REVERSE ENGINEERING BROWSER COMPONENTS DISSECTING and HACKING SILVERLIGHT, HTML 5 and FLEX Shreeraj Shah
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Association of Gene Ontology Categories with Decay Rate for Hepg2 Experiments These Tables Show Details for All Gene Ontology Categories
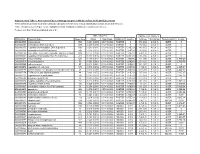
Supplementary Table 1: Association of Gene Ontology Categories with Decay Rate for HepG2 Experiments These tables show details for all Gene Ontology categories. Inferences for manual classification scheme shown at the bottom. Those categories used in Figure 1A are highlighted in bold. Standard Deviations are shown in parentheses. P-values less than 1E-20 are indicated with a "0". Rate r (hour^-1) Half-life < 2hr. Decay % GO Number Category Name Probe Sets Group Non-Group Distribution p-value In-Group Non-Group Representation p-value GO:0006350 transcription 1523 0.221 (0.009) 0.127 (0.002) FASTER 0 13.1 (0.4) 4.5 (0.1) OVER 0 GO:0006351 transcription, DNA-dependent 1498 0.220 (0.009) 0.127 (0.002) FASTER 0 13.0 (0.4) 4.5 (0.1) OVER 0 GO:0006355 regulation of transcription, DNA-dependent 1163 0.230 (0.011) 0.128 (0.002) FASTER 5.00E-21 14.2 (0.5) 4.6 (0.1) OVER 0 GO:0006366 transcription from Pol II promoter 845 0.225 (0.012) 0.130 (0.002) FASTER 1.88E-14 13.0 (0.5) 4.8 (0.1) OVER 0 GO:0006139 nucleobase, nucleoside, nucleotide and nucleic acid metabolism3004 0.173 (0.006) 0.127 (0.002) FASTER 1.28E-12 8.4 (0.2) 4.5 (0.1) OVER 0 GO:0006357 regulation of transcription from Pol II promoter 487 0.231 (0.016) 0.132 (0.002) FASTER 6.05E-10 13.5 (0.6) 4.9 (0.1) OVER 0 GO:0008283 cell proliferation 625 0.189 (0.014) 0.132 (0.002) FASTER 1.95E-05 10.1 (0.6) 5.0 (0.1) OVER 1.50E-20 GO:0006513 monoubiquitination 36 0.305 (0.049) 0.134 (0.002) FASTER 2.69E-04 25.4 (4.4) 5.1 (0.1) OVER 2.04E-06 GO:0007050 cell cycle arrest 57 0.311 (0.054) 0.133 (0.002) -
4. Empty Folders This Report Gives an Overview of All the Empty Folder and a List of Their Locations
File share analysis reports Introduction It is hard to find an organization that is not still using file shares. Nowadays, file shares are outdated, have high costs to maintain, create chaos due to the immense numbers of copies of files and insufficient ways of structuring them, and risk exposure is significant. Do you finally want to order this chaos and solve the problems it brings? Xillio file share analysis Xillio can perform extensive file share analysis, and generate reports in a very short time frame. You can run this process through your preferred systems integrator, or just let Xillio do the work. The analysis lets you understand which content on your file shares is redundant, obsolete and trivial. Or, gives insight in what content is located on your files shares in general. The Xillio file share analysis package includes a number of pre-built reports and analyses. This data is all captured using the delivered scripts and robots and stored in a database for easy access and reporting. This data may be further exported to Excel or integrated with another Business Intelligence tool of choice for further analysis. In this document Xillio explains the delivery of the file share analysis. Each report gives different insights, examples of which are also given in this document. These insights are not extensive, there are many other variations of these which can be produced to create your own new insights. To guide you through this process, for each report the most used insights that you can get out of it, is described. Report examples 1. -

