Turing's Influence on Programming — Book Extract from “The Dawn of Software Engineering: from Turing to Dijkstra”
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Elementary Functions: Towards Automatically Generated, Efficient
Elementary functions : towards automatically generated, efficient, and vectorizable implementations Hugues De Lassus Saint-Genies To cite this version: Hugues De Lassus Saint-Genies. Elementary functions : towards automatically generated, efficient, and vectorizable implementations. Other [cs.OH]. Université de Perpignan, 2018. English. NNT : 2018PERP0010. tel-01841424 HAL Id: tel-01841424 https://tel.archives-ouvertes.fr/tel-01841424 Submitted on 17 Jul 2018 HAL is a multi-disciplinary open access L’archive ouverte pluridisciplinaire HAL, est archive for the deposit and dissemination of sci- destinée au dépôt et à la diffusion de documents entific research documents, whether they are pub- scientifiques de niveau recherche, publiés ou non, lished or not. The documents may come from émanant des établissements d’enseignement et de teaching and research institutions in France or recherche français ou étrangers, des laboratoires abroad, or from public or private research centers. publics ou privés. Délivré par l’Université de Perpignan Via Domitia Préparée au sein de l’école doctorale 305 – Énergie et Environnement Et de l’unité de recherche DALI – LIRMM – CNRS UMR 5506 Spécialité: Informatique Présentée par Hugues de Lassus Saint-Geniès [email protected] Elementary functions: towards automatically generated, efficient, and vectorizable implementations Version soumise aux rapporteurs. Jury composé de : M. Florent de Dinechin Pr. INSA Lyon Rapporteur Mme Fabienne Jézéquel MC, HDR UParis 2 Rapporteur M. Marc Daumas Pr. UPVD Examinateur M. Lionel Lacassagne Pr. UParis 6 Examinateur M. Daniel Menard Pr. INSA Rennes Examinateur M. Éric Petit Ph.D. Intel Examinateur M. David Defour MC, HDR UPVD Directeur M. Guillaume Revy MC UPVD Codirecteur À la mémoire de ma grand-mère Françoise Lapergue et de Jos Perrot, marin-pêcheur bigouden. -

Edsger Dijkstra: the Man Who Carried Computer Science on His Shoulders
INFERENCE / Vol. 5, No. 3 Edsger Dijkstra The Man Who Carried Computer Science on His Shoulders Krzysztof Apt s it turned out, the train I had taken from dsger dijkstra was born in Rotterdam in 1930. Nijmegen to Eindhoven arrived late. To make He described his father, at one time the president matters worse, I was then unable to find the right of the Dutch Chemical Society, as “an excellent Aoffice in the university building. When I eventually arrived Echemist,” and his mother as “a brilliant mathematician for my appointment, I was more than half an hour behind who had no job.”1 In 1948, Dijkstra achieved remarkable schedule. The professor completely ignored my profuse results when he completed secondary school at the famous apologies and proceeded to take a full hour for the meet- Erasmiaans Gymnasium in Rotterdam. His school diploma ing. It was the first time I met Edsger Wybe Dijkstra. shows that he earned the highest possible grade in no less At the time of our meeting in 1975, Dijkstra was 45 than six out of thirteen subjects. He then enrolled at the years old. The most prestigious award in computer sci- University of Leiden to study physics. ence, the ACM Turing Award, had been conferred on In September 1951, Dijkstra’s father suggested he attend him three years earlier. Almost twenty years his junior, I a three-week course on programming in Cambridge. It knew very little about the field—I had only learned what turned out to be an idea with far-reaching consequences. a flowchart was a couple of weeks earlier. -

