Antivirus Software Before It Can Detect Them
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
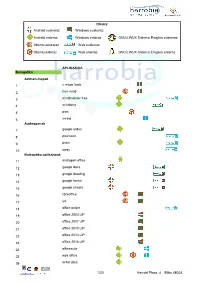
Android Euskaraz Windows Euskaraz Android Erderaz Windows Erderaz GNU/LINUX Sistema Eragilea Euskeraz Ubuntu Euskaraz We
Oharra: Android euskaraz Windows euskaraz Android erderaz Windows erderaz GNU/LINUX Sistema Eragilea euskeraz Ubuntu euskaraz Web euskaraz Ubuntu erderaz Web erderaz GNU/LINUX Sistema Eragilea erderaz APLIKAZIOA Bulegotika Adimen-mapak 1 c maps tools 2 free mind 3 mindmeister free 4 mindomo 5 plan 6 xmind Aurkezpenak 7 google slides 8 pow toon 9 prezi 10 sway Bulegotika-aplikazioak 11 andropen office 12 google docs 13 google drawing 14 google forms 15 google sheets 16 libreoffice 17 lyx 18 office online 19 office 2003 LIP 20 office 2007 LIP 21 office 2010 LIP 22 office 2013 LIP 23 office 2016 LIP 24 officesuite 25 wps office 26 writer plus 1/20 Harrobi Plaza, 4 Bilbo 48003 CAD 27 draftsight 28 librecad 29 qcad 30 sweet home 31 timkercad Datu-baseak 32 appserv 33 dbdesigner 34 emma 35 firebird 36 grubba 37 kexi 38 mysql server 39 mysql workbench 40 postgresql 41 tora Diagramak 42 dia 43 smartdraw Galdetegiak 44 kahoot Maketazioa 45 scribus PDF editoreak 46 master pdf editor 47 pdfedit pdf escape 48 xournal PDF irakurgailuak 49 adobe reader 50 evince 51 foxit reader 52 sumatraPDF 2/20 Harrobi Plaza, 4 Bilbo 48003 Hezkuntza Aditzak lantzeko 53 aditzariketak.wordpress 54 aditz laguntzailea 55 aditzak 56 aditzak.com 57 aditzapp 58 adizkitegia 59 deklinabidea 60 euskaljakintza 61 euskera! 62 hitano 63 ikusi eta ikasi 64 ikusi eta ikasi bi! Apunteak partekatu 65 flashcard machine 66 goconqr 67 quizlet 68 rincon del vago Diktaketak 69 dictation Entziklopediak 70 auñamendi eusko entziklopedia 71 elhuyar zth hiztegi entziklopedikoa 72 harluxet 73 lur entziklopedia tematikoa 74 lur hiztegi entziklopedikoa 75 wikipedia Esamoldeak 76 AEK euskara praktikoa 77 esamoldeapp 78 Ikapp-zaharrak berri Estatistikak 79 pspp 80 r 3/20 Harrobi Plaza, 4 Bilbo 48003 Euskara azterketak 81 ega app 82 egabai 83 euskal jakintza 84 euskara ikasiz 1. -

Checks to Avoid Malware Protect Your Laptop with Security Essentials
What is Malware? Malware is software that can infect you computer and can be a virus or malicious software that can harm & slow your system or try to steal your personal information. To help avoid malware follow the check list below. Checks to avoid Malware Check you have updated Antivirus software installed such as Microsoft Security Essentials Install and run an Anti-Malware program such as Malwarebytes Uninstall any Peer 2 Peer software such as Limewire or Vuze Be careful with email attachments and never respond to mails asking for your password Protect your Laptop with Security Essentials Microsoft Security Essentials is a free antivirus software product for Windows Vista, 7 & 8. It pro- vides protection against different types of malware such as computer virus, spyware, rootkits, trojans & other malicious software. Download & install Security Essentials from the following link http:// www.microsoft.com/security_essentials/ Clear Infections using Malwarebytes Malware bytes is free to download & install from http://www.malwarebytes.org Once installed it is recommended that you run a Full Scan of your laptop to check for any malware that may reside on the system. Once complete, follow the on screen instructions to finish removing any threats found. You should regularly run updates and scans to ensure your system remains clean. It is also advisable to scan external storage devices such as USB keys as they can spread infections. If the above criteria are fully met, ISS staff at the service desk on the ground floor of the library are happy to investigate problems on your laptop For more information go to http://www.dcu.ie/iss ISS online service desk: https://https://iss.servicedesk.dcu.ie Follow ISS on Twitter @ISSservice . -

