Ada User Journal
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Uefi وبعض أنظمة Bios Uefi واجهة الربنامج الثابت املوحدة والقابلة للتمديد
- جدول أقسامGUID GUID Partition Table جدول أقسام )أو تقسيم( يستخدم املعرفات الفريدة العميمة "! G % تعري. و-يي, ا+قسام *( ال)'ي& املقسم % أ$#مة !0/ و2ع1 أ$#مة 45!3 UEFI واج=ة ال>$ا;: ال9ا82 امل)7دة والقا62ة ل6تمديد مس جد? % ;<رم ّو@B @AA دة 'Cتمرب/أي6)ل DE@F2 " F جدول أقسام GUID *باIة *H تخGيط )أو تقسيم( جدول أقسام ;عياJI *( أج=,ة التخ,يH الفي,ياKيةM9; L ا+قراN الثا2تةL أو أقراN الحالة الC6OةPQ Lا التخGيط يستخدم املعرR الفريد العميم U@TS % متيي, ا+قسام وأ$)ا*هاL وXIم أ$W ج,H; V ;عياI واج=ة ال>نا;: الثا82 امل)حدة والقا62ة ل6تمديد !U ZD S YL /0 )املق^[ ;H ;\تد] h _`abc /0! 0defgبديM ل6\ظام التق6يدJ 45!3( $ظام Hlm GPj ا'تخدا;W أيضا % 2ع1 أ$#مة 45!3 بسnC ;حدو?ية جدول أقسام Lo3p الذJ يستخدم 82qTD فقط % تخ,يH ;ع6)مات ال<rم و*ناويr7 v; us3t Hم القGاw التق6يدqx@D Jبايu8 ;ع#م أ$#مة التشyيM تد*م P\; LGPj العام LDE@E 2ع1 ا+$#مة ;M9 ما{ أوu|} ومايكرو')ف8 ويندو~ )x86( تد*م فقط اإلقالH; w أقسام GPj % أ$#مة !L /0!B/0 2ي\ام ;ع#م ت)~يعات لي\lس و ت)~يعات 2ريhيل ي)$lس ;M9 فرJ يب |} ?lm J\ها اإلقالH; w أقسام GPj % أج=,ة 45!3 أو أج=,ة !u /0 6A TD % ا+قراN الثا2تة التي تستخدم r7م القطاw املعياx@D JI بايL8 ال<rم ا+قىص ل6قرN با'تخدام DuD (Q o3p ترياباي8 أو ) x@D × D بايuU @ S )8 2ي\ام ال<rم ا+قىص ل6قرN با'تخدام GPj 'يك)ن FuA ~يتاباي8 أو ) x@D × D بايU T S U @ S )8 والسnC % ذلك ا'تخدام H; 82 6A أجM *ناويH الكتM امل\Gقية % جدول أقسام u GPj تاIيخياL رشhة |$تي LM كا$8 وIاV تG)ير LGPj أواخر التسعينات )L)DEEE الذJ أصCح ج,H; V ;)اصفة !U D S Y /0 % عام DE@E وت<8 |?اIة Qيئة خاصة تد*ى !P\; u _`abc /0 عام uDEEF قطاعات GPT % عام LDE@E *ندما بدأ ;\تr)ن ا+قراN الثا2تة الت<)ل |ىل ت)ظي. -
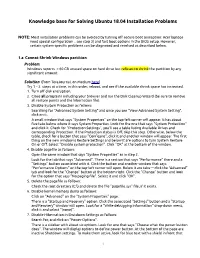
Knowledge Base for Solving Ubuntu 18.04 Installation Problems
Knowledge base for Solving Ubuntu 18.04 Installation Problems NOTE: Most installation problems can be avoided by turning off secure boot (exception: Acer laptops need special configuration .. see step 3) and fast boot options in the BIOS setup. However, certain system-specific problems can be diagnosed and resolved as described below. 1.a Cannot Shrink Windows partition Problem: Windows reports > 60 GB unused space on hard drive but refuses to shrink the partition by any significant amount. Solution: (from TeraJournal, on Medium here) Try 1 – 2 steps at a time, in this order, reboot, and see if the available shrink space has increased. 1. Turn off disk encryption. 2. Close all programs including your browser and run the Disk Cleanup Wizard (be sure to remove all restore points and the hibernation file). 3. Disable System Protection as follows: Searching for "Advanced System Setting" and once you see "View Advanced System Setting", click on it. A small window that says "System Properties" on the top-left corner will appear. It has about five tabs below where it says System Properties. Look for the one that says "System Protection" and click it. Check for "Protection Settings", you’ll see a table listing Available Drives and corresponding Protection. If the Protection status is Off, skip this step. Otherwise, below the table, check for a button that says "Configure", click it and another window will appear. The first thing on the new window is Restore Settings and below it are options to turn System Restore On or Off. Select "Disable system protection". Click "OK" at the bottom of the window. -

PC Hardware Contents
