Security Now! #750 - 01-21-20 the Crypto Curveball
Total Page:16
File Type:pdf, Size:1020Kb

Load more
Recommended publications
-

Email Transport Encryption STARTTLS Vs. DANE Vs. MTA-STS
Email Transport Encryption STARTTLS vs. DANE vs. MTA-STS Delimitation This document deals with the encrypted transport of messages between two email servers. Encryption during transport is crucial for a basic level of security for the exchange of messages. The exchange of messages between an email client and a server or the end-to-end encryption of messages are not covered in this article. If the aim is to create a secure overall system, these aspects should be considered in addition to the recommendations in this article. Initial situation When the first standard for the Simple Mail Transfer Protocol (in short: SMTP) was adopted, encryption of the transport was not included. All messages were exchanged as plain text between the servers. They were thus basically readable for anyone who could tap into the data exchange between the two servers. This only changed with the introduction of the SMTP Service Extensions for Extend SMTP (ESMTP for short), which made it possible to choose encrypted transport as an opportunistic feature of data exchange. Opportunistic, because it had to be assumed that not all servers would be able to handle transport encryption. They should only encrypt when it is opportune; encryption is not mandatory. To indicate the basic ability to encrypt to a sending server, it was agreed that the receiving server should send the keyword STARTTLS at the beginning of an ESMTP transport session. STARTTLS STARTTLS can encrypt the transport between two email servers. The receiving server signals the sending server that it is capable of encrypting after a connection is established and in the ESMTP session. -
MTA STS Improving Email Security.Pdf
Improving Email Security with the MTA-STS Standard By Brian Godiksen An Email Best Practices Whitepaper CONTENTS Executive Overview 03 Why Does Email Need Encryption in Transit? 04 The Problem with “Opportunistic Encryption” 07 The Anatomy of a Man-in-the-Middle Attack 08 The Next Major Step with Email Encryption: MTA-STS 10 What Steps Should Senders Take to Adopt MTA-STS? 11 About SocketLabs 12 Brian Godiksen Brian has been helping organizations optimize email deliverability since joining SocketLabs in 2011. He currently manages a team of deliverability analysts that consult with customers on best infrastructure practices, including email authentication implementation, bounce processing, IP address warm-up, and email marketing list management. Brian leads the fight against spam and email abuse at SocketLabs by managing compliance across the platform. He is an active participant in key industry groups such as M3AAWG and the Email Experience Council. You can read more of Brian’s content here on the SocketLabs website. ©2019 SocketLabs 2 Executive The Edward Snowden leaks of 2013 opened many peoples’ eyes to the fact that mass surveillance was possible by Overview intercepting and spying on email transmissions. Today, compromised systems, database thefts, and technology breaches remain common fixtures in news feeds around the world. As a natural response, the technology industry is rabidly focused on improving the security and encryption of communications across all platforms. Since those early days of enlightenment, industry experts have discussed and attempted a variety of new strategies to combat “pervasive monitoring” of email channels. While pervasive monitoring assaults can take many forms, the most prominent forms of interference were man-in-the-middle (MitM) attacks. -

