CS/IT423 Hall Ticket Number
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
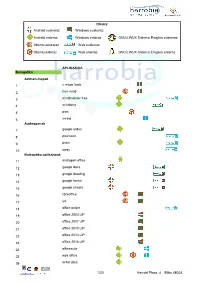
Android Euskaraz Windows Euskaraz Android Erderaz Windows Erderaz GNU/LINUX Sistema Eragilea Euskeraz Ubuntu Euskaraz We
Oharra: Android euskaraz Windows euskaraz Android erderaz Windows erderaz GNU/LINUX Sistema Eragilea euskeraz Ubuntu euskaraz Web euskaraz Ubuntu erderaz Web erderaz GNU/LINUX Sistema Eragilea erderaz APLIKAZIOA Bulegotika Adimen-mapak 1 c maps tools 2 free mind 3 mindmeister free 4 mindomo 5 plan 6 xmind Aurkezpenak 7 google slides 8 pow toon 9 prezi 10 sway Bulegotika-aplikazioak 11 andropen office 12 google docs 13 google drawing 14 google forms 15 google sheets 16 libreoffice 17 lyx 18 office online 19 office 2003 LIP 20 office 2007 LIP 21 office 2010 LIP 22 office 2013 LIP 23 office 2016 LIP 24 officesuite 25 wps office 26 writer plus 1/20 Harrobi Plaza, 4 Bilbo 48003 CAD 27 draftsight 28 librecad 29 qcad 30 sweet home 31 timkercad Datu-baseak 32 appserv 33 dbdesigner 34 emma 35 firebird 36 grubba 37 kexi 38 mysql server 39 mysql workbench 40 postgresql 41 tora Diagramak 42 dia 43 smartdraw Galdetegiak 44 kahoot Maketazioa 45 scribus PDF editoreak 46 master pdf editor 47 pdfedit pdf escape 48 xournal PDF irakurgailuak 49 adobe reader 50 evince 51 foxit reader 52 sumatraPDF 2/20 Harrobi Plaza, 4 Bilbo 48003 Hezkuntza Aditzak lantzeko 53 aditzariketak.wordpress 54 aditz laguntzailea 55 aditzak 56 aditzak.com 57 aditzapp 58 adizkitegia 59 deklinabidea 60 euskaljakintza 61 euskera! 62 hitano 63 ikusi eta ikasi 64 ikusi eta ikasi bi! Apunteak partekatu 65 flashcard machine 66 goconqr 67 quizlet 68 rincon del vago Diktaketak 69 dictation Entziklopediak 70 auñamendi eusko entziklopedia 71 elhuyar zth hiztegi entziklopedikoa 72 harluxet 73 lur entziklopedia tematikoa 74 lur hiztegi entziklopedikoa 75 wikipedia Esamoldeak 76 AEK euskara praktikoa 77 esamoldeapp 78 Ikapp-zaharrak berri Estatistikak 79 pspp 80 r 3/20 Harrobi Plaza, 4 Bilbo 48003 Euskara azterketak 81 ega app 82 egabai 83 euskal jakintza 84 euskara ikasiz 1. -

Antivirus Software Before It Can Detect Them
Computer virus A computer virus is a computer program that can copy itself and infect a computer without the permission or knowledge of the owner. The term "virus" is also commonly but erroneously used to refer to other types of malware, adware, and spyware programs that do not have the reproductive ability. A true virus can only spread from one computer to another (in some form of executable code) when its host is taken to the target computer; for instance because a user sent it over a network or the Internet, or carried it on a removable medium such as a floppy disk, CD, DVD, or USB drive. Viruses can increase their chances of spreading to other computers by infecting files on a network file system or a file system that is accessed by another computer.[1][2] The term "computer virus" is sometimes used as a catch-all phrase to include all types of malware. Malware includes computer viruses, worms, trojan horses, most rootkits, spyware, dishonest adware, crimeware, and other malicious and unwanted software), including true viruses. Viruses are sometimes confused with computer worms and Trojan horses, which are technically different. A worm can exploit security vulnerabilities to spread itself to other computers without needing to be transferred as part of a host, and a Trojan horse is a program that appears harmless but has a hidden agenda. Worms and Trojans, like viruses, may cause harm to either a computer system's hosted data, functional performance, or networking throughput, when they are executed. Some viruses and other malware have symptoms noticeable to the computer user, but many are surreptitious. -
Linux Security Review 2015
Linux Security Review 2015 www.av-comparatives.org AV-Comparatives Linux Security Review Language: English May 2015 Last revision: 26 th May 2015 www.av-comparatives.org -1- Linux Security Review 2015 www.av-comparatives.org Contents Introduction ....................................................................................................................... 3 Reviewed products ............................................................................................................... 4 Malware for Linux systems ..................................................................................................... 5 Linux security advice ............................................................................................................ 6 Items covered in the review .................................................................................................. 7 Avast File Server Security ...................................................................................................... 8 AVG Free Edition for Linux.................................................................................................... 11 Bitdefender Antivirus Scanner for Unices ................................................................................ 13 Clam Antivirus for Linux ....................................................................................................... 17 Comodo Antivirus for Linux .................................................................................................. 20 Dr.Web Anti-virus for -

