A Method for Comparative Analysis of Trusted Execution Environments
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Fact Sheet: the Next Generation of Computing Has Arrived
News Fact Sheet The Next Generation of Computing Has Arrived: Performance to Power Amazing Experiences The new 5th Generation Intel® Core™ processor family is Intel’s latest wave of 14nm processors, delivering improved system and graphics performance, more natural and immersive user experiences, and enabling longer battery life compared to previous generations. The release of the 5th Generation Intel Core technology includes 14 new processors for consumers and businesses, including 10 new 15W processors with Intel® HD Graphics and four new 28W products with Intel® Iris™ Graphics. The 5th Generation Intel Core processor is purpose-built for the next generation of compute devices offering a thinner, lighter and more efficient experience across diverse form factors, including traditional notebooks, 2 in 1s, Ultrabooks™, Chromebooks, all-in-one desktop PCs and mini PCs. With the 5th Generation Intel Core processor availability, the “Broadwell” microarchitecture is expected to be the fastest mobile transition in company history to offer consumers a broad selection and availability of devices. Intel also started shipping its next generation 14nm processor for tablets, codenamed “Cherry Trail”, to device manufacturers. The new system on a chip (SoC) offers 64-bit computing, improved graphics with Intel® Generation 8-LP graphics, great performance and battery life for mainstream tablets. The platform offers world-class modem capabilities with LTE-Advanced on Intel® XMM™ 726x platform, which supports Cat-6 speeds and carrier aggregation. Customers will introduce new products based on this platform starting in the first half of this year. Key benefits of the 5th Generation Intel Core family and the next-generation 14nm processor for tablets include: Powerful Performance. -

VOLUME V INFORMATIQUE NON AMERICAINE Première Partie Par L' Ingénieur Général De L'armement BOUCHER Henri TABLE
VOLUME V INFORMATIQUE NON AMERICAINE Première partie par l' Ingénieur Général de l'Armement BOUCHER Henri TABLE DES MATIERES INFORMATIQUE NON AMERICAINE Première partie 731 Informatique européenne (statistiques, exemples) 122 700 Histoire de l'Informatique allemande 1 701 Petits constructeurs 5 702 Les facturières de Kienzle Data System 16 703 Les minis de gestion de Nixdorf 18 704 Siemens & Halske AG 23 705 Systèmes informatiques d'origine allemande 38 706 Histoire de l'informatique britannique 40 707 Industriels anglais de l'informatique 42 708 Travaux des Laboratoires d' Etat 60 709 Travaux universitaires 63 710 Les coeurs synthétisables d' ARM 68 711 Computer Technology 70 712 Elliott Brothers et Elliott Automation 71 713 Les machines d' English Electric Company 74 714 Les calculateurs de Ferranti 76 715 Les études de General Electric Company 83 716 La patiente construction de ICL 85 Catalogue informatique – Volume E - Ingénieur Général de l'Armement Henri Boucher Page : 1/333 717 La série 29 d' ICL 89 718 Autres produits d' ICL, et fin 94 719 Marconi Company 101 720 Plessey 103 721 Systèmes en Grande-Bretagne 105 722 Histoire de l'informatique australienne 107 723 Informatique en Autriche 109 724 Informatique belge 110 725 Informatique canadienne 111 726 Informatique chinoise 116 727 Informatique en Corée du Sud 118 728 Informatique à Cuba 119 729 Informatique danoise 119 730 Informatique espagnole 121 732 Informatique finlandaise 128 733 Histoire de l'informatique française 130 734 La période héroïque : la SEA 140 735 La Compagnie -

1 Intel CEO Remarks Pat Gelsinger Q2'21 Earnings Webcast July 22
Intel CEO Remarks Pat Gelsinger Q2’21 Earnings Webcast July 22, 2021 Good afternoon, everyone. Thanks for joining our second-quarter earnings call. It’s a thrilling time for both the semiconductor industry and for Intel. We're seeing unprecedented demand as the digitization of everything is accelerated by the superpowers of AI, pervasive connectivity, cloud-to-edge infrastructure and increasingly ubiquitous compute. Our depth and breadth of software, silicon and platforms, and packaging and process, combined with our at-scale manufacturing, uniquely positions Intel to capitalize on this vast growth opportunity. Our Q2 results, which exceeded our top and bottom line expectations, reflect the strength of the industry, the demand for our products, as well as the superb execution of our factory network. As I’ve said before, we are only in the early innings of what is likely to be a decade of sustained growth across the industry. Our momentum is building as once again we beat expectations and raise our full-year revenue and EPS guidance. Since laying out our IDM 2.0 strategy in March, we feel increasingly confident that we're moving the company forward toward our goal of delivering leadership products in every category in which we compete. While we have work to do, we are making strides to renew our execution machine: 7nm is progressing very well. We’ve launched new innovative products, established Intel Foundry Services, and made operational and organizational changes to lay the foundation needed to win in the next phase of our company’s great history. Here at Intel, we’re proud of our past, pragmatic about the work ahead, but, most importantly, confident in our future. -

