How Can I Tell If My Computer Has a Virus? How Do I Find and Remove
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Symantec Report on Rogue Security Software July 08 – June 09
REPORT: SYMANTEC ENTERPRISE SECURITY SYMANTEC REPORT: Symantec Report on Rogue Security Software July 08 – June 09 Published October 2009 Confidence in a connected world. White Paper: Symantec Enterprise Security Symantec Report on Rogue Security Software July 08 – June 09 Contents Introduction . 1 Overview of Rogue Security Software. 2 Risks . 4 Advertising methods . 7 Installation techniques . 9 Legal actions and noteworthy scam convictions . 14 Prevalence of Rogue Security Software . 17 Top reported rogue security software. 17 Additional noteworthy rogue security software samples . 25 Top rogue security software by region . 28 Top rogue security software installation methods . 29 Top rogue security software advertising methods . 30 Analysis of Rogue Security Software Distribution . 32 Analysis of Rogue Security Software Servers . 36 Appendix A: Protection and Mitigation. 45 Appendix B: Methodologies. 48 Credits . 50 Symantec Report on Rogue Security Software July 08 – June 09 Introduction The Symantec Report on Rogue Security Software is an in-depth analysis of rogue security software programs. This includes an overview of how these programs work and how they affect users, including their risk implications, various distribution methods, and innovative attack vectors. It includes a brief discussion of some of the more noteworthy scams, as well as an analysis of the prevalence of rogue security software globally. It also includes a discussion on a number of servers that Symantec observed hosting these misleading applications. Except where otherwise noted, the period of observation for this report was from July 1, 2008, to June 30, 2009. Symantec has established some of the most comprehensive sources of Internet threat data in the world through the Symantec™ Global Intelligence Network. -
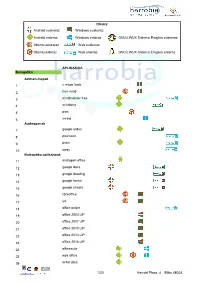
Android Euskaraz Windows Euskaraz Android Erderaz Windows Erderaz GNU/LINUX Sistema Eragilea Euskeraz Ubuntu Euskaraz We
Oharra: Android euskaraz Windows euskaraz Android erderaz Windows erderaz GNU/LINUX Sistema Eragilea euskeraz Ubuntu euskaraz Web euskaraz Ubuntu erderaz Web erderaz GNU/LINUX Sistema Eragilea erderaz APLIKAZIOA Bulegotika Adimen-mapak 1 c maps tools 2 free mind 3 mindmeister free 4 mindomo 5 plan 6 xmind Aurkezpenak 7 google slides 8 pow toon 9 prezi 10 sway Bulegotika-aplikazioak 11 andropen office 12 google docs 13 google drawing 14 google forms 15 google sheets 16 libreoffice 17 lyx 18 office online 19 office 2003 LIP 20 office 2007 LIP 21 office 2010 LIP 22 office 2013 LIP 23 office 2016 LIP 24 officesuite 25 wps office 26 writer plus 1/20 Harrobi Plaza, 4 Bilbo 48003 CAD 27 draftsight 28 librecad 29 qcad 30 sweet home 31 timkercad Datu-baseak 32 appserv 33 dbdesigner 34 emma 35 firebird 36 grubba 37 kexi 38 mysql server 39 mysql workbench 40 postgresql 41 tora Diagramak 42 dia 43 smartdraw Galdetegiak 44 kahoot Maketazioa 45 scribus PDF editoreak 46 master pdf editor 47 pdfedit pdf escape 48 xournal PDF irakurgailuak 49 adobe reader 50 evince 51 foxit reader 52 sumatraPDF 2/20 Harrobi Plaza, 4 Bilbo 48003 Hezkuntza Aditzak lantzeko 53 aditzariketak.wordpress 54 aditz laguntzailea 55 aditzak 56 aditzak.com 57 aditzapp 58 adizkitegia 59 deklinabidea 60 euskaljakintza 61 euskera! 62 hitano 63 ikusi eta ikasi 64 ikusi eta ikasi bi! Apunteak partekatu 65 flashcard machine 66 goconqr 67 quizlet 68 rincon del vago Diktaketak 69 dictation Entziklopediak 70 auñamendi eusko entziklopedia 71 elhuyar zth hiztegi entziklopedikoa 72 harluxet 73 lur entziklopedia tematikoa 74 lur hiztegi entziklopedikoa 75 wikipedia Esamoldeak 76 AEK euskara praktikoa 77 esamoldeapp 78 Ikapp-zaharrak berri Estatistikak 79 pspp 80 r 3/20 Harrobi Plaza, 4 Bilbo 48003 Euskara azterketak 81 ega app 82 egabai 83 euskal jakintza 84 euskara ikasiz 1. -
Rootkit- Rootkits.For.Dummies 2007.Pdf
01_917106 ffirs.qxp 12/21/06 12:04 AM Page i Rootkits FOR DUMmIES‰ 01_917106 ffirs.qxp 12/21/06 12:04 AM Page ii 01_917106 ffirs.qxp 12/21/06 12:04 AM Page iii Rootkits FOR DUMmIES‰ by Larry Stevenson and Nancy Altholz 01_917106 ffirs.qxp 12/21/06 12:04 AM Page iv Rootkits For Dummies® Published by Wiley Publishing, Inc. 111 River Street Hoboken, NJ 07030-5774 www.wiley.com Copyright © 2007 by Wiley Publishing, Inc., Indianapolis, Indiana Published by Wiley Publishing, Inc., Indianapolis, Indiana Published simultaneously in Canada No part of this publication may be reproduced, stored in a retrieval system or transmitted in any form or by any means, electronic, mechanical, photocopying, recording, scanning or otherwise, except as permit- ted under Sections 107 or 108 of the 1976 United States Copyright Act, without either the prior written permission of the Publisher, or authorization through payment of the appropriate per-copy fee to the Copyright Clearance Center, 222 Rosewood Drive, Danvers, MA 01923, (978) 750-8400, fax (978) 646-8600. Requests to the Publisher for permission should be addressed to the Legal Department, Wiley Publishing, Inc., 10475 Crosspoint Blvd., Indianapolis, IN 46256, (317) 572-3447, fax (317) 572-4355, or online at http://www.wiley.com/go/permissions. Trademarks: Wiley, the Wiley Publishing logo, For Dummies, the Dummies Man logo, A Reference for the Rest of Us!, The Dummies Way, Dummies Daily, The Fun and Easy Way, Dummies.com, and related trade dress are trademarks or registered trademarks of John Wiley & Sons, Inc. and/or its affiliates in the United States and other countries, and may not be used without written permission. -

