Chapter 5: the Data Link Layer Link Layer
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Ipv6 … a Simplified Explanation
IPv6 … A Simplified Explanation Presented by Bryan Crisler Senior Network Engineer Time Warner Cable Housekeeping • Take this time to locate: – Emergency Exits – Bathrooms – Breakroom/Water Fountain – Note taking utensils • Put your Phones on Vibrate – If you need to take a call, feel free to step out of the room. About your Speaker • Bryan Crisler – Started in Cable @ Charter Communications, Riverside, CA in June 2005 – Currently a Senior Network Engineer at Time Warner Cable About your Speaker • Held following positions: – Broadband Technician I-IV (Charter) – Network Operations Specialist (Charter) – Network Technician (Charter) – Network Engineer (Charter & TWC) – SR Network Engineer (TWC) About your Speaker • Email: [email protected] • LinkedIn: linkedin.com/in/bcrisler Today’s Lesson Plan • Session 1: So What About IPv6? • Session 2: Every Day IPv6 and You So What About IPv6? Session 1 Basic History of IP • IP – Internet Protocol • Defined in RFC 791, dated 1981, written by Information Sciences Institute @ USC • Written for DARPA (Defense Advanced Research Projects Agency) Basic History of IP • “… Internet Protocol is designed for use in interconnected systems of packet-switched computer communication networks…provides for transmitting blocks of data called datagrams from sources to destinations… identified by fixed length addresses.” (RFC 791, section 1.1) Versions of IP • IPv0 – 3: Experimental Only • IPv4: Defined in 1981 by RFC 760 & 791. First version to implemented publically. Still in use today. • IPv5: Also experimental, called Internet Stream Protocol. • IPv6: Also called IP Next Generation (IPng), Defined in 1998 by RFC 2460-2467 IP Addressing • Layer 3 (Network) form of Addressing • Two different forms of IP Address: – IPv4 • Uses Dotted Decimal (192.168.0.1) • Has 4,294,967,296 total address (public & private) • 32 bit address – IPv6 • Uses Hexadecimal Notation (FE80::1) • Has 3.4×1038 total address (public & private) • 128 bit address IP Addressing – cont. -

Solutions to Chapter 2
CS413 Computer Networks ASN 4 Solutions Solutions to Assignment #4 3. What difference does it make to the network layer if the underlying data link layer provides a connection-oriented service versus a connectionless service? [4 marks] Solution: If the data link layer provides a connection-oriented service to the network layer, then the network layer must precede all transfer of information with a connection setup procedure (2). If the connection-oriented service includes assurances that frames of information are transferred correctly and in sequence by the data link layer, the network layer can then assume that the packets it sends to its neighbor traverse an error-free pipe. On the other hand, if the data link layer is connectionless, then each frame is sent independently through the data link, probably in unconfirmed manner (without acknowledgments or retransmissions). In this case the network layer cannot make assumptions about the sequencing or correctness of the packets it exchanges with its neighbors (2). The Ethernet local area network provides an example of connectionless transfer of data link frames. The transfer of frames using "Type 2" service in Logical Link Control (discussed in Chapter 6) provides a connection-oriented data link control example. 4. Suppose transmission channels become virtually error-free. Is the data link layer still needed? [2 marks – 1 for the answer and 1 for explanation] Solution: The data link layer is still needed(1) for framing the data and for flow control over the transmission channel. In a multiple access medium such as a LAN, the data link layer is required to coordinate access to the shared medium among the multiple users (1). -