PC Hardware Contents 1 Computer hardware 1 1.1 Von Neumann architecture ...................................... 1 1.2 Sales .................................................. 1 1.3 Different systems ........................................... 2 1.3.1 Personal computer ...................................... 2 1.3.2 Mainframe computer ..................................... 3 1.3.3 Departmental computing ................................... 4 1.3.4 Supercomputer ........................................ 4 1.4 See also ................................................ 4 1.5 References ............................................... 4 1.6 External links ............................................. 4 2 Central processing unit 5 2.1 History ................................................. 5 2.1.1 Transistor and integrated circuit CPUs ............................ 6 2.1.2 Microprocessors ....................................... 7 2.2 Operation ............................................... 8 2.2.1 Fetch ............................................. 8 2.2.2 Decode ............................................ 8 2.2.3 Execute ............................................ 9 2.3 Design and implementation ...................................... 9 2.3.1 Control unit .......................................... 9 2.3.2 Arithmetic logic unit ..................................... 9 2.3.3 Integer range ......................................... 10 2.3.4 Clock rate ........................................... 10 2.3.5 Parallelism ......................................... -
UEFI+Linux on ARM Making It Just Work
UEFI+Linux on ARM Making it Just Work Korea Linux Forum 12 November 2013 Presentation by Grant Likely Agenda Introduction Rationale Enterprise Mobile Embedded Boot Sequence Runtime Services Device Tree, ACPI and SMBIOS Current Status Future Work? Questions Slide 2 Rationale: Enterprise New ARM enterprise products Competing with x86 platforms Any gratuitous difference from x86 is a cost For vendors – Engineering and manufacturing tools won't carry over For customers – Integrating into data centre requires new knowledge UEFI and U-Boot behave very differently U-Boot Boot variables specify kernel, initrd and command line Currently no default behaviour for booting automatically UEFI Specification for how to choose boot device. Specification for ABI and execution environment. Slide 3 Rationale: Enterprise ARM servers should behave the same Use same firmware ABI – UEFI Use same hardware description ABI – ACPI Use same interfaces Network boot – DHCP, and TFTP of UEFI executable Block device – GPT Partition table, FAT system partition Secure Boot – Ship in Setup Mode, as is appropriate for server machines Firmware device drivers – same ABIs Same software stack Second stage boot selection GRUB, Gummiboot or rEFInd UEFI stub embedded in kernel How can Linux developers influence UEFI development? Slide 4 Rationale: Mobile Smart phones have become general-purpose computers Abstracted at the userspace level. Much of the hardware looks the same anyway Big processor, large touch screen, a bunch of sensors and wireless -
Disable “Fast Startup” Function of Windows
Installing Ubuntu alongside other pre-installed OS Haanju Yoo & Sangdoo Yun Contents 1. Windows setup for dual booting with Ubuntu 2. Max OSX setup for dual booting with Ubuntu 3. Install Ubuntu 14.04 NOTICE: Depend on your pre-installed OS, use this material as below - Windows: Chapter 1 ⇒ Chapter 3 - Mac OSX: Chapter 2 ⇒ Chapter 3 2 Chapter 01. Windows setup for dual booting with Ubuntu Outline • If you are a Mac user, please proceed to the next chapter • In this section, we will introduce how to setup your Windows OS (8, 8.1, and 10) before installing Ubuntu alongside the Windows OS. • If you are familiar with installing operating system, please go to the link http://www.everydaylinuxuser.com/2014/05/install-ubuntu-1404-alongside- windows.html that contains more details. • The overall procedure is summarized by below 1. Make a backup of your files 2. Make a booting USB of Ubuntu 14.04 3. Disable “Fast Startup” function of Windows 4. Set up the partitions of your hard drive 5. Booting with “UEFI : USB DISK” 4 Make a backup of your files • Back up all of your Windows files and folders that you don't want to lose. • Reason • As long as you have enough free hard drive space for your new Ubuntu partition, this process should not interfere with Windows files. Should is a risky word, though. • Moreover, you can make a mistake during the process. • (Recommended) Open Windows Explorer, and copy them to a backup disk. • For using a backup tool of Windows, please refer ‘1. -

