manager for Linux, compatible with SysV and LSB init scripts. Lennart Poettering Beyond Init: systemd uses socket and D-Bus activation for starting services, offers on-demand starting of daemons, keeps track of processes using Linux cgroups, supports snapshotting and restoring of the system state, maintains mount and automount points and implements an elaborate transactional dependency-based service control logic. It can work as a drop-in replacement for sysvinit." \systemd is a system and session manager for Linux, compatible with SysV and LSB init scripts. systemd provides aggressive parallelization capabilities, Lennart Poettering Beyond Init: systemd offers on-demand starting of daemons, keeps track of processes using Linux cgroups, supports snapshotting and restoring of the system state, maintains mount and automount points and implements an elaborate transactional dependency-based service control logic. -

Command Line Interface (Shell)
Command Line Interface (Shell) 1 Organization of a computer system users applications graphical user shell interface (GUI) operating system hardware (or software acting like hardware: “virtual machine”) 2 Organization of a computer system Easier to use; users applications Not so easy to program with, interactive actions automate (click, drag, tap, …) graphical user shell interface (GUI) system calls operating system hardware (or software acting like hardware: “virtual machine”) 3 Organization of a computer system Easier to program users applications with and automate; Not so convenient to use (maybe) typed commands graphical user shell interface (GUI) system calls operating system hardware (or software acting like hardware: “virtual machine”) 4 Organization of a computer system users applications this class graphical user shell interface (GUI) operating system hardware (or software acting like hardware: “virtual machine”) 5 What is a Command Line Interface? • Interface: Means it is a way to interact with the Operating System. 6 What is a Command Line Interface? • Interface: Means it is a way to interact with the Operating System. • Command Line: Means you interact with it through typing commands at the keyboard. 7 What is a Command Line Interface? • Interface: Means it is a way to interact with the Operating System. • Command Line: Means you interact with it through typing commands at the keyboard. So a Command Line Interface (or a shell) is a program that lets you interact with the Operating System via the keyboard. 8 Why Use a Command Line Interface? A. In the old days, there was no choice 9 Why Use a Command Line Interface? A. -

The Pulseaudio Sound Server Linux.Conf.Au 2007
Introduction What is PulseAudio? Usage Internals Recipes Outlook The PulseAudio Sound Server linux.conf.au 2007 Lennart Poettering [email protected] Universit¨atHamburg, Department Informatik University of Hamburg, Department of Informatics Hamburg, Germany January 17th, 2007 Lennart Poettering The PulseAudio Sound Server 2 What is PulseAudio? 3 Usage 4 Internals 5 Recipes 6 Outlook Introduction What is PulseAudio? Usage Internals Recipes Outlook Contents 1 Introduction Lennart Poettering The PulseAudio Sound Server 3 Usage 4 Internals 5 Recipes 6 Outlook Introduction What is PulseAudio? Usage Internals Recipes Outlook Contents 1 Introduction 2 What is PulseAudio? Lennart Poettering The PulseAudio Sound Server 4 Internals 5 Recipes 6 Outlook Introduction What is PulseAudio? Usage Internals Recipes Outlook Contents 1 Introduction 2 What is PulseAudio? 3 Usage Lennart Poettering The PulseAudio Sound Server 5 Recipes 6 Outlook Introduction What is PulseAudio? Usage Internals Recipes Outlook Contents 1 Introduction 2 What is PulseAudio? 3 Usage 4 Internals Lennart Poettering The PulseAudio Sound Server 6 Outlook Introduction What is PulseAudio? Usage Internals Recipes Outlook Contents 1 Introduction 2 What is PulseAudio? 3 Usage 4 Internals 5 Recipes Lennart Poettering The PulseAudio Sound Server Introduction What is PulseAudio? Usage Internals Recipes Outlook Contents 1 Introduction 2 What is PulseAudio? 3 Usage 4 Internals 5 Recipes 6 Outlook Lennart Poettering The PulseAudio Sound Server Introduction What is PulseAudio? Usage Internals Recipes Outlook Who Am I? Student (Computer Science) from Hamburg, Germany Core Developer of PulseAudio, Avahi and a few other Free Software projects http://0pointer.de/lennart/ [email protected] IRC: mezcalero Lennart Poettering The PulseAudio Sound Server Introduction What is PulseAudio? Usage Internals Recipes Outlook Introduction Lennart Poettering The PulseAudio Sound Server It’s a mess! There are just too many widely adopted but competing and incompatible sound systems. -
Tuning Systemd for Embedded
Tuning systemd for Embedded Alison Chaiken [email protected] Mar. 23, 2015 Latest version: http://she-devel.com/ELC_systemd.pdf Auxiliary files: http://she-devel.com/ELC_auxiliary.tar.bz2 Text in blue is hyperlinked. ? ? ? ? Quiz: what is the most widely used Linux init system? ? ? ? ? phenomenom.” -- Gary Hamel “ Show Action Linux itself.” -- is Linux GKH, Linux “ Valley Silicon Gates,-- Bill industry.” the technology in position “ Success self-correcting Success is a hurt Thethatever thing can only has a guaranteed No one Linux needs to keepinnovating Pirates Pirates of Licensed under CC BY-SA 3.0 http://commons.wikimedia.org/wiki/File:Fire-lite-bg- 10.jpg#mediaviewer/File:Fire-lite-bg-10.jpg Philosophy of systemd Extract duplicate functionality from daemons and move it to systemd core or kernel. Replace /etc scripts with declarative config files. Expose newer kernel APIs to userspace via a simple interface. systemd is: ● modular; ● asynchronous and concurrent; ● described by declarative sets of properties; ● bundled with analysis tools and tests; ● features a fully language-agnostic API. One daemon to rule them all xinetd: a daemon to lazily launch internet services when activity is detected on an AF_INET socket systemd: a daemon to lazily launch any system service when activity is detected on an AF_UNIX socket (oversimplification) Complexity arising from many similar small units init.d scripts systemd units ● Unit's action and parameters: ExecStart= ● Dependencies: Before=, After=, Requires=, Conflicts= and Wants=. ● Default dependencies: – Requires= and After= on basic.target; – Conflicts= and Before= on shutdown.target. ● Types of unit files: service, socket, device, mount, scope, slice, automount, swap, target, path, timer, snapshot sysVinit runlevels ≈ systemd targets ● Targets are synchronization points.