DOMAIN/IX User's Guide Order No.: 005803 Revision: 01 Date of Publication: December, 1986
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

AIX® Version 6.1 Performance Toolbox Guide Limiting Access to Data Suppliers
AIX Version 6.1 Performance Toolbox Version 3 Guide and Reference AIX Version 6.1 Performance Toolbox Version 3 Guide and Reference Note Before using this information and the product it supports, read the information in Appendix G, “Notices,” on page 431. This edition applies to AIX Version 6.1 and to all subsequent releases and modifications until otherwise indicated in new editions. (c) Copyright AT&T, 1984, 1985, 1986, 1987, 1988, 1989. All rights reserved. Copyright Sun Microsystems, Inc., 1985, 1986, 1987, 1988. All rights reserved. The Network File System (NFS) was developed by Sun Microsystems, Inc. This software and documentation is based in part on the Fourth Berkeley Software Distribution under license from The Regents of the University of California. We acknowledge the following institutions for their role in its development: the Electrical Engineering and Computer Sciences Department at the Berkeley Campus. The Rand MH Message Handling System was developed by the Rand Corporation and the University of California. Portions of the code and documentation described in this book were derived from code and documentation developed under the auspices of the Regents of the University of California and have been acquired and modified under the provisions that the following copyright notice and permission notice appear: Copyright Regents of the University of California, 1986, 1987, 1988, 1989. All rights reserved. Redistribution and use in source and binary forms are permitted provided that this notice is preserved and that due credit is given to the University of California at Berkeley. The name of the University may not be used to endorse or promote products derived from this software without specific prior written permission. -

4010, 237 8514, 226 80486, 280 82786, 227, 280 a AA. See Anti-Aliasing (AA) Abacus, 16 Accelerated Graphics Port (AGP), 219 Acce
Index 4010, 237 AIB. See Add-in board (AIB) 8514, 226 Air traffic control system, 303 80486, 280 Akeley, Kurt, 242 82786, 227, 280 Akkadian, 16 Algebra, 26 Alias Research, 169 Alienware, 186 A Alioscopy, 389 AA. See Anti-aliasing (AA) All-In-One computer, 352 Abacus, 16 All-points addressable (APA), 221 Accelerated Graphics Port (AGP), 219 Alpha channel, 328 AccelGraphics, 166, 273 Alpha Processor, 164 Accel-KKR, 170 ALT-256, 223 ACM. See Association for Computing Altair 680b, 181 Machinery (ACM) Alto, 158 Acorn, 156 AMD, 232, 257, 277, 410, 411 ACRTC. See Advanced CRT Controller AMD 2901 bit-slice, 318 (ACRTC) American national Standards Institute (ANSI), ACS, 158 239 Action Graphics, 164, 273 Anaglyph, 376 Acumos, 253 Anaglyph glasses, 385 A.D., 15 Analog computer, 140 Adage, 315 Anamorphic distortion, 377 Adage AGT-30, 317 Anatomic and Symbolic Mapper Engine Adams Associates, 102 (ASME), 110 Adams, Charles W., 81, 148 Anderson, Bob, 321 Add-in board (AIB), 217, 363 AN/FSQ-7, 302 Additive color, 328 Anisotropic filtering (AF), 65 Adobe, 280 ANSI. See American national Standards Adobe RGB, 328 Institute (ANSI) Advanced CRT Controller (ACRTC), 226 Anti-aliasing (AA), 63 Advanced Remote Display Station (ARDS), ANTIC graphics co-processor, 279 322 Antikythera device, 127 Advanced Visual Systems (AVS), 164 APA. See All-points addressable (APA) AED 512, 333 Apalatequi, 42 AF. See Anisotropic filtering (AF) Aperture grille, 326 AGP. See Accelerated Graphics Port (AGP) API. See Application program interface Ahiska, Yavuz, 260 standard (API) AI. -

A Survey of Distributed File Systems