Forcepoint DLP Supported File Formats and Size Limits
Forcepoint DLP Supported File Formats and Size Limits Supported File Formats and Size Limits | Forcepoint DLP | v8.8.1 This article provides a list of the file formats that can be analyzed by Forcepoint DLP, file formats from which content and meta data can be extracted, and the file size limits for network, endpoint, and discovery functions. See: ● Supported File Formats ● File Size Limits © 2021 Forcepoint LLC Supported File Formats Supported File Formats and Size Limits | Forcepoint DLP | v8.8.1 The following tables lists the file formats supported by Forcepoint DLP. File formats are in alphabetical order by format group. ● Archive For mats, page 3 ● Backup Formats, page 7 ● Business Intelligence (BI) and Analysis Formats, page 8 ● Computer-Aided Design Formats, page 9 ● Cryptography Formats, page 12 ● Database Formats, page 14 ● Desktop publishing formats, page 16 ● eBook/Audio book formats, page 17 ● Executable formats, page 18 ● Font formats, page 20 ● Graphics formats - general, page 21 ● Graphics formats - vector graphics, page 26 ● Library formats, page 29 ● Log formats, page 30 ● Mail formats, page 31 ● Multimedia formats, page 32 ● Object formats, page 37 ● Presentation formats, page 38 ● Project management formats, page 40 ● Spreadsheet formats, page 41 ● Text and markup formats, page 43 ● Word processing formats, page 45 ● Miscellaneous formats, page 53 Supported file formats are added and updated frequently. Key to support tables Symbol Description Y The format is supported N The format is not supported P Partial metadata -

IDOL Keyview Filter SDK 12.8 C Programming Guide
IDOL KeyView Software Version 12.8 Filter SDK C Programming Guide Document Release Date: February 2021 Software Release Date: February 2021 Filter SDK C Programming Guide Legal notices Copyright notice © Copyright 2016-2021 Micro Focus or one of its affiliates. The only warranties for products and services of Micro Focus and its affiliates and licensors (“Micro Focus”) are as may be set forth in the express warranty statements accompanying such products and services. Nothing herein should be construed as constituting an additional warranty. Micro Focus shall not be liable for technical or editorial errors or omissions contained herein. The information contained herein is subject to change without notice. Documentation updates The title page of this document contains the following identifying information: l Software Version number, which indicates the software version. l Document Release Date, which changes each time the document is updated. l Software Release Date, which indicates the release date of this version of the software. To check for updated documentation, visit https://www.microfocus.com/support-and-services/documentation/. Support Visit the MySupport portal to access contact information and details about the products, services, and support that Micro Focus offers. This portal also provides customer self-solve capabilities. It gives you a fast and efficient way to access interactive technical support tools needed to manage your business. As a valued support customer, you can benefit by using the MySupport portal to: l Search for knowledge documents of interest l Access product documentation l View software vulnerability alerts l Enter into discussions with other software customers l Download software patches l Manage software licenses, downloads, and support contracts l Submit and track service requests l Contact customer support l View information about all services that Support offers Many areas of the portal require you to sign in. -

Videoscape Quickstart Solution Installation and Configuration Guide
Videoscape Quickstart Configuration Guide Overview Introduction This document provides configuration guidelines for Cisco® Videoscape Quickstart. Release Details This section lists component version numbers and other details verified for this release. Release Type: Official Release Release Version: Quickstart Videoscape Media Suite (VMS) Version: VMS 4.1 Cisco Transcode Manager (CTM) Version: CTM 4.1 Content Delivery System-Internet Streaming (CDS-IS) Version: CDS-IS 2.5.11 Videoscape Quickstart Soft Client Version: Quickstart (1.0) Core Functions Videoscape Quickstart establishes core functions for the On-the-Go subscriber experience for TV Everywhere: 1 Content Preparation—Create multiple representations of the same VOD asset to support Adaptive Bit Rate Streaming received from multiple locations 2 Subscriber Authentication—Authenticate or deny access of a user to the on-line video portal 3 Entitlement—Enforce entitlement policies defined by the operator 4 Content Protection—Deliver encrypted version of VOD assets being offered through the on-line portal 5 Content Distribution—Stream or download a VOD asset to a portable device [ Document Version This is the first formal release of this document. OL-26112-01 1 Terms and Acronyms Terms and Acronyms The following table lists terms and acronyms used throughout this document. Term or Acronym Description ABR Adaptive Bit Rate Armada Legacy name of the application suite, formerly developed by Inlet, Inc., on which the CTM 4.1 suite is built. CDN Content Delivery Network CDS-IS Content Delivery System for Internet Streaming CDSM Content Delivery System Manager CTM Cisco Transcode Manager DRM Digital Rights Management OpenCASE Legacy name of the application suite, formerly developed by Extend Media, Inc., on which the Videoscape Quickstart Soft Client is built. -

