V850 Series Development Environment Pamphlet
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Fill Your Boots: Enhanced Embedded Bootloader Exploits Via Fault Injection and Binary Analysis
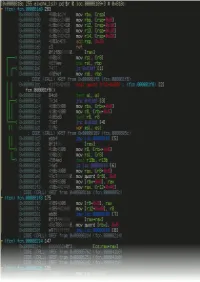
IACR Transactions on Cryptographic Hardware and Embedded Systems ISSN 2569-2925, Vol. 2021, No. 1, pp. 56–81. DOI:10.46586/tches.v2021.i1.56-81 Fill your Boots: Enhanced Embedded Bootloader Exploits via Fault Injection and Binary Analysis Jan Van den Herrewegen1, David Oswald1, Flavio D. Garcia1 and Qais Temeiza2 1 School of Computer Science, University of Birmingham, UK, {jxv572,d.f.oswald,f.garcia}@cs.bham.ac.uk 2 Independent Researcher, [email protected] Abstract. The bootloader of an embedded microcontroller is responsible for guarding the device’s internal (flash) memory, enforcing read/write protection mechanisms. Fault injection techniques such as voltage or clock glitching have been proven successful in bypassing such protection for specific microcontrollers, but this often requires expensive equipment and/or exhaustive search of the fault parameters. When multiple glitches are required (e.g., when countermeasures are in place) this search becomes of exponential complexity and thus infeasible. Another challenge which makes embedded bootloaders notoriously hard to analyse is their lack of debugging capabilities. This paper proposes a grey-box approach that leverages binary analysis and advanced software exploitation techniques combined with voltage glitching to develop a powerful attack methodology against embedded bootloaders. We showcase our techniques with three real-world microcontrollers as case studies: 1) we combine static and on-chip dynamic analysis to enable a Return-Oriented Programming exploit on the bootloader of the NXP LPC microcontrollers; 2) we leverage on-chip dynamic analysis on the bootloader of the popular STM8 microcontrollers to constrain the glitch parameter search, achieving the first fully-documented multi-glitch attack on a real-world target; 3) we apply symbolic execution to precisely aim voltage glitches at target instructions based on the execution path in the bootloader of the Renesas 78K0 automotive microcontroller. -
Radare2 Book
Table of Contents introduction 1.1 Introduction 1.2 History 1.2.1 Overview 1.2.2 Getting radare2 1.2.3 Compilation and Portability 1.2.4 Compilation on Windows 1.2.5 Command-line Flags 1.2.6 Basic Usage 1.2.7 Command Format 1.2.8 Expressions 1.2.9 Rax2 1.2.10 Basic Debugger Session 1.2.11 Contributing to radare2 1.2.12 Configuration 1.3 Colors 1.3.1 Common Configuration Variables 1.3.2 Basic Commands 1.4 Seeking 1.4.1 Block Size 1.4.2 Sections 1.4.3 Mapping Files 1.4.4 Print Modes 1.4.5 Flags 1.4.6 Write 1.4.7 Zoom 1.4.8 Yank/Paste 1.4.9 Comparing Bytes 1.4.10 Visual mode 1.5 Visual Disassembly 1.5.1 2 Searching bytes 1.6 Basic Searches 1.6.1 Configurating the Search 1.6.2 Pattern Search 1.6.3 Automation 1.6.4 Backward Search 1.6.5 Search in Assembly 1.6.6 Searching for AES Keys 1.6.7 Disassembling 1.7 Adding Metadata 1.7.1 ESIL 1.7.2 Scripting 1.8 Loops 1.8.1 Macros 1.8.2 R2pipe 1.8.3 Rabin2 1.9 File Identification 1.9.1 Entrypoint 1.9.2 Imports 1.9.3 Symbols (exports) 1.9.4 Libraries 1.9.5 Strings 1.9.6 Program Sections 1.9.7 Radiff2 1.10 Binary Diffing 1.10.1 Rasm2 1.11 Assemble 1.11.1 Disassemble 1.11.2 Ragg2 1.12 Analysis 1.13 Code Analysis 1.13.1 Rahash2 1.14 Rahash Tool 1.14.1 Debugger 1.15 3 Getting Started 1.15.1 Registers 1.15.2 Remote Access Capabilities 1.16 Remoting Capabilities 1.16.1 Plugins 1.17 Plugins 1.17.1 Crackmes 1.18 IOLI 1.18.1 IOLI 0x00 1.18.1.1 IOLI 0x01 1.18.1.2 Avatao 1.18.2 R3v3rs3 4 1.18.2.1 .intro 1.18.2.1.1 .radare2 1.18.2.1.2 .first_steps 1.18.2.1.3 .main 1.18.2.1.4 .vmloop 1.18.2.1.5 .instructionset 1.18.2.1.6 -