Clover Efi Manual Install
Clover Efi Manual Install Once the EFI drive is mounted, simply copy the EFI/Clover folder from your USB or OS-X partition (if you installed Clover on OS-X too) to root. Clover Bootloader is a great boot loader, it supports both UEFI and Legacy. This article will guide you how. Manually install Clover EFI Bootloader via Linux System on Legacy BIOS or UEFI Firmware. - badruzeus/CloverEFI-4MU. This is critical so don't rush to install Clover with a Standard Installation. These options should be selected. Clover Efi Manual Install --> Click For Download --> Hey, I successfully Installed Yosemite on my Hp probook, and now I can boot from the flash memory successfully and it is running fine, however. But that's not the case if you have installed macOS Mojave on VMware or installed While this way works perfectly but things are little manual to do. The Clover EFI Bootloader that configures and boots into OS X with UEFI or BIOS firmware. Q: Clover was installed and started from a USB flash drive but my HDD is not seen. Q: I am booting with UEFI but do not see my Mac partition, just the legacy ones. If automatic patching fails, add your own, manually customised, DSDT. (x) Install for UEFI booting only, (x) Install Clover in the ESP the USB drive before I figured out that I need to manually add the EFI boot options. When installing to HDD, also select "Install RC scripts on target volume" and "Install Clover Preference Pane". Picture. Make sure that it shows "Installation. -
Uefi Booting Boot Camp
TUTORIAL UEFI UEFI BOOTING BOOT TUTORIAL CAMP (REBOOTED) Upgrade your the way your system boots without installing a GRAHAM MORRISON distribution or resorting to Grub. e’ve been using the BIOS for decades. It’s to install another operating system. In reality, the as perennial as your keyboard and mouse, Secure Boot cataclysm has yet to materialise, as Wbreathing life into inert hardware when a many PCs still include a traditional BIOS or allow little electricity is applied. These days, the POST status you to disable Secure Boot. The latter option should messages delivered after your BIOS initialises the always be available, and you’ll need to disable Secure system race across the screen so quickly you seldom Boot unless you want to start dealing with signing a get the chance to read the text, making entering bootloader shim. the BIOS itself a mad keyboard-bashing mini-game that more often than not ends with Grub than the Muddy waters configuration menus you’re after. Modern PCs aren’t Another potentially confusing option is something well suited to the old-school charm of the BIOS. They called the Compatibility Support Module. To the user, don’t want to wait for permission, they don’t want low- this will appear as a hybrid between UEFI and the res large white fonts on a blue background. They just BIOS, a magical panacea that seems to allow us to want to get on with the job at hand, and that’s booting forget about UEFI and BIOS completely. You’ll typically your computer. -
CIS 4360 Secure Computer Systems System Boot