A Survey of Distributed File Systems M. Satyanarayanan Department of Computer Science Carnegie Mellon University February 1989 Abstract Abstract This paper is a survey of the current state of the art in the design and implementation of distributed file systems. It consists of four major parts: an overview of background material, case studies of a number of contemporary file systems, identification of key design techniques, and an examination of current research issues. The systems surveyed are Sun NFS, Apollo Domain, Andrew, IBM AIX DS, AT&T RFS, and Sprite. The coverage of background material includes a taxonomy of file system issues, a brief history of distributed file systems, and a summary of empirical research on file properties. A comprehensive bibliography forms an important of the paper. Copyright (C) 1988,1989 M. Satyanarayanan The author was supported in the writing of this paper by the National Science Foundation (Contract No. CCR-8657907), Defense Advanced Research Projects Agency (Order No. 4976, Contract F33615-84-K-1520) and the IBM Corporation (Faculty Development Award). The views and conclusions in this document are those of the author and do not represent the official policies of the funding agencies or Carnegie Mellon University. 1 1. Introduction The sharing of data in distributed systems is already common and will become pervasive as these systems grow in scale and importance. Each user in a distributed system is potentially a creator as well as a consumer of data. A user may wish to make his actions contingent upon information from a remote site, or may wish to update remote information. -
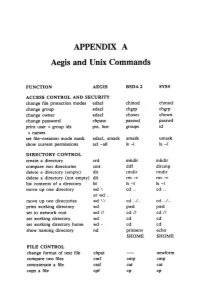
APPENDIX a Aegis and Unix Commands
APPENDIX A Aegis and Unix Commands FUNCTION AEGIS BSD4.2 SYSS ACCESS CONTROL AND SECURITY change file protection modes edacl chmod chmod change group edacl chgrp chgrp change owner edacl chown chown change password chpass passwd passwd print user + group ids pst, lusr groups id +names set file-creation mode mask edacl, umask umask umask show current permissions acl -all Is -I Is -I DIRECTORY CONTROL create a directory crd mkdir mkdir compare two directories cmt diff dircmp delete a directory (empty) dlt rmdir rmdir delete a directory (not empty) dlt rm -r rm -r list contents of a directory ld Is -I Is -I move up one directory wd \ cd .. cd .. or wd .. move up two directories wd \\ cd . ./ .. cd . ./ .. print working directory wd pwd pwd set to network root wd II cd II cd II set working directory wd cd cd set working directory home wd- cd cd show naming directory nd printenv echo $HOME $HOME FILE CONTROL change format of text file chpat newform compare two files emf cmp cmp concatenate a file catf cat cat copy a file cpf cp cp Using and Administering an Apollo Network 265 copy std input to std output tee tee tee + files create a (symbolic) link crl In -s In -s delete a file dlf rm rm maintain an archive a ref ar ar move a file mvf mv mv dump a file dmpf od od print checksum and block- salvol -a sum sum -count of file rename a file chn mv mv search a file for a pattern fpat grep grep search or reject lines cmsrf comm comm common to 2 sorted files translate characters tic tr tr SHELL SCRIPT TOOLS condition evaluation tools existf test test -

Timeline of Computer History
Timeline of Computer History By Year By Category Search AI & Robotics (55) Computers (145)(145) Graphics & Games (48) Memory & Storage (61) Networking & The Popular Culture (50) Software & Languages (60) Bell Laboratories scientist 1937 George Stibitz uses relays for a Hewlett-Packard is founded demonstration adder 1939 Hewlett and Packard in their garage workshop “Model K” Adder David Packard and Bill Hewlett found their company in a Alto, California garage. Their first product, the HP 200A A Called the “Model K” Adder because he built it on his Oscillator, rapidly became a popular piece of test equipm “Kitchen” table, this simple demonstration circuit provides for engineers. Walt Disney Pictures ordered eight of the 2 proof of concept for applying Boolean logic to the design of model to test recording equipment and speaker systems computers, resulting in construction of the relay-based Model the 12 specially equipped theatres that showed the movie I Complex Calculator in 1939. That same year in Germany, “Fantasia” in 1940. engineer Konrad Zuse built his Z2 computer, also using telephone company relays. The Complex Number Calculat 1940 Konrad Zuse finishes the Z3 (CNC) is completed Computer 1941 The Zuse Z3 Computer The Z3, an early computer built by German engineer Konrad Zuse working in complete isolation from developments elsewhere, uses 2,300 relays, performs floating point binary arithmetic, and has a 22-bit word length. The Z3 was used for aerodynamic calculations but was destroyed in a bombing raid on Berlin in late 1943. Zuse later supervised a reconstruction of the Z3 in the 1960s, which is currently on Operator at Complex Number Calculator (CNC) display at the Deutsches Museum in Munich. -
