Forensic Software Tools for Cell Phone Subscriber Identity Modules
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Location Update Procedure
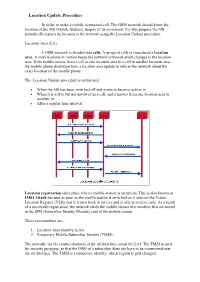
Location Update Procedure In order to make a mobile terminated call, The GSM network should know the location of the MS (Mobile Station), despite of its movement. For this purpose the MS periodically reports its location to the network using the Location Update procedure. Location Area (LA) A GSM network is divided into cells. A group of cells is considered a location area. A mobile phone in motion keeps the network informed about changes in the location area. If the mobile moves from a cell in one location area to a cell in another location area, the mobile phone should perform a location area update to inform the network about the exact location of the mobile phone. The Location Update procedure is performed: When the MS has been switched off and wants to become active, or When it is active but not involved in a call, and it moves from one location area to another, or After a regular time interval. Location registration takes place when a mobile station is turned on. This is also known as IMSI Attach because as soon as the mobile station is switched on it informs the Visitor Location Register (VLR) that it is now back in service and is able to receive calls. As a result of a successful registration, the network sends the mobile station two numbers that are stored in the SIM (Subscriber Identity Module) card of the mobile station. These two numbers are:- 1. Location Area Identity (LAI) 2. Temporary Mobile Subscriber Identity (TMSI). The network, via the control channels of the air interface, sends the LAI. -

Security for the Core Network of Third Generation Mobile Systems
Security for the core network of third generation mobile systems GUNTER HORN, DIRK KROSELBERG Siemens AG, Corporate Technology, D-81730 Muenchen, Germany STEFANPUTZ T-Mobil, P.O. Box 300463, D-53184 Bonn, Germany ROLAND SCHMITZ T-Nova Technology Centre, D-64307 Darmstadt, Germany Keywords: UMTS, MAP Security, Multimedia domain, SIP, IPSec, IKE, Key Management Abstract: This contribution gives a survey of the present standardisation activities by 3GPP (3'd Generation Partnership Project1) in the area of security for signalling in the core network of third generation mobile systems. We give an overview of the protocols that need to be secured, present the basic principles behind the overall security architecture and describe the key management and format of secured messages, as far as they have already been finalised. In particular, we address core network security aspects of the 3GPP multimedia domain. 1 3GPP was formed by regional standards organisations from Europe, Asia and North America to produce specifications for a third generation mobile system named UMTS which is designed to evolve from GSM core network. There is a competing effort known as 3GPP2 with partners from North America and Asia. The original version of this chapter was revised: The copyright line was incorrect. This has been corrected. The Erratum to this chapter is available at DOI: 10.1007/978-0-387-35413-2_36 R. Steinmetz et al. (eds.), Communications and Multimedia Security Issues of the New Century © IFIP International Federation for Information Processing 2001 298 1. THREATS TO CORE NETWORK SECURITY FOR MOBILE RADIO NETWORKS The core network of mobile radio systems is the part of the network which is independent of the radio interface technology of the mobile terminal. -

Cellular Technology.Pdf
Cellular Technologies Mobile Device Investigations Program Technical Operations Division - DFB DHS - FLETC Basic Network Design Frequency Reuse and Planning 1. Cellular Technology enables mobile communication because they use of a complex two-way radio system between the mobile unit and the wireless network. 2. It uses radio frequencies (radio channels) over and over again throughout a market with minimal interference, to serve a large number of simultaneous conversations. 3. This concept is the central tenet to cellular design and is called frequency reuse. Basic Network Design Frequency Reuse and Planning 1. Repeatedly reusing radio frequencies over a geographical area. 2. Most frequency reuse plans are produced in groups of seven cells. Basic Network Design Note: Common frequencies are never contiguous 7 7 The U.S. Border Patrol uses a similar scheme with Mobile Radio Frequencies along the Southern border. By alternating frequencies between sectors, all USBP offices can communicate on just two frequencies Basic Network Design Frequency Reuse and Planning 1. There are numerous seven cell frequency reuse groups in each cellular carriers Metropolitan Statistical Area (MSA) or Rural Service Areas (RSA). 2. Higher traffic cells will receive more radio channels according to customer usage or subscriber density. Basic Network Design Frequency Reuse and Planning A frequency reuse plan is defined as how radio frequency (RF) engineers subdivide and assign the FCC allocated radio spectrum throughout the carriers market. Basic Network Design How Frequency Reuse Systems Work In concept frequency reuse maximizes coverage area and simultaneous conversation handling Cellular communication is made possible by the transmission of RF. This is achieved by the use of a powerful antenna broadcasting the signals. -

