Learning Mysql
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Sydney 18 Våra Medlemmar
AZeelAnd.se UNDER A ZeeländskA vänskApsföreningen www.AustrAlien-ny DAustrAlisk A ny WN nr 4 / 2012 the sAints AustrAlien där och sverige regnskogen långt emellAn men möter revet ändå likA dykning på nyA ZeelAnd • NYHETER • samaRbETE mEd sTudiEfRämjaNdET • KaNgoRoo HoppET • LäsaRfRågoR Besök vänskApsföreningens nyA hemsidA på hemsidan hittar du senaste nytt om evenemang, nyheter, medlemsförmåner och tips. du kan läsa artiklar, reseskildringar och få information om working holiday, visum mm. www.AustrAlien-nyAZeelAnd.se Bli medlem i AustrAliskA nyA ZeeländskA vänskApsföreningen medlemsavgift 200:- kalenderår. förutom vår medlemstidning erhåller du en mängd rabatter hos företag och föreningar som vi samarbetar med. att bli medlem utvecklar och lönar sig! inbetalning till plusgiro konto 54 81 31-2. uppge namn, ev. medlemsnummer och e-postadress. 2 D WN UNDER Det sprakar från elden i kakelugnen och förs- ta adventsljuset är tänt när jag skriver denna ledare. Den första snön har redan fallit, det nal- kas mot jul och vi närmar oss ett nytt och spän- nande år. År 2012 har varit alldeles fantastiskt oRdföRaNdEN HaR oRdET 4 för egen del. Jag har börjat på ett nytt arbete som verksamhetsutvecklare hos Studiefrämjan- däR REgNsKogEN möTER REvET 5 det Bohuslän Norra med inriktning på musik och kultur. Vågar nog påstå att det är det mest inspirerande arbete KaNgoRoo HoppET 7 jag hittills haft. Inspirerande är också att just Studiefrämjandet och Vänskapsföreningen under hösten inlett ett samarbete som jag hoppas DykniNg på NYa ZEELaNd 8 ni kan ha mycket glädje och nytta av. Som vanligt går man omkring och längtar till vänner och platser på andra sidan jordklotet. -

Here Is a Printable
Ryan Leach is a skateboarder who grew up in Los Angeles and Ventura County. Like Belinda Carlisle and Lorna Doom, he graduated from Newbury Park High School. With Mor Fleisher-Leach he runs Spacecase Records. Leach’s interviews are available at Bored Out (http://boredout305.tumblr.com/). Razorcake is a bi-monthly, Los Angeles-based fanzine that provides consistent coverage of do-it-yourself punk culture. We believe in positive, progressive, community-friendly DIY punk, and are the only bona fide 501(c)(3) non-profit music magazine in America. We do our part. An Oral History of The Gun Club originally appeared in Razorcake #29, released in December 2005/January 2006. Original artwork and layout by Todd Taylor. Photos by Edward Colver, Gary Leonard and Romi Mori. Cover photo by Edward Colver. Zine design by Marcos Siref. Printing courtesy of Razorcake Press, Razorcake.org he Gun Club is one of Los Angeles’s greatest bands. Lead singer, guitarist, and figurehead Jeffrey Lee Pierce fits in easily with Tthe genius songwriting of Arthur Lee (Love), Chris Hillman (Byrds), and John Doe and Exene (X). Unfortunately, neither he nor his band achieved the notoriety of his fellow luminary Angelinos. From 1979 to 1996, Jeffrey manned the Gun Club ship through thick and mostly thin. Understandably, the initial Fire of Love and Miami lineup of Ward Dotson (guitar), Rob Ritter (bass), Jeffrey Lee Pierce (vocals/ guitar) and Terry Graham (drums) remains the most beloved; setting the spooky, blues-punk template for future Gun Club releases. At the time of its release, Fire of Love was heralded by East Coast critics as one of the best albums of 1981. -

