(U//FOUO) Standardizing Our SIGAD/PDDG Naming Conventions
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Case3:08-Cv-04373-JSW Document174-2 Filed01/10/14 Page1 of 7 Exhibit 2
Case3:08-cv-04373-JSW Document174-2 Filed01/10/14 Page1 of 7 Exhibit 2 Exhibit 2 1/9/14 Case3:08-cv-04373-JSWNew Details S Document174-2how Broader NSA Surveil la n Filed01/10/14ce Reach - WSJ.com Page2 of 7 Dow Jones Reprints: This copy is for your personal, non-commercial use only. To order presentation-ready copies for distribution to your colleagues, clients or customers, use the Order Reprints tool at the bottom of any article or visit www.djreprints.com See a sample reprint in PDF Order a reprint of this article now format. U.S. NEWS New Details Show Broader NSA Surveillance Reach Programs Cover 75% of Nation's Traffic, Can Snare Emails By SIOBHAN GORMAN and JENNIFER VALENTINO-DEVRIES Updated Aug. 20, 2013 11:31 p.m. ET WASHINGTON—The National Security Agency—which possesses only limited legal authority to spy on U.S. citizens—has built a surveillance network that covers more Americans' Internet communications than officials have publicly disclosed, current and former officials say. The system has the capacity to reach roughly 75% of all U.S. Internet traffic in the hunt for foreign intelligence, including a wide array of communications by foreigners and Americans. In some cases, it retains the written content of emails sent between citizens within the U.S. and also filters domestic phone calls made with Internet technology, these people say. The NSA's filtering, carried out with telecom companies, is designed to look for communications that either originate or end abroad, or are entirely foreign but happen to be passing through the U.S. -
Meeting the Privacy Movement
-----BEGIN PGP MESSAGE----- Charset: utf-8 Version: GnuPG v2 hQIMA5xNM/DISSENT7ieVABAQ//YbpD8i8BFVKQfbMy I3z8R8k/ez3oexH+sGE+tPRIVACYMOVEMENTRvU+lSB MY5dvAkknydTOF7xIEnODLSq42eKbrCToDMboT7puJSlWr W Meeting the Privacy Movement d 76hzgkusgTrdDSXure5U9841B64SwBRzzkkpLra4FjR / D z e F Dissent in the Digital Age 0 M 0 0 m BIPhO84h4cCOUNTERREVOLUTION0xm17idq3cF5zS2 GXACTIVISTSXvV3GEsyU6sFmeFXNcZLP7My40pNc SOCIALMOVEMENTgQbplhvjN8i7cEpAI4tFQUPN0dtFmCu h8ZOhP9B4h5Y681c5jr8fHzGNYRDC5IZCDH5uEZtoEBD8 FHUMANRIGHTSwxZvWEJ16pgOghWYoclPDimFCuIC 7K0dxiQrN93RgXi/OEnfPpR5nRU/Qv7PROTESTaV0scT nwuDpMiAGdO/byfCx6SYiSURVEILLANCEFnE+wGGpKA0rh C9Qtag+2qEpzFKU7vGt4TtJAsRc+5VhNSAq8OMmi8 n+i4W54wyKEPtkGREENWALDk41TM9DN6ES7sHtA OfzszqKTgB9y10Bu+yUYNO2d4XY66/ETgjGX3a7OY/vbIh Ynl+MIZd3ak5PRIVACYbNQICGtZAjPOITRAS6E ID4HpDIGITALAGEBhcsAd2PWKKgHARRISON4hN4mo7 LIlcr0t/U27W7ITTIEpVKrt4ieeesji0KOxWFneFpHpnVcK t4wVxfenshwUpTlP4jWE9vaa/52y0xibz6az8M62rD9F/ XLigGR1jBBJdgKSba38zNLUq9GcP6YInk5YSfgBVsvTzb VhZQ7kUU0IRyHdEDgII4hUyD8BERLINmdo/9bO/4s El249ZOAyOWrWHISTLEBLOWINGrQDriYnDcvfIGBL 0q1hORVro0EBDqlPA6MOHchfN+ck74AY8HACKTIVISMy 8PZJLCBIjAJEdJv88UCZoljx/6BrG+nelwt3gCBx4dTg XqYzvOSNOWDENTEahLZtbpAnrot5APPELBAUMzAW Qn6tpHj1NSrAseJ/+qNC74QuXYXrPh9ClrNYN6DNJGQ +u8ma3xfeE+psaiZvYsCRYPTOGRAPHYwkZFimy R9bjwhRq35Fe1wXEU4PNhzO5muDUsiDwDIGITAL A Loes Derks van de Ven X o J 9 1 H 0 w J e E n 2 3 S i k k 3 W Z 5 s XEGHpGBXz3njK/Gq+JYRPB+8D5xV8wI7lXQoBKDGAs -----END PGP MESSAGE----- Meeting the Privacy Movement Dissent in the Digital Age by Loes Derks van de Ven A thesis presented to the -
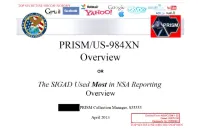
PRISM/US-984XN Overview