Computer History – the Pitfalls of Past Futures
Research Collection Working Paper Computer history – The pitfalls of past futures Author(s): Gugerli, David; Zetti, Daniela Publication Date: 2019 Permanent Link: https://doi.org/10.3929/ethz-b-000385896 Rights / License: In Copyright - Non-Commercial Use Permitted This page was generated automatically upon download from the ETH Zurich Research Collection. For more information please consult the Terms of use. ETH Library TECHNIKGESCHICHTE DAVID GUGERLI DANIELA ZETTI COMPUTER HISTORY – THE PITFALLS OF PAST FUTURES PREPRINTS ZUR KULTURGESCHICHTE DER TECHNIK // 2019 #33 WWW.TG.ETHZ.CH © BEI DEN AUTOREN Gugerli, Zetti/Computer History Preprints zur Kulturgeschichte der Technik #33 Abstract The historicization of the computer in the second half of the 20th century can be understood as the effect of the inevitable changes in both its technological and narrative development. What interests us is how past futures and therefore history were stabilized. The development, operation, and implementation of machines and programs gave rise to a historicity of the field of computing. Whenever actors have been grouped into communities – for example, into industrial and academic developer communities – new orderings have been constructed historically. Such orderings depend on the ability to refer to archival and published documents and to develop new narratives based on them. Professional historians are particularly at home in these waters – and nevertheless can disappear into the whirlpool of digital prehistory. Toward the end of the 1980s, the first critical review of the literature on the history of computers thus offered several programmatic suggestions. It is one of the peculiar coincidences of history that the future should rear its head again just when the history of computers was flourishing as a result of massive methodological and conceptual input. -

Advancing Automatic Programming: Regeneration, Meta-Circularity, and Two-Sided Interfaces
SOFTNET 2019 Advancing Automatic Programming: Regeneration, Meta-circularity, and Two-Sided Interfaces HERWIGMANNAERT NOVEMBER 2 7 , 2 0 1 9 • Automatic Programming • Toward Automatic Regeneration • Creating Meta-Circular Regeneration • On Meta-Programming Interfaces ADVANCING AUTOMATIC PROGRAMMING • Concluding Facts and Thoughts Overview • Questions and Discussion • Automatic Programming • Concept and Trends • Remaining Challenges • Toward Automatic Regeneration ADVANCING AUTOMATIC PROGRAMMING • Creating Meta-Circular Regeneration • On Meta-Programming Interfaces Overview • Concluding Facts and Thoughts • Questions and Discussion Automatic Programming • Automatic programming: • The act of automatically generating source code from a model or template • Sometimes distinguished from code generation, as performed by a compiler • Has always been a euphemism for programming in a higher-level language than was then available to the programmer [David Parnas] • Also referred to a generative or meta-programming • To manufacture software components in an automated way • It is as old as programming itself: System.out.println(“Hello world.”); System.out.println(“System.out.println(\“Hello world.\”);”); The Need for Automatic Programming • Goal is and has always been to improve programmer productivity • In general, to manufacture software components in an automated way, in the same way as automation in the industrial revolution, would: • Increase programming productivity • Consolidate programming knowledge • Eliminate human programming errors • Such -