HTTP2 Explained
HTTP2 Explained Daniel Stenberg Mozilla Corporation [email protected] ABSTRACT credits to everyone who helps out! I hope to make this document A detailed description explaining the background and problems better over time. with current HTTP that has lead to the development of the next This document is available at http://daniel.haxx.se/http2. generation HTTP protocol: HTTP 2. It also describes and elaborates around the new protocol design and functionality, 1.3 License including some implementation specifics and a few words about This document is licensed under the the future. Creative Commons Attribution 4.0 This article is an editorial note submitted to CCR. It has NOT license: been peer reviewed. The author takes full responsibility for this http://creativecommons.org/licenses/by/4.0/ article’s technical content. Comments can be posted through CCR Online. 2. HTTP Today Keywords HTTP 1.1 has turned into a protocol used for virtually everything HTTP 2.0, security, protocol on the Internet. Huge investments have been done on protocols and infrastructure that takes advantage of this. This is taken to the 1. Background extent that it is often easier today to make things run on top of HTTP rather than building something new on its own. This is a document describing http2 from a technical and protocol level. It started out as a presentation I did in Stockholm in April 2014. I've since gotten a lot of questions about the contents of 2.1 HTTP 1.1 is Huge that presentation from people who couldn't attend, so I decided to When HTTP was created and thrown out into the world it was convert it into a full-blown document with all details and proper probably perceived as a rather simple and straight-forward explanations. -
Vmware Vrealize Configuration Manager Installation Guide Vrealize Configuration Manager 5.8
VMware vRealize Configuration Manager Installation Guide vRealize Configuration Manager 5.8 This document supports the version of each product listed and supports all subsequent versions until the document is replaced by a new edition. To check for more recent editions of this document, see http://www.vmware.com/support/pubs. EN-001815-00 vRealize Configuration Manager Installation Guide You can find the most up-to-date technical documentation on the VMware Web site at: Copyright http://www.vmware.com/support/ The VMware Web site also provides the latest product updates. If you have comments about this documentation, submit your feedback to: [email protected] © 2006–2015 VMware, Inc. All rights reserved. This product is protected by U.S. and international copyright and intellectual property laws. VMware products are covered by one or more patents listed at http://www.vmware.com/go/patents. VMware is a registered trademark or trademark of VMware, Inc. in the United States and/or other jurisdictions. All other marks and names mentioned herein may be trademarks of their respective companies. VMware, Inc. 3401 Hillview Ave. Palo Alto, CA 94304 www.vmware.com 2 VMware, Inc. Contents About This Book 5 Preparing to Install VCM 7 Typical or Advanced Installation 7 VCM Installation Configurations 8 Create VCM Domain Accounts 8 VCM Account Configuration 9 VCM Administrator Account 10 VCM User Accounts 10 Service Accounts 10 Network Authority Account 11 ECMSRSUser Account 12 SQL Server Permissions and Constructs 12 Gather Supporting Software -

Curriculum Vitae Di Tommaso Cucinotta
Curriculum Vitae: Prof. Tommaso Cucinotta Personal data Birth date and place: April 1974, Potenza (Italy) Phone: +39 (0)50 882 028 Skype Id: t.cucinotta E-mail: Home page: http:// retis . santannapisa .it/~tommaso Current status Dec 2015 to date: Associate Professor at the Real-Time Systems Laboratory (ReTiS) of Scuola Superiore Sant'Anna RESEARCH TOPICS & COMPETENCIES ❑ Real-time and reliable NoSQL Database systems for cloud services ❑ Adaptive resource management and scheduling in Cloud Computing & Network Function Virtualization infrastructures ❑ Artificial Intelligence and Machine Learning to support Data Center Operations in Cloud & NFV infrastructures ❑ Platforms for real-time data streaming and analytics ❑ Quality of service control for adaptive soft real-time applications, including multimedia and IMS systems ❑ Operating Systems for real-time and embedded applications and many-core and massively distributed systems ❑ Trusted computing and confidentiality in cloud computing ❑ Smart-cards: interoperability, protocols and architectures ❑ Digital signatures, biometrics identification, multicast security Experience highlights (details below) ❑ 7 Granted and 25 Filed EU and US Patents in the areas of security, resource management and scheduling ❑ 25 International Journal Publications, including IEEE Transaction on Computers, IEEE Transaction on Industrial Informatics and ACM Transactions on Embedded and Computing Systems ❑ 65 International Conference and Workshop Peer-reviewed Publications and 13 Book Chapters ❑ 3 EU Projects scientific -