Spamalytics: an Empirical Analysis of Spam Marketing Conversion
Spamalytics: An Empirical Analysis of Spam Marketing Conversion Chris Kanich∗ Christian Kreibich† Kirill Levchenko∗ Brandon Enright∗ Geoffrey M. Voelker∗ Vern Paxson† Stefan Savage∗ † ∗ International Computer Science Institute Dept. of Computer Science and Engineering Berkeley, USA University of California, San Diego, USA [email protected],[email protected] {ckanich,klevchen,voelker,savage}@cs.ucsd.edu [email protected] ABSTRACT Unraveling such questions is essential for understanding the eco- The “conversion rate” of spam — the probability that an unso- nomic support for spam and hence where any structural weaknesses licited e-mail will ultimately elicit a “sale” — underlies the entire may lie. Unfortunately, spammers do not file quarterly financial spam value proposition. However, our understanding of this critical reports, and the underground nature of their activities makes third- behavior is quite limited, and the literature lacks any quantitative party data gathering a challenge at best. Absent an empirical foun- study concerning its true value. In this paper we present a method- dation, defenders are often left to speculate as to how successful ology for measuring the conversion rate of spam. Using a parasitic spam campaigns are and to what degree they are profitable. For ex- infiltration of an existing botnet’s infrastructure, we analyze two ample, IBM’s Joshua Corman was widely quoted as claiming that spam campaigns: one designed to propagate a malware Trojan, the spam sent by the Storm worm alone was generating “millions and other marketing on-line pharmaceuticals. For nearly a half billion millions of dollars every day” [2]. While this claim could in fact be spam e-mails we identify the number that are successfully deliv- true, we are unaware of any public data or methodology capable of ered, the number that pass through popular anti-spam filters, the confirming or refuting it. -

Hostscan 4.8.01064 Antimalware and Firewall Support Charts
HostScan 4.8.01064 Antimalware and Firewall Support Charts 10/1/19 © 2019 Cisco and/or its affiliates. All rights reserved. This document is Cisco public. Page 1 of 76 Contents HostScan Version 4.8.01064 Antimalware and Firewall Support Charts ............................................................................... 3 Antimalware and Firewall Attributes Supported by HostScan .................................................................................................. 3 OPSWAT Version Information ................................................................................................................................................. 5 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.890.0 for Windows .................................................. 5 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.890.0 for Windows ........................................................ 44 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.824.0 for macos .................................................... 65 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.824.0 for macOS ........................................................... 71 Cisco AnyConnect HostScan Antimalware Compliance Module v4.3.730.0 for Linux ...................................................... 73 Cisco AnyConnect HostScan Firewall Compliance Module v4.3.730.0 for Linux .............................................................. 76 ©201 9 Cisco and/or its affiliates. All rights reserved. This document is Cisco Public. -

Address Munging: the Practice of Disguising, Or Munging, an E-Mail Address to Prevent It Being Automatically Collected and Used
Address Munging: the practice of disguising, or munging, an e-mail address to prevent it being automatically collected and used as a target for people and organizations that send unsolicited bulk e-mail address. Adware: or advertising-supported software is any software package which automatically plays, displays, or downloads advertising material to a computer after the software is installed on it or while the application is being used. Some types of adware are also spyware and can be classified as privacy-invasive software. Adware is software designed to force pre-chosen ads to display on your system. Some adware is designed to be malicious and will pop up ads with such speed and frequency that they seem to be taking over everything, slowing down your system and tying up all of your system resources. When adware is coupled with spyware, it can be a frustrating ride, to say the least. Backdoor: in a computer system (or cryptosystem or algorithm) is a method of bypassing normal authentication, securing remote access to a computer, obtaining access to plaintext, and so on, while attempting to remain undetected. The backdoor may take the form of an installed program (e.g., Back Orifice), or could be a modification to an existing program or hardware device. A back door is a point of entry that circumvents normal security and can be used by a cracker to access a network or computer system. Usually back doors are created by system developers as shortcuts to speed access through security during the development stage and then are overlooked and never properly removed during final implementation. -