The Turing Approach Vs. Lovelace Approach
Connecting the Humanities and the Sciences: Part 2. Two Schools of Thought: The Turing Approach vs. The Lovelace Approach* Walter Isaacson, The Jefferson Lecture, National Endowment for the Humanities, May 12, 2014 That brings us to another historical figure, not nearly as famous, but perhaps she should be: Ada Byron, the Countess of Lovelace, often credited with being, in the 1840s, the first computer programmer. The only legitimate child of the poet Lord Byron, Ada inherited her father’s romantic spirit, a trait that her mother tried to temper by having her tutored in math, as if it were an antidote to poetic imagination. When Ada, at age five, showed a preference for geography, Lady Byron ordered that the subject be replaced by additional arithmetic lessons, and her governess soon proudly reported, “she adds up sums of five or six rows of figures with accuracy.” Despite these efforts, Ada developed some of her father’s propensities. She had an affair as a young teenager with one of her tutors, and when they were caught and the tutor banished, Ada tried to run away from home to be with him. She was a romantic as well as a rationalist. The resulting combination produced in Ada a love for what she took to calling “poetical science,” which linked her rebellious imagination to an enchantment with numbers. For many people, including her father, the rarefied sensibilities of the Romantic Era clashed with the technological excitement of the Industrial Revolution. Lord Byron was a Luddite. Seriously. In his maiden and only speech to the House of Lords, he defended the followers of Nedd Ludd who were rampaging against mechanical weaving machines that were putting artisans out of work. -
CODEBREAKING Suggested Reading List (Can Also Be Viewed Online at Good Reads)
MARSHALL LEGACY SERIES: CODEBREAKING Suggested Reading List (Can also be viewed online at Good Reads) NON-FICTION • Aldrich, Richard. Intelligence and the War against Japan. Cambridge: Cambridge University Press, 2000. • Allen, Robert. The Cryptogram Challenge: Over 150 Codes to Crack and Ciphers to Break. Philadelphia: Running Press, 2005 • Briggs, Asa. Secret Days Code-breaking in Bletchley Park. Barnsley: Frontline Books, 2011 • Budiansky, Stephen. Battle of Wits: The Complete Story of Codebreaking in World War Two. New York: Free Press, 2000. • Churchhouse, Robert. Codes and Ciphers: Julius Caesar, the Enigma, and the Internet. Cambridge: Cambridge University Press, 2001. • Clark, Ronald W. The Man Who Broke Purple. London: Weidenfeld and Nicholson, 1977. • Drea, Edward J. MacArthur's Ultra: Codebreaking and the War Against Japan, 1942-1945. Kansas: University of Kansas Press, 1992. • Fisher-Alaniz, Karen. Breaking the Code: A Father's Secret, a Daughter's Journey, and the Question That Changed Everything. Naperville, IL: Sourcebooks, 2011. • Friedman, William and Elizebeth Friedman. The Shakespearian Ciphers Examined. Cambridge: Cambridge University Press, 1957. • Gannon, James. Stealing Secrets, Telling Lies: How Spies and Codebreakers Helped Shape the Twentieth century. Washington, D.C.: Potomac Books, 2001. • Garrett, Paul. Making, Breaking Codes: Introduction to Cryptology. London: Pearson, 2000. • Hinsley, F. H. and Alan Stripp. Codebreakers: the inside story of Bletchley Park. Oxford: Oxford University Press, 1993. • Hodges, Andrew. Alan Turing: The Enigma. New York: Walker and Company, 2000. • Kahn, David. Seizing The Enigma: The Race to Break the German U-boat Codes, 1939-1943. New York: Barnes and Noble Books, 2001. • Kahn, David. The Codebreakers: The Comprehensive History of Secret Communication from Ancient Times to the Internet. -