TOP SFCRF.T//SI//ORCON//NOFORX a msn Hotmail Go« „ paltalk™n- Youffl facebook Gr-iai! AOL b mail & PRISM/US-984XN Overview OR The SIGAD Used Most in NSA Reporting Overview PRISM Collection Manager, S35333 Derived From: NSA/CSSM 1-52 April 20L-3 Dated: 20070108 Declassify On: 20360901 TOP SECRET//SI// ORCON//NOFORN TOP SECRET//SI//ORCON//NOEÛEK ® msnV Hotmail ^ paltalk.com Youi Google Ccnmj<K8t« Be>cnö Wxd6 facebook / ^ AU • GM i! AOL mail ty GOOglC ( TS//SI//NF) Introduction ILS. as World's Telecommunications Backbone Much of the world's communications flow through the U.S. • A target's phone call, e-mail or chat will take the cheapest path, not the physically most direct path - you can't always predict the path. • Your target's communications could easily be flowing into and through the U.S. International Internet Regional Bandwidth Capacity in 2011 Source: Telegeographv Research TOP SECRET//SI// ORCON//NOFORN TOP SECRET//SI//ORCON//NOEQBN Hotmail msn Google ^iïftvgm paltalk™m YouSM) facebook Gm i ¡1 ^ ^ M V^fc i v w*jr ComnuMcatiw Bemm ^mmtmm fcyGooglc AOL & mail  xr^ (TS//SI//NF) FAA702 Operations U « '«PRISM/ -A Two Types of Collection 7 T vv Upstream •Collection of ;ommujai£ations on fiber You Should Use Both PRISM • Collection directly from the servers of these U.S. Service Providers: Microsoft, Yahoo, Google Facebook, PalTalk, AOL, Skype, YouTube Apple. TOP SECRET//SI//ORCON//NOFORN TOP SECRET//SI//ORCON//NOEÛEK Hotmail ® MM msn Google paltalk.com YOUE f^AVi r/irmiVAlfCcmmjotal«f Rhnnl'MirBe>coo WxdS6 GM i! facebook • ty Google AOL & mail Jk (TS//SI//NF) FAA702 Operations V Lfte 5o/7?: PRISM vs. -
SURVEILLE NSA Paper Based on D2.8 Clean JA V5
FP7 – SEC- 2011-284725 SURVEILLE Surveillance: Ethical issues, legal limitations, and efficiency Collaborative Project This project has received funding from the European Union’s Seventh Framework Programme for research, technological development and demonstration under grant agreement no. 284725 SURVEILLE Paper on Mass Surveillance by the National Security Agency (NSA) of the United States of America Extract from SURVEILLE Deliverable D2.8: Update of D2.7 on the basis of input of other partners. Assessment of surveillance technologies and techniques applied in a terrorism prevention scenario. Due date of deliverable: 31.07.2014 Actual submission date: 29.05.2014 Start date of project: 1.2.2012 Duration: 39 months SURVEILLE WorK PacKage number and lead: WP02 Prof. Tom Sorell Author: Michelle Cayford (TU Delft) SURVEILLE: Project co-funded by the European Commission within the Seventh Framework Programme Dissemination Level PU Public X PP Restricted to other programme participants (including the Commission Services) RE Restricted to a group specified by the consortium (including the Commission Services) CO Confidential, only for members of the consortium (including the Commission Services) Commission Services) Executive summary • SURVEILLE deliverable D2.8 continues the approach pioneered in SURVEILLE deliverable D2.6 for combining technical, legal and ethical assessments for the use of surveillance technology in realistic serious crime scenarios. The new scenario considered is terrorism prevention by means of Internet monitoring, emulating what is known about signals intelligence agencies’ methods of electronic mass surveillance. The technologies featured and assessed are: the use of a cable splitter off a fiber optic backbone; the use of ‘Phantom Viewer’ software; the use of social networking analysis and the use of ‘Finspy’ equipment installed on targeted computers. -
