Diffie and Hellman Receive 2015 Turing Award Rod Searcey/Stanford University
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Tarjan Transcript Final with Timestamps
A.M. Turing Award Oral History Interview with Robert (Bob) Endre Tarjan by Roy Levin San Mateo, California July 12, 2017 Levin: My name is Roy Levin. Today is July 12th, 2017, and I’m in San Mateo, California at the home of Robert Tarjan, where I’ll be interviewing him for the ACM Turing Award Winners project. Good afternoon, Bob, and thanks for spending the time to talk to me today. Tarjan: You’re welcome. Levin: I’d like to start by talking about your early technical interests and where they came from. When do you first recall being interested in what we might call technical things? Tarjan: Well, the first thing I would say in that direction is my mom took me to the public library in Pomona, where I grew up, which opened up a huge world to me. I started reading science fiction books and stories. Originally, I wanted to be the first person on Mars, that was what I was thinking, and I got interested in astronomy, started reading a lot of science stuff. I got to junior high school and I had an amazing math teacher. His name was Mr. Wall. I had him two years, in the eighth and ninth grade. He was teaching the New Math to us before there was such a thing as “New Math.” He taught us Peano’s axioms and things like that. It was a wonderful thing for a kid like me who was really excited about science and mathematics and so on. The other thing that happened was I discovered Scientific American in the public library and started reading Martin Gardner’s columns on mathematical games and was completely fascinated. -

Butler Lampson, Martin Abadi, Michael Burrows, Edward Wobber
Outline • Chapter 19: Security (cont) • A Method for Obtaining Digital Signatures and Public-Key Cryptosystems Ronald L. Rivest, Adi Shamir, and Leonard M. Adleman. Communications of the ACM 21,2 (Feb. 1978) – RSA Algorithm – First practical public key crypto system • Authentication in Distributed Systems: Theory and Practice, Butler Lampson, Martin Abadi, Michael Burrows, Edward Wobber – Butler Lampson (MSR) - He was one of the designers of the SDS 940 time-sharing system, the Alto personal distributed computing system, the Xerox 9700 laser printer, two-phase commit protocols, the Autonet LAN, and several programming languages – Martin Abadi (Bell Labs) – Michael Burrows, Edward Wobber (DEC/Compaq/HP SRC) Oct-21-03 CSE 542: Operating Systems 1 Encryption • Properties of good encryption technique: – Relatively simple for authorized users to encrypt and decrypt data. – Encryption scheme depends not on the secrecy of the algorithm but on a parameter of the algorithm called the encryption key. – Extremely difficult for an intruder to determine the encryption key. Oct-21-03 CSE 542: Operating Systems 2 Strength • Strength of crypto system depends on the strengths of the keys • Computers get faster – keys have to become harder to keep up • If it takes more effort to break a code than is worth, it is okay – Transferring money from my bank to my credit card and Citibank transferring billions of dollars with another bank should not have the same key strength Oct-21-03 CSE 542: Operating Systems 3 Encryption methods • Symmetric cryptography – Sender and receiver know the secret key (apriori ) • Fast encryption, but key exchange should happen outside the system • Asymmetric cryptography – Each person maintains two keys, public and private • M ≡ PrivateKey(PublicKey(M)) • M ≡ PublicKey (PrivateKey(M)) – Public part is available to anyone, private part is only known to the sender – E.g. -