Location Update and Paging in Wireless Networks — Location Management Plays the Central Role in Providing Ubiquitous Communica
Location Update and Paging in Wireless Networks Paging • Paging is the one-to-one communication between the mobile and the base station • Paging is a procedure the network uses to find out a subscriber's location before actual call establishment. • Paging is used to alert the mobile station of an incoming call — Location management plays the central role in providing ubiquitous communications services in the future wireless mobile networks. Location update and paging are commonly used in tracking mobile users on the move, location update is to update a mobile user’s current location while the paging is used to locate a mobile user, both will incur signaling traffic in the wireless networks. The more frequent the location updates, the less paging in locating a mobile user, thus there is a tradeoff in terms of signaling cost There are two basic operations for tracking a mobile user: location update and terminal paging. Location update is the process for the mobile terminals to report their locations to the network, thus all mobiles are actively sending location update messages to keep the network informed. Terminal paging is the process for the network to search the called terminal by sending polling signals to cells close to the last reported location of the called terminal. When an incoming calls to a mobile user (we will use mobile user and mobile terminal interchangeably) arrives, the wireless network simply routes the call to the last reported location of the mobile terminal. Intuitively, the location accuracy depends on the location update frequency, the more often the location updates, the more accurate the location information. -

SCCP Signalling Aspects for Roaming Version 3.2.1 10 October 2005
GSM Association Non-confidential Official Document IR.22 - SCCP Signalling Aspects for Roaming SCCP Signalling Aspects for Roaming Version 3.2.1 10 October 2005 This is a Non-binding Permanent Reference Document of the GSMA Security Classification: Non-confidential Access to and distribution of this document is restricted to the persons permitted by the security classification. This document is confidential to the Association and is subject to copyright protection. This document is to be used only for the purposes for which it has been supplied and information contained in it must not be disclosed or in any other way made available, in whole or in part, to persons other than those permitted under the security classification without the prior written approval of the Association. Copyright Notice Copyright © 2015 GSM Association Disclaimer The GSM Association (“Association”) makes no representation, warranty or undertaking (express or implied) with respect to and does not accept any responsibility for, and hereby disclaims liability for the accuracy or completeness or timeliness of the information contained in this document. The information contained in this document may be subject to change without prior notice. Antitrust Notice The information contain herein is in full compliance with the GSM Association’s antitrust compliance policy. V3.2.1 Page 1 of 11 GSM Association Non-confidential Official Document IR.22 - SCCP Signalling Aspects for Roaming Table of Contents 1 Introduction 3 1.1 Scope 3 1.2 Abbreviations 3 2 Numbering Plan Indicator of Global Title 3 3 SCCP Requirement for a Node in the International ISDN 4 4 Process for the Establishment of PLMN Signalling Relationships 5 4.1 Message Routing 6 4.2 Establishment Process 6 5. -

Mobile Broadband Explosion, Rysavy Research/4G Americas, August 2013 Page 2 Advanced Receivers
Table of Contents INTRODUCTION........................................................................................................ 4 DATA EXPLOSION ..................................................................................................... 7 Data Consumption ................................................................................................... 7 Cloud Computing ................................................................................................... 10 Technology Drives Demand ..................................................................................... 11 Wireless Vs. Wireline .............................................................................................. 11 Bandwidth Management ......................................................................................... 14 Market and Deployment .......................................................................................... 16 SPECTRUM DEVELOPMENTS .................................................................................... 18 Incentive Auctions ................................................................................................. 20 NTIA-Managed Spectrum ........................................................................................ 20 3550 to 3650 MHz “Small-Cell” Band ........................................................................ 20 Harmonization ....................................................................................................... 21 Unlicensed Spectrum ............................................................................................. -