How the Fallout from Post-9/11 Surveillance Programs Can Inform Privacy Protections for COVID-19 Contact Tracing Programs
City University of New York Law Review Volume 24 Issue 1 Winter 2021 How the Fallout from Post-9/11 Surveillance Programs Can Inform Privacy Protections for COVID-19 Contact Tracing Programs Emma Mendelson CUNY School of Law Follow this and additional works at: https://academicworks.cuny.edu/clr Part of the Law Commons Recommended Citation Emma Mendelson, How the Fallout from Post-9/11 Surveillance Programs Can Inform Privacy Protections for COVID-19 Contact Tracing Programs, 24 CUNY L. Rev. 35 (2021). Available at: https://academicworks.cuny.edu/clr/vol24/iss1/4 The CUNY Law Review is published by the Office of Library Services at the City University of New York. For more information please contact [email protected]. HOW THE FALLOUT FROM POST-9/11 SURVEILLANCE PROGRAMS CAN INFORM PRIVACY PROTECTIONS FOR COVID-19 CONTACT TRACING PROGRAMS Emma Mendelson† INTRODUCTION ................................................................... 35 I. THE BUSH ADMINISTRATION AND THE BROADENED SCOPE OF SURVEILLANCE ................................................................... 38 A. The Law and the NSA .................................................... 38 B. The Wave of Backlash Comes Crashing Down ............. 44 II. NATIONAL SECURITY AND PUBLIC HEALTH SURVEILLANCE DURING COVID-19 ........................................................... 46 A. Background on the Data Changes Since 9/11 .............. 47 B. What Does Surveillance During the COVID-19 Pandemic Look Like? .................................................. 48 C. Emerging Criticisms -
SSO Corporate Portfolio Overview
SSO Corporate Portfolio Overview Derived From: NSA/CSSM 1-52 Dated: 20070108 Declassify On: 20361201 What is SSO's Corporate Portfolio? What data can we collect? Where do I go for more help? Agenda 2 What is SSO's Corporate Portfolio? What is SSO Corporate access collection? (TS//SI//NF) Access and collection of telecommunications on cable, switch network, and/or routers made possible by the partnerships involving NSA and commercial telecommunications companies. 3 Brief discussion of global telecommunications infrastructure. How access points in the US can collect on communications from "bad guy" countries (least cost routing, etc.) 4 Unique Aspects Access to massive amounts of data Controlled by variety of legal authorities Most accesses are controlled by partner Tasking delays (TS//SI//NF) Key Points: 1) SSO provides more than 80% of collection for NSA. SSO's Corporate Portfolio represents a large portion of this collection. 2) Because of the partners and access points, the Corporate Portfolio is governed by several different legal authorities (Transit, FAA, FISA, E012333), some of which are extremely time-intensive. 3) Because of partner relations and legal authorities, SSO Corporate sites are often controlled by the partner, who filters the communications before sending to NSA. 4) Because we go through partners and do not typically have direct access to the systems, it can take some time for OCTAVE/UTT/Cadence tasking to be updated at site (anywhere from weekly for some BLARNEY accesses to a few hours for STORMBREW). 5 Explanation of how we can collect on a call between (hypothetically) Iran and Brazil using Transit Authority. -

By Gil Carlson