Diamondoid Mechanosynthesis Prepared for the International Technology Roadmap for Productive Nanosystems
IMM White Paper Scanning Probe Diamondoid Mechanosynthesis Prepared for the International Technology Roadmap for Productive Nanosystems 1 August 2007 D.R. Forrest, R. A. Freitas, N. Jacobstein One proposed pathway to atomically precise manufacturing is scanning probe diamondoid mechanosynthesis (DMS): employing scanning probe technology for positional control in combination with novel reactive tips to fabricate atomically-precise diamondoid components under positional control. This pathway has its roots in the 1986 book Engines of Creation, in which the manufacture of diamondoid parts was proposed as a long-term objective by Drexler [1], and in the 1989 demonstration by Donald Eigler at IBM that individual atoms could be manipulated by a scanning tunelling microscope [2]. The proposed DMS-based pathway would skip the intermediate enabling technologies proposed by Drexler [1a, 1b, 1c] (these begin with polymeric structures and solution-phase synthesis) and would instead move toward advanced DMS in a more direct way. Although DMS has not yet been realized experimentally, there is a strong base of experimental results and theory that indicate it can be achieved in the near term. • Scanning probe positional assembly with single atoms has been successfully demonstrated in by different research groups for Fe and CO on Ag, Si on Si, and H on Si and CNHCH3. • Theoretical treatments of tip reactions show that carbon dimers1 can be transferred to diamond surfaces with high fidelity. • A study on tip design showed that many variations on a design turn out to be suitable for accurate carbon dimer placement. Therefore, efforts can be focused on the variations of tooltips of many kinds that are easier to synthesize. -
Communications of the Acm
COMMUNICATIONS CACM.ACM.ORG OF THEACM 11/2014 VOL.57 NO.11 Scene Understanding by Labeling Pixels Evolution of the Product Manager The Data on Diversity On Facebook, Most Ties Are Weak Keeping Online Reviews Honest Association for Computing Machinery tvx-full-page.pdf-newest.pdf 1 11/10/2013 12:03 3-5 JUNE, 2015 BRUSSELS, BELGIUM Course and Workshop C proposals by M 15 November 2014 Y CM Paper Submissions by MY 12 January 2015 CY CMY K Work in Progress, Demos, DC, & Industrial Submissions by 2 March 2015 Welcoming Submissions on Content Production Systems & Infrastructures Devices & Interaction Techniques Experience Design & Evaluation Media Studies Data Science & Recommendations Business Models & Marketing Innovative Concepts & Media Art TVX2015.COM [email protected] ACM Books M MORGAN& CLAYPOOL &C PUBLISHERS Publish your next book in the ACM Digital Library ACM Books is a new series of advanced level books for the computer science community, published by ACM in collaboration with Morgan & Claypool Publishers. I’m pleased that ACM Books is directed by a volunteer organization headed by a dynamic, informed, energetic, visionary Editor-in-Chief (Tamer Özsu), working closely with a forward-looking publisher (Morgan and Claypool). —Richard Snodgrass, University of Arizona books.acm.org ACM Books ◆ will include books from across the entire spectrum of computer science subject matter and will appeal to computing practitioners, researchers, educators, and students. ◆ will publish graduate level texts; research monographs/overviews of established and emerging fields; practitioner-level professional books; and books devoted to the history and social impact of computing. ◆ will be quickly and attractively published as ebooks and print volumes at affordable prices, and widely distributed in both print and digital formats through booksellers and to libraries and individual ACM members via the ACM Digital Library platform. -
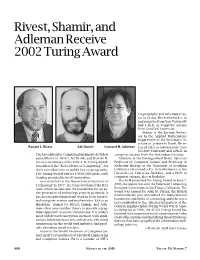
Rivest, Shamir, and Adleman Receive 2002 Turing Award, Volume 50
Rivest, Shamir, and Adleman Receive 2002 Turing Award Cryptography and Information Se- curity Group. He received a B.A. in mathematics from Yale University and a Ph.D. in computer science from Stanford University. Shamir is the Borman Profes- sor in the Applied Mathematics Department of the Weizmann In- stitute of Science in Israel. He re- Ronald L. Rivest Adi Shamir Leonard M. Adleman ceived a B.S. in mathematics from Tel Aviv University and a Ph.D. in The Association for Computing Machinery (ACM) has computer science from the Weizmann Institute. named RONALD L. RIVEST, ADI SHAMIR, and LEONARD M. Adleman is the Distinguished Henry Salvatori ADLEMAN as winners of the 2002 A. M. Turing Award, Professor of Computer Science and Professor of considered the “Nobel Prize of Computing”, for Molecular Biology at the University of Southern their contributions to public key cryptography. California. He earned a B.S. in mathematics at the The Turing Award carries a $100,000 prize, with University of California, Berkeley, and a Ph.D. in funding provided by Intel Corporation. computer science, also at Berkeley. As researchers at the Massachusetts Institute of The ACM presented the Turing Award on June 7, Technology in 1977, the team developed the RSA 2003, in conjunction with the Federated Computing code, which has become the foundation for an en- Research Conference in San Diego, California. The tire generation of technology security products. It award was named for Alan M. Turing, the British mathematician who articulated the mathematical has also inspired important work in both theoret- foundation and limits of computing and who was a ical computer science and mathematics. -