Technical Report RHUL–ISG–2021–3 10 March 2021
Testing Antivirus in Linux: An Investigation on the Effectiveness of Solutions Available for Desktop Computers Giuseppe Raffa Technical Report RHUL–ISG–2021–3 10 March 2021 Information Security Group Royal Holloway University of London Egham, Surrey, TW20 0EX United Kingdom Student Number: 100907703 Giuseppe Raffa Testing Antivirus in Linux: An Investigation on the Effectiveness of Solutions Available for Desktop Computers Supervisor: Daniele Sgandurra Submitted as part of the requirements for the award of the MSc in Information Security at Royal Holloway, University of London. I declare that this assignment is all my own work and that I have acknowledged all quotations from published or unpublished work of other people. I also declare that I have read the statements on plagiarism in Section 1 of the Regulations Governing Examination and Assessment Offences, and in accordance with these regulations I submit this project report as my own work. Signature: Giuseppe Raffa Date: 24th August 2020 Table of Contents 1 Introduction.....................................................................................................................7 1.1 Motivation.......................................................................................................................................7 1.2 Objectives........................................................................................................................................8 1.3 Methodology...................................................................................................................................8 -
SAFETY GUIDE for JOURNALISTS a Handbook for Reporters in High-Risk Environments
SAFETY GUIDE FOR JOURNALISTS A handbook for reporters in high-risk environments United Nations Educational, Scientific and Cultural Organization REPORTERS WITHOUT BORDERS 1 REPORTERS WITHOUT BORDERS 1 SAFETY GUIDE FOR JOURNALISTS A handbook for reporters in high-risk environments United Nations Educational, Scientific and Cultural Organization CONTENTS PREFACE...........................................................................................................................................4 INTRODUCTION: RSF and the protection of journalists...........................10 CHAPTER 1: The growing risks for journalists................................................13 CHAPTER 2: Planning and preparation..................................................................15 1. Local knowledge and risk assessment..................................................15 2. Health precautions.................................................................................................18 3. First aid and hostile environment training...........................................20 4. Finances, formalities, family: set off with peace of mind.......21 5. Preparing your kitbag: checklists...............................................................23 CHAPTER 3: Keeping safe on assignment........................................................30 1. Accommodation, travel and communications..................................30 2. Safety precautions in war zones.................................................................36 3. Mines and cluster munitions..........................................................................45 -

Clam Antivirus 0.88.2 User Manual Contents 1
Clam AntiVirus 0.88.2 User Manual Contents 1 Contents 1 Introduction 6 1.1 Features.................................. 6 1.2 Mailinglists................................ 7 1.3 Virussubmitting.............................. 7 2 Base package 7 2.1 Supportedplatforms............................ 7 2.2 Binarypackages.............................. 8 2.3 Dailybuiltsnapshots ........................... 10 3 Installation 11 3.1 Requirements ............................... 11 3.2 Installingonashellaccount . 11 3.3 Addingnewsystemuserandgroup. 12 3.4 Compilationofbasepackage . 12 3.5 Compilationwithclamav-milterenabled . .... 12 4 Configuration 13 4.1 clamd ................................... 13 4.1.1 On-accessscanning. 13 4.2 clamav-milter ............................... 14 4.3 Testing................................... 14 4.4 Settingupauto-updating . 15 4.5 Closestmirrors .............................. 16 5 Usage 16 5.1 Clamdaemon ............................... 16 5.2 Clamdscan ................................ 17 5.3 Clamuko.................................. 17 5.4 Outputformat............................... 18 5.4.1 clamscan ............................. 18 5.4.2 clamd............................... 19 6 LibClamAV 20 6.1 Licence .................................. 20 6.2 Features.................................. 20 6.2.1 Archivesandcompressedfiles . 20 6.2.2 Mailfiles ............................. 21 Contents 2 6.3 API .................................... 21 6.3.1 Headerfile ............................ 21 6.3.2 Databaseloading . .. .. .. .. .. . -