No longer is there a separation between Earthly technology, other worldly technology, science fiction stories of our past, hopes and aspirations of the future, our dimension and dimensions that were once inaccessible, dreams and nightmares… for it is now all the same! By Gil Carlson (C) Copyright 2016 Gil Carlson Wicked Wolf Press Email: [email protected] To discover the rest of the books in this Blue Planet Project Series: www.blue-planet-project.com/ -1- Air Hopper Robot Grasshopper…7 Aqua Sciences Water from Atmospheric Moisture…8 Avatar Program…9 Biometrics-At-A-Distance…9 Chembot Squishy SquishBot Robots…10 Cormorant Submarine/Sea Launched MPUAV…11 Cortical Modem…12 Cyborg Insect Comm System Planned by DARPA…13 Cyborg Insects with Nuclear-Powered Transponders…14 EATR - Energetically Autonomous Tactical Robot…15 EXACTO Smart Bullet from DARPA…16 Excalibur Program…17 Force Application and Launch (FALCON)…17 Fast Lightweight Autonomy Drones…18 Fast Lightweight Autonomous (FLA) indoor drone…19 Gandalf Project…20 Gremlin Swarm Bots…21 Handheld Fusion Reactors…22 Harnessing Infrastructure for Building Reconnaissance (HIBR) project…24 HELLADS: Lightweight Laser Cannon…25 ICARUS Project…26 InfoChemistry and Self-Folding Origami…27 Iron Curtain Active Protection System…28 ISIS Integrated Is Structure…29 Katana Mono-Wing Rotorcraft Nano Air Vehicle…30 LANdroid WiFi Robots…31 Lava Missiles…32 Legged Squad Support System Monster BigDog Robot…32 LS3 Robot Pack Animal…34 Luke’s Binoculars - A Cognitive Technology Threat Warning…34 Materials -

SSO FAIRVIEW Overview
TOP SECRET//SI/OC//NOFORN SSO FAIRVIEW Overview TOP SECRET//SI/OC//NOFORN TOP SECRET//SI/OC//NOFORN AGENDA • (U) FAIRVIEW DEFINED • (U) OPERATIONAL AUTHORITIES/CAPABILITIES • (U) STATS: WHO IS USING DATA WE COLLECTED • (U) FAIRVIEW WAY AHEAD AND WHAT IT MEANS FOR YOU • (U) QUESTIONS TOP SECRET//SI/OC//NOFORN TOP SECRET//SI/OC//NOFORN International Cables (TS//SI//NF) (TS//SI//NF) TOP SECRET//SI/OC//NOFORN Brief discussion of global telecommunications infrastructure. How access points in the US can collect on communications from “bad guy” countries (least cost routing, etc.) TOP SECRET//SI/OC//NOFORN WHERE SSO IS ACCESSING YOUR TARGET (TS//SI//NF) SSO TARGET UNILATERAL PROGRAMS CABLE MAIL, VOIP, TAP CLOUD SERVICES CORP PARTNER RAM-A RAM-I/X RAM-T RAM-M DGO SSO WINDSTOP BLARNEY SSO CORP MYSTIC AND PRISM FAIRVIEW STORMBREW OAKSTAR TOPI PINWALE XKEYSCORE TURMOIL (TS//SI//NF) TOP SECRET//SI/OC//NOFORN TOP SECRET//SI/OC//NOFORN FAIRVIEW DEFINED • (TS//SI//NF) Large SSO Program involves NSA and Corporate Partner (Transit, FAA and FISA) • (TS//SI//REL FVEY) Cooperative effort associated witH mid- point collection (cable, switch, router) • (TS//SI//NF) THe partner operates in tHe U.S., but Has access to information tHat transits tHe nation and tHrougH its corporate relationships provide unique accesses to otHer telecoms and ISPs (TS//SI//NF) 5 (TS//SI//NF) TOP SECRET//SI/OC//NOFORN TOP SECRET//SI/OC//NOFORN Unique Aspects (C) Access to massive amounts of data (C) Controlled by variety of legal authorities (C) Most accesses are controlled by partner (C) Tasking delays TOP SECRET//SI/OC//NOFORN (TS//SI//NF) Key Points: 1) SSO provides more than 80% of collection for NSA. -

Witness Statement of Eric King