CIS 4360 Secure Computer Systems System Boot Professor Qiang Zeng Spring 2017 Previous Class • What a TPM is: – Hardware protected keys • Endorsement key: for signing (PCR values) • Storage root key: for encrypting storage keys – Crypto-processor • RSA • HMAC • SHA-1 (SHA-2 in TPM 2.0) – PCR • What the TPM can do – Attestation – Sealed storage CIS 4360 – Secure Computer Systems 2 TPM-Based Attestation Example [Gasser et al. ‘89], [Arbaugh et al. ‘97], [Sailer et al. ‘04], [Marchesini et al. ‘04] Module Module Module App Module App App BIOS Bootloader OS PCRs TPM KPriv 3 Establishing Trust via a TPM [Gasser et al. ‘89], [Arbaugh et al. ‘97], [Sailer et al. ‘04], [Marchesini et al. ‘04] Guarantees randomModule # Accurate! Module freshness Module A Module Module A Module p App Module p A Module App p p p App K OS Pu p BIOS Bootloader Guarantees BIOS Bootloader b OS Module A real TPM Module A Module p Module p A p p p OS p BIOS Bootloader Sign ( random # ) Kpriv PCRs Guarantees actual TPM logs TPM KPriv 4 BitLocker • At system boot (before OS boot) – Optional: BIOS requests PIN or USB key from user – TPM unseals VMK, if PCR and PIN are correct • PIN is to derive the keyAuth (recall TPM_SEAL) • TPM defends against dictionary attack on PIN • Many options for VMK recovery in certain cases – Disk, USB, paper (all encrypted with password) – Recovery needed after legitimate system change: • Moving disk to a new computer • Replacing system board containing TPM • Clearing TPM CIS 4360 – Secure Computer Systems 5 Previous Class What is Measured Boot? At each stage of system booIng, the code and configuraon for the next stage is scanned and the hash value is recorded in TPM (by extending a specified PCR) CIS 4360 – Secure Computer Systems 6 Previous Class What aacks can you do if you have extracted the private key from a TPM A soSware module can claim itself as a TPM. -

Strengthening the Chain of Trust
presented by Strengthening the Chain of Trust Kevin Lane – HP Jeff Bobzin – Insyde Software August Updated22, 2014 2011-06-01 Agenda • Quick Intro to UEFI • UEFI Myths • Using Linux + Secure Boot • Continuing the Chain-of- Trust LinuxCon 2014 www.uefi.org 2 UEFI Specification: What Is It? • Defines a PC operating system and platform firmware interface • Replaces Basic Input/Output System (BIOS) firmware interface – Note: most UEFI images provide legacy support for BIOS services. • Consists of platform data tables, boot and runtime service calls • Supports remote diagnostics and repair, even without an OS • Standardizes booting of OSes and running pre-boot applications • Evolved from Intel’s EFI (Extensible Firmware Interface) specification – Note: EFI was deprecated by UEFI in 2005. • Managed by the UEFI Forum LinuxCon 2014 www.uefi.org 3 UEFI Specification: Milestones • Mid-90s: First Intel–HP Itanium system development occurs – BIOS limitations (e.g., 16-bit processor mode, 1 MB addressable space and PC AT hardware) don’t meet needs of larger server platforms • 1998: Intel creates EFI (originally “Intel Boot Initiative") to solve BIOS issue • 2005: Intel ceases EFI spec development at v1.10; contributes it to UEFI Forum – Original EFI specification remains owned and licensed by Intel • 2007: UEFI Forum releases UEFI specification v2.1 – Adds cryptography, network authentication, user interface architecture (UEFI’s Human Interface Infrastructure) • 2008: UEFI Forum releases UEFI specification v2.2 – Adds Secure Boot • 2013: UEFI Forum -
The Ultimate Linux Newbie Guide
The Ultimate Linux Newbie Guide The ultimate guide for choosing, installing and using Linux for everyday people Table of Contents Choosing, Installing and Using Linux has never been easier! The Ultimate Linux Newbie Guide is the guide for the everyday person. This eBook version of the guide provides the main guide from the website, as well as a few select articles. 1. Introduction 2. About The Author 3. About the Author (continued) 4. The Guide 5. Chapter 1: What is Linux 6. Chapter 2: Why Linux - What are the Benets? 7. Chapter 3: Choosing a Linux Distribution 8. Chapter 4: Preparing to Install Linux 9. Chapter 5: Installing Linux (Ubuntu) 10. Chapter 6: How do I use Linux? 11. Chapter 7: Using Linux Every Day 12. Other Tutorials 13. Linux Command Line Introduction 14. Is there a OneDrive client for Linux? 