SPARC/IOBP-CPU-56 Installation Guide
SPARC/IOBP-CPU-56 Installation Guide P/N 220226 Revision AB September 2003 Copyright The information in this publication is subject to change without notice. Force Computers, GmbH reserves the right to make changes without notice to this, or any of its products, to improve reliability, performance, or design. Force Computers, GmbH shall not be liable for technical or editorial errors or omissions contained herein, nor for indirect, special, incidental, or consequential damages resulting from the furnishing, performance, or use of this material. This information is provided "as is" and Force Computers, GmbH expressly disclaims any and all warranties, express, implied, statutory, or otherwise, including without limitation, any express, statutory, or implied warranty of merchantability, fitness for a particular purpose, or non−infringement. This publication contains information protected by copyright. This publication shall not be reproduced, transmitted, or stored in a retrieval system, nor its contents used for any purpose, without the prior written consent of Force Computers, GmbH. Force Computers, GmbH assumes no responsibility for the use of any circuitry other than circuitry that is part of a product of Force Computers, GmbH. Force Computers, GmbH does not convey to the purchaser of the product described herein any license under the patent rights of Force Computers, GmbH nor the rights of others. CopyrightE 2003 by Force Computers, GmbH. All rights reserved. The Force logo is a trademark of Force Computers, GmbH. IEEER is a registered trademark of the Institute for Electrical and Electronics Engineers, Inc. PICMGR, CompactPCIR, and the CompactPCI logo are registered trademarks and the PICMG logo is a trademark of the PCI Industrial Computer Manufacturer’s Group. -

Sistemi Operativi Real-Time Marco Cesati Lezione R13 Sistemi Operativi Real-Time – II Schema Della Lezione
Sistemi operativi real-time Marco Cesati Lezione R13 Sistemi operativi real-time – II Schema della lezione Caratteristiche comuni VxWorks LynxOS Sistemi embedded e real-time QNX eCos Windows Linux come RTOS 15 gennaio 2013 Marco Cesati Dipartimento di Ingegneria Civile e Ingegneria Informatica Università degli Studi di Roma Tor Vergata SERT’13 R13.1 Sistemi operativi Di cosa parliamo in questa lezione? real-time Marco Cesati In questa lezione descriviamo brevemente alcuni dei più diffusi sistemi operativi real-time Schema della lezione Caratteristiche comuni VxWorks LynxOS 1 Caratteristiche comuni degli RTOS QNX 2 VxWorks eCos 3 LynxOS Windows Linux come RTOS 4 QNX Neutrino 5 eCos 6 Windows Embedded CE 7 Linux come RTOS SERT’13 R13.2 Sistemi operativi Caratteristiche comuni dei principali RTOS real-time Marco Cesati Corrispondenza agli standard: generalmente le API sono proprietarie, ma gli RTOS offrono anche compatibilità (compliancy) o conformità (conformancy) allo standard Real-Time POSIX Modularità e Scalabilità: il kernel ha una dimensione Schema della lezione Caratteristiche comuni (footprint) ridotta e le sue funzionalità sono configurabili VxWorks Dimensione del codice: spesso basati su microkernel LynxOS QNX Velocità e Efficienza: basso overhead per cambi di eCos contesto, latenza delle interruzioni e primitive di Windows sincronizzazione Linux come RTOS Porzioni di codice non interrompibile: generalmente molto corte e di durata predicibile Gestione delle interruzioni “separata”: interrupt handler corto e predicibile, ISR lunga -