Welcome to AI Matters 5(1)
AI MATTERS, VOLUME 5, ISSUE 1 5(1) 2019 Welcome to AI Matters 5(1) Amy McGovern, co-editor (University of Oklahoma; [email protected]) Iolanda Leite, co-editor (Royal Institute of Technology (KTH); [email protected]) DOI: 10.1145/3320254.3320255 Issue overview receiving the 2018 ACM A.M. Turing Award! Welcome to the first issue of the fifth vol- ume of the AI Matters Newsletter! This issue opens with some news on a new SIGAI Stu- Submit to AI Matters! dent Travel Scholarship where we aim to en- Thanks for reading! Don’t forget to send courage students from traditionally underrep- your ideas and future submissions to AI resented geographic locations to apply and at- Matters! We’re accepting articles and an- tend SIGAI supported events. We also sum- nouncements now for the next issue. De- marize the fourth AAAI/ACM SIGAI Job Fair, tails on the submission process are avail- which continues to grow with the increasing able at http://sigai.acm.org/aimatters. popularity of AI. In our interview series, Marion Neumann interviews Tom Dietterich, an Emer- itus Professor at Oregon State University and one of the pioneers in Machine Learning. Amy McGovern is co- In our regular columns, we have a summary editor of AI Matters. She of recent and upcoming AI conferences and is a Professor of com- events from Michael Rovatsos. Our educa- puter science at the Uni- tional column this issue is dedicated to “biduc- versity of Oklahoma and tive computing”, one of Prolog’s most distinc- an adjunct Professor of tive features. -

Benchmarks for IP Forwarding Tables
Reviewers James Abello Richard Cleve Vassos Hadzilacos Dimitris Achilioptas James Clippinger Jim Hafner Micah Adler Anne Condon Torben Hagerup Oswin Aichholzer Stephen Cook Armin Haken William Aiello Tom Cormen Shai Halevi Donald Aingworth Dan Dooly Eric Hansen Susanne Albers Oliver Duschka Refael Hassin Eric Allender Martin Dyer Johan Hastad Rajeev Alur Ran El-Yaniv Lisa Hellerstein Andris Ambainis David Eppstein Monika Henzinger Amihood Amir Jeff Erickson Tom Henzinger Artur Andrzejak Kousha Etessami Jeremy Horwitz Boris Aronov Will Evans Russell Impagliazzo Sanjeev Arora Guy Even Piotr Indyk Amotz Barnoy Ron Fagin Sandra Irani Yair Bartal Michalis Faloutsos Ken Jackson Julien Basch Martin Farach-Colton David Johnson Saugata Basu Uri Feige John Jozwiak Bob Beals Joan Feigenbaum Bala Kalyandasundaram Paul Beame Stefan Felsner Ming-Yang Kao Steve Bellantoni Faith Fich Haim Kaplan Micahel Ben-Or Andy Fingerhut Bruce Kapron Josh Benaloh Paul Fischer Michael Kaufmann Charles Bennett Lance Fortnow Michael Kearns Marshall Bern Steve Fortune Sanjeev Khanna Nikolaj Bjorner Alan Frieze Samir Khuller Johannes Blomer Anna Gal Joe Kilian Avrim Blum Naveen Garg Valerie King Dan Boneh Bernd Gartner Philip Klein Andrei Broder Rosario Gennaro Spyros Kontogiannis Nader Bshouty Ashish Goel Gilad Koren Adam Buchsbaum Michel Goemans Dexter Kozen Lynn Burroughs Leslie Goldberg Dina Kravets Ran Canetti Paul Goldberg S. Ravi Kumar Pei Cao Oded Goldreich Eyal Kushilevitz Moses Charikar John Gray Stephen Kwek Chandra Chekuri Dan Greene Larry Larmore Yi-Jen Chiang -