PC Anti-Virus Protection 2011
PC Anti-Virus Protection 2011 12 POPULAR ANTI-VIRUS PROGRAMS COMPARED FOR EFFECTIVENESS Dennis Technology Labs, 03/08/2010 www.DennisTechnologyLabs.com This test aims to compare the effectiveness of the most recent releases of popular anti-virus software1. The products include those from Kaspersky, McAfee, Microsoft, Norton (Symantec) and Trend Micro, as well as free versions from Avast, AVG and Avira. Other products include those from BitDefender, ESET, G-Data and K7. The tests were conducted between 07/07/2010 and 22/07/2010 using the most up to date versions of the software available. A total of 12 products were exposed to genuine internet threats that real customers could have encountered during the test period. Crucially, this exposure was carried out in a realistic way, reflecting a customer’s experience as closely as possible. For example, each test system visited real, infected websites that significant numbers of internet users were encountering at the time of the test. These results reflect what would have happened if those users were using one of the seven products tested. EXECUTIVE SUMMARY Q Products that block attacks early tended to protect the system more fully The nature of web-based attacks means that the longer malware has access to a system, the more chances it has of downloading and installing further threats. Products that blocked the malicious and infected websites from the start reduced the risk of compromise by secondary and further downloads. Q 100 per cent protection is rare This test recorded an average protection rate of 87.5 per cent. New threats appear online frequently and it is inevitable that there will be times when specific security products are unable to protect from some of these threats. -

