Data Integrity Threats and Countermeasures in Railway Spot Transmission Systems Hoon Wei Lim, William G
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

ERTMS/ETCS Railway Signalling
Appendix A ERTMS/ETCS Railway Signalling Salvatore Sabina, Fabio Poli and Nazelie Kassabian A.1 Interoperable Constituents The basic interoperability constituents in the Control-Command and Signalling Sub- systems are, respectively, defined in TableA.1 for the Control-Command and Sig- nalling On-board Subsystem [1] and TableA.2 for the Control-Command and Sig- nalling Trackside Subsystem [1]. The functions of basic interoperability constituents may be combined to form a group. This group is then defined by those functions and by its remaining exter- nal interfaces. If a group is formed in this way, it shall be considered as an inter- operability constituent. TableA.3 lists the groups of interoperability constituents of the Control-Command and Signalling On-board Subsystem [1]. TableA.4 lists the groups of interoperability constituents of the Control-Command and Signalling Trackside Subsystem [1]. S. Sabina (B) Ansaldo STS S.p.A, Via Paolo Mantovani 3-5, 16151 Genova, Italy e-mail: [email protected] F. Poli Ansaldo STS S.p.A, Via Ferrante Imparato 184, 80147 Napoli, Italy e-mail: [email protected] N. Kassabian Ansaldo STS S.p.A, Via Volvera 50, 10045 Piossasco Torino, Italy e-mail: [email protected] © Springer International Publishing AG, part of Springer Nature 2018 233 L. Lo Presti and S. Sabina (eds.), GNSS for Rail Transportation,PoliTO Springer Series, https://doi.org/10.1007/978-3-319-79084-8 234 Appendix A: ERTMS/ETCS Railway Signalling Table A.1 Basic interoperability constituents in the Control-Command -

EULYNX the Next Generation Signalling Strategy for Europe
European Initiative Linking Interlocking Subsystems EULYNX The next generation signalling strategy for Europe Signalling Seminar IRSE ITC – JR East Frans Heijnen 7 April 2016 With thanks to Maarten van der Werff What would you do? European Initiative Linking Interlocking Subsystems Situation: • You are an infra manager (…. passenger, tax payer) • Expectations concerning signalling • Huge installed base • Many generations of equipment • Obsolete within 10..20 years • Not enough budget to replace And you know: “At all European railways these problems are similar …” EULYNX 2 What is the problem? European Initiative Linking Interlocking Subsystems • Each railway project adds new assets to become obsolete again • They get overage sooner than expected • Costs depend on whoever was chosen in the past as the supplier of the system • There are potential savings but the railway is stuck with current solutions • But you don’t have a strategy for a new solution EULYNX 3 EULYNX. What is EULYNX? European Initiative Linking Interlocking Subsystems EULYNX is the strategic approach for standardisation of signalling systems Because standardisation is a key factor to reduce: • A ‘technology zoo’ with many different systems, • The number of multiple incompatible interfaces • The cost involved in replacing and renewal EULYNX 4 The vision that becomes reality European Initiative Linking Interlocking Subsystems By systems engineering and the development process • Use a common architecture • With a common apportionment of functionalities • Define standardised -

CBTC Test Simulation Bench
Computers in Railways XII 485 CBTC test simulation bench J. M. Mera, I. Gómez-Rey & E. Rodrigo CITEF (Railway Technology Research Centre), Escuela Técnica Superior de Ingenieros Industriales, Universidad Politécnica de Madrid, Spain Abstract Due to its safety characteristics, signalling equipment requires a great amount of testing and validation during the different stages of its life cycle, and particularly during the installation and commissioning of a new line or upgrade of an existing line, the latter being even more complicated due to the short engineering periods available overnight. This project aims to develop a tool to reduce the above-mentioned efforts by simulating the CBTC trackside, fulfilling the interfaces between subsystems and