Network Architecture
Chapter 1 Network Architecture This section gives an overview of the most important entities in a GSM network and the different protocols that are used between these entities. A single GSM network is often referred to as a Public Land Mobile Network (PLMN). This is the network operated by a single provider in a single region. In most countries each provider maintains a single PLMN, but in certain large countries, like the USA, several PLMNs can be maintained by a single provider. A PLMN manages all traffic between mobile phones and all traffic between mobile phones and the other land networks. These land networks can either be the Public Switched Telephone Network (PSTN), an ISDN network, or the Internet. Figure 1.1 shows an overview of all the entities in a GSM network. These entities are often subdivided between three “domains”; the Mobile Station (MS) – i.e. mobile phones – , the Base Station Subsytem (BSS) and the Network Switching Subsystem (NSS). We will now look at each of these in more detail. 1.1 Mobile Station (MS) The Mobile Station (MS) is the subscribers module most people are familiar with. It consists of both some Mobile Equipment (ME) and a Subscriber Identity Module (SIM). Both are needed for the Mobile Station (MS) to function in the GSM network. Hence MS = ME+SIM. 1.1.1 Mobile Equipment (ME) The Mobile Equipment (ME) is simply the GSM phone people use to make and receive calls in a cellular network. It is basically a transmitter-receiver unit that is independent from network providers1. -

We Know Where You Are!
2016 8th International Conference on Cyber Conflict Permission to make digital or hard copies of this publication for internal use within NATO and for personal or educational use when for non-profit or non-commercial Cyber Power purposes is granted providing that copies bear this notice and a full citation on the N.Pissanidis, H.Rõigas, M.Veenendaal (Eds.) first page. Any other reproduction or transmission requires prior written permission by NATO CCD COE. 2016 © NATO CCD COE Publications, Tallinn We Know Where You Are! Siddharth Prakash Rao Dr Silke Holtmanns Department of Computer Science Bell Labs, Nokia Aalto University, Finland Espoo, Finland [email protected] [email protected] Dr Ian Oliver Dr Tuomas Aura Bell Labs, Nokia Department of Computer Science Espoo, Finland Aalto University, Finland [email protected] [email protected] Abstract: Mobile network technologies require some degree of tracking of user location, specifically user equipment tracking, as part of their fundamental mechanism of working. Without this basic function, features such as hand-over between cells would not work. Since mobile devices are typically associated with a single person, this provides a potential mechanism for user location surveillance. Network operators are bound by strict privacy legislation. However, spying by certain agencies, hackers and even advertisers without the users’ or operators’ knowledge has become a serious issue. In this article, we introduce and explain all known recent attacks on mobile networks that compromised user privacy. We focus on attacks using the Signalling System 7 (SS7) protocol as the interconnection interface between operators mainly in GSM networks. -

GSM – Artikkel
International Journal of Digital Evidence Spring 2003, Volume 2, Issue 1 Forensics and the GSM mobile telephone system Svein Yngvar Willassen, M.Sc, Senior Investigator, Computer Forensics, Ibas AS Abstract The GSM system has become the most popular system for mobile communication in the world. Criminals commonly use GSM phones, and it is therefore a need for forensic investigators to understand which evidence can be obtained from the GSM system. This paper briefly explains the basics of the GSM system. Evidence items that can be obtained from the Mobile Equipment, the SIM and the core network are explored. Tools to extract such evidence from the components of the system exist, but there is a need to develop more sound forensic procedures and tools for extracting such evidence. The paper concludes with a short presentation on the future UMTS system, which largely builds on the design of GSM. 1.0 Introduction With GSM, systems for mobile communication reached a global scale. In the western world, it seems everyone has their own mobile phone, and GSM has taken more and more of the market. GSM allows users to roam seamlessly between networks, and separate the user identity from the phone equipment. In addition the GSM system provides the functional basis for the 3rd generation mobile system, UMTS. All these factors make it important for forensic investigators to understand how the GSM system works, and how evidence can be extracted from it. Criminals took the step into the mobile age a long time ago, and information from the mobile system can give the investigator crucial information on the criminal’s actions. -