Girls Like Us: Linder
Linder Sterling is a British These include her 13-hour artist and performer whose NICOLE EMMENEGGER improvised dance perfor- career spans the 1970s WORDS mance piece Darktown Cake- B Manchester punk scene to Y walk and her most recent her current collaborations work, The Ultimate Form, a with Tate St. Ives and The 'performance ballet' inspired Hepworth Centre in north- at the photographed by Barbara Hepworth, fea- west England. turing dancers from North- PORTRAITS PORTRAITS ern Ballet and costumes by She has worked in a variety B arbara Pam Hogg. of mediums – from music H B Y DEVIN (as singer/songwriter/gui- Ives St. Tate Museum in epworth We met at the The Barbican B tarist for post-punk band LAIR Centre in London on a crisp Ludus) and collage (using March morning, just days a steady scalpel to splice after the opening of her first pornographic images into big retrospective at Le Musée feminist statements), to her d’Art Moderne in Paris. current durational works. Linder 18 19 Nicole Emmenegger: First off, thank you for send- Yes, I used to have this fascination for the mid-fifties. People ing through the preparatory text about you and your I know at every age seem to have this fascination about the work. It ended up being ten pages in 10-point font! culture that you were born into, climbed into. It’s your own personal etymology and you have to go back and work it Linder: How strange, I don’t even enjoy writing! out. It’s good detective work. It makes sense and how lucky for you that 1976 was such a great year. -
Laura Harker & Paul Sullivan on Nick Cave and the 80S East
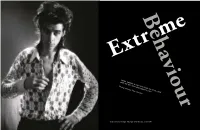
Behaviour 11 Extr me LaurA HArKer & PAul SullIvAn On Nick CAve AnD THe 80S East KreuzBerg SCene Photography by Peter gruchot 10 ecords), 24 April 1986 Studio session for the single ‘The Singer’ (Mute r Cutting a discreet diagonal between Kottbusser Tor and Oranienplatz, Dresdener Straße is one of the streets that provides blissful respite from east Kreuzberg’s constant hustle and bustle. Here, the noise of the traffic recedes and the street’s charms surge subtly into focus: fashion boutiques and indie cafés tucked into the ground floors of 19th Century Altbauten, the elegantly run-down Kino Babylon and the dark and seductive cocktail bar Würgeengel, the “exterminating angel”, a name borrowed from a surrealist film by luis Buñuel. It all looked very different in the 80s of course, when the Berlin Wall stood just under a kilometre away and the façades of these houses – now expensively renovated and worth a pretty penny – were still pockmarked by World War Two bulletholes. Mostly devoid of baths, the interiors heated by coal, their inhabitants – mostly Turkish immigrants – shivered and shuffled their way through the Berlin winter. 12 13 It was during this pre-Wende milieu that a tall, skinny and largely unknown Australian musician named Nicholas Edward Cave moved into no. 11. Aside from brief spells in apartments on naumannstraße (Schöneberg), yorckstraße, and nearby Oranienstraße, Cave spent the bulk of his seven on-and-off years in Berlin living in a tiny apartment alongside filmmaker and musician Christoph Dreher, founder of local outfit Die Haut. It was in this house that Cave wrote the lyrics and music for several Birthday Party and Bad Seeds albums, penned his debut novel (And The Ass Saw The Angel) and wielded a sizeable influence over Kreuzberg’s burgeoning post-punk scene. -

NICK CAVE &The Bad Seeds
DAustrAlisk A NyA ZeeläWNNdskA väNskApsföreNiNgeN www.AustrAlieN-Ny AZeelANd.se UNDER NR 1 / 2013 NICK CAVE & THE BAD FISKEÄVENTYR SEEDS i Auckland intervju + recension Husbils- SEMESTER på Nya Zeeland THE GRAND B.Y.O, Barbie & Beetroot? CIRCLE Nyheter & medlemsförmåner Tasmanien runt The Swan Bell Tower / Whitsundays Hells Gate i Rotorua / Stewart Island VÄNSKAPSFÖRENINGENS NYA HEMSIDA På hemsidan hittar du senaste nytt om evenemang, nyheter, medlemsförmåner och tips. Du kan läsa artiklar, reseskildringar och få information om working holiday, visum mm. Besök WWW.AUSTRalien-nYAZEELAND.SE I AUSTRALISKA NYA ZEELÄNDSKA VÄNSKAPSFÖRENINGEN Medlemsavgift 200:- kalenderår. Förutom vår medlemstidning erhåller du en mängd rabatter hos företag och föreningar som vi samarbetar med. Att bli medlem utvecklar och lönar sig! Inbetalning till PlusGiro konto 54 81 31-2. Uppge Bli namn, medlem ev. medlemsnummer och e-postadress. 2 Det känns The Grand Circle - Tasmanian runt 5 & att få skriva årets första ledare i detta nr 1 år 2013. Nytt år och ny layout på Down Under, dessutom en massa spän- nande aktiviteter på gång i kalendern.inspirerande Jag vet att många av er un- der våra kallaste månader, november till februari varit på besök i våra länderfantastiskt Australien och kul Nya Zeeland. Jag tycker det är lika spännande varje gång att få höra om vad ni upplevt och varit med om. Skriv gärna och berätta om era resor till oss på Down Under. Den 10 februari hade vi årsmöte i Lund, ett möte som även inne- höll en spännande föreläsning av vår ordförande Erwin Apitzsch. Föreningens samarbete med Studiefrämjandet gjorde att vi kunde använda oss av deras lokaler, något vi är mycket tacksamma över. -