Key Benefits Core Technologies and Technical Features
Advanced threat prevention Malwarebytes Endpoint Security is an innovative platform that delivers powerful multi- layered defense for smart endpoint protection. Malwarebytes Endpoint Security enables small and large enterprise businesses to thoroughly protect against the latest malware and advanced threats—including stopping known and unknown exploit attacks. Key Benefits Blocks zero-hour malware Easy management Reduces the chances of data exfiltration and saves Simplifies endpoint security management and identifies on IT resources by protecting against zero-hour vulnerable endpoints. Streamlines endpoint security malware that traditional security solutions can miss. deployment and maximizes IT management resources. Saves legacy systems Scalable threat prevention Protects unsupported programs by armoring Deploys protection for every endpoint and scales as vulnerabilities against exploits. your company grows. Increases productivity Detects unprotected systems Maintains end-user productivity by preserving Discovers all endpoints and installed software on your system performance and keeping staff on revenue- network. Systems without Malwarebytes that are positive projects. vulnerable to cyber attacks can be easily secured. Core Technologies and Technical Features Anti-Malware Proactive anti-malware/anti-spyware scanning Three system scan modes (Quick, Flash, Full) engine Enables selection of the most efficient system scan Detects and eliminates zero-hour and known based on endpoint security requirements and available viruses, Trojans, worms, rootkits, adware, and system resources. spyware in real time to ensure data security and network integrity. Extends its protection to Windows Server operating systems. | Santa Clara, CA | malwarebytes.com | [email protected] | 1.800.520.2796 Advanced threat prevention Malicious website blocking Advanced malware remediation Prevents access to known malicious IP addresses Employs delete-on-reboot to remove persistent or so that end users are proactively protected from deeply embedded malware. -