Solutions for Increased Productivity Simple “Do-It-Yourself” Tips For
_ Solutions for Increased Productivity Simple “Do-it-Yourself” tips for speeding up your Computer So your computer is running slow. There are numerous things that can cause a slow PC. They are: • Spyware Programs running in the background without your knowledge. (Programs that spy on your surfing habits, etc, and report this info to someone else.) • Viruses, Trojans and other forms of Malware ( Mal icious Soft ware ). • Fragmented File Systems. • Lack of Hard Drive Space. • System Tray Overload After we look at these 5 “Anti-Productivity” Scenarios, we will look at ways of dealing with them, and bringing your system back up to speed. Spyware Let’s start off with Spyware. Spyware is software installed without your knowledge. How does this software get installed without you knowing about it, you ask? Remember the old saying, “The best things in life are free.” Well, as it turns out, Software isn’t one of them. You see, just because it is free for you (financially speaking), the company is still making money on it. Yes, I know.. you have the free version, and there is a full version, which you can buy. But, even the free version is making the software company money. How you ask? Spyware. This is how it works. A Big Software Company, lets call them “ Company A ”, has a product that they want to put on the market, but they don’t want the user to have to pay for it. They still however, want to make money off it though. How, you ask? This is where the Little Software Company (“ Company B ”) comes into the picture. -
Fraudware How It Works and How to Prevent It from Attacking Your System a Fast Rhino Presentation to the Vistoso Computer Society November 11, 2012
Fraudware How it works and how to prevent it from attacking your system A Fast Rhino Presentation to the Vistoso Computer Society November 11, 2012 Before we jump in to Fraudware, we should most likely begin by defining "Malware ", which is short for "Malicious software". We've all heard a lot in the past about viruses, adware, & spyware. Today, the industry basically refers to just about any software-based threat as "Malware". More specifically, Malware is a term used to define software that is intended to disrupt the operation of a computer, collect sensitive data, or gain access to private computer systems. Its definition is always expanding since new exploits continue to evolve. Malware consists of a broad spectrum of techniques used to infect systems, including viruses, worms, Trojan horses, rootkits, backdoors and drive-by downloads. Each of these operate differently, however, attacks can very often include a combination of these methods. And, although many of you in this room may already be aware of these, some of you may not, so please bear with me as we go through a basic understanding of these. A virus is a program that infects executable software. When it runs, it allows the virus to spread to other executables. In the spring of 1999, a man named David L. Smith created a computer virus based on a Microsoft Word macro. He built the virus so that it could spread through e-mail messages. Smith named the virus "Melissa," saying that he named it after an exotic dancer from Florida. "Melissa" was one of the first major computer viruses to get the public's attention. -

The Most Common Blunder People Make When the Topic of a Computer Virus Arises Is to Refer to a Worm Or Trojan Horse As a Virus
Trojan And Email Forging 1) Introduction To Trojan&viruses: A Trojan horse, or Trojan, in computing is a generally non-self-replicating type of malware program containing malicious code that, when executed, carries out actions determined by the nature of the Trojan, typically causing loss or theft of data, and possible system harm. The term is derived from the story of the wooden horse used to trick defenders of Troy into taking concealed warriors into their city in ancient Anatolia, because computer Trojans often employ a form of social engineering, presenting themselves as routine, useful, or interesting in order to persuade victims to install them on their computers.[1][2][3][4][5] A Trojan often acts as a backdoor, contacting a controller which can then have unauthorized access to the affected computer.[6] While Trojans and backdoors are not easily detectable by themselves, computers may appear to run slower due to heavy processor or network usage. Malicious programs are classified as Trojans if they do not attempt to inject themselves into other files (computer virus) or otherwise propagate themselves (worm).[7] A computer may host a Trojan via a malicious program a user is duped into executing (often an e-mail attachment disguised to be unsuspicious, e.g., a routine form to be filled in) or by drive-by download. The Difference Between a Computer Virus, Worm and Trojan Horse The most common blunder people make when the topic of a computer virus arises is to refer to a worm or Trojan horse as a virus. One common mistake that people make when the topic of a computer virus arises is to refer to a worm or Trojan horse as a virus. -

Hostscan 4.8.01064 Antimalware and Firewall Support Charts
HostScan 4.8.01064 Antimalware and Firewall Support Charts 10/1/19 © 2019 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 76 Contents HostScan Version 4.8.01064 Antimalware and Firewall Support Charts ............................................................................... 3 Antimalware and Firewall Attributes Supported by HostScan .................................................................................................. 3 OPSWAT Version Information ................................................................................................................................................. 5 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.890.0 for Windows .................................................. 5 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.890.0 for Windows ........................................................ 44 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.824.0 for macos .................................................... 65 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.824.0 for macOS ........................................................... 71 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.730.0 for Linux ...................................................... 73 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.730.0 for Linux .............................................................. 76 ©201 9 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. -