Firmware Analysis of Linksys E900 V. 1.0.09.002
Firmware Analysis of Linksys E900 v. 1.0.09.002 HID Linksys E900 v. 1.0.09.002 Device Name E900 Vendor Linksys Device Class Routers Version 1.0.09.002 Release Date 1970-01-01 Size 7.39 MiB (7,746,560 Byte) Unpacker (v. 0.7) Plugin generic carver Extracted 2 Output: DECIMAL HEXADECIMAL DESCRIPTION ——————————————————————————– 0 0x0 BIN-Header, board ID: E900, hardware version: 4702, firmware v ersion: 1.0.0, build date: 2018-08-08 32 0x20 TRX firmware header, little endian, image size: 7745536 bytes, CRC32: 0x756770AD, flags: 0x0, version: 1, header size: 28 bytes, loader offset: 0x1C, linux kernel offset: 0x14FDFC, rootfs offset: 0x0 60 0x3C gzip compressed data, maximum compression, has original file n ame: ”piggy”, from Unix, last modified: 2018-08-08 05:28:28 1375772 0x14FE1C Squashfs filesystem, little endian, non-standard signature, ve rsion 3.0, size: 6365444 bytes, 1718 inodes, blocksize: 65536 bytes, created: 2018-08-08 05:33:15 Entropy 0.89 1 File Type (v. 1.0) File Type data MIME application/octet-stream Containing Files application/CDFV2 (2) application/gzip (1) application/octet-stream (3) application/x-executable (67) application/x-object (27) application/x-sharedlib (116) filesystem/squashfs (1) image/gif (42) image/jpeg (8) image/png (17) image/x-icon (1) inode/symlink (7) text/plain (990) 2 Binwalk (v. 0.5.2) Signature Analysis: DECIMAL HEXADECIMAL DESCRIPTION ——————————————————————————– 0 0x0 BIN-Header, board ID: E900, hardware version: 4702, firmware version: 1.0.0, build date: 2018-08-08 32 0x20 TRX firmware header, little endian, -

ASHS Is Inviting/Encouraging Poster Presenters to Up- Posters: Load a PDF of Their Poster
vt- •• ��t E�. Gallo Winery � BalL American Funding Generations of Floral Progress Through Research Image Analysis for Plant Science Endowment and Scholarships 1 of 262 General Information Conference Facilities: Speaker Ready Room: All Conference activities will take place at the Tropicana Oral, Workshop, Special Sessions, and Keynote speakers Las Vegas. are requested to check in at the Speaker Ready Room located in Churchill. Please note, even if you have Registration hours: uploaded in advance, you are still asked to check in at the Speaker Ready room at least 24 hours in advance of Sunday, July 21. .3:00 PM – 6:00 PM your presentation to confirm that your media and Pow- erPoint presentations were successfully uploaded and Monday, July 22 .............7:30 AM – 6:00 PM running properly. Updates and modifications can only Tuesday, July 23. 7:30 AM – 6:00 PM be made up to 24 hours in advance of your presentation. Wednesday, July 24. .7:30 AM – 5:00 PM Thursday, July 25 ............7:30 AM – 2:00 PM Poster Presenters and E-Posters: ASHS is inviting/encouraging poster presenters to up- Posters: load a PDF of their poster. You may also upload mp4 video or audio files to go along with the poster. Posters are located in Cohiba 5-12. As part of enhancing the ASHS online conference proceedings, you have the option to make your poster Poster Set Up: into an interactive electronic version (E-Poster). If you would like to explore this option, a link will appear once Monday, July 22 .............2:00 PM – 5:00 PM you have uploaded your PDF file with instructions on how to create your E-Poster. -