SXSW2016 Music Full Band List
P.O. Box 685289 | Austin, Texas | 78768 T: 512.467.7979 | F: 512.451.0754 sxsw.com PRESS RELEASE - FOR IMMEDIATE RELEASE SXSW Music - Where the Global Community Connects SXSW Music Announces Full Artist List and Artist Conversations March 10, 2016 - Austin, Texas - Every March the global music community descends on the South by Southwest® Music Conference and Festival (SXSW®) in Austin, Texas for six days and nights of music discovery, networking and the opportunity to share ideas. To help with this endeavor, SXSW is pleased to release the full list of over 2,100 artists scheduled to perform at the 30th edition of the SXSW Music Festival taking place Tuesday, March 15 - Sunday, March 20, 2016. In addition, many notable artists will be participating in the SXSW Music Conference. The Music Conference lineup is stacked with huge names and stellar latebreak announcements. Catch conversations with Talib Kweli, NOFX, T-Pain and Sway, Kelly Rowland, Mark Mothersbaugh, Richie Hawtin, John Doe & Mike Watt, Pat Benatar & Neil Giraldo, and more. All-star panels include Hired Guns: World's Greatest Backing Musicians (with Phil X, Ray Parker, Jr., Kenny Aranoff, and more), Smart Studios (with Butch Vig & Steve Marker), I Wrote That Song (stories & songs from Mac McCaughan, Matthew Caws, Dan Wilson, and more) and Organized Noize: Tales From the ATL. For more information on conference programming, please go here. Because this is such an enormous list of artists, we have asked over thirty influential music bloggers to flip through our confirmed artist list and contribute their thoughts on their favorites. The 2016 Music Preview: the Independent Bloggers Guide to SXSW highlights 100 bands that should be seen live and in person at the SXSW Music Festival. -

The History of Rock Music - the Eighties
The History of Rock Music - The Eighties The History of Rock Music: 1976-1989 New Wave, Punk-rock, Hardcore History of Rock Music | 1955-66 | 1967-69 | 1970-75 | 1976-89 | The early 1990s | The late 1990s | The 2000s | Alpha index Musicians of 1955-66 | 1967-69 | 1970-76 | 1977-89 | 1990s in the US | 1990s outside the US | 2000s Back to the main Music page (Copyright © 2009 Piero Scaruffi) Singer-songwriters of the 1980s (These are excerpts from my book "A History of Rock and Dance Music") Female folksingers 1985-88 TM, ®, Copyright © 2005 Piero Scaruffi All rights reserved. Once the effects of the new wave were fully absorbed, it became apparent that the world of singer-songwriters would never be the same again. A conceptual mood had taken over the scene, and that mood's predecessors were precisely the Bob Dylans, the Neil Youngs, the Leonard Cohens, the Tim Buckleys, the Joni Mitchells, who had not been the most popular stars of the 1970s. Instead, they became the reference point for a new generation of "auteurs". Women, in particular, regained the status of philosophical beings (and not only disco-divas or cute front singers) that they had enjoyed with the works of Carole King and Joni Mitchell. Suzy Gottlieb, better known as Phranc (1), was the (Los Angeles-based) songwriter who started the whole acoustic folk revival with her aptly-titled Folksinger (? 1984/? 1985 - nov 1985), whose protest themes and openly homosexual confessions earned her the nickname of "all-american jewish-lesbian folksinger". She embodied the historic meaning of that movement because she was a punkette (notably in Nervous Gender) before she became a folksinger, and because she continued to identify, more than anyone else, with her post- feminist and AIDS-stricken generation in elegies such as Take Off Your Swastika (1989) and Outta Here (1991). -