Microsoft Windows Server 2008 PKI and Deploying the Ncipher Hardware Security Module
This is a joint nCipher and IdentIT authored whitepaper Microsoft Windows Server 2008 PKI and Deploying the nCipher Hardware Security Module Abstract This paper discusses the benefits that are unique to deploying the integrated solution of the Windows Server 2008 PKI and the nCipher nShield and netHSM hardware security modules (HSM). This includes the essential concepts and technologies used to deploy a PKI and the best practice security and life cycle key management features provided by nCipher HSMs.. MicrosofT WIndoWs server 2008 PKI and dePloyIng The nCipher hardWare seCurity Module Introduction...............................................................................................................................................................................................3 PKI – A Crucial Component to Securing e-commerce ......................................................................................................................4 Microsoft Windows Server 2008 ...............................................................................................................................................................4 nCipher Hardware Security Modules ......................................................................................................................................................4 Best.Practice.Security.–.nCipher.HSMs.with.Windows.Server.2008.PKI................................................................................5 Overview...............................................................................................................................................................................................................5 -

Invisimole: the Hidden Part of the Story Unearthing Invisimole’S Espionage Toolset and Strategic Cooperations
ESET Research white papers TLP: WHITE INVISIMOLE: THE HIDDEN PART OF THE STORY UNEARTHING INVISIMOLE’S ESPIONAGE TOOLSET AND STRATEGIC COOPERATIONS Authors: Zuzana Hromcová Anton Cherepanov TLP: WHITE 2 InvisiMole: The hidden part of the story CONTENTS 1 EXECUTIVE SUMMARY � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � 4 2 ATTACKS AND INVESTIGATION � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � 4 2.1 InvisiMole’s toolset ������������������������������������������������������������������������������������������������������������������������ 5 2.2 Cooperation between InvisiMole and Gamaredon . 5 3 BUILDING BLOCKS � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � � 6 3.1 Structure ������������������������������������������������������������������������������������������������������������������������������������������6 3.1.1 InvisiMole blobs . 6 3.1.2 Execution guardrails with DPAPI ���������������������������������������������������������������������������������7 3.2 Payload ��������������������������������������������������������������������������������������������������������������������������������������������8 3.2.1 TCP downloader ��������������������������������������������������������������������������������������������������������������9 3.2.2 DNS downloader . 9 3.2.3 RC2CL backdoor �������������������������������������������������������������������������������������������������������������13 -

Communication & Network Security
6/13/19 Communication & Network Security MIS-5903 http://community.mis.temple.edu/mis5903sec011s17/ OSI vs. TCP/IP Model • Transport also called Host-to-Host in TCP/IP model. Encapsulation • System 1 is a “subject” (client) • System 2 has the “object” (server) 1 6/13/19 OSI Reference Notice: • Segments • Packets (Datagrams) • Frames • Bits Well known ports Protocol TCP/UDP Port Number File Transfer Protocol (FTP) (RFC 959) TCP 20/21 Secure Shell (SSH) (RFC 4250-4256) TCP 22 Telnet (RFC TCP 23 854) Simple Mail Transfer Protocol (SMTP) (RFC 5321) TCP 25 Domain Name System (DNS) (RFC 1034-1035) TCP/UDP 53 Dynamic Host Configuration Protocol (DHCP) (RFC 2131) UDP 67/68 Trivial File Transfer Protocol (TFTP) (RFC 1350) UDP 69 Hypertext Transfer Protocol (HTTP) (RFC 2616) TCP 80 Post Office Protocol (POP) version 3 (RFC 1939) TCP 110 Network Time Protocol (NTP) (RFC 5905) UDP 123 NetBIOS (RFC TCP/UDP 1001-1002) 137/138/139 Internet Message Access Protocol (IMAP) (RFC 3501) TCP 143 Well known ports (continued) Protocol TCP/UDP Port Number Simple Network Management Protocol (SNMP) UDP (RFC 1901-1908, 3411-3418) 161/162 Border Gateway Protocol (BGP) (RFC 4271) TCP 179 Lightweight Directory Access Protocol (LDAP) (RFC 4510) TCP/UDP 389 Hypertext Transfer Protocol over SSL/TLS (HTTPS) (RFC 2818) TCP 443 Line Print Daemon (LPD) TCP 515 Lightweight Directory Access Protocol over TLS/SSL (LDAPS) (RFC 4513) TCP/UDP 636 FTP over TLS/SSL (RFC 4217) TCP 989/990 Microsoft SQL Server TCP 1433 Oracle Server TCP 1521 Microsoft Remote Desktop Protocol (RDP) TCP 3389 • http://www.iana.org/assignments/service-names-port- numbers/service-names-port-numbers.xml. -

