Windirstat - Directory Statistics Copyright (C) 2003-2005 Bernhard Seifert
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

What Is UNIX? the Directory Structure Basic Commands Find
What is UNIX? UNIX is an operating system like Windows on our computers. By operating system, we mean the suite of programs which make the computer work. It is a stable, multi-user, multi-tasking system for servers, desktops and laptops. The Directory Structure All the files are grouped together in the directory structure. The file-system is arranged in a hierarchical structure, like an inverted tree. The top of the hierarchy is traditionally called root (written as a slash / ) Basic commands When you first login, your current working directory is your home directory. In UNIX (.) means the current directory and (..) means the parent of the current directory. find command The find command is used to locate files on a Unix or Linux system. find will search any set of directories you specify for files that match the supplied search criteria. The syntax looks like this: find where-to-look criteria what-to-do All arguments to find are optional, and there are defaults for all parts. where-to-look defaults to . (that is, the current working directory), criteria defaults to none (that is, select all files), and what-to-do (known as the find action) defaults to ‑print (that is, display the names of found files to standard output). Examples: find . –name *.txt (finds all the files ending with txt in current directory and subdirectories) find . -mtime 1 (find all the files modified exact 1 day) find . -mtime -1 (find all the files modified less than 1 day) find . -mtime +1 (find all the files modified more than 1 day) find . -

CS101 Lecture 8
What is a program? What is a “Window Manager” ? What is a “GUI” ? How do you navigate the Unix directory tree? What is a wildcard? Readings: See CCSO’s Unix pages and 8-2 Applications Unix Engineering Workstations UNIX- operating system / C- programming language / Matlab Facilitate machine independent program development Computer program(software): a sequence of instructions that tells the computer what to do. A program takes raw data as input and produces information as output. System Software: • Operating Systems Unix,Windows,MacOS,VM/CMS,... • Editor Programs gedit, pico, vi Applications Software: • Translators and Interpreters gcc--gnu c compiler matlab – interpreter • User created Programs!!! 8-4 X-windows-a Window Manager and GUI(Graphical User Interface) Click Applications and follow the menus or click on an icon to run a program. Click Terminal to produce a command line interface. When the following slides refer to Unix commands it is assumed that these are entered on the command line that begins with the symbol “>” (prompt symbol). Data, information, computer instructions, etc. are saved in secondary storage (auxiliary storage) in files. Files are collected or organized in directories. Each user on a multi-user system has his/her own home directory. In Unix users and system administrators organize files and directories in a hierarchical tree. secondary storage Home Directory When a user first logs in on a computer, the user will be “in” the users home directory. To find the name of the directory type > pwd (this is an acronym for print working directory) So the user is in the directory “gambill” The string “/home/gambill” is called a path. -

Trees, Binary Search Trees, Heaps & Applications Dr. Chris Bourke
Trees Trees, Binary Search Trees, Heaps & Applications Dr. Chris Bourke Department of Computer Science & Engineering University of Nebraska|Lincoln Lincoln, NE 68588, USA [email protected] http://cse.unl.edu/~cbourke 2015/01/31 21:05:31 Abstract These are lecture notes used in CSCE 156 (Computer Science II), CSCE 235 (Dis- crete Structures) and CSCE 310 (Data Structures & Algorithms) at the University of Nebraska|Lincoln. This work is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License 1 Contents I Trees4 1 Introduction4 2 Definitions & Terminology5 3 Tree Traversal7 3.1 Preorder Traversal................................7 3.2 Inorder Traversal.................................7 3.3 Postorder Traversal................................7 3.4 Breadth-First Search Traversal..........................8 3.5 Implementations & Data Structures.......................8 3.5.1 Preorder Implementations........................8 3.5.2 Inorder Implementation.........................9 3.5.3 Postorder Implementation........................ 10 3.5.4 BFS Implementation........................... 12 3.5.5 Tree Walk Implementations....................... 12 3.6 Operations..................................... 12 4 Binary Search Trees 14 4.1 Basic Operations................................. 15 5 Balanced Binary Search Trees 17 5.1 2-3 Trees...................................... 17 5.2 AVL Trees..................................... 17 5.3 Red-Black Trees.................................. 19 6 Optimal Binary Search Trees 19 7 Heaps 19 -
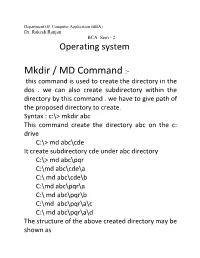
Mkdir / MD Command :- This Command Is Used to Create the Directory in the Dos
Department Of Computer Application (BBA) Dr. Rakesh Ranjan BCA Sem - 2 Operating system Mkdir / MD Command :- this command is used to create the directory in the dos . we can also create subdirectory within the directory by this command . we have to give path of the proposed directory to create. Syntax : c:\> mkdir abc This command create the directory abc on the c: drive C:\> md abc\cde It create subdirectory cde under abc directory C:\> md abc\pqr C:\md abc\cde\a C:\ md abc\cde\b C:\md abc\pqr\a C:\ md abc\pqr\b C:\md abc\pqr\a\c C:\ md abc\pqr\a\d The structure of the above created directory may be shown as ABC CDE PQR A B A B C D Tree command :- this command in dos is used to display the structure of the directory and subdirectory in DOS. C:\> tree This command display the structure of c: Drive C:\> tree abc It display the structure of abc directory on the c: drive Means that tree command display the directory structure of the given directory of given path. RD Command :- RD stands for Remove directory command . this command is used to remove the directory from the disk . it should be noted that directory which to be removed must be empty otherwise , can not be removed . Syntax :- c:\ rd abc It display error because , abc is not empty C:\ rd abc\cde It also display error because cde is not empty C:\ rd abc\cde\a It works and a directory will remove from the disk C:\ rd abc\cde\b It will remove the b directory C:\rd abc\cde It will remove the cde directory because cde is now empty. -

