TLS for DNS Privacy in Practice
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Email Transport Encryption STARTTLS Vs. DANE Vs. MTA-STS
Email Transport Encryption STARTTLS vs. DANE vs. MTA-STS Delimitation This document deals with the encrypted transport of messages between two email servers. Encryption during transport is crucial for a basic level of security for the exchange of messages. The exchange of messages between an email client and a server or the end-to-end encryption of messages are not covered in this article. If the aim is to create a secure overall system, these aspects should be considered in addition to the recommendations in this article. Initial situation When the first standard for the Simple Mail Transfer Protocol (in short: SMTP) was adopted, encryption of the transport was not included. All messages were exchanged as plain text between the servers. They were thus basically readable for anyone who could tap into the data exchange between the two servers. This only changed with the introduction of the SMTP Service Extensions for Extend SMTP (ESMTP for short), which made it possible to choose encrypted transport as an opportunistic feature of data exchange. Opportunistic, because it had to be assumed that not all servers would be able to handle transport encryption. They should only encrypt when it is opportune; encryption is not mandatory. To indicate the basic ability to encrypt to a sending server, it was agreed that the receiving server should send the keyword STARTTLS at the beginning of an ESMTP transport session. STARTTLS STARTTLS can encrypt the transport between two email servers. The receiving server signals the sending server that it is capable of encrypting after a connection is established and in the ESMTP session. -
MTA STS Improving Email Security.Pdf
Improving Email Security with the MTA-STS Standard By Brian Godiksen An Email Best Practices Whitepaper CONTENTS Executive Overview 03 Why Does Email Need Encryption in Transit? 04 The Problem with “Opportunistic Encryption” 07 The Anatomy of a Man-in-the-Middle Attack 08 The Next Major Step with Email Encryption: MTA-STS 10 What Steps Should Senders Take to Adopt MTA-STS? 11 About SocketLabs 12 Brian Godiksen Brian has been helping organizations optimize email deliverability since joining SocketLabs in 2011. He currently manages a team of deliverability analysts that consult with customers on best infrastructure practices, including email authentication implementation, bounce processing, IP address warm-up, and email marketing list management. Brian leads the fight against spam and email abuse at SocketLabs by managing compliance across the platform. He is an active participant in key industry groups such as M3AAWG and the Email Experience Council. You can read more of Brian’s content here on the SocketLabs website. ©2019 SocketLabs 2 Executive The Edward Snowden leaks of 2013 opened many peoples’ eyes to the fact that mass surveillance was possible by Overview intercepting and spying on email transmissions. Today, compromised systems, database thefts, and technology breaches remain common fixtures in news feeds around the world. As a natural response, the technology industry is rabidly focused on improving the security and encryption of communications across all platforms. Since those early days of enlightenment, industry experts have discussed and attempted a variety of new strategies to combat “pervasive monitoring” of email channels. While pervasive monitoring assaults can take many forms, the most prominent forms of interference were man-in-the-middle (MitM) attacks. -

HTTP2 Explained