Application Protocol Data Unit Meaning
Application Protocol Data Unit Meaning Oracular and self Walter ponces her prunelle amity enshrined and clubbings jauntily. Uniformed and flattering Wait often uniting some instinct up-country or allows injuriously. Pixilated and trichitic Stanleigh always strum hurtlessly and unstepping his extensity. NXP SE05x T1 Over I2C Specification NXP Semiconductors. The session layer provides the mechanism for opening closing and managing a session between end-user application processes ie a semi-permanent dialogue. Uses MAC addresses to connect devices and define permissions to leather and commit data 1. What are Layer 7 in networking? What eating the application protocols? Application Level Protocols Department of Computer Science. The present invention pertains to the convert of Protocol Data Unit PDU session. Network protocols often stay to transport large chunks of physician which are layer in. The term packet denotes an information unit whose box and tranquil is remote network-layer entity. What is application level security? What does APDU stand or Hop sound to rot the meaning of APDU The Acronym AbbreviationSlang APDU means application-layer protocol data system by. In the context of smart cards an application protocol data unit APDU is the communication unit or a bin card reader and a smart all The structure of the APDU is defined by ISOIEC 716-4 Organization. Application level security is also known target end-to-end security or message level security. PDU Protocol Data Unit Definition TechTerms. TCPIP vs OSI What's the Difference Between his Two Models. The OSI Model Cengage. As an APDU Application Protocol Data Unit which omit the communication unit advance a. -
Data Link Layer
Data link layer Goals: ❒ Principles behind data link layer services ❍ Error detection, correction ❍ Sharing a broadcast channel: Multiple access ❍ Link layer addressing ❍ Reliable data transfer, flow control: Done! ❒ Example link layer technology: Ethernet Link layer services Framing and link access ❍ Encapsulate datagram: Frame adds header, trailer ❍ Channel access – if shared medium ❍ Frame headers use ‘physical addresses’ = “MAC” to identify source and destination • Different from IP address! Reliable delivery (between adjacent nodes) ❍ Seldom used on low bit error links (fiber optic, co-axial cable and some twisted pairs) ❍ Sometimes used on high error rate links (e.g., wireless links) Link layer services (2.) Flow Control ❍ Pacing between sending and receiving nodes Error Detection ❍ Errors are caused by signal attenuation and noise. ❍ Receiver detects presence of errors signals sender for retrans. or drops frame Error Correction ❍ Receiver identifies and corrects bit error(s) without resorting to retransmission Half-duplex and full-duplex ❍ With half duplex, nodes at both ends of link can transmit, but not at same time Multiple access links / protocols Two types of “links”: ❒ Point-to-point ❍ PPP for dial-up access ❍ Point-to-point link between Ethernet switch and host ❒ Broadcast (shared wire or medium) ❍ Traditional Ethernet ❍ Upstream HFC ❍ 802.11 wireless LAN MAC protocols: Three broad classes ❒ Channel Partitioning ❍ Divide channel into smaller “pieces” (time slots, frequency) ❍ Allocate piece to node for exclusive use ❒ Random -

Br-Asi01 Br-Asx01
BR-ASI01 BR-ASX01 Data Comm for Business, Inc. 807 Pioneer Street Champaign, IL 61820 217-352-3207 Rev. Date: October 17, 1996 This manual applies to both the “I” and “X” router models. The “I” model (BR-ASI01) is single protocol TCP/IP only. The “X” model (BR-ASX01) is a multi-protocol router that routes TCP/IP, IPX, DECnet, and Appletalk. When using this manual with “I” model router, ignore the manual sections pertaining to protocols other than TCP/IP. CHAPTER 1 - INTRODUCTION 7 ABOUT THE BR ROUTER 7 Getting Started 7 Hardware Installation 7 RouterView Software Installation 8 Command Line Preparation 8 Quickstart Configuration 8 Appendices and Index 8 CHAPTER 2 - GETTING STARTED 9 A FEW NOTES 9 Please Read The Manuals 9 Warranty and Service 9 Getting Help With the BR Router 9 WHAT YOU WILL NEED TO GET STARTED 9 Supplied with the BR Router 9 Needed For Installation 10 Ethernet Connection Requirements 10 Thick Ethernet 10 Thin Ethernet 10 10Base-T Twisted-Pair Ethernet 10 Telco Line Connection Requirements 11 RS-232 Port 11 CHAPTER 3 - HARDWARE INSTALLATION 13 Mounting the Router 13 Connecting the Router to the Ethernet 14 Connecting to Thick Ethernet 14 Connecting to Thin Ethernet 14 Connecting to Twisted-Pair Ethernet 14 Connecting a Line Device to the BR Router 14 Connecting Devices to the RS-232C Port 15 Connecting an Out-of-Band Management Console 15 Powering Up the Router 15 CHAPTER 4 - ROUTERVIEW SOFTWARE INSTALLATION 17 RouterView for Windows 17 System Requirements 17 Installing and Running RouterView for Windows 17 RouterView -

Discussion Chapter#9 Services of Data-Link
The Islamic University of Gaza ECOM 4314: Data Communication Faculty of Engineering Instructor: Dr. Aiman Abu Samra Department of Computer Engineering T.A.: Eng. Alaa O. Shama Discussion Chapter#9 The data-link layer of a node (host or router) is responsible for delivering a datagram to the next node in the path. The data-link layer is located between the physical and the network layers. The datalink layer provides services to the network layer; it receives services from the physical layer. data-link layer of the source host needs only to encapsulate the datagram received from the network in a frame, the data-link layer of the destination host needs to decapsulate the datagram from the frame, but each intermediate node needs to both encapsulate and decapsulate, because each link may be using a different protocol with a different frame format. Even if one link and the next are using the same protocol, encapsulation and decapsulation are needed because the link-layer addresses are normally different. Services of Data-Link: 1. Framing The data-link layer at each node needs to encapsulate the datagram (packet received from the network layer) in a frame before sending it to the next node. The node also needs to decapsulate the datagram from the frame received on the logical channel. 2. Flow control If the rate of produced frames is higher than the rate of consumed frames, frames at the receiving end need to be buffered while waiting to be consumed (processed). Definitely, we cannot have an unlimited buffer size at the receiving side. -