I102.PDF (7.191Mb)
PuUis/ied witA t/2e a~,probatio,z o t/ze Board o Trustees XOL. XII.—No. 102.] BALTIMORE, JANUARY, 1893. [PRICE, 10 CENTS. I~OTES IN PHILOLOGY. The Limitation of the Imperative in the Attic Ora- directly or imidirectl y, from the point of view of mercy, kindness, justice, tors. By C. W. E. MILLER. fairn~es, propriety, tutilily, moral obligation, absolute necessity, etc. The following are somine of the actually occuirring substitutes: l~o~ram ~rc~m’,~?, (Abstract of a paper read before tbe American Phflolo ~ ~sos and Ir’tcasov used personally, i~er’Aw, xpoo%ces, eimc6s, ai.m-o~,mcas, &~L&, 6ical Association, July, 1892, and d~moe, liucamoe’, oornp~psr, eie-~pduo w. inf.; eimc~-ws, Ismcatcmmc &m’ w. opt.; c’dm’ with before the University PhilologicalAssociation, October 28, 1892.) subjunctive or ci witir optative; tine verbal in -n-iou’ and ~p-~’ov with the An examination of the use of the imperative in tire Attic osators, that benitive or tine possessive prosroun followed by tine infinitive. was undertaken to ascertain the Greek fooling of the imperativo, showed To an emrtiu-ely differ-eat sphere belong tire mnse of the so-called imperative that the harsh tonse attributed to the imperative by lJernrobenes* gave rise question anti tire imperative use offfmramv with tine future indicative. These to certain limitations as to tire use of this mode.’ In tho discussion of these are snot nnolhifying substitutes for the imperative. oirwn- with the future limitations the following order has boon found convenient. indierstive is undoubtedly colloqtuial, as the statistics given by Weber, 1. -
Designing Silverlight® Business Applications
Praise for Designing Silverlight® Business Applications “Jeremy’s writing style and approach to this broad subject has produced a very readable book. Beginners won’t be lost or discouraged, and there’s plenty of serious content for the experienced developer. This book will be open on your desk for reference while you’re coding.” —Dave Campbell, SilverlightCream.com “I strongly recommend this book to anyone seriously interested in developing applications with Silverlight. The book is written in an easy-to-read style and answers those tough questions that you would normally spend hours searching the Net for.” —Michael Crump, Microsoft MVP, michaelcrump.net “Jeremy explores Silverlight well beyond the basics, while maintaining crystal clarity about each subject. Should be on every Silverlight developer’s bookshelf.” —Jesse Liberty, Developer Evangelist, Telerik “What’s cooking in Jeremy’s kitchen? Silverlight delicacies that will benefit every Silverlight developer, regardless of experience level. And worth the price for the information on MVVM and MEF alone.” —Jeff Prosise, Cofounder, Wintellect “This book is a must-read for anyone writing business applications using Silverlight. Jeremy has combined his clear and precise writing style with great code examples in a book that is both instructive and enjoyable to read.” —Beatriz Stollnitz, President, Zag Studio “This book is a great companion for any Silverlight developer building or looking to build enterprise applications. Jeremy does a great job covering Silverlight concepts and techniques, -

Xap Files Download
Xap files download click here to download Download WhatsApp XAP File v for Windows Phone. WhatsApp is a free and useful Social app. Download and install manually now. Download Files XAP File v for Windows Phone. Files is a free and useful Productivity app. Download and install manually now. Asphalt 8: Airborne: August 24, Download. 2. Castle Clash: August for Windows Phone. Goal Centre XAP - Free Sports App for Windows Phone Apps · Games · Appx4Fun - Top Windows · Top Games. We have all best and latest windows phone apps and www.doorway.ruad Free Xap games, appx download for windows phone,windows 10 phone www.doorway.ru It is a quick guide to download xap files from mobile and INSTALL it on your Windows Phone! Presented by. After the updation of the Store I cannot find any option to download XAP files. Earlier there was this option saying "Download and install how i can install XAP files on windows Phone 10? It's not possible anymore to download the app files (xap or the new package format appx) directly from the Microsoft Store homepage. There are. But, if you have a device with Windows Phone 8, or higher, and an SD card slot then you can download www.doorway.ru file and install it manually. A description for this result is not available because of this site's www.doorway.ru So guys today i am going to show you how to download and install APPX and XAP files directly in windows 10 pc or any tablet what ever you. XAP files for apps in your computer. -