Doctor of Philosophy
A thesis submitted in total fulfilment of the requirements for the degree of Doctor of Philosophy School of Social Sciences University of Western Sydney March 2007 ii CONTENTS LIST OF TABLES........................................................................................ VIII LIST OF FIGURES ...................................................................................... VIII LIST OF PHOTOGRAPHS ............................................................................ IX ACKNOWLEDGMENTS................................................................................. X STATEMENT OF AUTHORSHIP .................................................................. XI PRESENTATION OF RESEARCH............................................................... XII SUMMARY ..................................................................................................XIV CHAPTER 1 INTRODUCING MUSIC FESTIVALS AS POSTMODERN SITES OF CONSUMPTION.............................................................................1 1.1 The Aim of the Research ................................................................................................................. 6 1.2 Consumer Society............................................................................................................................. 8 1.3 Consuming ‘Youth’........................................................................................................................ 10 1.4 Defining Youth .............................................................................................................................. -

Kid Congo Powers
KID CONGO POWERS The gigantic tone of Kid Congo Powers’ open-tuned guitar is one of the more readily identifiable sounds in the history of underground rock. Best known for his contribution to the development of the contemporary noise guitar with The Gun Club, The Cramps, and Nick Cave and the Bad Seeds in the 1980s, Kid’s spent the last fifteen years as a sideman (Make-Up, Mark Eitzel, Angels of Light, etc.), as a partner in Congo Norvell and Kid and Khan, a member of garage rock supergroup Knoxville Girls, and, most recently, the leader of Kid Congo Powers and the Pink Monkey Birds. What’s important about Kid’s resume isn’t only that he played with some of the best bands of all time, but that he did so during their finest hours, from The Cramps’ Psychedelic Jungle to Nick Cave’s Tender Prey to Angels of Light’s How I Loved You, Kid’s always had a knack for being with the right people at the right place at the right time. The last five years however, Kid’s gradually quit relying on his luck and taken matters into his own hands, emerged as a world-class songwriter and a distinctive vocalist. Jump-starting his career when he and Jeffrey Lee Pierce formed The Gun Club in 1979, Kid Congo Powers left the obscure new band in late 1980 when he was offered the universally coveted gig replacing Bryan Gregory in The Cramps. Though Kid was already a Cramp when The Gun Club recorded their classic debut Fire of Love (1981), a number of songs that he helped write and develop appear on the record. -

Univerzita Karlova V Praze Pedagogická Fakulta BAKALÁŘSKÁ
Univerzita Karlova v Praze Pedagogická fakulta BAKALÁ ŘSKÁ PRÁCE 2015 Eva Wicheová Univerzita Karlova v Praze Pedagogická fakulta Katedra anglického jazyka a literatury BAKALÁ ŘSKÁ PRÁCE Recurrent topics in Nick Cave´s lyrics and prose Eva Wicheová Vedoucí práce: Mgr. Jakub Ženíšek Studijní program: Specializace v pedagogice Studijní obor: Aj- Čj 2015 Prohlašuji, že jsem bakalá řskou práci na téma Recurrent topics in Nick Cave´s lyrics and prose vypracovala pod vedením vedoucího práce samostatn ě za použití v práci uvedených pramen ů a literatury. Dále prohlašuji, že tato práce nebyla využita k získání jiného nebo stejného titulu. V Praze dne ........................................................ podpis Cht ěl bych pod ěkovat svému vedoucímu bakalá řské práce Mgr. Jakubu Ženíškovi za odborné vedení, za pomoc a rady p ři zpracování této práce. ANOTACE Cílem této práce je srovnání pís ňové tvorby australského hudebníka Nicka Cavea s jeho prózou, zejména s románem A uz řela oslice and ěla. Práce se zam ěř uje na témata opakující se v jeho díle, nap říklad téma lásky, smutku, utrpení, smrti, vraždy, hudby, násilí, sexu a náboženství. P ředm ětem zkoumání je také vliv témat na lyricitu nebo epi čnost textu. V jeho románové tvorb ě m ůžeme vysledovat paralely k jeho životnímu stylu hudebníka a zp ěváka. ANNOTATION The aim of this thesis is to compare Nick Cave´s lyrics with his prosaic work, especially the novel And the Ass Saw the Angel. It focuses on the main topics covered in his work, such as love, sadness, suffering, death, murder, violence, music, drugs, sex and religion. The topic are observed in relation to the lyrical or epic elements of the text. -