Empfehlungen Für Den Einsatz Von Transportverschlüsselung Zwischen Mailservern
Empfehlungen für den Einsatz von Transportverschlüsselung zwischen Mailservern 11.08.2017 Empfehlungen für Transportverschlüsselung zwischen Mailservern Seite 2 von 19 Dokument-Informationen Autoren Antje Bendrich, Jürgen Brauckmann, Lars Weber, Marc Thomas, Stefan Kelm Dateiname smtp-transportverschluesslung.pdf letzte Bearbeitung 15. August 2017 Seitenzahl 19 Version Datum Autor(en) Änderungen 0.1 1.1.1970 Marc Thomas Formatvorlage 0.2 28.11.2016 Marc Thomas Struktur, Inhalt 0.3 07.12.2016 Lars Weber Kapitel 2.4, 3 0.4 24.02.2017 Marc Thomas Kapitel 4 0.5 27.03.2017 Stefan Kelm QA 0.6 28.03.2017 Antje Bendrich QA 0.7 01.06.2017 Jürgen Brauckmann QA 0.8 13.06.2017 Lars Weber Kapitel 2.4.3 0.9 11.08.2017 Lars Weber Kapitel 2.4 überarbeitet ©2017 by DFN-CERT Services GmbH / All Rights reserved. Stand: 11.08.2017 Empfehlungen für Transportverschlüsselung zwischen Mailservern Seite 3 von 19 Inhaltsverzeichnis 1. Einleitung 4 2. TLS-Konfiguration 4 2.1. SSL/TLS-Protokolle . .5 2.2. SSL/TLS-Algorithmen . .6 2.3. SSL/TLS-Parameter . .7 2.4. MTA-Konfiguration . .8 2.4.1. Grenzen der Konfiguration . .8 2.4.2. Postfix . .9 2.4.3. Exim . 11 3. DNS-based Authentication of Named Entities (DANE) 14 3.1. Postfix . 15 3.2. Exim . 15 4. Best-Practices-Konfiguration 16 4.1. Postfix . 16 4.2. Exim . 17 A. Quellen 19 ©2017 by DFN-CERT Services GmbH / All Rights reserved. Stand: 11.08.2017 Empfehlungen für Transportverschlüsselung zwischen Mailservern Seite 4 von 19 1. Einleitung Moderne Bürokommunikation läuft zum großen Teil über E-Mail. -

Game Programming Gems 7
Game Programming Gems 7 Edited by Scott Jacobs Charles River Media A part of Course Technology, Cengage Learning Australia • Brazil • Japan • Korea • Mexico • Singapore • Spain • United Kingdom • United States Publisher and General Manager, © 2008 Course Technology, a part of Cengage Learning. Course Technology PTR: Stacy L. Hiquet Associate Director of Marketing: ALL RIGHTS RESERVED. No part of this work covered by the copyright Sarah Panella herein may be reproduced, transmitted, stored, or used in any form or by any means graphic, electronic, or mechanical, including but not limited to Heather Manager of Editorial Services: photocopying, recording, scanning, digitizing, taping, Web distribution, Talbot information networks, or information storage and retrieval systems, except Marketing Manager: Jordan Casey as permitted under Section 107 or 108 of the 1976 United States Copyright Senior Acquisitions Editor: Emi Smith Act, without the prior written permission of the publisher. Project/Copy Editor: Kezia Endsley CRM Editorial Services Coordinator: Jen Blaney For product information and technology assistance, contact us at Cengage Learning Customer & Sales Support, 1-800-354-9706 Interior Layout Tech: Judith Littlefield Cover Designer: Tyler Creative Services For permission to use material from this text or product, CD-ROM Producer: Brandon Penticuff submit all requests online at cengage.com/permissions Further permissions questions can be emailed to Valerie Haynes Perry Indexer: [email protected] Proofreader: Sue Boshers Library of Congress Control Number: 2007939358 ISBN-13: 978-1-58450-527-3 ISBN-10: 1-58450-527-3 eISBN-10: 1-30527-676-0 Course Technology 25 Thomson Place Boston, MA 02210 USA Cengage Learning is a leading provider of customized learning solutions with office locations around the globe, including Singapore, the United Kingdom, Australia, Mexico, Brazil, and Japan. -