Forcepoint Email Security Cloud Help
Forcepoint Cloud Security Gateway Portal Help Forcepoint Email Security Cloud 2021 ©2021 Forcepoint Forcepoint. Forcepoint and the FORCEPOINT logo are trademarks of Forcepoint. All other trademarks used in this document are the property of their respective owner. Every effort has been made to ensure the accuracy of this document. However, Forcepoint makes no warranties with respect to this documentation and disclaims any implied warranties of merchantability and fitness for a particular purpose. Forcepoint shall not be liable for any error or for incidental or consequential damages in connection with the furnishing, performance, or use of this manual or the examples herein. The information in this documentation is subject to change without notice. Last modified: June 25, 2021 Contents Chapter 1 Getting Started . .1 About this guide . .2 Initial steps . .3 Logging on and portal security. .3 Locking down your firewalls . .4 Privacy statement . .4 Idle timeout . .4 Customizable landing page . .4 Cloud portal navigation . .5 Dashboard . .6 Alerts . .7 Chapter 2 Account Settings . .9 My Account . .10 Configuring SIEM storage . .10 Contacts . .12 Adding a contact . .12 Password settings . .16 Password policy . .17 Password expiration limit . .18 User lockout . .18 Changing passwords . .19 Forgotten passwords . .20 Two-factor authentication . .21 Terms of use. .22 Custom file types . .23 Identity Management . .23 End Users . .24 Groups . .25 Downloading and uploading groups . .25 Licenses . .26 Licenses page . .27 License information. .27 Accepting licenses. .27 Data Protection Settings . .28 Important rules for configuring accounts . .29 Chapter 3 Working with External Directories. .31 Forcepoint Cloud Security Gateway Portal Help 1 Contents What is LDAP?. -

Differences Winzip Standard Pro Enterprise
http://www.winpro.com.sg GST Reg : 02-0117585-2 Co Reg : 199305875R “WE POWERING BUSINESS” WinZip WinZip WinZip Com press/Decompress Standard Pro Enterprise NEW ! Compress smaller Zipx files faster. √ √ √ ENHAN CED! Switch between Zip and Zipx file creation with a simple Ribbon toggle. √ √ √ ENHAN CED! Choose to save as Zip or Zipx when saving files. √ √ √ Drag and Drop ‘Add to Zip’ in WinZip’s Files Pane. √ √ √ Direct Access Technology for faster display and unzipping. √ √ √ Quickl y unzip to the folder displayed in the WinZip Files Pane with the click of a button. √ √ √ Convenient prompts simplify unzipping Zip files from Explorer, the WinZip Files Pane, and the √ √ √ WinZ ip Ribbon or File menu to your choice of folders Open and unzip POSIX TAR files √ √ √ Enjoy up to 50% faster start-up performance √ √ √ Unzip and replace a group of Zip files with their content √ √ √ Create a split Zip file from Explorer for hassle-free sharing of large files √ √ √ Open more files types as a Zip, including DOCX, XLSX, PPTX, XPS, ODT, ODS, ODP, √ √ √ ODG,WMZ, WSZ, YFS, XPI, XAP, CRX, EPUB, and C4Z Use the super picker to unzip locally or to the cloud √ √ √ Get up to speed quickly with the Interactive Welcome Screen √ √ √ Compress MP3 files by 15 - 20 % on average √ √ √ Zip and unzip files instantly with 64-bit, best-in-class software √ √ √ Open and extract Zipx, RAR, 7Z, LHA, BZ2, IMG, ISO and all other major compression file √ √ √ formats Open CAB, Zip and Zip 2.0 Methods √ √ √ Convert other major compressed file formats to Zip format √ √ √ Apply