Hostscan 4.9.06037 Antimalware and Firewall Support Charts
HostScan 4.9.06037 Antimalware and Firewall Support Charts 2/5/2021 © 2021 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 92 [Type here] Contents HostScan Version 4.9.06037 Antimalware and Firewall Support Charts ............................................................................... 3 Antimalware and Firewall Attributes Supported by HostScan .................................................................................................. 3 OPSWAT Version Information ................................................................................................................................................. 5 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.1634.0 for Windows .............................................. 50 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.1634.0 for Windows ...................................................... 50 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.1501.0 for macOS………………………….…..……80 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.1501.0 for macOS…………….…….……………..………90 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.1333.0 for Linux…………….……..…..…….………94 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.1333.0 for Linux…………………………………..……….96 ©2021 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. Page 2 of 92 [Type here] HostScan Version 4.9.06037 Antimalware and Firewall Support Charts The VPN Posture (HostScan) module provides the AnyConnect -

License Information GNU General Public License
################################################################# ################################################################# ####### ####### ####### Open Icon Library ####### ####### License File ####### ####### ####### ################################################################# ################################################################# Table of Contents: * Description * Sources * Licenses * File List * Icons from Wikicommons * Icons under Creative Commons licenses * Icons under GPL and LGPL licenses * Icons under Public Domain * Icons under MIT license * Icons under BSD license * Icons from app-install-data ################################################################# ## Description: The Open Icon Library contains icons from various sources. This file list the license and source of each file in this package. In the rare occasion where there is two files with the same name, you will have to check the developers package. If you wish to use these icons in your project, include this file in your projects documentation. ################################################################# ## Sources: AEM Pictorial Database (aem) link: http://www.aem.org/Technical/PictorialDatabase/index.asp license: PD license link: http://en.wikipedia.org/wiki/Public_domain format: eps -> svg, png subdirectory: open_icon_library-devel/icons/aem app-install-data (app-install) link: http://packages.debian.org/lenny/app-install-data licenses: Various, see docs/AUTHORS_app-install license link: see docs/AUTHORS_app-install format: xpm, svg, -

Antivirus Para Armar… O Más Bien, Hágalo Usted Mismo
Antivirus para armar… o más bien, hágalo usted mismo M.Sc. Alberto García Fumero FLISOL 2014 Ciudad de La Habana ClamAV (Clam antivirus) El proyecto ClamAV Antivirus fue fundado en el año 2001 por Tomasz Kojm. Nació como un proyecto opensource que pretende identificar y bloquear virus en el sistema. Pero...¿y por qué? ¿qué sentido tiene? ¿Acaso hay virus en Linux o UNIX? (Porque todo el mundo me dice que a Linux no le entran los virus, y yo he visto que las máquinas Windows se infectan y esas no...) Una de las vulnerabilidades de GNU/Linux (en realidad, vulnerabilidad de sus usuarios) es que multitud de usuarios piensan que Linux no es vulnerable a los virus. Los virus y ataques malintencionados presentan una amenaza real a los sistemas Linux. Si un binario infectado contiene uno de esos virus, al ser ejecutado el binario, el sistema se infectaría. el nivel de infección dependerá de los privilegios del usuario que ejecutó el programa. Por eso se recomienda tanto no trabajar con nivel de root a no ser que resulte imprescindible. Normalmente uno no trabaja (no debería trabajar) con la cuenta root. Para eso existen sudo y las tantísimas cuentas que crean las aplicaciones que necesitan permisos especiales. Si el virus entra por la cuenta de superusuario podría llegar a infectar el sistema entero. En caso de un usuario normal, el sistema operativo estaría seguro aunque los datos del usuario no. El virus podría borrar e incluso enviar esos datos a otro equipo remoto. Por otro lado, las vulnerabilidades de escalada de privilegios pueden permitir que malware ejecutándose bajo una cuenta de acceso limitado también se propague por todo el sistema. -
Computer Security 37 8.1 Vulnerabilities
Contents 1 Antivirus software 1 1.1 History ................................................ 1 1.1.1 1949-1980 period (pre-antivirus days) ............................ 1 1.1.2 1980-1990 period (early days) ................................ 2 1.1.3 1990-2000 period (emergence of the antivirus industry) ................... 2 1.1.4 2000-2005 period ...................................... 3 1.1.5 2005 to present ........................................ 3 1.2 Identification methods ........................................ 4 1.2.1 Signature-based detection .................................. 4 1.2.2 Heuristics ........................................... 4 1.2.3 Rootkit detection ....................................... 5 1.2.4 Real-time protection ..................................... 5 1.3 Issues of concern ........................................... 5 1.3.1 Unexpected renewal costs ................................... 5 1.3.2 Rogue security applications .................................. 5 1.3.3 Problems caused by false positives .............................. 5 1.3.4 System and interoperability related issues ........................... 6 1.3.5 Effectiveness ......................................... 6 1.3.6 New viruses .......................................... 6 1.3.7 Rootkits ............................................ 6 1.3.8 Damaged files ......................................... 6 1.3.9 Firmware issues ........................................ 7 1.4 Performance and other drawbacks .................................. 7 1.5 Alternative solutions -