Networker Module for SAP 18.2 Administration Guide CONTENTS
Dell EMC NetWorker Module for SAP Version 18.2 Administration Guide 302-005-292 REV 02 Copyright © 2009-2019 Dell Inc. or its subsidiaries. All rights reserved. Published May 2019 Dell believes the information in this publication is accurate as of its publication date. The information is subject to change without notice. THE INFORMATION IN THIS PUBLICATION IS PROVIDED “AS-IS.“ DELL MAKES NO REPRESENTATIONS OR WARRANTIES OF ANY KIND WITH RESPECT TO THE INFORMATION IN THIS PUBLICATION, AND SPECIFICALLY DISCLAIMS IMPLIED WARRANTIES OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. USE, COPYING, AND DISTRIBUTION OF ANY DELL SOFTWARE DESCRIBED IN THIS PUBLICATION REQUIRES AN APPLICABLE SOFTWARE LICENSE. Dell, EMC, and other trademarks are trademarks of Dell Inc. or its subsidiaries. Other trademarks may be the property of their respective owners. Published in the USA. Dell EMC Hopkinton, Massachusetts 01748-9103 1-508-435-1000 In North America 1-866-464-7381 www.DellEMC.com 2 NetWorker Module for SAP 18.2 Administration Guide CONTENTS Figures 9 Tables 11 Preface 13 Chapter 1 Overview of NMSAP Features 17 Road map for NMSAP operations............................................................... 18 Terminology that is used in this guide......................................................... 19 Importance of backups and the backup lifecycle.........................................19 NMSAP features for all supported applications.......................................... 20 Scheduled backups........................................................................20 -
Expert Python Programming Third Edition
Expert Python Programming Third Edition Become a master in Python by learning coding best practices and advanced programming concepts in Python 3.7 Michał Jaworski Tarek Ziadé BIRMINGHAM - MUMBAI Expert Python Programming Third Edition Copyright © 2019 Packt Publishing All rights reserved. No part of this book may be reproduced, stored in a retrieval system, or transmitted in any form or by any means, without the prior written permission of the publisher, except in the case of brief quotations embedded in critical articles or reviews. Every effort has been made in the preparation of this book to ensure the accuracy of the information presented. However, the information contained in this book is sold without warranty, either express or implied. Neither the authors, nor Packt Publishing or its dealers and distributors, will be held liable for any damages caused or alleged to have been caused directly or indirectly by this book. Packt Publishing has endeavored to provide trademark information about all of the companies and products mentioned in this book by the appropriate use of capitals. However, Packt Publishing cannot guarantee the accuracy of this information. Commissioning Editor: Kunal Chaudhari Acquisition Editor: Chaitanya Nair Content Development Editor: Zeeyan Pinheiro Technical Editor: Ketan Kamble Copy Editor: Safis Editing Project Coordinator: Vaidehi Sawant Proofreader: Safis Editing Indexer: Priyanka Dhadke Graphics: Alishon Mendonsa Production Coordinator: Shraddha Falebhai First published: September 2008 Second edition: May 2016 Third edition: April 2019 Production reference: 1270419 Published by Packt Publishing Ltd. Livery Place 35 Livery Street Birmingham B3 2PB, UK. ISBN 978-1-78980-889-6 www.packtpub.com To my beloved wife, Oliwia, for her love, inspiration, and her endless patience. -

Introduction to GNU/Linux and the Shell 07/10/2019 | J