Nama:Dennis Kelas;X-1 No:7
Nama:dennis Kelas;X-1 No:7 Virus komputer merupakan program komputer yang dapat menggandakan atau menyalin dirinya sendiri dan menyebar dengan cara menyisipkan salinan dirinya ke dalam program atau dokumen lain. Virus komputer dapat dianalogikan dengan virus biologis yang menyebar dengan cara menyisipkan dirinya sendiri ke sel makhluk hidup. Virus komputer dapat merusak (misalnya dengan merusak data pada dokumen), membuat pengguna komputer merasa terganggu, maupun tidak menimbulkan efek sama sekali. Virus komputer umumnya dapat merusak perangkat lunak komputer dan tidak dapat secara langsung merusak perangkat keras komputer dengan cara memuat program yang memaksa over process ke perangkat tertentu misalnya VGA, Memory bahkan Procesor (terutama pada sistem operasi , seperti sistem operasi berbasis keluarga Windows (Windows 95, Windows 98/98SE, Windows NT, Windows NT Server, Windows 2000, Windows 2000 Server, Windows 2003, Windows 2003 Server, Windows XP Home Edition, Windows XP Professional, Windows XP Service Pack 1, Windows XP Service Pack 2, Windows Vista Service Pack 1 ) bahkan GNU/Linux. Efek negatif virus komputer terutama adalah memperbanyak dirinya sendiri, yang membuat sumber daya pada komputer (seperti CPU Real Time, penggunaan memori) menjadi berkurang secara signifikan. Hampir 95% Virus adalah virus komputer berbasis sistem operasi Windows. Sisanya, 2% menyerang Linux/GNU dengan versi kernel dibawah 1.4 (dan Unix, sebagai source dari Linux, tentunya), 1% menyerang Mac terutama Mac OS 9, Mac OS X (Tiger, Leopard). 2% lagi menyerang sistim operasi lain seperti FreeBSD, OS/2 IBM, dan Sun Operating System. Cara Mengatasi Virus Komputer Serangan virus dapat dicegah atau ditanggulangi dengan menggunakan perangkat lunak antivirus. Jenis perangkat lunak ini dapat juga mendeteksi dan menghapus virus komputer, asalkan basis data virus komputer yang dimiliki oleh perangkat lunak antivirus telah mengandung kode untuk menghapus virus tersebut. -
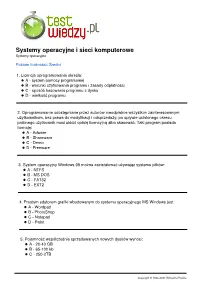
Systemy Operacyjne I Sieci Komputerowe Systemy Operacyjne
Systemy operacyjne i sieci komputerowe Systemy operacyjne Poziom trudności: Średni 1. Licencja oprogramowania określa: A - system pomocy programowej B - warunki użytkowania programu i zasady odpłatności C - sposób kasowania programu z dysku D - wielkość programu 2. Oprogramowanie udostępniane przez autorów nieodpłatnie wszystkim zainteresowanym użytkownikom, bez prawa do modyfikacji i odsprzedaży; po upływie ustalonego okresu próbnego użytkownik musi uiścić opłatę licencyjną albo skasować. Taki program posiada licencję: A - Adware B - Shareware C - Demo D - Freeware 3. System operacyjny Windows 98 można zainstalować używając systemu plików: A - NTFS B - MS DOS C - FAT32 D - EXT2 4. Prostym edytorem grafiki wbudowanym do systemu operacyjnego MS Windows jest: A - Wordpad B - PhotoShop C - Notepad D - Paint 5. Pojemność współcześnie sprzedawanych nowych dysków wynosi: A - 20-40 GB B - 65-100 kb C - 250-2TB Copyright © 1995-2021 Wirtualna Polska D - 512 MB 6. Konfiguracja sprzętowa systemu przechowywana jest w kluczu rejestru: A - HKEY_CLASSES_ROOT B - HKEY_LOCAL_MACHINE C - HKEY_CURRENT_CONFIG D - HKEY_USERS 7. W którym roku Microsoft wydał pierwszy system Windows? A - 1986 B - 1982 C - 1985 D - 1993 8. Jak brzmi angielski skrót od nazwy system operacyjny? A - OS B - DOS C - SO D - BIOS 9. Do programów antywirusowych nie należy: A - FDISK B - NOD32 C - Kaspersky D - MKS VIR 10. Poniżej podano cechy systemu NTFS, wskaż zdanie nieprawdziwe: A - możliwość przydziału uprawnień do plików i folderów użytkownikom i grupom B - brak dostępu do woluminów NTFS z poziomu systemów MS-DOS, Windows 95 i C - możliwość ograniczania ilości przestrzeni dyskowej wykorzystywanej przez użytkowników D - brak możliwości wykonania kopii systemu Copyright © 1995-2021 Wirtualna Polska 11. Którym poleceniem z linii poleceń sprawdzisz atrybuty plików? A - dir B - cd C - atrrib D - atribb 12. -