Diapositiva 1
Feliciano Intini Responsabile dei programmi di Sicurezza e Privacy di Microsoft Italia • NonSoloSecurity Blog: http://blogs.technet.com/feliciano_intini • Twitter: http://twitter.com/felicianointini 1. Introduction - Microsoft Security Intelligence Report (SIR) 2. Today‘s Threats - SIR v.8 New Findings – Italy view 3. Advancements in Software Protection and Development 4. What the Users and Industry Can Do The 8th volume of the Security Intelligence Report contains data and intelligence from the past several years, but focuses on the second half of 2009 (2H09) Full document covers Malicious Software & Potentially Unwanted Software Email, Spam & Phishing Threats Focus sections on: Malware and signed code Threat combinations Malicious Web sites Software Vulnerability Exploits Browser-based exploits Office document exploits Drive-by download attacks Security and privacy breaches Software Vulnerability Disclosures Microsoft Security Bulletins Exploitability Index Usage trends for Windows Update and Microsoft Update Microsoft Malware Protection Center (MMPC) Microsoft Security Response Center (MSRC) Microsoft Security Engineering Center (MSEC) Guidance, advice and strategies Detailed strategies, mitigations and countermeasures Fully revised and updated Guidance on protecting networks, systems and people Microsoft IT ‗real world‘ experience How Microsoft IT secures Microsoft Malware patterns around the world with deep-dive content on 26 countries and regions Data sources Malicious Software and Potentially Unwanted Software MSRT has a user base -

Antivirus Software Before It Can Detect Them
Computer virus A computer virus is a computer program that can copy itself and infect a computer without the permission or knowledge of the owner. The term "virus" is also commonly but erroneously used to refer to other types of malware, adware, and spyware programs that do not have the reproductive ability. A true virus can only spread from one computer to another (in some form of executable code) when its host is taken to the target computer; for instance because a user sent it over a network or the Internet, or carried it on a removable medium such as a floppy disk, CD, DVD, or USB drive. Viruses can increase their chances of spreading to other computers by infecting files on a network file system or a file system that is accessed by another computer.[1][2] The term "computer virus" is sometimes used as a catch-all phrase to include all types of malware. Malware includes computer viruses, worms, trojan horses, most rootkits, spyware, dishonest adware, crimeware, and other malicious and unwanted software), including true viruses. Viruses are sometimes confused with computer worms and Trojan horses, which are technically different. A worm can exploit security vulnerabilities to spread itself to other computers without needing to be transferred as part of a host, and a Trojan horse is a program that appears harmless but has a hidden agenda. Worms and Trojans, like viruses, may cause harm to either a computer system's hosted data, functional performance, or networking throughput, when they are executed. Some viruses and other malware have symptoms noticeable to the computer user, but many are surreptitious. -

A Glance Into the Eye Pyramid Technical Article V2
A glance into the Eye Pyramid RĂZVAN OLTEANU Security Reasercher We keep you safe and we keep it simple. 01 Introduction On January 11, 2017 Italian news agency AGI, published a court order regarding cyber-attacks against high ranking Italian government members and Italian institutions. The attacks were conducted by two Italian brothers to get financial information that would help them gain an advantage when trading on financial markets. Overview The campaign was carried out over several years starting in 2008 and continuing into 2010, 2011, 2012 and 2014. The mechanism the brothers used to distribute their malware was simple; targeted spear-phishing emails aimed at victims who had already been selected. The emails con- tained a malware attachment, which once opened harvested information from the victims’ computers. This information consisted of pictures, documents, archives, presenta- tions, email contacts, email bodies, usernames, passwords, keystrokes, web pages content and databases. Technical details The malware was written in VisualBasic.net and was obfuscated twice using common obfuscators: Dotfuscator and Skater .NET which can be easily reversed. The malware stored its sensitive data – license keys, URLs and paths – by encrypting with the Triple DES algorithm using the MD5 of a provided password as key and SHA256 of the pass- word as initialization vector. A glance into the Eye Pyramid 01 02 Figure 1 Security applications To remain unnoticed, it tried to disable any security application installed on the victim’s computer. Targeted -
Linux Security Review 2015
Linux Security Review 2015 www.av-comparatives.org AV-Comparatives Linux Security Review Language: English May 2015 Last revision: 26 th May 2015 www.av-comparatives.org -1- Linux Security Review 2015 www.av-comparatives.org Contents Introduction ....................................................................................................................... 3 Reviewed products ............................................................................................................... 4 Malware for Linux systems ..................................................................................................... 5 Linux security advice ............................................................................................................ 6 Items covered in the review .................................................................................................. 7 Avast File Server Security ...................................................................................................... 8 AVG Free Edition for Linux.................................................................................................... 11 Bitdefender Antivirus Scanner for Unices ................................................................................ 13 Clam Antivirus for Linux ....................................................................................................... 17 Comodo Antivirus for Linux .................................................................................................. 20 Dr.Web Anti-virus for