Applied Crypto Hardening
Applied Crypto Hardening Wolfgang Breyha, David Durvaux, Tobias Dussa, L. Aaron Kaplan, Florian Mendel, Christian Mock, Manuel Koschuch, Adi Kriegisch, Ulrich Pöschl, Ramin Sabet, Berg San, Ralf Schlatterbeck, Thomas Schreck, Alexander Würstlein, Aaron Zauner, Pepi Zawodsky (University of Vienna, CERT.be, KIT-CERT, CERT.at, A-SIT/IAIK, coretec.at,FH Campus Wien, VRVis, MilCERT Austria, A-Trust, Runtux.com,Friedrich-Alexander University Erlangen-Nuremberg, azet.org, maclemon.at) April 25, 2017 Contents 1. Abstract 5 1.1. Acknowledgements ........................................ 6 2. Introduction 8 2.1. Audience .............................................. 8 2.2. Related publications ........................................ 8 2.3. How to read this guide ....................................... 8 2.4. Disclaimer and scope ........................................ 9 2.4.1. Scope ............................................ 10 2.5. Methods ............................................... 11 3. Practical recommendations 12 3.1. Webservers ............................................. 12 3.1.1. Apache ........................................... 12 3.1.2. lighttpd ........................................... 13 3.1.3. nginx ............................................ 14 3.1.4. Cherokee .......................................... 15 3.1.5. MS IIS ............................................ 17 3.2. SSH ................................................. 20 3.2.1. OpenSSH .......................................... 20 3.2.2. Cisco ASA ......................................... -
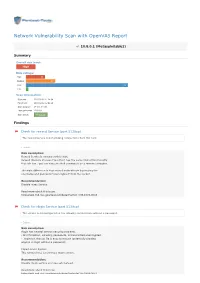
Network Vulnerability Scan with Openvas Report
Network Vulnerability Scan with OpenVAS Report 10.8.0.1 (Metasploitable2) Summary Overall risk level: High Risk ratings: High: 13 Medium: 20 Low: 69 Info: 1 Scan information: Start time: 2018-03-02 11:24:54 Finish time: 2018-03-02 12:02:48 Scan duration: 37 min, 54 sec Tests performed: 103/103 Scan status: Finished Findings Check for rexecd Service (port 512/tcp) The rexecd Service is not allowing connections from this host. Details Risk description: Rexecd Service is running at this Host. Rexecd (Remote Process Execution) has the same kind of functionality that rsh has : you can execute shell commands on a remote computer. The main difference is that rexecd authenticate by reading the username and password *unencrypted* from the socket. Recommendation: Disable rexec Service. Read more about this issue: https//web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-1999-0618 Check for rlogin Service (port 513/tcp) The service is misconfigured so it is allowing conntections without a password. Details Risk description: rlogin has several serious security problems, - All information, including passwords, is transmitted unencrypted. - .rlogin (or .rhosts) file is easy to misuse (potentially allowing anyone to login without a password) Impact Level: System This remote host is running a rlogin service. Recommendation: Disable rlogin service and use ssh instead. Read more about this issue: https//web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-1999-0651 https//web.nvd.nist.gov/view/vuln/detail?vulnId=CVE-1999-0651 http//en.wikipedia.org/wiki/Rlogin http//www.ietf.org/rfc/rfc1282.txt DistCC Detection (port 3632/tcp) No evidence Details Risk description: DistCC is a program to distribute builds of C, C++, Objective C or Objective C++ code across several machines on a network.