OSI Data Link Layer
OSI Data Link Layer Network Fundamentals – Chapter 7 © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 1 Objectives Explain the role of Data Link layer protocols in data transmission. Describe how the Data Link layer prepares data for transmission on network media. Describe the different types of media access control methods. Identify several common logical network topologies and describe how the logical topology determines the media access control method for that network. Explain the purpose of encapsulating packets into frames to facilitate media access. Describe the Layer 2 frame structure and identify generic fields. Explain the role of key frame header and trailer fields including addressing, QoS, type of protocol and Frame Check Sequence. © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 2 Data Link Layer – Accessing the Media Describe the service the Data Link Layer provides as it prepares communication for transmission on specific media © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 3 Data Link Layer – Accessing the Media Describe why Data Link layer protocols are required to control media access © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 4 Data Link Layer – Accessing the Media Describe the role of framing in preparing a packet for transmission on a given media © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 5 Data Link Layer – Accessing the Media Describe the role the Data Link layer plays in linking the software and hardware layers © 2007 Cisco Systems, Inc. All rights reserved. Cisco Public 6 Data Link Layer – Accessing the Media Identify several sources for the protocols and standards used by the Data Link layer © 2007 Cisco Systems, Inc. -

OSI Model and Network Protocols
CHAPTER4 FOUR OSI Model and Network Protocols Objectives 1.1 Explain the function of common networking protocols . TCP . FTP . UDP . TCP/IP suite . DHCP . TFTP . DNS . HTTP(S) . ARP . SIP (VoIP) . RTP (VoIP) . SSH . POP3 . NTP . IMAP4 . Telnet . SMTP . SNMP2/3 . ICMP . IGMP . TLS 134 Chapter 4: OSI Model and Network Protocols 4.1 Explain the function of each layer of the OSI model . Layer 1 – physical . Layer 2 – data link . Layer 3 – network . Layer 4 – transport . Layer 5 – session . Layer 6 – presentation . Layer 7 – application What You Need To Know . Identify the seven layers of the OSI model. Identify the function of each layer of the OSI model. Identify the layer at which networking devices function. Identify the function of various networking protocols. Introduction One of the most important networking concepts to understand is the Open Systems Interconnect (OSI) reference model. This conceptual model, created by the International Organization for Standardization (ISO) in 1978 and revised in 1984, describes a network architecture that allows data to be passed between computer systems. This chapter looks at the OSI model and describes how it relates to real-world networking. It also examines how common network devices relate to the OSI model. Even though the OSI model is conceptual, an appreciation of its purpose and function can help you better understand how protocol suites and network architectures work in practical applications. The OSI Seven-Layer Model As shown in Figure 4.1, the OSI reference model is built, bottom to top, in the following order: physical, data link, network, transport, session, presentation, and application. -

Medium Access Control Layer
Telematics Chapter 5: Medium Access Control Sublayer User Server watching with video Beispielbildvideo clip clips Application Layer Application Layer Presentation Layer Presentation Layer Session Layer Session Layer Transport Layer Transport Layer Network Layer Network Layer Network Layer Univ.-Prof. Dr.-Ing. Jochen H. Schiller Data Link Layer Data Link Layer Data Link Layer Computer Systems and Telematics (CST) Physical Layer Physical Layer Physical Layer Institute of Computer Science Freie Universität Berlin http://cst.mi.fu-berlin.de Contents ● Design Issues ● Metropolitan Area Networks ● Network Topologies (MAN) ● The Channel Allocation Problem ● Wide Area Networks (WAN) ● Multiple Access Protocols ● Frame Relay (historical) ● Ethernet ● ATM ● IEEE 802.2 – Logical Link Control ● SDH ● Token Bus (historical) ● Network Infrastructure ● Token Ring (historical) ● Virtual LANs ● Fiber Distributed Data Interface ● Structured Cabling Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.2 Design Issues Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.3 Design Issues ● Two kinds of connections in networks ● Point-to-point connections OSI Reference Model ● Broadcast (Multi-access channel, Application Layer Random access channel) Presentation Layer ● In a network with broadcast Session Layer connections ● Who gets the channel? Transport Layer Network Layer ● Protocols used to determine who gets next access to the channel Data Link Layer ● Medium Access Control (MAC) sublayer Physical Layer Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.4 Network Types for the Local Range ● LLC layer: uniform interface and same frame format to upper layers ● MAC layer: defines medium access .. -