Reconfigurable Embedded Control Systems: Problems and Solutions
RECONFIGURABLE EMBEDDED CONTROL SYSTEMS: PROBLEMS AND SOLUTIONS By Dr.rer.nat.Habil. Mohamed Khalgui ⃝c Copyright by Dr.rer.nat.Habil. Mohamed Khalgui, 2012 v Martin Luther University, Germany Research Manuscript for Habilitation Diploma in Computer Science 1. Reviewer: Prof.Dr. Hans-Michael Hanisch, Martin Luther University, Germany, 2. Reviewer: Prof.Dr. Georg Frey, Saarland University, Germany, 3. Reviewer: Prof.Dr. Wolf Zimmermann, Martin Luther University, Germany, Day of the defense: Monday January 23rd 2012, Table of Contents Table of Contents vi English Abstract x German Abstract xi English Keywords xii German Keywords xiii Acknowledgements xiv Dedicate xv 1 General Introduction 1 2 Embedded Architectures: Overview on Hardware and Operating Systems 3 2.1 Embedded Hardware Components . 3 2.1.1 Microcontrollers . 3 2.1.2 Digital Signal Processors (DSP): . 4 2.1.3 System on Chip (SoC): . 5 2.1.4 Programmable Logic Controllers (PLC): . 6 2.2 Real-Time Embedded Operating Systems (RTOS) . 8 2.2.1 QNX . 9 2.2.2 RTLinux . 9 2.2.3 VxWorks . 9 2.2.4 Windows CE . 10 2.3 Known Embedded Software Solutions . 11 2.3.1 Simple Control Loop . 12 2.3.2 Interrupt Controlled System . 12 2.3.3 Cooperative Multitasking . 12 2.3.4 Preemptive Multitasking or Multi-Threading . 12 2.3.5 Microkernels . 13 2.3.6 Monolithic Kernels . 13 2.3.7 Additional Software Components: . 13 2.4 Conclusion . 14 3 Embedded Systems: Overview on Software Components 15 3.1 Basic Concepts of Components . 15 3.2 Architecture Description Languages . 17 3.2.1 Acme Language . -
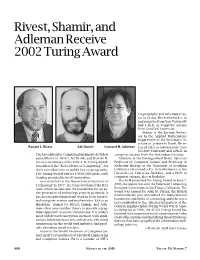
Rivest, Shamir, and Adleman Receive 2002 Turing Award, Volume 50
Rivest, Shamir, and Adleman Receive 2002 Turing Award Cryptography and Information Se- curity Group. He received a B.A. in mathematics from Yale University and a Ph.D. in computer science from Stanford University. Shamir is the Borman Profes- sor in the Applied Mathematics Department of the Weizmann In- stitute of Science in Israel. He re- Ronald L. Rivest Adi Shamir Leonard M. Adleman ceived a B.S. in mathematics from Tel Aviv University and a Ph.D. in The Association for Computing Machinery (ACM) has computer science from the Weizmann Institute. named RONALD L. RIVEST, ADI SHAMIR, and LEONARD M. Adleman is the Distinguished Henry Salvatori ADLEMAN as winners of the 2002 A. M. Turing Award, Professor of Computer Science and Professor of considered the “Nobel Prize of Computing”, for Molecular Biology at the University of Southern their contributions to public key cryptography. California. He earned a B.S. in mathematics at the The Turing Award carries a $100,000 prize, with University of California, Berkeley, and a Ph.D. in funding provided by Intel Corporation. computer science, also at Berkeley. As researchers at the Massachusetts Institute of The ACM presented the Turing Award on June 7, Technology in 1977, the team developed the RSA 2003, in conjunction with the Federated Computing code, which has become the foundation for an en- Research Conference in San Diego, California. The tire generation of technology security products. It award was named for Alan M. Turing, the British mathematician who articulated the mathematical has also inspired important work in both theoret- foundation and limits of computing and who was a ical computer science and mathematics. -

19 Theory of Computation
19 Theory of Computation "You are about to embark on the study of a fascinating and important subject: the theory of computation. It com- prises the fundamental mathematical properties of computer hardware, software, and certain applications thereof. In studying this subject we seek to determine what can and cannot be computed, how quickly, with how much memory, and on which type of computational model." - Michael Sipser, "Introduction to the Theory of Computation", one of the driest computer science textbooks ever In which we go back to the basics with arcane, boring, and irrelevant set theory and counting. This week’s material is made challenging by two orthogonal issues. There’s a whole bunch of stuff to cover, and 95% of it isn’t the least bit interesting to a physical scientist. Nevertheless, being the starry-eyed optimist that I am, I’ll forge ahead through the mountainous bulk of knowledge. In other words, expect these notes to be long! But skim when necessary; if you look at the homework first (and haven’t entirely forgotten the lectures), you should be able to pick out the important parts. I understand if this type of stuff isn’t exactly your cup of tea, but bear with me while you can. In some sense, most of what we refer to as computer science isn’t computer science at all, any more than what an accountant does is math. Sure, modern economics takes some crazy hardcore theory to make it all work, but un- derlying the whole thing is a solid layer of applications and industrial moolah. -