Turing's Influence on Programming — Book Extract from “The Dawn of Software Engineering: from Turing to Dijkstra”
Turing's Influence on Programming | Book extract from \The Dawn of Software Engineering: from Turing to Dijkstra" Edgar G. Daylight∗ Eindhoven University of Technology, The Netherlands [email protected] Abstract Turing's involvement with computer building was popularized in the 1970s and later. Most notable are the books by Brian Randell (1973), Andrew Hodges (1983), and Martin Davis (2000). A central question is whether John von Neumann was influenced by Turing's 1936 paper when he helped build the EDVAC machine, even though he never cited Turing's work. This question remains unsettled up till this day. As remarked by Charles Petzold, one standard history barely mentions Turing, while the other, written by a logician, makes Turing a key player. Contrast these observations then with the fact that Turing's 1936 paper was cited and heavily discussed in 1959 among computer programmers. In 1966, the first Turing award was given to a programmer, not a computer builder, as were several subsequent Turing awards. An historical investigation of Turing's influence on computing, presented here, shows that Turing's 1936 notion of universality became increasingly relevant among programmers during the 1950s. The central thesis of this paper states that Turing's in- fluence was felt more in programming after his death than in computer building during the 1940s. 1 Introduction Many people today are led to believe that Turing is the father of the computer, the father of our digital society, as also the following praise for Martin Davis's bestseller The Universal Computer: The Road from Leibniz to Turing1 suggests: At last, a book about the origin of the computer that goes to the heart of the story: the human struggle for logic and truth. -

Cryptography: DH And
1 ì Key Exchange Secure Software Systems Fall 2018 2 Challenge – Exchanging Keys & & − 1 6(6 − 1) !"#ℎ%&'() = = = 15 & 2 2 The more parties in communication, ! $ the more keys that need to be securely exchanged Do we have to use out-of-band " # methods? (e.g., phone?) % Secure Software Systems Fall 2018 3 Key Exchange ì Insecure communica-ons ì Alice and Bob agree on a channel shared secret (“key”) that ì Eve can see everything! Eve doesn’t know ì Despite Eve seeing everything! ! " (alice) (bob) # (eve) Secure Software Systems Fall 2018 Whitfield Diffie and Martin Hellman, 4 “New directions in cryptography,” in IEEE Transactions on Information Theory, vol. 22, no. 6, Nov 1976. Proposed public key cryptography. Diffie-Hellman key exchange. Secure Software Systems Fall 2018 5 Diffie-Hellman Color Analogy (1) It’s easy to mix two colors: + = (2) Mixing two or more colors in a different order results in + + = the same color: + + = (3) Mixing colors is one-way (Impossible to determine which colors went in to produce final result) https://www.crypto101.io/ Secure Software Systems Fall 2018 6 Diffie-Hellman Color Analogy ! # " (alice) (eve) (bob) + + $ $ = = Mix Mix (1) Start with public color ▇ – share across network (2) Alice picks secret color ▇ and mixes it to get ▇ (3) Bob picks secret color ▇ and mixes it to get ▇ Secure Software Systems Fall 2018 7 Diffie-Hellman Color Analogy ! # " (alice) (eve) (bob) $ $ Mix Mix = = Eve can’t calculate ▇ !! (secret keys were never shared) (4) Alice and Bob exchange their mixed colors (▇,▇) (5) Eve will -