elements of these subsystems, and using some real elements. In this way, a testing environment for signalling equipment and data has been developed for the CBTC system. The aims of the project that were set out at the beginning of the development and completed with the present simulator are as follows: Real CBTC equipment trials and integration: CBTC on-board equipment, CBTC Radio Centre, etc. Other signalling elements trials and integration: interlockings and SCCs. CBTC track data validation. In order to achieve these objectives, various simulation applications have been developed, of which the most important are the following: Infrastructure, Automatic trains, Train systems, Planning and Control Desk, etc. This system has been developed, and is currently adding new modules and functionalities, for companies of the Invensys Group: Westinghouse Rail WIT Transactions on The Built Environment, Vol 114, © 2010 WIT Press www.witpress.com, ISSN 1743-3509 (on-line) doi:10.2495/CR100451 486 Computers in Railways XII Systems in the UK and Dimetronic Signals in Spain, which are using it for the new CBTC lines under their responsibility. -

A New Signalling System for Automatic Block Signal Between Stations Controlling Through an IP Network
A New Signalling System for Automatic Block Signal between Stations Controlling through an IP Network 1R. Ishima, 1Y. Fukuta, 1M. Matsumoto, 2N. Shimizu, 3H. Soutome, 4M. Mori East Japan Railway Company, Saitama, Japan1; Daido Signal Co.,Ltd., Tokyo, Japan2; Hitachi, Ltd., Hitachinaka, Japan3; Toshiba Corp., Tokyo, Japan4 Abstract This paper describes a new signalling system which controls signalling field devices of automatic block signal between stations through an IP network. The system improves the method of the system already installed to Ichikawaono station on the Musasino line in February 2007. The Logic Controller (LC), placed in a signal house, exchanges the command and feedback data with the Field Controller (FC), placed near each automatic block signal, through the Ethernet Passive Optical Network (E- PON). Following the command data, the FC electrically controls signalling field devices such as signals, track circuits, transponders of the Automatic Train Stop (i.e. Automatic Train Protection) system with Pattern (ATS-P), transponders of the S-type of ATS (ATS-S), and output relays. Only optical fiber cable requires between the LC and the FC. The system has high reliability because the LC, the FC, and the data paths of E-PON are all duplex. The system provides sufficient maintenance information through the IP network. The system can realize higher reliability, less wire-connection- work, less amount of cable, cost cutting, and faster troubleshooting. A prototype system was under evaluation on the Joban Rapid Service line between Mabashi and Kitakashiwa from August 2006 to January 2008. Evaluating the results of the field test, we conclude that the prototype system is technically suitable for signal control. -
Report on Railway Accident with Freight Car Set That Rolled Uncontrolledly from Alnabru to Sydhavna on 24 March 2010
Issued March 2011 REPORT JB 2011/03 REPORT ON RAILWAY ACCIDENT WITH FREIGHT CAR SET THAT ROLLED UNCONTROLLEDLY FROM ALNABRU TO SYDHAVNA ON 24 MARCH 2010 Accident Investigation Board Norway • P.O. Box 213, N-2001 Lillestrøm, Norway • Phone: + 47 63 89 63 00 • Fax: + 47 63 89 63 01 www.aibn.no • [email protected] This report has been translated into English and published by the AIBN to facilitate access by international readers. As accurate as the translation might be, the original Norwegian text takes precedence as the report of reference. The Accident Investigation Board has compiled this report for the sole purpose of improving railway safety. The object of any investigation is to identify faults or discrepancies which may endanger railway safety, whether or not these are causal factors in the accident, and to make safety recommendations. It is not the Board’s task to apportion blame or liability. Use of this report for any other purpose than for railway safety should be avoided. Photos: AIBN and Ruter As Accident Investigation Board Norway Page 2 TABLE OF CONTENTS NOTIFICATION OF THE ACCIDENT ............................................................................................. 4 SUMMARY ......................................................................................................................................... 4 1. INFORMATION ABOUT THE ACCIDENT ..................................................................... 6 1.1 Chain of events ................................................................................................................... -