Introduction to GNU/Linux and the Shell 07/10/2019 | J. Albert-von der Gönna Leibniz Supercomputing Centre Bavarian Academy of Sciences and Humanities IT Service Backbone for the Advancement of Science and Research Computer Centre 250 for all Munich Universities employees approx. Regional Computer Centre for all Bavarian Universities National Supercomputing Centre 57 (GCS) years of European Supercomputing Centre IT support (PRACE) Introduction to GNU/Linux and the Shell | 07/10/2019 | J. Albert-von der Gönna 3 Course Information • The aim of this course is to provide an introduction to GNU/Linux and the Unix Shell • You will probably benefit the most, if you’re not yet familiar with GNU/Linux and the Unix Shell, but if you plan to work on the HPC and/or Compute Cloud infrastructure provided by LRZ -> by the end of this workshop, you should have the basic skills to successfully interact with GNU/Linux-based systems • Consider the following – especially during hands-on sessions: -> you may want to partner up with the person sitting next to you -> it may be beneficial to sit back and watch the slides/demos -> the slides will be made available after the workshop -> generally: please ask, if you have any questions Introduction to GNU/Linux and the Shell | 07/10/2019 | J. Albert-von der Gönna 4 What is GNU/Linux • Free and open-source operating system • Alternative to Microsoft Windows, Apple macOS, Google Android … • Generally consists of the Linux kernel, libraries and tools, a desktop environment and various applications (e.g. web browser, office suite, …) • Different distributions: Arch Linux, Debian, Fedora/RHEL, openSUSE/SLES, Ubuntu, … Introduction to GNU/Linux and the Shell | 07/10/2019 | J. -
Dtrace-Ebook.Pdf
The illumos Dynamic Tracing Guide The contents of this Documentation are subject to the Public Documentation License Version 1.01 (the “License”); you may only use this Documentation if you comply with the terms of this License. Further information about the License is available in AppendixA. Many of the designations used by manufacturers and sellers to distinguish their products are claimed as trademarks. Where those designations appear in this document, and the publisher was aware of the trademark claim, the designations have been followed by the “™” or the “®” symbol, or printed with initial capital letters or in all capitals. This distribution may include materials developed by third parties. Parts of the product may be derived from Berkeley BSD systems, licensed from the University of California. UNIX is a registered trademark of The Open Group. illumos and the illumos logo are trademarks or registered trademarks of Garrett D’Amore. Sun, Sun Microsystems, StarOffice, Java, and Solaris are trademarks or registered trademarks of Oracle, Inc. or its subsidiaries in the U.S. and other countries. All SPARC trademarks are used under license and are trademarks or registered trademarks of SPARC International, Inc. in the U.S. and other countries. Products bearing SPARC trademarks are based upon an architecture developed by Sun Microsystems, Inc. DOCUMENTATION IS PROVIDED “AS IS” AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTA- TIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. Copyright © 2008 Sun Microsystems, Inc. -

A History of the Personal Computer Index/11
A History of the Personal Computer 6100 CPU. See Intersil Index 6501 and 6502 microprocessor. See MOS Legend: Chap.#/Page# of Chap. 6502 BASIC. See Microsoft/Prog. Languages -- Numerals -- 7000 copier. See Xerox/Misc. 3 E-Z Pieces software, 13/20 8000 microprocessors. See 3-Plus-1 software. See Intel/Microprocessors Commodore 8010 “Star” Information 3Com Corporation, 12/15, System. See Xerox/Comp. 12/27, 16/17, 17/18, 17/20 8080 and 8086 BASIC. See 3M company, 17/5, 17/22 Microsoft/Prog. Languages 3P+S board. See Processor 8514/A standard, 20/6 Technology 9700 laser printing system. 4K BASIC. See Microsoft/Prog. See Xerox/Misc. Languages 16032 and 32032 micro/p. See 4th Dimension. See ACI National Semiconductor 8/16 magazine, 18/5 65802 and 65816 micro/p. See 8/16-Central, 18/5 Western Design Center 8K BASIC. See Microsoft/Prog. 68000 series of micro/p. See Languages Motorola 20SC hard drive. See Apple 80000 series of micro/p. See Computer/Accessories Intel/Microprocessors 64 computer. See Commodore 88000 micro/p. See Motorola 80 Microcomputing magazine, 18/4 --A-- 80-103A modem. See Hayes A Programming lang. See APL 86-DOS. See Seattle Computer A+ magazine, 18/5 128EX/2 computer. See Video A.P.P.L.E. (Apple Pugetsound Technology Program Library Exchange) 386i personal computer. See user group, 18/4, 19/17 Sun Microsystems Call-A.P.P.L.E. magazine, 432 microprocessor. See 18/4 Intel/Microprocessors A2-Central newsletter, 18/5 603/4 Electronic Multiplier. Abacus magazine, 18/8 See IBM/Computer (mainframe) ABC (Atanasoff-Berry 660 computer. -