Clam Antivirus Mac Free Download
Clam Antivirus Mac Free Download Clam Antivirus Mac Free Download 1 / 3 Sadly, there is no version of ClamWin Antivirus for Mac available for download, but there are plenty other virus protection tools that you can use instead.. 0/10 0/11 0 (PowerPC/Intel), and many more programs ClamTk is an open source desktop application that provides users with a graphical front-end for the well known Clam AntiVirus virus scanner application that runs on Linux-based operating systems. 1. clam antivirus 2. clam antivirus mac 3. clam antivirus ubuntu Download ClamWin Free Antivirus and get free virus scanning and free virus definition updates.. ClamWin Antivirus by Alch is an open-source antivirus application that will help you protect your system against various types of viruses, spyware, trojans and other malware.. Thank you for choosing ClamXAV – your download will begin in a moment If nothing seems to be happening, try the direct download link.. Clamxav Antivirus Mac DownloadClam Antivirus Mac Free Download CnetClam Antivirus ReviewDownload ClamWin Free Antivirus - Antimalware solution that has a scheduler, virus database updater, standalone scanner, context menu integration, and more features. clam antivirus clam antivirus, clam antivirus windows, clam antivirus mac, clam antivirus review, clam antivirus ubuntu, clam antivirus for linux, clamwin antivirus free download, clam antivirus real time scanning, clam antivirus windows 10, clamav antivirus download Unduh Zombie Defense Escape Mod Apk Data File Host App name: clamav 0 99 2App description: Anti-virus softwareApp website: http://www.. 000 viruses, worms and trojans in order to protect your computer and email from security threats. -

Linux Software Superstore APCUG Winter 2015 Virtual Technology
Linux Software Superstore APCUG Winter 2015 Virtual Technology Conference February 21, 2015 Linux Software Superstore Presentation by: John Kennedy, Co-Leader Linux Help Desk/SIG East Central Ohio Technology Users Club Newark, Ohio Linux Software Superstore Aisle 1 Aisle 2 Internet Productivity Aisle 3 Aisle 4 Multimedia Graphics Aisle 5 Aisle 6 Desktop Tools Disk/File Tools Aisle 7 Aisle 8 Games Security What You'll See In my series of slides, I will share with you the different areas of computer tasks and some of the programs that are available to complete those tasks. In small print I will sometimes include the names for some of the Microsoft products that you might use. Then I will share with you some actual screen shots of the programs that I like to use with Linux to complete my routine computer tasks. Aisle 1: Internet lBrowsers (Internet Explorer) lFirefox, Chromium (Chrome), Opera, Midori lE-mail Clients (Outlook Express) lThunderbird, Evolution, kMail lRemote Access lTeamviewer lCommunications (VoIP) (chat) lSkype, Pidgin, Empathy, Ekiga lFile Transfer Protocol (FTP) Client lFilleZilla Aisle 2: Productivity lOffice Suite (MS Office) lLibreOffice, OpenOffice, Koffice lDesktop Publishing (MS Publisher) lScribus lWord Processor/Spreadsheet lAbiWord / Gnumeric lPDF Reader (Adobe Reader) lEvince, Okular lPersonal Finance (Quicken) lGnuCash, KMyMoney Aisle 3: Multimedia lPlayers (Media Player) lVLC, Rhythmbox, Banshee, SMPlayer lCD/DVD Burning (Roxio, Nero) lK3b, Brasero, Xfburn lAudio/Video Editing (Windows Movie Maker) lAudacity / Avidemux, OpenShot lDVD Authoring lDeVeDe, Kdenlive, Cinelerra Aisle 4: Graphics lViewers (Photo Viewer, Photo Gallery) lEye of Gnome, Gwenview, gThumb lManagers lDigiKam, F-Spot, lEditors lShotwell, F-Spot, Pinta, Fotoxx, DigiKam, Darktable, G.I.M.P.