IN THE INVESTIGATORY POWERS TRIBUNAL Case No IPT/13/92/CH BETWEEN: PRIVACY INTERNATIONAL Claimants -and- (1) SECRETARY OF STATE FOR FOREIGN AND COMMONWEALTH AFFAIRS (2) GOVERNMENT COMMUNICATION HEADQUARTERS Defendants WITNESS STATEMENT OF ERIC KING I, Eric King, Deputy Director, Privacy International, 62 Britton Street, London EC1M 5UY, SAY AS FOLLOWS: 1. I am the Deputy Director of Privacy International. 2. I hold a Bachelor of Laws from the London School of Economics and have worked on issues related to communications surveillance at Privacy International since 2011. My areas of interest and expertise are signals intelligence, surveillance technologies and communications surveillance practices. I regularly speak at academic conferences, with government policy makers, and to international media. I have spent the past year researching the “Five Eyes” intelligence-sharing arrangement and the materials disclosed by Edward Snowden. 3. I make this statement in support of Privacy International’s claim. The contents of this statement are true to the best of my knowledge, information and belief and are the product of discussion and consultation with other experts. Where I rely on other sources, I have endeavoured to identify the source . 4. In this statement I will address, in turn, the following matters: a. The transmission and interception of digital communications; b. The difference between internal and external communications under RIPA, as applied to the internet and modern communications techniques; c. Intelligence sharing practices among the US, UK, Australia, New Zealand and Canada (“the Five Eyes”); d. The UK’s consequent access to signals intelligence collected by the United States through its PRISM and UPSTREAM collection programmes; e. -

Biblioteca Digital
Universidad de Buenos Aires Facultades de Ciencias Económicas, Ciencias Exactas y Naturales e Ingeniería Carrera de Especialización en Seguridad Informática Trabajo Final “Vigilancia masiva y manipulación de la opinión pública” Autor: Ing. Juan Ignacio Schab Tutor: Dr. Pedro Hecht Año de presentación: 2020 Cohorte 2018 Declaración Jurada del origen de los contenidos Por medio de la presente, el autor manifiesta conocer y aceptar el Reglamento de Trabajos Finales vigente y se hace responsable que la totalidad de los contenidos del presente documento son originales y de su creación exclusiva, o bien pertenecen a terceros u otras fuentes, que han sido adecuadamente referenciados y cuya inclusión no infringe la legislación Nacional e Internacional de Propiedad Intelectual. Ing. Juan Ignacio Schab DNI 37.338.256 Resumen Dos escándalos de gran repercusión internacional han contribuido para probar la real dimensión de los dos temas que dan título al presente trabajo. El primero de ellos fue la revelación de miles de documentos clasificados de agencias de inteligencia, principalmente estadounidenses, realizada por Edward Snowden, ex contratista de la CIA y la NSA, en el año 2013, la cual dio detalles de la extendida y profunda vigilancia masiva a escala global, la cual destruye el derecho a la privacidad y limita las libertades individuales. El otro hecho fue la participación de la empresa Cambridge Analytica en procesos electorales de distintos países del mundo, especialmente en las elecciones presidenciales de Estados Unidos en 2016 y en el referéndum para la salida de Gran Bretaña de la Unión Europea en el mismo año, revelada por ex trabajadores de la misma y por investigaciones de medios de comunicación, el cual permitió dar detalles sobre la capacidad de manipulación de la opinión pública principalmente a través de redes sociales. -

No Oversight, No Limits, No Worries: a Primer on Presidential Spying and Executive Order 12,333 ______