15. How to use Google Drive, OneDrive, Dropbox, Amazon S3 and more in Linux 16. How to install Linux on a Macintosh and dual boot with macOS 17. How I got my job in Linux: from Newbie to Pro Introduction Since 2001, The Ultimate Linux Newbie Guide has been helping individuals switch to the Linux Operating System. This guide can help both beginners and seasoned computer users alike learn all the important parts of choosing, using and installing Linux, a great free operating system for your computer and help you remove dependency on non-free, closed source software that is commonplace in Microsoft Windows or Mac OS. Throughout the guide, you’ll nd out heaps of valuable information, such as: How Linux offers a real alternative to other operating systems, how you can install Linux on to your computer for free, and how to get to grips with using Linux on a daily basis without any techno jargon! After you've nished reading the book, don't forget to visit the website. -

Copyrighted Material
Index COPYRIGHTED MATERIAL Index [ ] (brackets) in file naming, 180 adding, 348–350 ` (backtick) character, 21 password setting, 350–351 | (pipe) character, 19–20 ACL (access control list), 205 ~ (tilde) character in commands, 6 AD (Active Directory), 357–358 / (root) directory, 218 addresses, network, 414–415 * (asterisk) in file naming, 179, 180 base-10 numbers, 416 \ (backward slash) in file naming, 179 broadcasts, 419–420 - (dash) in file naming, 178 DHCP and, 415 . (dot) in file naming, 178 IPv4, 416 / (forward slash) in file naming, 179 IPv6, 416–417 ? (question mark) in file naming, 179, link-local, 417 180 MAC, 415 ~ (tilde) in file naming, 178 managing, 415–316, 415–417 _ (underscore) in file naming, 178 network mask, 417–419 “ (quotation mark) in file naming, 179 aliases, 459–460 alien utility, 75–77 answers to questions, 576–612 A apt-cache, 67 Accelerated-X, 281 apt-get, 68–71 accessibility, X archiving files, 187 display, 312–314 cpio utility, 191–194 keyboard, 310–312 dd utility, 194–195 mouse, 310–312 tar utility, 188–191 AccessX utility, keyboard, 310–312 zip files, 188 accounts assistive technologies in X, 314 chage, 354–355 at, 396–398 configuration files, 355–357 attackers, 525 deleting, 358–359 automated tasks groups, 345–346 at, 396–398 network account databases, 357–358 cron, 389 records, viewing, 362–364 anacron, 394–396 usermod, 352–353 cron jobs, 389 usernames, 345 creating, 390–391 users, 344–345 user cron jobs, 391–393 616 background processes – command completion boot process B kernel ring buffer, 247 background -

Quick Summary (By Francisco Novoa) 1. First Boot Mac OS Install Using
Quick Summary (By Francisco Novoa) 1. First boot Mac OS install using your opencore usb stick 2. At MacOS Install you need to configure hardisk to be ready to install Windows. 3. Do not install yet MacOS 4. Restart to Windows Install with your USB (you can make one on Windows with Microsoft Tool) 5. Insteas of install windows throug gui press Shift+F10 to entender Shell 6. Follow instructions on this guide to use diskpart and create needed partitions 7. Install Windows following this guide (not gui install) 8. Reboot to Windows and setup it normally 9. Reboot using your opencore + install macos usb stick 10. Install mac os on MacOS partition that you have created on the first step 11. Configure normally your MacOS 12. Reboot with your usb to be ensure that windos and mac shows at opencore menú 13. If you select Windows, probably you’ll get a nice blue screen, so dont worry 14. Start your MacOS with your usb 15. Download Refind from this link https://sourceforge.net/projects/refind/ 16. Unzip it 17. Install “Refind-install” 18. Mount your hardisk efi folder (use mountefi https://github.com/corpnewt/MountEFI) 19. Your efi folder Will not be empty (Windows files Will be there) 20. Copy your OC folder from your opencore usb drive to your hardisk efi folder 21. Look for your bootx64.efi file inside your efi/boot folder and copy it into your EFI/OC folder inside your hardisk efi partition. 22. Copy your downloaded “Refind” folder to your EFI Disk 23.