UNIX (Solaris/Linux) Quick Reference Card Logging in Directory Commands at the Login: Prompt, Enter Your Username
UNIX (Solaris/Linux) QUICK REFERENCE CARD Logging In Directory Commands At the Login: prompt, enter your username. At the Password: prompt, enter ls Lists files in current directory your system password. Linux is case-sensitive, so enter upper and lower case ls -l Long listing of files letters as required for your username, password and commands. ls -a List all files, including hidden files ls -lat Long listing of all files sorted by last Exiting or Logging Out modification time. ls wcp List all files matching the wildcard Enter logout and press <Enter> or type <Ctrl>-D. pattern Changing your Password ls dn List files in the directory dn tree List files in tree format Type passwd at the command prompt. Type in your old password, then your new cd dn Change current directory to dn password, then re-enter your new password for verification. If the new password cd pub Changes to subdirectory “pub” is verified, your password will be changed. Many systems age passwords; this cd .. Changes to next higher level directory forces users to change their passwords at predetermined intervals. (previous directory) cd / Changes to the root directory Changing your MS Network Password cd Changes to the users home directory cd /usr/xx Changes to the subdirectory “xx” in the Some servers maintain a second password exclusively for use with Microsoft windows directory “usr” networking, allowing you to mount your home directory as a Network Drive. mkdir dn Makes a new directory named dn Type smbpasswd at the command prompt. Type in your old SMB passwword, rmdir dn Removes the directory dn (the then your new password, then re-enter your new password for verification. -

System Analysis and Tuning Guide System Analysis and Tuning Guide SUSE Linux Enterprise Server 15 SP1
SUSE Linux Enterprise Server 15 SP1 System Analysis and Tuning Guide System Analysis and Tuning Guide SUSE Linux Enterprise Server 15 SP1 An administrator's guide for problem detection, resolution and optimization. Find how to inspect and optimize your system by means of monitoring tools and how to eciently manage resources. Also contains an overview of common problems and solutions and of additional help and documentation resources. Publication Date: September 24, 2021 SUSE LLC 1800 South Novell Place Provo, UT 84606 USA https://documentation.suse.com Copyright © 2006– 2021 SUSE LLC and contributors. All rights reserved. Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.2 or (at your option) version 1.3; with the Invariant Section being this copyright notice and license. A copy of the license version 1.2 is included in the section entitled “GNU Free Documentation License”. For SUSE trademarks, see https://www.suse.com/company/legal/ . All other third-party trademarks are the property of their respective owners. Trademark symbols (®, ™ etc.) denote trademarks of SUSE and its aliates. Asterisks (*) denote third-party trademarks. All information found in this book has been compiled with utmost attention to detail. However, this does not guarantee complete accuracy. Neither SUSE LLC, its aliates, the authors nor the translators shall be held liable for possible errors or the consequences thereof. Contents About This Guide xii 1 Available Documentation xiii -
The Substitution Model
The Substitution Model Nate Foster Spring 2018 Review Previously in 3110: simple interpreter for expression language • abstract syntax tree (AST) • evaluation based on single steps • parser and lexer (in lab) Today: • Formal syntax: BNF • Formal dynamic semantics: small-step, substitution model • Formal static semantics Substitution (* [subst e v x] is e{v/x}, that is, * [e] with [v] substituted for [x]. *) let rec subst e v x = match e with | Var y -> if x=y then v else e | Int n -> Int n | Add(el,er) -> Add(subst el v x, subst er v x) | Let(y,ebind,ebody) -> let ebind' = subst ebind v x in if x=y then Let(y, ebind', ebody) else Let(y, ebind', subst ebody v x) Step let rec step = function | Int n -> failwith "Does not step" | Add(Int n1, Int n2) -> Int (n1 + n2) | Add(Int n1, e2) -> Add (Int n1, step e2) | Add(e1, e2) -> Add (step e1, e2) | Var _ -> failwith "Unbound variable" | Let(x, Int n, e2) -> subst e2 (Int n) x | Let(x, e1, e2) -> Let (x, step e1, e2) FORMAL SYNTAX Abstract syntax of expression lang. e ::= x | i | e1+e2 | let x = e1 in e2 e, x, i: meta-variables that stand for pieces of syntax • e: expressions • x: program variables, aka identifiers • i: integer constants, aka literals ::= and | are meta-syntax: used to describe syntax of language notation is called Backus-Naur Form (BNF) from its use by Backus and Naur in their definition of Algol-60 Backus and Naur John Backus (1924-2007) ACM Turing Award Winner 1977 “For profound, influential, and lasting contributions to the design of practical high-level programming systems” Peter Naur (1928-2016) ACM Turing Award Winner 2005 “For fundamental contributions to programming language design” Abstract syntax of expr. -