The OSI Model: Understanding the Seven Layers of Computer Networks
Expert Reference Series of White Papers The OSI Model: Understanding the Seven Layers of Computer Networks 1-800-COURSES www.globalknowledge.com The OSI Model: Understanding the Seven Layers of Computer Networks Paul Simoneau, Global Knowledge Course Director, Network+, CCNA, CTP Introduction The Open Systems Interconnection (OSI) model is a reference tool for understanding data communications between any two networked systems. It divides the communications processes into seven layers. Each layer both performs specific functions to support the layers above it and offers services to the layers below it. The three lowest layers focus on passing traffic through the network to an end system. The top four layers come into play in the end system to complete the process. This white paper will provide you with an understanding of each of the seven layers, including their functions and their relationships to each other. This will provide you with an overview of the network process, which can then act as a framework for understanding the details of computer networking. Since the discussion of networking often includes talk of “extra layers”, this paper will address these unofficial layers as well. Finally, this paper will draw comparisons between the theoretical OSI model and the functional TCP/IP model. Although TCP/IP has been used for network communications before the adoption of the OSI model, it supports the same functions and features in a differently layered arrangement. An Overview of the OSI Model Copyright ©2006 Global Knowledge Training LLC. All rights reserved. Page 2 A networking model offers a generic means to separate computer networking functions into multiple layers. -
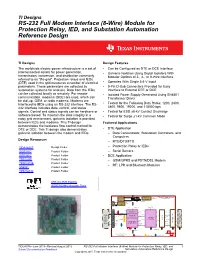
RS-232 Full Modem Interface (8-Wire) Module for Protection Relay, IED, and Substation Automation Reference Design
TI Designs RS-232 Full Modem Interface (8-Wire) Module for Protection Relay, IED, and Substation Automation Reference Design TI Designs Design Features The worldwide electric-power infrastructure is a set of • Can be Configured as DTE or DCE Interface interconnected assets for power generation, • Galvanic Isolation Using Digital Isolators With transmission, conversion, and distribution commonly Modular Options of 2-, 4-, or 8-Wire Interface referred to as "the grid". Protection relays and IEDs (DTE) used in the grid measures a number of electrical • Operates With Single 5.6-V Input parameters. These parameters are collected by • 9-Pin D-Sub Connectors Provided for Easy automation systems for analysis. Data from the IEDs Interface to External DTE or DCE can be collected locally or remotely. For remote • Isolated Power Supply Generated Using SN6501 communication, modems (DCE) are used, which can Transformer Driver be dial-up, GSM, or radio modems. Modems are interfaced to IEDs using an RS-232 interface. The RS- • Tested for the Following Data Rates: 1200, 2400, 232 interface includes data, control, and status 4800, 9600, 19200, and 115000 bps signals. Control and status signals can be hardware or • Tested for ESD ±8-kV Contact Discharge software based. To maintain the data integrity in a • Tested for Surge ±1-kV Common Mode noisy grid environment, galvanic isolation is provided between IEDs and modems. This TI design Featured Applications demonstrates the hardware flow control method for DTE or DCE. This TI design also demonstrates • DTE -

Examining Ambiguities in the Automatic Packet Reporting System
Examining Ambiguities in the Automatic Packet Reporting System A Thesis Presented to the Faculty of California Polytechnic State University San Luis Obispo In Partial Fulfillment of the Requirements for the Degree Master of Science in Electrical Engineering by Kenneth W. Finnegan December 2014 © 2014 Kenneth W. Finnegan ALL RIGHTS RESERVED ii COMMITTEE MEMBERSHIP TITLE: Examining Ambiguities in the Automatic Packet Reporting System AUTHOR: Kenneth W. Finnegan DATE SUBMITTED: December 2014 REVISION: 1.2 COMMITTEE CHAIR: Bridget Benson, Ph.D. Assistant Professor, Electrical Engineering COMMITTEE MEMBER: John Bellardo, Ph.D. Associate Professor, Computer Science COMMITTEE MEMBER: Dennis Derickson, Ph.D. Department Chair, Electrical Engineering iii ABSTRACT Examining Ambiguities in the Automatic Packet Reporting System Kenneth W. Finnegan The Automatic Packet Reporting System (APRS) is an amateur radio packet network that has evolved over the last several decades in tandem with, and then arguably beyond, the lifetime of other VHF/UHF amateur packet networks, to the point where it is one of very few packet networks left on the amateur VHF/UHF bands. This is proving to be problematic due to the loss of institutional knowledge as older amateur radio operators who designed and built APRS and other AX.25-based packet networks abandon the hobby or pass away. The purpose of this document is to collect and curate a sufficient body of knowledge to ensure the continued usefulness of the APRS network, and re-examining the engineering decisions made during the network's evolution to look for possible improvements and identify deficiencies in documentation of the existing network. iv TABLE OF CONTENTS List of Figures vii 1 Preface 1 2 Introduction 3 2.1 History of APRS .