HTTP2 Explained Daniel Stenberg Mozilla Corporation [email protected] ABSTRACT credits to everyone who helps out! I hope to make this document A detailed description explaining the background and problems better over time. with current HTTP that has lead to the development of the next This document is available at http://daniel.haxx.se/http2. generation HTTP protocol: HTTP 2. It also describes and elaborates around the new protocol design and functionality, 1.3 License including some implementation specifics and a few words about This document is licensed under the the future. Creative Commons Attribution 4.0 This article is an editorial note submitted to CCR. It has NOT license: been peer reviewed. The author takes full responsibility for this http://creativecommons.org/licenses/by/4.0/ article’s technical content. Comments can be posted through CCR Online. 2. HTTP Today Keywords HTTP 1.1 has turned into a protocol used for virtually everything HTTP 2.0, security, protocol on the Internet. Huge investments have been done on protocols and infrastructure that takes advantage of this. This is taken to the 1. Background extent that it is often easier today to make things run on top of HTTP rather than building something new on its own. This is a document describing http2 from a technical and protocol level. It started out as a presentation I did in Stockholm in April 2014. I've since gotten a lot of questions about the contents of 2.1 HTTP 1.1 is Huge that presentation from people who couldn't attend, so I decided to When HTTP was created and thrown out into the world it was convert it into a full-blown document with all details and proper probably perceived as a rather simple and straight-forward explanations. -

Communication & Network Security
6/13/19 Communication & Network Security MIS-5903 http://community.mis.temple.edu/mis5903sec011s17/ OSI vs. TCP/IP Model • Transport also called Host-to-Host in TCP/IP model. Encapsulation • System 1 is a “subject” (client) • System 2 has the “object” (server) 1 6/13/19 OSI Reference Notice: • Segments • Packets (Datagrams) • Frames • Bits Well known ports Protocol TCP/UDP Port Number File Transfer Protocol (FTP) (RFC 959) TCP 20/21 Secure Shell (SSH) (RFC 4250-4256) TCP 22 Telnet (RFC TCP 23 854) Simple Mail Transfer Protocol (SMTP) (RFC 5321) TCP 25 Domain Name System (DNS) (RFC 1034-1035) TCP/UDP 53 Dynamic Host Configuration Protocol (DHCP) (RFC 2131) UDP 67/68 Trivial File Transfer Protocol (TFTP) (RFC 1350) UDP 69 Hypertext Transfer Protocol (HTTP) (RFC 2616) TCP 80 Post Office Protocol (POP) version 3 (RFC 1939) TCP 110 Network Time Protocol (NTP) (RFC 5905) UDP 123 NetBIOS (RFC TCP/UDP 1001-1002) 137/138/139 Internet Message Access Protocol (IMAP) (RFC 3501) TCP 143 Well known ports (continued) Protocol TCP/UDP Port Number Simple Network Management Protocol (SNMP) UDP (RFC 1901-1908, 3411-3418) 161/162 Border Gateway Protocol (BGP) (RFC 4271) TCP 179 Lightweight Directory Access Protocol (LDAP) (RFC 4510) TCP/UDP 389 Hypertext Transfer Protocol over SSL/TLS (HTTPS) (RFC 2818) TCP 443 Line Print Daemon (LPD) TCP 515 Lightweight Directory Access Protocol over TLS/SSL (LDAPS) (RFC 4513) TCP/UDP 636 FTP over TLS/SSL (RFC 4217) TCP 989/990 Microsoft SQL Server TCP 1433 Oracle Server TCP 1521 Microsoft Remote Desktop Protocol (RDP) TCP 3389 • http://www.iana.org/assignments/service-names-port- numbers/service-names-port-numbers.xml. -

Empfehlungen Für Den Einsatz Von Transportverschlüsselung Zwischen Mailservern
Empfehlungen für den Einsatz von Transportverschlüsselung zwischen Mailservern 11.08.2017 Empfehlungen für Transportverschlüsselung zwischen Mailservern Seite 2 von 19 Dokument-Informationen Autoren Antje Bendrich, Jürgen Brauckmann, Lars Weber, Marc Thomas, Stefan Kelm Dateiname smtp-transportverschluesslung.pdf letzte Bearbeitung 15. August 2017 Seitenzahl 19 Version Datum Autor(en) Änderungen 0.1 1.1.1970 Marc Thomas Formatvorlage 0.2 28.11.2016 Marc Thomas Struktur, Inhalt 0.3 07.12.2016 Lars Weber Kapitel 2.4, 3 0.4 24.02.2017 Marc Thomas Kapitel 4 0.5 27.03.2017 Stefan Kelm QA 0.6 28.03.2017 Antje Bendrich QA 0.7 01.06.2017 Jürgen Brauckmann QA 0.8 13.06.2017 Lars Weber Kapitel 2.4.3 0.9 11.08.2017 Lars Weber Kapitel 2.4 überarbeitet ©2017 by DFN-CERT Services GmbH / All Rights reserved. Stand: 11.08.2017 Empfehlungen für Transportverschlüsselung zwischen Mailservern Seite 3 von 19 Inhaltsverzeichnis 1. Einleitung 4 2. TLS-Konfiguration 4 2.1. SSL/TLS-Protokolle . .5 2.2. SSL/TLS-Algorithmen . .6 2.3. SSL/TLS-Parameter . .7 2.4. MTA-Konfiguration . .8 2.4.1. Grenzen der Konfiguration . .8 2.4.2. Postfix . .9 2.4.3. Exim . 11 3. DNS-based Authentication of Named Entities (DANE) 14 3.1. Postfix . 15 3.2. Exim . 15 4. Best-Practices-Konfiguration 16 4.1. Postfix . 16 4.2. Exim . 17 A. Quellen 19 ©2017 by DFN-CERT Services GmbH / All Rights reserved. Stand: 11.08.2017 Empfehlungen für Transportverschlüsselung zwischen Mailservern Seite 4 von 19 1. Einleitung Moderne Bürokommunikation läuft zum großen Teil über E-Mail. -