SIMD Extensions
SIMD Extensions PDF generated using the open source mwlib toolkit. See http://code.pediapress.com/ for more information. PDF generated at: Sat, 12 May 2012 17:14:46 UTC Contents Articles SIMD 1 MMX (instruction set) 6 3DNow! 8 Streaming SIMD Extensions 12 SSE2 16 SSE3 18 SSSE3 20 SSE4 22 SSE5 26 Advanced Vector Extensions 28 CVT16 instruction set 31 XOP instruction set 31 References Article Sources and Contributors 33 Image Sources, Licenses and Contributors 34 Article Licenses License 35 SIMD 1 SIMD Single instruction Multiple instruction Single data SISD MISD Multiple data SIMD MIMD Single instruction, multiple data (SIMD), is a class of parallel computers in Flynn's taxonomy. It describes computers with multiple processing elements that perform the same operation on multiple data simultaneously. Thus, such machines exploit data level parallelism. History The first use of SIMD instructions was in vector supercomputers of the early 1970s such as the CDC Star-100 and the Texas Instruments ASC, which could operate on a vector of data with a single instruction. Vector processing was especially popularized by Cray in the 1970s and 1980s. Vector-processing architectures are now considered separate from SIMD machines, based on the fact that vector machines processed the vectors one word at a time through pipelined processors (though still based on a single instruction), whereas modern SIMD machines process all elements of the vector simultaneously.[1] The first era of modern SIMD machines was characterized by massively parallel processing-style supercomputers such as the Thinking Machines CM-1 and CM-2. These machines had many limited-functionality processors that would work in parallel. -

Historical Perspective and Further Reading 162.E1
2.21 Historical Perspective and Further Reading 162.e1 2.21 Historical Perspective and Further Reading Th is section surveys the history of in struction set architectures over time, and we give a short history of programming languages and compilers. ISAs include accumulator architectures, general-purpose register architectures, stack architectures, and a brief history of ARMv7 and the x86. We also review the controversial subjects of high-level-language computer architectures and reduced instruction set computer architectures. Th e history of programming languages includes Fortran, Lisp, Algol, C, Cobol, Pascal, Simula, Smalltalk, C+ + , and Java, and the history of compilers includes the key milestones and the pioneers who achieved them. Accumulator Architectures Hardware was precious in the earliest stored-program computers. Consequently, computer pioneers could not aff ord the number of registers found in today’s architectures. In fact, these architectures had a single register for arithmetic instructions. Since all operations would accumulate in one register, it was called the accumulator , and this style of instruction set is given the same name. For example, accumulator Archaic EDSAC in 1949 had a single accumulator. term for register. On-line Th e three-operand format of RISC-V suggests that a single register is at least two use of it as a synonym for registers shy of our needs. Having the accumulator as both a source operand and “register” is a fairly reliable indication that the user the destination of the operation fi lls part of the shortfall, but it still leaves us one has been around quite a operand short. Th at fi nal operand is found in memory. -

Computer Hardware
Computer Hardware MJ Rutter mjr19@cam Michaelmas 2014 Typeset by FoilTEX c 2014 MJ Rutter Contents History 4 The CPU 10 instructions ....................................... ............................................. 17 pipelines .......................................... ........................................... 18 vectorcomputers.................................... .............................................. 36 performancemeasures . ............................................... 38 Memory 42 DRAM .................................................. .................................... 43 caches............................................. .......................................... 54 Memory Access Patterns in Practice 82 matrixmultiplication. ................................................. 82 matrixtransposition . ................................................107 Memory Management 118 virtualaddressing .................................. ...............................................119 pagingtodisk ....................................... ............................................128 memorysegments ..................................... ............................................137 Compilers & Optimisation 158 optimisation....................................... .............................................159 thepitfallsofF90 ................................... ..............................................183 I/O, Libraries, Disks & Fileservers 196 librariesandkernels . ................................................197 -
Pwny Documentation Release 0.9.0
pwny Documentation Release 0.9.0 Author Nov 19, 2017 Contents 1 pwny package 3 2 pwnypack package 5 2.1 asm – (Dis)assembler..........................................5 2.2 bytecode – Python bytecode manipulation..............................7 2.3 codec – Data transformation...................................... 11 2.4 elf – ELF file parsing.......................................... 16 2.5 flow – Communication......................................... 36 2.6 fmtstring – Format strings...................................... 41 2.7 marshal – Python marshal loader................................... 42 2.8 oracle – Padding oracle attacks.................................... 43 2.9 packing – Data (un)packing...................................... 44 2.10 php – PHP related functions....................................... 46 2.11 pickle – Pickle tools.......................................... 47 2.12 py_internals – Python internals.................................. 49 2.13 rop – ROP gadgets........................................... 50 2.14 shellcode – Shellcode generator................................... 50 2.15 target – Target definition....................................... 79 2.16 util – Utility functions......................................... 80 3 Indices and tables 83 Python Module Index 85 i ii pwny Documentation, Release 0.9.0 pwnypack is the official CTF toolkit of Certified Edible Dinosaurs. It aims to provide a set of command line utilities and a python library that are useful when playing hacking CTFs. The core functionality of pwnypack -