Irish Railway Standard IRS-203-A
Irish Railway Standard IRS-203-A EMC Co-ordination Issue Published by Issue Date A CRR on behalf of the Irish Railway Industry 22.10.2019 Irish Railway Standards IRS-203-A EMC Co-ordination 1 Foreword 1.1 This Irish Railway Standard: i. cannot replace any Technical Standard for Interoperability (TSI) or other legal requirements which may be applicable to a given project; ii. is recommended to be chosen in accordance with RFU-STR-088 as an Alternative Solution in conjunction with a TSI Parameter to demonstrate conformity with the Essential Requirements; iii. may be called up as a code of practice in conjunction with CSM-REA 352/2009 and 402/2013; iv. may be called up as good industry practice in conjunction with Railway Safety Act 2005; v. may be called up as a code of practice in conjunction with the safe integration of projects within the Railway System in the Republic of Ireland as defined under 2008/57/EC Art15 or 2016/797 (EU) Art 18; vi. may in parts or in full be called up as a National Technical Rule (NTR) for the Republic of Ireland in conjunction with 2008/57/EC or 2016/797 (EU). 1.2 Where this document is called up as an NTR, the reason for its application shall be identified in line with EU 2016/797 Art 13(2): i. where the TSIs do not cover, or do not fully cover, certain aspects corresponding to the essential requirements, including open points as referred to in 2016/797 Article 4(6); ii. -
![[(Central] [Central, 6 E -1 4](https://docslib.b-cdn.net/cover/6230/central-central-6-e-1-4-316230.webp)
[(Central] [Central, 6 E -1 4
/NEWYORK^ Fnewyork^ [(Central] [Central, 6 e -1 4 Reference Marks NEW YORK CENTRAL LC.L Between POPULAR ALL-COACH DAYLINER Dally. II Meal station. Sunday only. • Thla train does not carry baggage SERVICE ADVANTAGES Chicago, Pittsburgh & Boston Daily except Sunday- Ex. Sun.—Runs dally except Sunday. Daily except Monday. E.T.—Eastern Standard Time. Daily except Saturday. C.T.—Central Standard Time. In addition to the train service shown, buses of the United Traction Company run at frequent intervals between Albany and Troy. | I i^i ichedulot . pcart'd to 5 Packing and handling research Stops on signal to receive passengers for stations beyond Albuny. traffic requirement! for most ... they assure the security ol Stops to receive or discbarge passengers for or from Astatabula and beyond. Stops except Saturdays and Sundays. rX|M*llitioilH .1. Ii\ i-r n--. the shipped merchandise. bb Stops at 6.25 a. m. to discharge passengers from Rochester and beyond or to 2 Free pick up and delivery ser• receive passengers for Chicago. Smooth operation . easy 4 Stops on signal to receive passengers for beyond Troy. vice . direct from Hliippcr's grades... superlative roadbed. Stops on signal to discharge or receive passengers. to roiisipiirrV door. No baggage handled for or from this station; *y Constant supervision and pro• Stops regularly, but only to receive passengers. * f Optional trucking allowance to tection in transit.. still mon Stops only to discbarge passengers. nhi|»|MTH jiiul roiittignrcR ... a security for shipped merchan Runs Saturdays only. mi I • i i ii i ii I tavina to both. dise. -

Positive Train Control