Automatic Handover Control for Distributed Load Balancing In
Automatic Handover Control for Distributed Load Balancing in Mobile Communication Network 1 1, 1 Dina Farouk ALtayeb Ali , Fatima abdelgani Mustafa Mohamed Osman Mustafa Fdolelsid 1Future University, Faculty of Engineering, Department of Computer Engineering ABSTRACT: Due to technology and its daily continuous advancing and enhancement the users dealing with it are hungry for the best and better quality of service and this demand never stops, from this point came the idea of my research which aims to enhance the mobile network using the LOAD BALANCE and its algorithm to make it better ,in my research am requiring a HANDOVER process to be involved to get the best results , the simulation was implemented by MATLAP software to implement the two systems the normal system and the system with the load balance, result and graphs also came from the MATLAP software, one of the load balance methods was used and it’s the round robin method with all the needed variables based on the quantum or time slice. It’s the round robin method that helped to get better results first reducing the execution timing by (722626 MS) and improvement in the blocking probability and reduce it by 20% Introduction: Due to rapid change in technology the demand for better and faster cellular communication also increases. This growth in field of cellular communication has led to increase intensive research toward and development toward cellular system. The main reason of this growth is newly concept of mobile terminal and user mobility. The main characteristics of cellular communication system offer user maximum freedom of movement while using cell phones (mobiles). -

SIM/USIM Cards
SIM/USIM cards Samia Bouzefrane [email protected] CEDRIC Lab CNAM http://cedric.cnam.fr/~bouzefra 11 [email protected] Agenda - Introduction to GSM network - Introduction to SIM cards - SIM card services - Security - File systems of SIM cards 22 [email protected] Introduction to GSM network 33 [email protected] GSM - Early 1980’s, several cellular networks in Europe - the systems are incompatible from one country to another - Consequences : - mobile equipements are limited to the frontiers - limited market -Creation of « Group Special Mobile » to: •Increase the quality of service • international support : roaming • new functionalities • provide terminals and services with low cost 44 [email protected] GSM Standardization in 1982 : called « Group Special Mobile » Since 1989, the ETSI (European Telecommunications Standard Institute) provides the spécifications of GSM and of UMTS ( Universal Mobile Telecommunications System , 3rd generation ntework). ETSI is at Sophia Antipolis (Nice, France). 1991 : becomes an international standard called « Global System for Mobile communications » In Europe, the GSM standard uses frequency bandwidth of 900 MHz and 1800 MHz. In US, the bandwidth used is of 1900 MHz. Tri-band : cell phones are usable in Europe and US (3 frequencies) Bi-band : cell phones are usable only in Europe. The GSM standard allows a maximal rate of 9,6 kbps => transmission of voice, of data, text messages ( SMS , Short Message Service ) or multimedia messages ( MMS , Multimedia Message Service ). 55 [email protected] Cell network principle A cellular network is based on cells, Each cell covers a geographical area. A cell: hundred of meters (urban zone), thirty kms (rural zone ). -

Handover in a Mobile Wireless Communication Network –A Review Phase DOI
/ijcci1912 10.34256 RESEARCH ARTICLE RESEARCH Handover in a mobile wireless communication network –A Review Phase DOI: Rebin Abdullah Saeed a,* a PG Student, Department of Information Technology, Lebanese French University, Erbil, Kurdistan Region, Iraq *Corresponding Author ABSTRACT: Mobility is the features of mobile communication that makes it desirable by all [email protected] and varied. The whole world is now attractive in wireless communication as it provides (Rebin Abdullah Saeed) users' ability to communicate on-the-go. IT is accomplished by transferring users from a radio network to another. This process is called handover. Handover occurs by adjusting Received : 18-04-2019 the duration of soft handovers, the size of the areas and either by cell crossing or by Accepted : 20-05-2019 deterioration in the signal quality of the current channel — the brief overview of handover, Handover in WiMAX and LTE, types of handover, handover types solutions, usually used handover parameters, some methods employed in the literature and I contemporary the convergent fact for continuance in the area of mobile wireless communication Handover. Keywords: Wireless Communication Network, WiMAX, LTE, Handover, GSM and CDMA 1. Introduction considering all the parameters properly to ensure QoS is not affected and unnecessary handover is avoided. Handover is a progression in mobile communications and telecommunications in which a 2. The classification of Handover is based on the connected a data session, or cellular call is transferred from following factors one cell site (base station) to another without disconnecting the session. Cellular services are based on handover and 2.1 Access Technology mobility, permitting the user to be progressed from one cell 2.1.1 Horizontal Handover position range to another or to be moved to the nearest cell position for better action [1, 2, 3].