Nanorobot Construction Crews
Nanorobot Construction Crews Jaeseung Jeong, Ph.D Department of Bio and Brain engineering, KAIST Nanorobotics • Nanorobotics is the technology of creating machines or robots atltthit or close to the microscopi c scal lfe of a nanomet res (10-9 metres). More specifically, nanorobotics refers to the still largely ‘hypothetical’ nanotechnology engineering discipline of designing and building nanorobots. • Nanorobots ((,,nanobots, nanoids, nanites or nanonites ) would be typically devices ranging in size from 0.1-10 micrometers and constructed of nanoscale or molecular components. As no artificial non-biological nanorobots have yet been created, they remain a ‘hypothetical’ concept. • Another definition sometimes used is a robot which allows precision interactions with nanoscale objects , or can manipulate with nanoscale resolution. • Followingggpp this definition even a large apparatus such as an atomic force microscope can be considered a nanorobotic instrument when configured to perform nanomanipulation. • Also, macroscalble robots or mi crorob ots which can move wi th nanoscale precision can also be considered nanorobots. The T-1000 in Terminator 2: Judggyment Day • Since nanorobots would be microscopic in size , it would probably be necessary for very large numbers of them to work together to perform microscopic and macroscopic tasks. • These nanorobot swarms are fdifound in many sci ence fi fitiction stories, such as The T-1000 in Terminator 2: Judgment Day, nanomachine i n Meta l G ear So lid. • The word "nanobot" (also "nanite",,g, "nanogene", or "nanoant") is often used to indicate this fictional context and is a n info rma l o r eve n pejo rat ive term to refer to the engineering concept of nanorobots. -

Magnetic RSA
Magnetic RSA Rémi Géraud-Stewart1;2 and David Naccache2 1 QPSI, Qualcomm Technologies Incorporated, USA [email protected] 2 ÉNS (DI), Information Security Group CNRS, PSL Research University, 75005, Paris, France [email protected] Abstract. In a recent paper Géraud-Stewart and Naccache [GSN21] (GSN) described an non-interactive process allowing a prover P to con- vince a verifier V that a modulus n is the product of two randomly generated primes (p; q) of about the same size. A heuristic argument conjectures that P cannot control p; q to make n easy to factor. GSN’s protocol relies upon elementary number-theoretic properties and can be implemented efficiently using very few operations. This contrasts with state-of-the-art zero-knowledge protocols for RSA modulus proper generation assessment. This paper proposes an alternative process applicable in settings where P co-generates a modulus n “ p1q1p2q2 with a certification authority V. If P honestly cooperates with V, then V will only learn the sub-products n1 “ p1q1 and n2 “ p2q2. A heuristic argument conjectures that at least two of the factors of n are beyond P’s control. This makes n appropriate for cryptographic use provided that at least one party (of P and V) is honest. This heuristic argument calls for further cryptanalysis. 1 Introduction Several cryptographic protocols rely on the assumption that an integer n “ pq is hard to factor. This includes for instance RSA [RSA78], Rabin [Rab79], Paillier [Pai99] or Fiat–Shamir [FS86]. One way to ascertain that n is such a product is to generate it oneself; however, this becomes a concern when n is provided by a third-party. -

Fall 2016 Dear Electrical Engineering Alumni and Friends, This Past
ABBAS EL GAMAL Fortinet Founders Chair of the Department of Electrical Engineering Hitachi America Professor Fall 2016 Dear Electrical Engineering Alumni and Friends, This past academic year was another very successful one for the department. We made great progress toward implementing the vision of our strategic plan (EE in the 21st Century, or EE21 for short), which I outlined in my letter to you last year. I am also proud to share some of the exciting research in the department and the significant recognitions our faculty have received. I will first briefly describe the progress we have made toward implementing our EE21 plan. Faculty hiring. The top priority in our strategic plan is hiring faculty with complementary vision and expertise and who enhance our faculty diversity. This past academic year, we conducted a junior faculty broad area search and participated in a School of Engineering wide search in the area of robotics. I am happy to report that Mary Wootters joined our faculty in September as an assistant professor jointly with Computer Science. Mary’s research focuses on applying probability to coding theory, signal processing, and randomized algorithms. She also explores quantum information theory and complexity theory. Mary was previously an NSF postdoctoral fellow in the CS department at Carnegie Mellon University. The robotics search yielded two top candidates. I will report on the final results of this search in my next year’s letter. Reinventing the undergraduate curriculum. We continue to innovate our undergraduate curriculum, introducing two new, exciting project-oriented courses: EE107: Embedded Networked Systems and EE267: Virtual Reality.