Apollo Computerapr 15,981
apollo computerAPR 15,981 APOLLO DOMAIN ARCHITECTURE (February 1981) apollo computer inc. 5 Executive ParK Drive, N. Billerica, MA 01862617-667-8800 ARCHITECTURE EVOLUTION (1960-80) 1980s l.tARCHITECTURE EVOLUTION: This figure depicts the evolution of architecture over the called dedicated minicomputers. Minicomputers are past 20 years. In the center diamonD at the top we show characterized by having goodinteractivenesst good batch computing of the 1960's which is characterb:ed by, human interfaces, and very good performance, but first, very littte or n~ interactivenessand, second, very lacked in the· sharing of peripherals and data among a ritfle or no sharing of peripherals and data fifes. tn the late community of users. 1960's computer architecture evolved into two distinct The Apollo DOMAIN system has evolved as a direct result forms. On the one hand there was timesharing which was of improvements in technology and is widely h.eld to be intended for people who, needed/arge machine the architecture of the 1960's. It combines the goOd parts architecture, but could sacrifice certain degrees of of both timesharing and dedicated minicomputers, but performance and interactive ness. Timesharrng systems eliminates Ute disadvantages of both of these earlier are characterized by poor interactiveness but very good forms. The ApolfoDOMAIN system has good sharing sharing characteristics and also large machine capabilities provided by a high speed interactive network architecture. On the other hand batch evolved into a form as well as interactiveness provided by a dedicated computer available to each user. GOVERNING PRINCIPLES • DEDICATED CPU PER USER • INTEGRAL WIDE BAND LOCAL NETWORK • HIGH LEVEL DESIGN (ISP, VAS, PMS INDEPENDENCE) • USE OF ADVANCED TECHNOLOGIES (VLSI CPU, WINCHESTER DISKS, etc.) 1.2 GOVERNING PRINCIPLES: There are several principles that have been used to design of the architecture is based on high level govern the design < of the Apollo computer system. -

National Software Works) Lessons Lerrned(U) 1/2 Massachusetts Computer Associates Inc Wakefield Sunclassified F3@602-83-C-8940Muntzet Al
AD-R146 737 NSW (NATIONAL SOFTWARE WORKS) LESSONS LERRNED(U) 1/2 MASSACHUSETTS COMPUTER ASSOCIATES INC WAKEFIELD SUNCLASSIFIED F3@602-83-C-8940MUNTZET AL. MAY 84 CAIDD-83i2-38ei-/ RRDC-TR-84-90- 9/ N-tL mImmIIIIIIu IIIIIIIIIIIIII I I I I IIfflllll IIIIIIIIIIIIEIIEEIIII 7 - EM"- s la 1L.", 1111.0 I 12.5 36 Em2L * 11111 1.8 11.25 l . 116 - .. .+,., . AD-A146 737 Sl LESSONS LEARNED -. S Mmmbmfu Cput~rAmdepusn 0 Ch... MM . .urm.It Kirk Sattbey aid Obpmwo .e.e DTIC ELECTE OCT 2 3, AIR DEVELOPMENT CENTER . uj ROMEAir Force Systems Command Griffiss Air Force Base, NY 13441 84 10 19 148 F0 This report has been reviewed by the RADC Public Affairs Office (PA) and is releasable to the National Technical Information Service (NTIS). At NTIS it will be releasable to the general public, including foreign nations. RADC-TR-84-90 has been reviewed and is approved for publication. 0 APPROVED:& " 3 PATRICIA J. BASKINGER Project Engineer APPROVED: RONALD S. OSO Acting Chief, Command & Control Division FOR THE COMMANDER: • JOHN A. RITZ Acting Chief, Plans Office 4S If your address has changed or if you wish to be removed from the RADC mailing list, or if the addressee is no longer employed by your organization, please notify RADC (COTD) Griffiss AFB NY 13441. This will assist us in . maintaining a current mailing list. Do not return copies of this report unless contractual obligations or notices on a specific document requires that it be returned. UNCLASSIFIED SECUR4ITY CLASSIFICATION OP T141 PAGE REPORT DOCUMENTATION PAGE I11111PORT SECURITY CLAESIP#CATION 1b.