Μitron 4.0 Specification (Ver. 4.03.00) TEF024-S001-04.03.00/En July 2010 Copyright © 2010 by T-Engine Forum
μITRON 4.0 Specification Ver. 4.03.00 TEF024-S001-04.03.00/en July 2010 μITRON 4.0 Specification (Ver. 4.03.00) TEF024-S001-04.03.00/en July 2010 Copyright © 2010 by T-Engine Forum. This “μITRON 4.0 Specification (Ver. 4.03.00)” was originally released by TRON ASSOCIATION which has been integrated into T-Engine Forum since January 2010. The same specification now has been released by T-Engine Forum as its own specification without modification of the content after going through the IPR procedures. T-Engine Forum owns the copyright of this specification. Permission of T-Engine Forum is necessary for copying, republishing, posting on servers, or redistribution to lists of the contents of this specification. The contents written in this specification may be changed without a prior notice for improvement or other reasons in the future. About this specification, please refer to follows; Publisher T-Engine Forum The 28th Kowa Building 2-20-1 Nishi-gotanda Shinagawa-Ward Tokyo 141-0031 Japan TEL:+81-3-5437-0572 FAX:+81-3-5437-2399 E-mail:[email protected] TEF024-S001-04.03.00/en µITRON4.0 Specification Ver. 4.03.00 Supervised by Ken Sakamura Edited and Published by TRON ASSOCIATION µITRON4.0 Specification (Ver. 4.03.00) The copyright of this specification document belongs to TRON Association. TRON Association grants the permission to copy the whole or a part of this specification document and to redistribute it intact without charge or at cost. However, when a part of this specification document is redistributed, it must clearly state (1) that it is a part of the µITRON4.0 Specification document, (2) which part was taken, and (3) the method to obtain the whole specification document. -

Reverse Software Engineering As a Project-Based Learning Tool
Paper ID #33764 Reverse Software Engineering as a Project-Based Learning Tool Ms. Cynthia C. Fry, Baylor University CYNTHIA C. FRY is currently a Senior Lecturer of Computer Science at Baylor University. She worked at NASA’s Marshall Space Flight Center as a Senior Project Engineer, a Crew Training Manager, and the Science Operations Director for STS-46. She was an Engineering Duty Officer in the U.S. Navy (IRR), and worked with the Naval Maritime Intelligence Center as a Scientific/Technical Intelligence Analyst. She was the owner and chief systems engineer for Systems Engineering Services (SES), a computer systems design, development, and consultation firm. She joined the faculty of the School of Engineering and Computer Science at Baylor University in 1997, where she teaches a variety of engineering and computer science classes, she is the Faculty Advisor for the Women in Computer Science (WiCS), the Director of the Computer Science Fellows program, and is a KEEN Fellow. She has authored and co- authored over fifty peer-reviewed papers. Mr. Zachary Michael Steudel Zachary Steudel is a 2021 graduate of Baylor University’s computer science department. In his time at Baylor, he worked as a Teaching Assistant under Ms. Cynthia C. Fry. As part of the Teaching Assistant role, Zachary designed and created the group project for the Computer Systems course. Zachary Steudel worked as a Software Developer Intern at Amazon in the Summer of 2019, a Software Engineer Intern at Microsoft in the Summer of 2020, and begins his full-time career with Amazon in the summer of 2021 as a software engineer. -

Reassembleable Disassembling
Reassembleable Disassembling Shuai Wang, Pei Wang, and Dinghao Wu College of Information Sciences and Technology The Pennsylvania State University fszw175, pxw172, [email protected] Abstract struction level to enforce certain security policies. To ensure program control-flow integrity (CFI, meaning that Reverse engineering has many important applications in program execution is dictated to a predetermined control- computer security, one of which is retrofitting software flow graph) [1,4, 43, 17, 29, 37] without source code, the for safety and security hardening when source code is not original control-flow graph must be recovered from a bi- available. By surveying available commercial and aca- nary executable and the binary must be retrofitted with demic reverse engineering tools, we surprisingly found the CFI enforcement facility embedded [50, 49]. Sym- that no existing tool is able to disassemble executable bolic taint analysis [34] on binaries must recover assem- binaries into assembly code that can be correctly assem- bly code and data faithfully. The defending techniques bled back in a fully automated manner, even for simple against return-oriented programming (ROP) attacks also programs. Actually in many cases, the resulted disas- rely on binary analysis and reconstruction to identify and sembled code is far from a state that an assembler ac- eliminate ROP gadgets [44,9, 47, 22, 39]. cepts, which is hard to fix even by manual effort. This Despite the fact that many security hardening tech- has become a severe obstacle. People have tried to over- niques are highly dependent on reverse engineering, flex- come it by patching or duplicating new code sections for ible and easy-to-use binary manipulation itself remains retrofitting of executables, which is not only inefficient an unsolved problem. -