More General Naming a Substitution Model for Bindex Table of Contents
Substitution subst Bindex subst model Bindex environment model More general naming A substitution model for Bindex Theory of Programming Languages Computer Science Department Wellesley College Substitution subst Bindex subst model Bindex environment model Table of contents Substitution subst Bindex subst model Bindex environment model Substitution subst Bindex subst model Bindex environment model Substitution Renaming is a special case of a more general program form of • program manipulation called substitution. In substitution, all free occurrences of a variable name are • replaced by a given expression. For example, substituting (+ b c) for a in (* a a) yields (* (+ b c) (+ b c)). If we view expressions as trees, then substitution replaces • certain leaves (those with the specified name) by new subtrees. Substitution subst Bindex subst model Bindex environment model Substituting trees for trees For example, substituting the tree on the left for the one on the right yields the tree Substitution subst Bindex subst model Bindex environment model Preserving the “naming wiring structure” of expressions As in renaming, substitution must avoid variable capture to preserve the “naming wiring structure” of expressions. In particular, when substituting for a variable I, we will never • perform substitutions on I within the scope of a bind expression that binds I. For example, substituting (+ b c) for a in • (bind a (* a a) (- a 3)) yields: (bind a (* (+ b c) (+ b c)) (- a 3)) Here the free occurrences of a have been replaced by (+ b • c), but the bound occurrences have not been changed. Substitution subst Bindex subst model Bindex environment model Renaming to avoid variable capture Furthermore, bind-bound variables may be renamed to avoid variable capture • with free variables in the expression being substituted for the variable. -

List of MS-DOS Commands - Wikipedia, the Free Encyclopedia Page 1 of 25
List of MS-DOS commands - Wikipedia, the free encyclopedia Page 1 of 25 List of MS-DOS commands From Wikipedia, the free encyclopedia In the personal computer operating systems MS -DOS and PC DOS, a number of standard system commands were provided for common Contents tasks such as listing files on a disk or moving files. Some commands were built-in to the command interpreter, others existed as transient ■ 1 Resident and transient commands commands loaded into memory when required. ■ 2 Command line arguments Over the several generations of MS-DOS, ■ 3 Windows command prompt commands were added for the additional ■ 4 Commands functions of the operating system. In the current ■ 4.1 @ Microsoft Windows operating system a text- ■ 4.2 : mode command prompt window can still be ■ 4.3 ; used. Some DOS commands carry out functions ■ 4.4 /* equivalent to those in a UNIX system but ■ 4.5 ( ) always with differences in details of the ■ 4.6 append function. ■ 4.7 assign ■ 4.8 attrib ■ 4.9 backup and restore Resident and transient ■ 4.10 BASIC and BASICA commands ■ 4.11 call ■ 4.12 cd or chdir ■ 4.13 chcp The command interpreter for MS-DOS runs ■ 4.14 chkdsk when no application programs are running. ■ 4.15 choice When an application exits, if the command ■ 4.16 cls interpreter in memory was overwritten, MS- ■ 4.17 copy DOS will re-load it from disk. The command ■ 4.18 ctty interpreter is usually stored in a file called ■ 4.19 defrag "COMMAND.COM". Some commands are ■ 4.20 del or erase internal and built-into COMMAND.COM, ■ 4.21 deltree others are stored on disk in the same way as ■ 4.22 dir application programs. -