Welcome to AI Matters 5(1)
AI MATTERS, VOLUME 5, ISSUE 1 5(1) 2019 Welcome to AI Matters 5(1) Amy McGovern, co-editor (University of Oklahoma; [email protected]) Iolanda Leite, co-editor (Royal Institute of Technology (KTH); [email protected]) DOI: 10.1145/3320254.3320255 Issue overview receiving the 2018 ACM A.M. Turing Award! Welcome to the first issue of the fifth vol- ume of the AI Matters Newsletter! This issue opens with some news on a new SIGAI Stu- Submit to AI Matters! dent Travel Scholarship where we aim to en- Thanks for reading! Don’t forget to send courage students from traditionally underrep- your ideas and future submissions to AI resented geographic locations to apply and at- Matters! We’re accepting articles and an- tend SIGAI supported events. We also sum- nouncements now for the next issue. De- marize the fourth AAAI/ACM SIGAI Job Fair, tails on the submission process are avail- which continues to grow with the increasing able at http://sigai.acm.org/aimatters. popularity of AI. In our interview series, Marion Neumann interviews Tom Dietterich, an Emer- itus Professor at Oregon State University and one of the pioneers in Machine Learning. Amy McGovern is co- In our regular columns, we have a summary editor of AI Matters. She of recent and upcoming AI conferences and is a Professor of com- events from Michael Rovatsos. Our educa- puter science at the Uni- tional column this issue is dedicated to “biduc- versity of Oklahoma and tive computing”, one of Prolog’s most distinc- an adjunct Professor of tive features. -

YANLI: a Powerful Natural Language Front-End Tool
AI Magazine Volume 8 Number 1 (1987) (© AAAI) John C. Glasgow I1 YANLI: A Powerful Natural Language Front-End Tool An important issue in achieving acceptance of computer sys- Since first proposed by Woods (1970), ATNs have be- tems used by the nonprogramming community is the ability come a popular method of defining grammars for natural to communicate with these systems in natural language. Of- language parsing programs. This popularity is due to the ten, a great deal of time in the design of any such system is flexibility with which ATNs can be applied to hierarchically devoted to the natural language front end. An obvious way to describable phenomenon and to their power, which is that of simplify this task is to provide a portable natural language a universal Turing machine. As discussed later, a grammar front-end tool or facility that is sophisticated enough to allow in the form of an ATN (written in LISP) is more informative for a reasonable variety of input; allows modification; and, than a grammar in Backus-Naur notation. As an example, yet, is easy to use. This paper describes such a tool that is the first few lines of a grammar for an English sentence writ- based on augmented transition networks (ATNs). It allows ten in Backus-Naur notation might look like the following: for user input to be in sentence or nonsentence form or both, provides a detailed parse tree that the user can access, and sentence : := [subject] predicate also provides the facility to generate responses and save in- subject ::= noun-group formation. -

An Early Program Proof by Alan Turing F
An Early Program Proof by Alan Turing F. L. MORRIS AND C. B. JONES The paper reproduces, with typographical corrections and comments, a 7 949 paper by Alan Turing that foreshadows much subsequent work in program proving. Categories and Subject Descriptors: 0.2.4 [Software Engineeringj- correctness proofs; F.3.1 [Logics and Meanings of Programs]-assertions; K.2 [History of Computing]-software General Terms: Verification Additional Key Words and Phrases: A. M. Turing Introduction The standard references for work on program proofs b) have been omitted in the commentary, and ten attribute the early statement of direction to John other identifiers are written incorrectly. It would ap- McCarthy (e.g., McCarthy 1963); the first workable pear to be worth correcting these errors and com- methods to Peter Naur (1966) and Robert Floyd menting on the proof from the viewpoint of subse- (1967); and the provision of more formal systems to quent work on program proofs. C. A. R. Hoare (1969) and Edsger Dijkstra (1976). The Turing delivered this paper in June 1949, at the early papers of some of the computing pioneers, how- inaugural conference of the EDSAC, the computer at ever, show an awareness of the need for proofs of Cambridge University built under the direction of program correctness and even present workable meth- Maurice V. Wilkes. Turing had been writing programs ods (e.g., Goldstine and von Neumann 1947; Turing for an electronic computer since the end of 1945-at 1949). first for the proposed ACE, the computer project at the The 1949 paper by Alan M.