Q3 Consumer Endpoint Protection Jul-Sep 2020
HOME ANTI- MALWARE PROTECTION JUL - SEP 2020 selabs.uk [email protected] @SELabsUK www.facebook.com/selabsuk blog.selabs.uk SE Labs tested a variety of anti-malware (aka ‘anti-virus’; aka ‘endpoint security’) products from a range of well-known vendors in an effort to judge which were the most effective. Each product was exposed to the same threats, which were a mixture of targeted attacks using well-established techniques and public email and web-based threats that were found to be live on the internet at the time of the test. The results indicate how effectively the products were at detecting and/or protecting against those threats in real time. 2 Home Anti-Malware Protection July - September 2020 MANAGEMENT Chief Executive Officer Simon Edwards CONTENTS Chief Operations Officer Marc Briggs Chief Human Resources Officer Magdalena Jurenko Chief Technical Officer Stefan Dumitrascu Introduction 04 TEstING TEAM Executive Summary 05 Nikki Albesa Zaynab Bawa 1. Total Accuracy Ratings 06 Thomas Bean Solandra Brewster Home Anti-Malware Protection Awards 07 Liam Fisher Gia Gorbold Joseph Pike 2. Threat Responses 08 Dave Togneri Jake Warren 3. Protection Ratings 10 Stephen Withey 4. Protection Scores 12 IT SUPPORT Danny King-Smith 5. Protection Details 13 Chris Short 6. Legitimate Software Ratings 14 PUBLICatION Sara Claridge 6.1 Interaction Ratings 15 Colin Mackleworth 6.2 Prevalence Ratings 16 Website selabs.uk Twitter @SELabsUK 6.3 Accuracy Ratings 16 Email [email protected] Facebook www.facebook.com/selabsuk 6.4 Distribution of Impact Categories 17 Blog blog.selabs.uk Phone +44 (0)203 875 5000 7. -
Linux Security Review 2015
Linux Security Review 2015 www.av-comparatives.org AV-Comparatives Linux Security Review Language: English May 2015 Last revision: 26 th May 2015 www.av-comparatives.org -1- Linux Security Review 2015 www.av-comparatives.org Contents Introduction ....................................................................................................................... 3 Reviewed products ............................................................................................................... 4 Malware for Linux systems ..................................................................................................... 5 Linux security advice ............................................................................................................ 6 Items covered in the review .................................................................................................. 7 Avast File Server Security ...................................................................................................... 8 AVG Free Edition for Linux.................................................................................................... 11 Bitdefender Antivirus Scanner for Unices ................................................................................ 13 Clam Antivirus for Linux ....................................................................................................... 17 Comodo Antivirus for Linux .................................................................................................. 20 Dr.Web Anti-virus for -

Who Wrote Sobig? Copyright 2003-2004 Authors Page 1 of 48
Who Wrote Sobig? Copyright 2003-2004 Authors Page 1 of 48 Who Wrote Sobig? Version 1.0: 19-August-2003. Version 1.1: 25-August-2003. Version 1.2: 19-November-2003. Version 1.3: 17-July-2004. This sanitized variation for public release. Scheduled for release: 1-November-2004. This document is Copyright 2003-2004 by the authors. The PGP key included within this document identifies the authors. Who Wrote Sobig? Copyright 2003-2004 Authors Page 2 of 48 Table of Contents Table of Contents................................................................................................................................................... 2 1 About This Document..................................................................................................................................... 3 2 Overview........................................................................................................................................................ 5 3 Spam and Virus Release History..................................................................................................................... 6 3.1 Identifying Tools .................................................................................................................................... 6 3.2 Identifying Individuals and Specific Groups ............................................................................................ 6 3.3 Identifying Open Proxies and Usage........................................................................................................ 8 3.4 -

Technical Report RHUL–ISG–2021–3 10 March 2021
Testing Antivirus in Linux: An Investigation on the Effectiveness of Solutions Available for Desktop Computers Giuseppe Raffa Technical Report RHUL–ISG–2021–3 10 March 2021 Information Security Group Royal Holloway University of London Egham, Surrey, TW20 0EX United Kingdom Student Number: 100907703 Giuseppe Raffa Testing Antivirus in Linux: An Investigation on the Effectiveness of Solutions Available for Desktop Computers Supervisor: Daniele Sgandurra Submitted as part of the requirements for the award of the MSc in Information Security at Royal Holloway, University of London. I declare that this assignment is all my own work and that I have acknowledged all quotations from published or unpublished work of other people. I also declare that I have read the statements on plagiarism in Section 1 of the Regulations Governing Examination and Assessment Offences, and in accordance with these regulations I submit this project report as my own work. Signature: Giuseppe Raffa Date: 24th August 2020 Table of Contents 1 Introduction.....................................................................................................................7 1.1 Motivation.......................................................................................................................................7 1.2 Objectives........................................................................................................................................8 1.3 Methodology...................................................................................................................................8