Applied Crypto Hardening
Applied Crypto Hardening Wolfgang Breyha, David Durvaux, Tobias Dussa, L. Aaron Kaplan, Florian Mendel, Christian Mock, Manuel Koschuch, Adi Kriegisch, Ulrich Pöschl, Ramin Sabet, Berg San, Ralf Schlatterbeck, Thomas Schreck, Alexander Würstlein, Aaron Zauner, Pepi Zawodsky (University of Vienna, CERT.be, KIT-CERT, CERT.at, A-SIT/IAIK, coretec.at,FH Campus Wien, VRVis, MilCERT Austria, A-Trust, Runtux.com,Friedrich-Alexander University Erlangen-Nuremberg, azet.org, maclemon.at) April 25, 2017 Contents 1. Abstract 5 1.1. Acknowledgements ........................................ 6 2. Introduction 8 2.1. Audience .............................................. 8 2.2. Related publications ........................................ 8 2.3. How to read this guide ....................................... 8 2.4. Disclaimer and scope ........................................ 9 2.4.1. Scope ............................................ 10 2.5. Methods ............................................... 11 3. Practical recommendations 12 3.1. Webservers ............................................. 12 3.1.1. Apache ........................................... 12 3.1.2. lighttpd ........................................... 13 3.1.3. nginx ............................................ 14 3.1.4. Cherokee .......................................... 15 3.1.5. MS IIS ............................................ 17 3.2. SSH ................................................. 20 3.2.1. OpenSSH .......................................... 20 3.2.2. Cisco ASA ......................................... -
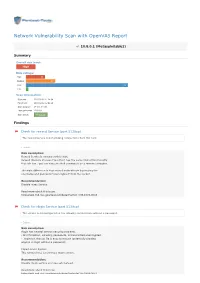
Network Vulnerability Scan with Openvas Report
Network Vulnerability Scan with OpenVAS Report 10.8.0.1 (Metasploitable2) Summary Overall risk level: High Risk ratings: High: 13 Medium: 20 Low: 69 Info: 1 Scan information: Start time: 2018-03-02 11:24:54 Finish time: 2018-03-02 12:02:48 Scan duration: 37 min, 54 sec Tests performed: 103/103 Scan status: Finished Findings Check for rexecd Service (port 512/tcp) The rexecd Service is not allowing connections from this host. Details Risk description: Rexecd Service is running at this Host. Rexecd (Remote Process Execution) has the same kind of functionality that rsh has : you can execute shell commands on a remote computer. The main difference is that rexecd authenticate by reading the username and password *unencrypted* from the socket. Recommendation: Disable rexec Service. Read more about this issue: https//web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-1999-0618 Check for rlogin Service (port 513/tcp) The service is misconfigured so it is allowing conntections without a password. Details Risk description: rlogin has several serious security problems, - All information, including passwords, is transmitted unencrypted. - .rlogin (or .rhosts) file is easy to misuse (potentially allowing anyone to login without a password) Impact Level: System This remote host is running a rlogin service. Recommendation: Disable rlogin service and use ssh instead. Read more about this issue: https//web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-1999-0651 https//web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-1999-0651 http//en.wikipedia.org/wiki/Rlogin http//www.ietf.org/rfc/rfc1282.txt DistCC Detection (port 3632/tcp) No evidence Details Risk description: DistCC is a program to distribute builds of C, C++, Objective C or Objective C++ code across several machines on a network. -

Implementing TLS on the CLEARSWIFT SECURE Email Gateway