A Survey of Reverse Engineering Tools for the 32-Bit Microsoft Windows Environment
A Survey of Reverse Engineering Tools for the 32-Bit Microsoft Windows Environment RAYMOND J. CANZANESE, JR., MATTHEW OYER, SPIROS MANCORIDIS, and MOSHE KAM College of Engineering Drexel University, Philadelphia, PA, USA Reverse engineering is defined by Chikosfky and Cross as the process of analyzing a subject system to identify the system's components and their relationships, and to create representations of the system in another form or at a higher level of abstraction. The process of reverse engineering is accomplished using specific tools that, for the 32-bit Microsoft Windows environment, are categorized as hex editors, disassemblers/debuggers, decompilers, or related technologies such as code obfuscators, unpackers, and PE editors. An evaluation of each tool is provided that identifies its domain of applicability and usability. Categories and Subject Descriptors: A.1 [General]: Introductory and Survey; D.2.5 [Software Engineering]: Testing and Debugging General Terms: Security, Documentation Additional Key Words and Phrases: Reverse Engineering, Disassemblers, Debuggers, Decompilers, Code Obfuscators, PE Editors Unpackers, Hex Editors 1. INTRODUCTION 1.1 The Reverse Engineering Process Software engineers are sometimes asked to understand the behavior of a program given that program's binary executable file. If they have access to the appropriate reverse engineering tools, they might choose to adhere to the following process. First, a general disassembler/debugger is used to determine the basic functionality of the program. If disassembly and debugging shows that the binary code has been obfuscated, the next step would be to determine whether the obfuscator used is a common commercial obfuscator or a custom protection scheme. A PE editor would be used to make this determination. -

Implementing the UCSD PASCAL System on the MODCOMP Computer
TDA Progress Report 42-60 September and October 1960 Implementing the UCSD PASCAL System on the MODCOMP Computer T. Wolfe DSN Data Systems Section This article describes the UCSD PASCAL system developed by the University of California, San Diego, now available on the MODCOMP computer. The system includes a Pascal compiler and many useful utility programs. A BASIC compiler and a FORTRAN 77 compiler are also avatkble. There is currently a large amount of software availabie written in UCSD PASCAL, including a data base system, word processing systems and a MODULA compiler. I. Introduction Assembly language subroutines thus produced may also be called from either Pascal or FORTRAN. Currently the assem- The UCSD PASCAL* System is a complete interactive bler has not been modified to produce MODCOMP machine software development system consisting of an operating sys- code. A system library program may be used to build libraries tem, compilers (Pascal, BASIC, FORTRAN 77) two text of useful subroutines and the system linker used to link them editors (screen editor and line-oriented editor), a linker and to user programs. many useful utility programs. The system is written and main- tained in Pascal. The compiler generates code for an idealized processor known as the “pseudo-machine.” The “pseudo- Interpreters currently exist for Z80/8080, PDP 11 /LSI-1 1, code” (p-code) generated by the compiler is interpreted at 6800, 9900 and 6502 computers and are being developed for runtime by a program (known as the interpreter) which emu- other computers. Thus, software could be developed on an lates the pseudo-machine. -