Protecting Million-User Ios Apps with Obfuscation: Motivations, Pitfalls, and Experience
Protecting Million-User iOS Apps with Obfuscation: Motivations, Pitfalls, and Experience Pei Wang∗ Dinghao Wu Zhaofeng Chen Tao Wei [email protected] [email protected] [email protected] [email protected] The Pennsylvania State The Pennsylvania State Baidu X-Lab Baidu X-Lab University University ABSTRACT ACM Reference Format: In recent years, mobile apps have become the infrastructure of many Pei Wang, Dinghao Wu, Zhaofeng Chen, and Tao Wei. 2018. Protecting popular Internet services. It is now fairly common that a mobile app Million-User iOS Apps with Obfuscation: Motivations, Pitfalls, and Experi- ence. In ICSE-SEIP ’18: 40th International Conference on Software Engineering: serves a large number of users across the globe. Different from web- Software Engineering in Practice Track, May 27–June 3, 2018, Gothenburg, based services whose important program logic is mostly placed on Sweden. ACM, New York, NY, USA, 10 pages. https://doi.org/10.1145/3183519. remote servers, many mobile apps require complicated client-side 3183524 code to perform tasks that are critical to the businesses. The code of mobile apps can be easily accessed by any party after the software is installed on a rooted or jailbroken device. By examining the code, skilled reverse engineers can learn various knowledge about the 1 INTRODUCTION design and implementation of an app. Real-world cases have shown During the last decade, mobile devices and apps have become the that the disclosed critical information allows malicious parties to foundations of many million-dollar businesses operated globally. abuse or exploit the app-provided services for unrightful profits, However, the prosperity has drawn many malevolent attempts to leading to significant financial losses for app vendors. -