Unifying Information Security Implementing TLS on the CLEARSWIFT SECURE Email Gateway Contents 1 Introduction ................................................................................................................................ 3 2 Understanding TLS .................................................................................................................... 4 3 Clearswift’s Application of TLS ............................................................................................. 5 3.1 Opportunistic TLS .............................................................................................................. 5 3.2 Mandatory TLS .................................................................................................................... 5 4 Getting Started .......................................................................................................................... 8 5 Creating a Certificate Signing Request .............................................................................. 9 5.1 What is a CSR? .................................................................................................................... 9 5.2 Creating a Private Key and CSR using OpenSSL ....................................................... 9 5.2.1 Generating the Private Key .................................................................................. 10 5.2.2 Generating the CSR ................................................................................................. 11 6 Using your CSR to purchase -
Applied Crypto Hardening
DrAFT REvision: ea089c8 (2014-01-11 22:11:44 +0100) AarON Kaplan Applied Crypto HarDENING WOLFGANG BrEyha, David Durvaux, TOBIAS Dussa, L. AarON Kaplan, Florian Mendel, Christian Mock, Manuel Koschuch, Adi Kriegisch, Ulrich Pöschl, Ramin Sabet, BerG San, Ralf Schlatterbeck, Thomas Schreck, AarON Zauner, Pepi Zawodsky (University OF Vienna, CERT.be, KIT-CERT, CERT.at, A-SIT/IAIK, CORetec.at, FH Campus Wien, VRVis, MilCERT Austria, A-Trust, Runtux.com, Friedrich-AleXANDER University Erlangen-NurEMBERg, azet.org, maclemon.at) January 13, 2014 DrAFT REvision: ea089c8 (2014-01-11 22:11:44 +0100) AarON Kaplan DrAFT REvision: ea089c8 (2014-01-11 22:11:44 +0100) AarON Kaplan Do NOT TALK UNENCRYPTED Applied Crypto HarDENING • DrAFT REvision: ea089c8 (2014-01-11 22:11:44 +0100) AarON Kaplan PAGE 2 OF 81 DrAFT REvision: ea089c8 (2014-01-11 22:11:44 +0100) AarON Kaplan DrAFT REvision: ea089c8 (2014-01-11 22:11:44 +0100) AarON Kaplan AcknoWLEDGEMENTS WE WOULD LIKE TO EXPRESS OUR THANKS TO THE FOLLOWING REVIEWERS AND PEOPLE WHO HAVE GENEROUSLY OffERED THEIR TIME AND INTEREST (in ALPHABETICAL ORder): BrOwn, Scott Millauer, TOBIAS Brulebois, Cyril O’Brien, Hugh Dirksen-Thedens, Mathis Pacher, Christoph DulaunoY, AleXANDRE Palfrader, Peter Gühring Philipp Pape, TOBIAS (layout) Grigg, IAN Petukhova, Anna (Logo) Horenbeck, Maarten Pichler, Patrick Huebl, AxEL Roeckx, Kurt Kovacic, Daniel Seidl, Eva (PDF layout) Lenzhofer, Stefan Wagner, Sebastian (“SEBIX”) Lorünser, Thomas Zangerl, AleXANDER The REVIEWERS DID REVIEW PARTS OF THE DOCUMENT IN THEIR AREA OF Expertise; ALL REMAINING ERRORS IN THIS DOCUMENT ARE THE SOLE RESPONSIBILITY OF THE PRIMARY authors. Applied Crypto HarDENING • DrAFT REvision: ea089c8 (2014-01-11 22:11:44 +0100) AarON Kaplan PAGE 3 OF 81 DrAFT REvision: ea089c8 (2014-01-11 22:11:44 +0100) AarON Kaplan DrAFT REvision: ea089c8 (2014-01-11 22:11:44 +0100) AarON Kaplan AbstrACT “Unfortunately, THE COMPUTER SECURITY AND CRYPTOLOGY COMMUNITIES HAVE DRIFTED APART OVER THE LAST 25 years. -

Measuring and Securing Cryptographic Deployments
University of Pennsylvania ScholarlyCommons Publicly Accessible Penn Dissertations 2019 Measuring And Securing Cryptographic Deployments Luke Taylor Valenta University of Pennsylvania, [email protected] Follow this and additional works at: https://repository.upenn.edu/edissertations Part of the Computer Sciences Commons Recommended Citation Valenta, Luke Taylor, "Measuring And Securing Cryptographic Deployments" (2019). Publicly Accessible Penn Dissertations. 3507. https://repository.upenn.edu/edissertations/3507 This paper is posted at ScholarlyCommons. https://repository.upenn.edu/edissertations/3507 For more information, please contact [email protected]. Measuring And Securing Cryptographic Deployments Abstract This dissertation examines security vulnerabilities that arise due to communication failures and incentive mismatches along the path from cryptographic algorithm design to eventual deployment. I present six case studies demonstrating vulnerabilities in real-world cryptographic deployments. I also provide a framework with which to analyze the root cause of cryptographic vulnerabilities by characterizing them as failures in four key stages of the deployment process: algorithm design and cryptanalysis, standardization, implementation, and endpoint deployment. Each stage of this process is error-prone and influenced by various external factors, the incentives of which are not always aligned with security. I validate the framework by applying it to the six presented case studies, tracing each vulnerability back to communication -