LSU EE 4720 Homework 1 Solution Due: 3 March 2006
LSU EE 4720 Homework 1 Solution Due: 3 March 2006 Several Web links appear below and at least one is long, to avoid the tedium of typing them view the assignment in Adobe reader and click. Problem 1: Consider these add instructions in three common ISAs. (Use the ISA manuals linked to the references page, http://www.ece.lsu.edu/ee4720/reference.html.) # MIPS64 addu r1, r2, r3 # SPARC V9 add g2, g3, g1 # PA RISC 2 add r1, r2, r3 (a) Show the encoding (binary form) for each instruction. Show the value of as many bits as possible. Codings shown below. For PA-RISC the ea, ec, and ed ¯elds are labeled e1, e2, and e3, respectively in the instruction descriptions. There is no label for the eb ¯eld in the instruction description of the add and yes it would make sense to use e0 instead of e1 but they didn't for whatever reason. opcode rs rt rd sa func MIPS64: 0 2 3 1 0 0x21 31 26 25 21 20 16 15 11 10 6 5 0 op rd op3 rs1 i asi rs2 SPARC V9: 2 1 0 2 0 0 3 31 30 29 25 24 19 18 14 13 13 12 5 4 0 OPCD r2 r1 c f ea eb ec ed d t PA-RISC 2: 2 3 2 0 0 01 1 0 00 0 1 0 5 6 10 11 15 16 18 19 19 20 21 22 22 23 23 24 25 26 26 27 31 (b) Identify the ¯eld or ¯elds in the SPARC add instruction which are the closest equivalent to MIPS' func ¯eld. -

Ross Technology RT6224K User Manual 1 (Pdf)
Full-service, independent repair center -~ ARTISAN® with experienced engineers and technicians on staff. TECHNOLOGY GROUP ~I We buy your excess, underutilized, and idle equipment along with credit for buybacks and trade-ins. Custom engineering Your definitive source so your equipment works exactly as you specify. for quality pre-owned • Critical and expedited services • Leasing / Rentals/ Demos equipment. • In stock/ Ready-to-ship • !TAR-certified secure asset solutions Expert team I Trust guarantee I 100% satisfaction Artisan Technology Group (217) 352-9330 | [email protected] | artisantg.com All trademarks, brand names, and brands appearing herein are the property o f their respective owners. Find the Ross Technology RT6224K-200/512S at our website: Click HERE 830-0016-03 Rev A 11/15/96 PRELIMINARY Colorado 4 RT6224K hyperSPARC CPU Module Features D Based on ROSS’ fifth-generation D SPARC compliant — Zero-wait-state, 512-Kbyte or hyperSPARC processor — SPARC Instruction Set Architec- 1-Mbyte 2nd-level cache — RT620D Central Processing Unit ture (ISA) Version 8 compliant — Demand-paged virtual memory (CPU) — Conforms to SPARC Reference management — RT626 Cache Controller, Memory MMU Architecture D Module design Management, and Tag Unit — Conforms to SPARC Level 2 MBus — MBus-standard form factor: 3.30” (CMTU) Module Specification (Revision 1.2) (8.34 cm) x 5.78” (14.67 cm) — Four (512-Kbyte) or eight D Dual-clock architecture — Provides CPU upgrade path at (1-Mbyte) RT628 Cache Data Units module level (CDUs) Ċ CPU scaleable up to -

SPARC Assembly Language Reference Manual
SPARC Assembly Language Reference Manual 2550 Garcia Avenue Mountain View, CA 94043 U.S.A. A Sun Microsystems, Inc. Business 1995 Sun Microsystems, Inc. 2550 Garcia Avenue, Mountain View, California 94043-1100 U.S.A. All rights reserved. This product or document is protected by copyright and distributed under licenses restricting its use, copying, distribution and decompilation. No part of this product or document may be reproduced in any form by any means without prior written authorization of Sun and its licensors, if any. Portions of this product may be derived from the UNIX® system, licensed from UNIX Systems Laboratories, Inc., a wholly owned subsidiary of Novell, Inc., and from the Berkeley 4.3 BSD system, licensed from the University of California. Third-party software, including font technology in this product, is protected by copyright and licensed from Sun’s Suppliers. RESTRICTED RIGHTS LEGEND: Use, duplication, or disclosure by the government is subject to restrictions as set forth in subparagraph (c)(1)(ii) of the Rights in Technical Data and Computer Software clause at DFARS 252.227-7013 and FAR 52.227-19. The product described in this manual may be protected by one or more U.S. patents, foreign patents, or pending applications. TRADEMARKS Sun, Sun Microsystems, the Sun logo, SunSoft, the SunSoft logo, Solaris, SunOS, OpenWindows, DeskSet, ONC, ONC+, and NFS are trademarks or registered trademarks of Sun Microsystems, Inc. in the United States and other countries. UNIX is a registered trademark in the United States and other countries, exclusively licensed through X/Open Company, Ltd. OPEN LOOK is a registered trademark of Novell, Inc.