58 Harvard National Security Journal / Vol. 12 ARTICLE No Oversight, No Limits, No Worries: A Primer on Presidential Spying and Executive Order 12,333 _________________________ Mark M. Jaycox* *Mark M. Jaycox, Policy Counsel, Google. Prior to this, the author served as the Civil Liberties Legislative Lead at the Electronic Frontier Foundation, where he specialized on consumer privacy issues, cybersecurity, electronic surveillance, and national security law. B.A., Reed College; J.D., UC Berkeley School of Law. The author would like to thank the Professor who oversaw the initial drafts of this paper at Berkeley, Jim Dempsey. He would also like to thank Lee Tien, Jonathan Mayer, Ashkan Soltani, Neema Singh Guliani, and many more for their critical insights, discussions, and debates on this topic. Copyright © 2021 by the President and Fellows of Harvard College and Mark M. Jaycox. 2021 / No Oversight, No Limits, No Worries 59 Abstract Executive Order 12,333 ("EO 12333") is a 1980s Executive Order signed by President Ronald Reagan that, among other things, establishes an overarching policy framework for the Executive Branch's spying powers. Although electronic surveillance programs authorized by EO 12333 generally target foreign intelligence from foreign targets, its permissive targeting standards allow for the substantial collection of Americans' communications containing little to no foreign intelligence value. This fact alone necessitates closer inspection. This Article conducts such an inspection by collecting and coalescing the various declassifications, disclosures, legislative investigations, and news reports concerning EO 12333 electronic surveillance programs in order to provide a better understanding of how the Executive Branch implements the order and the surveillance programs it authorizes. -

NSA's Global Interception Network Search
FUN GADGET WORLD Fun Gadget World, Samsung Tool PRO, Android Multi Tools, Android Jelly Bean, stock firmware, AT&T Connect, Ulefone Tiger, techno n8 and Octopus Box LG Setup HOME ANDROID INFO ANDROID APPS APPLE PHONE APPLICATIONS BLACKBERRY SAMSUNG PHONE Home » NSA » NSA's global interception network Search.. GO NSA's global interception network By untu MENGENAI SAYA NSA's global interception network - a lot of websites that discuss information about gadgets, including this blog Fun Gadget World we discuss all the information from various brands of gadgets, from the old to the latest, which is very dear if you miss, now Kimberly Madeline we discuss first about NSA's global interception network we have collect lots of data to Lihat profil lengkapku create this article so that you get complete information, so please read it: Articles : NSA's global interception network full Link : NSA's global interception network Article NSA, You can also see our article on: POPULAR POSTS Is the Shadow Brokers leak the latest in a series? For All Networks, "Fiber to Where You Can Make Money" is the Issue "Fiber to where you can make money" is a good NSA's global interception network way to evaluate various fixed network access methods. For cable TV operators, the is... (Updated: July 17, 2014) All Internet of Things Forecasts Slope Up and to the Right On November 23, the Dutch newspaper NRC Handelsblad published a new slide from the It is impossible to find any Internet of Things Snowden documents. The slide is from a Top Secret NSA management presentation from forecasts, for any segment of the market, that fail to show an”upward sloping to the right” ..