Smash Hits Volume 24
November 1-14 1979 30p m> POLICE SPi im BATS LPs to be won Uover forbidden 1 *-.,. Records Mv" Rec . __.. ,«i»i Atlantic L^rs^ur^tohavevou onn !*»-»- »*' BY Chic at verv love you Chorus . er d MV no other *°^lr We'll just ?JJK» no o^er and everv *nev You're 'cause " do * « anc ' <e :«•want to your beckner- "VTn'tI - „ at I didn t tr oe And love" indeed That your ^neW ves to and the you are You «Y AppearanceapP That sinister a«W» Repeat chorus Those ur love dQ ^ forbidden .... ,o«e is : ooh " NlyK hidden g^— iV.WeeVo«r»ov. indeed yes chorus to Vou are a.neat D»ne at chorus U" Hello, I'm Page 3. I'm the page that gives the rundown on the rest of the issue, makes it all sound utterly fantastic and desirable, gets to crack a joke or Nov 1-14 1979 two, and generally acts all snappy and hot to trot. It's a piece of cake in this magazine, 'cause the other pages work so hard to come up with the goods — Vol 1 No 24 now my cousin, who's Page 3 of The Sun, he has a rotten time trying to dream up captions for pictures of nude ladies. (Get on with it — Ed.) OK OK, this time around Page 24 has asked me to tell you about his Quiz; Page 31 has Editorial address; Smash Hits, Lisa 52-55 asked me to remind you about his terrific badge offer — the complete set of House, Carnaby Street, London five W1V 1PF. -

SS&H Journal LH9.U6 S46 Semper Floreat. £003 Received On
SS&H Journal LH9.U6 S46 Semper floreat. £003 Received on: £7-11-03 THE UNIVERSITY OF QUEENSUND LIBRARY ,.; '• ••'•:-•••» ,.r 'i'l*'.'!;"'.'. --, . ive in the very Heart of the Brisbane CBD from $2IOp/w City Cat Ferry y Botanic Gardens \Queen Street Mall ^ Waterfront Place Riverside Boardwall QuayWest R,yE„ciTY i^'"*Centra' l Plaza srsity W Cross River Ferry \V StoStoci k Exchange ^ . v RjV^gji Sebel I • : ! u^ •• • i. ^ • Harriot Hotels:.: :.v-n,7;^«»' fe '.m'^ii •^«WS-S5^. i' tf Minutes to Colleges Feel the excitement and pulse of living in one of Australia's most vibrant and cosmopolitan cities.Tliis is not just inner city living, this is living in the very heart of Brisbane's CBD. il;. !i:i River City Apartments offers city centre living to the privileged few with superb shops, restaurants, nightclubs, movie theatres and the Casino just a minute or two away. Imagine leaving home and arriving at work just a few minutes later, without the hassle and expense of commuting and parl<ing. Style and Luxury -i; • High quality stylish 1,2 and 2 + study bedroom apartments with designer finishes • Panoramic city or river views • A few minutes walk to the mall, Casino, everything in town! &i-; • 2 minutes walk to Queensland University of Technology • Heated 25 metre pool & spa • Gymnasium and sauna • Generously sized balconies (20m2 on average) Smart Building by Design •ilM'^^sia* River City Apartments offers more than just an exercise in style, form and function, it is truly a building for "i: •»>». the 21st Century.The entire building has been wired with 'smart technology' to give residents access to such services as the internet and intranet video streaming.