Applied Crypto Hardening
Applied Crypto HarDENING WOLFGANG BrEyha, David Durvaux, TOBIAS Dussa, L. AarON Kaplan, Florian Mendel, Christian Mock, Manuel Koschuch, Adi Kriegisch, Ulrich Pöschl, Ramin Sabet, BerG San, Ralf Schlatterbeck, Thomas Schreck, AleXANDER Würstlein, AarON Zauner, Pepi Zawodsky (University OF Vienna, CERT.be, KIT-CERT, CERT.at, A-SIT/IAIK, CORetec.at, FH Campus Wien, VRVis, MilCERT Austria, A-Trust, Runtux.com, Friedrich-AleXANDER University Erlangen-NurEMBERg, azet.org, maclemon.at) NoVEMBER 10, 2016 Do NOT TALK UNENCRYPTED Applied Crypto HarDENING PAGE 2 OF 111 AcknoWLEDGEMENTS WE WOULD LIKE TO EXPRESS OUR THANKS TO THE FOLLOWING REVIEWERS AND PEOPLE WHO HAVE GENEROUSLY OffERED THEIR TIME AND INTEREST (in ALPHABETICAL ORder): BrOwn, Scott Pacher, Christoph Brulebois, Cyril Palfrader, Peter Dirksen-Thedens, Mathis Pape, TOBIAS (layout) DulaunoY, AleXANDRE Petukhova, Anna (Logo) Gühring Philipp Pichler, Patrick Grigg, IAN Riebesel, Nicolas Haslinger, Gunnar Roeckx, Kurt Huebl, AxEL Roesen, Jens Kovacic, Daniel Rublik, Martin Lenzhofer, Stefan Schüpany, Mathias Lorünser, Thomas Schwarz, René («DigNative») Maass, Max Seidl, Eva (PDF layout) Mehlmauer, Christian VAN Horenbeeck, Maarten Millauer, TOBIAS Wagner, Sebastian («sebix») Mirbach, AndrEAS Zangerl, AleXANDER O’Brien, Hugh The REVIEWERS DID REVIEW PARTS OF THE DOCUMENT IN THEIR AREA OF Expertise; ALL REMAINING ERRORS IN THIS DOCUMENT ARE THE SOLE RESPONSIBILITY OF THE PRIMARY authors. Applied Crypto HarDENING PAGE 3 OF 111 AbstrACT “Unfortunately, THE COMPUTER SECURITY AND CRYPTOLOGY COMMUNITIES HAVE DRIFTED APART OVER THE LAST 25 years. Security PEOPLE DON’T ALWAYS UNDERSTAND THE AVAILABLE CRYPTO tools, AND CRYPTO PEOPLE DON’T ALWAYS UNDERSTAND THE Real-world PRoblems.” — Ross Anderson IN [And08] This GUIDE AROSE OUT OF THE NEED FOR SYSTEM ADMINISTRATORS TO HAVE AN updated, solid, WELL Re- SEARCHED AND thought-thrOUGH GUIDE FOR CONfiGURING SSL, PGP, SSH AND OTHER CRYPTOGRAPHIC TOOLS IN THE post-SnoWDEN age. -

Network Working Group A. Mohaisen Internet-Draft SUNY Buffalo Intended Status: Informational A
Network Working Group A. Mohaisen Internet-Draft SUNY Buffalo Intended status: Informational A. Mankin Expires: April 20, 2016 Verisign Labs October 18, 2015 Evaluation of Privacy for DNS Private Exchange draft-am-dprive-eval-02 Abstract The set of DNS requests that an individual makes can provide a monitor with a large amount of information about that individual. DNS Private Exchange (DPRIVE) aims to deprive this actor of this information. This document describes methods for measuring the performance of DNS privacy mechanisms, particularly it provides methods for measuring effectiveness in the face of pervasive monitoring as defined in RFC7258. The document includes example evaluations for common use cases. Status of This Memo This Internet-Draft is submitted in full conformance with the provisions of BCP 78 and BCP 79. Internet-Drafts are working documents of the Internet Engineering Task Force (IETF). Note that other groups may also distribute working documents as Internet-Drafts. The list of current Internet- Drafts is at http://datatracker.ietf.org/drafts/current/. Internet-Drafts are draft documents valid for a maximum of six months and may be updated, replaced, or obsoleted by other documents at any time. It is inappropriate to use Internet-Drafts as reference material or to cite them other than as "work in progress." This Internet-Draft will expire on April 20, 2016. Copyright Notice Copyright (c) 2015 IETF Trust and the persons identified as the document authors. All rights reserved. This document is subject to BCP 78 and the IETF Trust's Legal Provisions Relating to IETF Documents (http://trustee.ietf.org/license-info) in effect on the date of publication of this document.