POSITIVE TRAIN CONTROL Carolyn Hayward-Williams Director – Technical Oversight Dennis Stonecypher PTC Specialist National Space-Based PNT Advisory Board Meeting – June 2019 Outline 1. What is Positive Train Control (PTC) and Why is it being Implemented? 2. What does PTC do? 3. The Interoperable Electronic Train Management System (I-ETMS) 4. Use of Non-Us GNSS signals for PTC 2 What is Positive Train Control? PTC is a technology capable of automatically controlling train speeds and movements, should a train operator fail to take appropriate action in the prevailing conditions. PTC MUST reliably and functionally prevent train-to-train collisions, overspeed derailments, incursions into established work zone limits, and movements of trains through switches in the wrong position. 3 Why PTC? Chatsworth, CA September 12, 2008 25 Deaths, 135 Injuries 4 PTC is Required by Statute Congress passed the Rail Safety Improvement Act of 2008 (RSIA), requiring PTC systems to be fully implemented by December 31, 2015 on: Class I railroads’ main lines that transport poison- or toxic-by-inhalation hazardous materials and Any main lines with regularly scheduled intercity or commuter rail passenger service In October 2015, Congress extended the deadline for full implementation by at least three years to December 31, 2018, and required FRA to approve any railroad’s request for an “alternative schedule and sequence” with a final deadline not later than December 31, 2020, if a railroad demonstrated it met certain statutory criteria by December 31, 2018. 5 Overview of a PTC System GPS 2. Communication Segment 3. Wayside Segment Back Office Server (BOS) 4. -
BACKTRACK 22-1 2008:Layout 1 21/11/07 14:14 Page 1
BACKTRACK 22-1 2008:Layout 1 21/11/07 14:14 Page 1 BRITAIN‘S LEADING HISTORICAL RAILWAY JOURNAL VOLUME 22 • NUMBER 1 • JANUARY 2008 • £3.60 IN THIS ISSUE 150 YEARS OF THE SOMERSET & DORSET RAILWAY GWR RAILCARS IN COLOUR THE NORTH CORNWALL LINE THE FURNESS LINE IN COLOUR PENDRAGON BRITISH ENGLISH-ELECTRIC MANUFACTURERS PUBLISHING THE GWR EXPRESS 4-4-0 CLASSES THE COMPREHENSIVE VOICE OF RAILWAY HISTORY BACKTRACK 22-1 2008:Layout 1 21/11/07 15:59 Page 64 THE COMPREHENSIVE VOICE OF RAILWAY HISTORY END OF THE YEAR AT ASHBY JUNCTION A light snowfall lends a crisp feel to this view at Ashby Junction, just north of Nuneaton, on 29th December 1962. Two LMS 4-6-0s, Class 5 No.45058 piloting ‘Jubilee’ No.45592 Indore, whisk the late-running Heysham–London Euston ‘Ulster Express’ past the signal box in a flurry of steam, while 8F 2-8-0 No.48349 waits to bring a freight off the Ashby & Nuneaton line. As the year draws to a close, steam can ponder upon the inexorable march south of the West Coast Main Line electrification. (Tommy Tomalin) PENDRAGON PUBLISHING www.pendragonpublishing.co.uk BACKTRACK 22-1 2008:Layout 1 21/11/07 14:17 Page 4 SOUTHERN GONE WEST A busy scene at Halwill Junction on 31st August 1964. BR Class 4 4-6-0 No.75022 is approaching with the 8.48am from Padstow, THE NORTH CORNWALL while Class 4 2-6-4T No.80037 waits to shape of the ancient Bodmin & Wadebridge proceed with the 10.00 Okehampton–Padstow. -
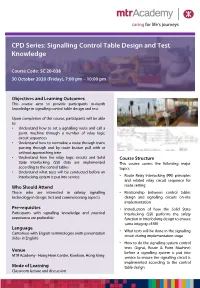
Signalling Control Table Design and Test Knowledge
CPD Series: Signalling Control Table Design and Test Knowledge Course Code: SC 20-038 30 October 2020 (Friday), 7:00 pm – 10:00 pm Objectives and Learning Outcomes This course aims to provide participants in-depth knowledge in signalling control table design and test. Upon completion of this course, participants will be able to: • Understand how to set a signalling route and call a point machine through a number of relay logic circuit sequences • Understand how to normalize a route through trains passing through and by route button pull with or without approaching train • Understand how the relay logic circuits and Solid Course Structure State Interlocking (SSI) data are implemented This course covers the following major according to the control tables topics: • Understand what tests will be conducted before an interlocking system is put into service • Route Relay Interlocking (RRI) principles and related relay circuit sequence for Who Should Attend route setting Those who are interested in railway signalling • Relationship between control tables technology in design, test and commissioning aspects design and signalling circuits on-site implementation Pre-requisites • Introduction of how the Solid