Validated Products List, 1993 No. 2
mmmmm NJST PUBLICATIONS NISTIR 5167 (Supersedes NISTIR 5103) Validated Products List 1993 No. 2 Programming Languages Database Language SQL Graphics GOSIP POSIX Judy B. Kailey Computer Security Editor U.S. DEPARTMENT OF COMMERCE Technology Administration National Institute of Standards and Technology Computer Systems Laboratory Software Standards Validation Group Gaithersburg, MD 20899 April 1993 (Supersedes January 1993 issue) —QC 100 NIST . U56 #5167 1993 NISTIR 5167 (Supersedes NISTIR 5103) Validated Products List 1993 No. 2 Programming Languages Database Language SQL Graphics GOSIP POSIX Judy B. Kailey Computer Security Editor U.S. DEPARTMENT OF COMMERCE Technology Administration National Institute of Standards and Technology Computer Systems Laboratory Software Standards Validation Group Gaithersburg, MD 20899 April 1993 (Supersedes January 1993 issue) U.S. DEPARTMENT OF COMMERCE Ronald H. Brown, Secretary NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY Raymond Kammer, Acting Director FOREWORD The Validated Products List is a collection of registers describing implementations of Federal Information Processing Standards (FIPS) that have been validated for conformance to FTPS. The Validated Products List also contains information about the organizations, test methods and procedures that support the validation programs for the FIPS identified in this document. The Validated Products List is updated quarterly. iii iv TABLE OF CONTENTS 1. INTRODUCTION 1 1.1 Purpose 1 1.2 Document Organization 2 1.2.1 Programming Languages 2 1.2.2 Database -
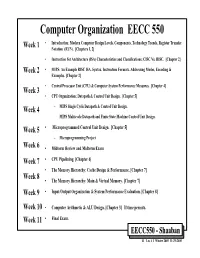
Computer Organization EECC 550 • Introduction: Modern Computer Design Levels, Components, Technology Trends, Register Transfer Week 1 Notation (RTN)
Computer Organization EECC 550 • Introduction: Modern Computer Design Levels, Components, Technology Trends, Register Transfer Week 1 Notation (RTN). [Chapters 1, 2] • Instruction Set Architecture (ISA) Characteristics and Classifications: CISC Vs. RISC. [Chapter 2] Week 2 • MIPS: An Example RISC ISA. Syntax, Instruction Formats, Addressing Modes, Encoding & Examples. [Chapter 2] • Central Processor Unit (CPU) & Computer System Performance Measures. [Chapter 4] Week 3 • CPU Organization: Datapath & Control Unit Design. [Chapter 5] Week 4 – MIPS Single Cycle Datapath & Control Unit Design. – MIPS Multicycle Datapath and Finite State Machine Control Unit Design. Week 5 • Microprogrammed Control Unit Design. [Chapter 5] – Microprogramming Project Week 6 • Midterm Review and Midterm Exam Week 7 • CPU Pipelining. [Chapter 6] • The Memory Hierarchy: Cache Design & Performance. [Chapter 7] Week 8 • The Memory Hierarchy: Main & Virtual Memory. [Chapter 7] Week 9 • Input/Output Organization & System Performance Evaluation. [Chapter 8] Week 10 • Computer Arithmetic & ALU Design. [Chapter 3] If time permits. Week 11 • Final Exam. EECC550 - Shaaban #1 Lec # 1 Winter 2005 11-29-2005 Computing System History/Trends + Instruction Set Architecture (ISA) Fundamentals • Computing Element Choices: – Computing Element Programmability – Spatial vs. Temporal Computing – Main Processor Types/Applications • General Purpose Processor Generations • The Von Neumann Computer Model • CPU Organization (Design) • Recent Trends in Computer Design/performance • Hierarchy -
Intel 2019 Year Book
YEARBOOK 2019 POWERING THE FUTURE Our 2019 yearbook invites you to look back and reflect on a memorable year for Intel. TABLE OF CONTENTS 2019 kicked off with the announcement of our new p4 New CEO. Evolving culture. Expanded ambitions. chief executive, Bob Swan. It was followed by a stream of notable news: product announcements, technology p6 More data. More storage. More processing. breakthroughs, new customers and partnerships, p10 Innovation for the PC user experience and important moves to evolve Intel’s culture as the company entered its sixth decade. p12 Self-driving cars hit the road p2 p16 AI unlocks the power of data It’s a privilege to tell the Intel story in all its complexity and humanity. Looking through these pages, the p18 Helping customers push boundaries breadth and depth of what we’ve achieved in 12 p22 More supply to meet strong demand months is substantial, as is the strong foundation we’ve built for even greater impact in the future. p26 Next-gen hardware and software to unlock it p28 Tech’s future: Inventing and investing I hope you enjoy this colorful look at what’s possible when more than 100,000 individuals from every p32 Reinforcing the nature of Moore’s Law corner of the globe unite to change the world – p34 Building for the smarter future through technologies that make a positive difference to our customers, to society, and to people’s lives. — Claire Dixon, Chief Communications Officer NEW CEO. EVOLVING CULTURE. EXPANDED AMBITIONS. 2019 was an important year in Intel’s transformation, with a new chief executive officer, ambitious business priorities, an aspirational culture evolution, and a farewell to Focal. -

Using Arm Scalable Vector Extension to Optimize OPEN MPI
Using Arm Scalable Vector Extension to Optimize OPEN MPI Dong Zhong1,2, Pavel Shamis4, Qinglei Cao1,2, George Bosilca1,2, Shinji Sumimoto3, Kenichi Miura3, and Jack Dongarra1,2 1Innovative Computing Laboratory, The University of Tennessee, US 2fdzhong, [email protected], fbosilca, [email protected] 3Fujitsu Ltd, fsumimoto.shinji, [email protected] 4Arm, [email protected] Abstract— As the scale of high-performance computing (HPC) with extension instruction sets. systems continues to grow, increasing levels of parallelism must SVE is a vector extension for AArch64 execution mode be implored to achieve optimal performance. Recently, the for the A64 instruction set of the Armv8 architecture [4], [5]. processors support wide vector extensions, vectorization becomes much more important to exploit the potential peak performance Unlike other SIMD architectures, SVE does not define the size of target architecture. Novel processor architectures, such as of the vector registers, instead it provides a range of different the Armv8-A architecture, introduce Scalable Vector Extension values which permit vector code to adapt automatically to the (SVE) - an optional separate architectural extension with a new current vector length at runtime with the feature of Vector set of A64 instruction encodings, which enables even greater Length Agnostic (VLA) programming [6], [7]. Vector length parallelisms. In this paper, we analyze the usage and performance of the constrains in the range from a minimum of 128 bits up to a SVE instructions in Arm SVE vector Instruction Set Architec- maximum of 2048 bits in increments of 128 bits. ture (ISA); and utilize those instructions to improve the memcpy SVE not only takes advantage of using long vectors but also and various local reduction operations.