Command Line Interface (Shell)
Command Line Interface (Shell) 1 Organization of a computer system users applications graphical user shell interface (GUI) operating system hardware (or software acting like hardware: “virtual machine”) 2 Organization of a computer system Easier to use; users applications Not so easy to program with, interactive actions automate (click, drag, tap, …) graphical user shell interface (GUI) system calls operating system hardware (or software acting like hardware: “virtual machine”) 3 Organization of a computer system Easier to program users applications with and automate; Not so convenient to use (maybe) typed commands graphical user shell interface (GUI) system calls operating system hardware (or software acting like hardware: “virtual machine”) 4 Organization of a computer system users applications this class graphical user shell interface (GUI) operating system hardware (or software acting like hardware: “virtual machine”) 5 What is a Command Line Interface? • Interface: Means it is a way to interact with the Operating System. 6 What is a Command Line Interface? • Interface: Means it is a way to interact with the Operating System. • Command Line: Means you interact with it through typing commands at the keyboard. 7 What is a Command Line Interface? • Interface: Means it is a way to interact with the Operating System. • Command Line: Means you interact with it through typing commands at the keyboard. So a Command Line Interface (or a shell) is a program that lets you interact with the Operating System via the keyboard. 8 Why Use a Command Line Interface? A. In the old days, there was no choice 9 Why Use a Command Line Interface? A. -
2 Subst. Crim. L. § 13.2 (2D Ed.)
For Educational Use Only § 13.2. Accomplice liability-Acts and mental state, 2 Subst. Crim. L. § 13.2 (2d ed.) 2 Subst. Crim. L. § 13.2 (2d ed.) Substantive Criminal Law Current through the 2011 Update Wayne R. LaFaveao Part Two. General Principles Chapter 13. Parties; Liability for Conduct of Another § 13.2. Accomplice liability-Acts and mental state In the commission of each criminal offense there may be several persons or groups which play distinct roles before, during and after the offense. Collectively these persons or groups are termed the parties to the crime. The common law classification of parties to a felony consisted of four categories: (1) principal in the first degree; (2) principal in the second degree; (3) accessory before the fact; and (4) accessory after the fact. A much more modem approach to the entire subject of parties to crime is to abandon completely the old common law terminology and simply provide that a person is legally accountable for the conduct of another when he is an accomplice of the other person in the commission of the crime. Such is the view taken in the Model Penal Code, which provides that a person is an accomplice of another person in the commission of an offense if, with the purpose of promoting or facilitating the commission of the offense, he solicits the other person to commit it, or aids or agrees or attempts to aid the other person in planning or committing it, or (having a legal duty to prevent the crime) fails to make proper effort to prevent it. -
Ch 7 Using ATTRIB, SUBST, XCOPY, DOSKEY, and the Text Editor
Using ATTRIB, SUBST, XCOPY, DOSKEY, and the Text Editor Ch 7 1 Overview The purpose and function of file attributes will be explained. Ch 7 2 Overview Utility commands and programs will be used to manipulate files and subdirectories to make tasks at the command line easier to do. Ch 7 3 Overview This chapter will focus on the following commands and programs: ATTRIB XCOPY DOSKEY EDIT Ch 7 4 File Attributes and the ATTRIB Command Root directory keeps track of information about every file on a disk. Ch 7 5 File Attributes and the ATTRIB Command Each file in the directory has attributes. Ch 7 6 File Attributes and the ATTRIB Command Attributes represented by single letter: S - System attribute H - Hidden attribute R - Read-only attribute A - Archive attribute Ch 7 7 File Attributes and the ATTRIB Command NTFS file system: Has other attributes At command line only attributes can change with ATTRIB command are S, H, R, and A Ch 7 8 File Attributes and the ATTRIB Command ATTRIB command: Used to manipulate file attributes Ch 7 9 File Attributes and the ATTRIB Command ATTRIB command syntax: ATTRIB [+R | -R] [+A | -A] [+S | -S] [+H | -H] [[drive:] [path] filename] [/S [/D]] Ch 7 10 File Attributes and the ATTRIB Command Attributes most useful to set and unset: R - Read-only H - Hidden Ch 7 11 File Attributes and the ATTRIB Command The A attribute (archive bit) signals file has not been backed up. Ch 7 12 File Attributes and the ATTRIB Command XCOPY command can read the archive bit.