State Participants with signalling knowledge and practical Interlocking (SSI) performs the safety experience are preferable* function in Interlocking design to ensure same integrity of RRI Language • What tests will be done in the signalling Cantonese with English terminologies (with presentation circuit during implementation stage slides in English) • How to do the signalling system control tests (Signal, Route & Point Machine) Venue before a signalling system is put into MTR Academy - Hung Hom Centre, Kowloon, Hong Kong service to ensure the signalling circuit is implemented according to the control Mode of Learning table design Classroom lecture and discussion Speaker Timothy Y.T. -
Balise Lifecheck the Control of Balises Is Mainly Manual and Often Basic
utomation of Balise A maintenance Balise LifeCheck The control of balises is mainly manual and often basic. There are several tools available on the market to help performing balise maintenance, but a vast majority of them follow a corrective approach. ERTMS Solutions’ BaliseLifeCheck is the only on-board tool able to do predictive maintenance. he Tsolution • Compatibility with all balises’ and legacy KER balises (KVB, EBICAB,...) • Geolocalization of the balises and creation of a cartography • Detection of possible Big Metal Masses on the track that will affect BTM performances • Computation of a signature on measurements • Auto-marking on all balises matching signature • Generation of a full report after each test journey The BaliseLifeCheck is a preventive balise measurement instrument that can be used on both diagnostic and commercial trains. While capable of measuring balise, the BaliseLifeCheck is also highly customizable and can be set-up to deliver preventive maintenance to any ‘legacy’ Automatic Train Protection (ATP) balises, regardless if they are fitted or not with ERTMS. The Benefits On-board The system has been designed to be installed on-board a test or maintenance train which purpose is to analyze test tracks and active lines. Measurement It measures key electrical parameters of the up link signal and verifies if they comply with the requirements of Subset-036 in the case of ETCS balises. In this case some measurements/tests are performed against requirements of Subset-085. Diagnosis The main goal of the tool is to provide measurements and evidences which assess the correct behavior of balises that are already deployed on the field. -

Education, Research and Collaboration in Railway Signalling, Control and Automation Yul Yunazwin Nazaruddin, Prof
International Webinar on “Railway-University Link: Railway Research and Education Outlook“, Thursday, 21 January’2021 Education, Research and Collaboration in Railway Signalling, Control and Automation Yul Yunazwin Nazaruddin, Prof. Chair of Instrumentation and Control Research Group, ITB Senior Research Fellow of the National Center for Sustainable Transportation Technology (NCSTT) e-mail : [email protected] OUTLINE 1. Graduate Program in Instrumentation and Control with Specialization in Railway Signalling, Control and Automation 2. Research Activities and Collaboration in Railway Signaling, Control and Automation 3. Collaboration with Research and Development Agency, MoT 2 Program Studi Magister Instrumentasi dan Kontrol, ITB, 2020 Graduate Program Master in Instrumentation and Control with special concentration in Railway Signalling, Control and Automation in collaboration with : Faculty of Industrial Technology Institut Teknologi Bandung 3 Master Program in Instrumentation & Control (I&C) • Master Program in Instrumentation dan Control (I&C) is a graduate program in the Faculty of Industrial Technology, Institut Teknologi Bandung (FTI ITB). • Established in 1991, this Program has produced more than hundreds of graduates who are currently working in various universities, industry, institutions / R&D. 4 Master Program in Instrumentation & Control (I&C) • Objectives of the Program “to produce qualified graduates with masters Dozens of graduates have obtained Doctorate degrees and are currently competency level who have the ability pursuing