How to Leak a Secret
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Butler Lampson, Martin Abadi, Michael Burrows, Edward Wobber
Outline • Chapter 19: Security (cont) • A Method for Obtaining Digital Signatures and Public-Key Cryptosystems Ronald L. Rivest, Adi Shamir, and Leonard M. Adleman. Communications of the ACM 21,2 (Feb. 1978) – RSA Algorithm – First practical public key crypto system • Authentication in Distributed Systems: Theory and Practice, Butler Lampson, Martin Abadi, Michael Burrows, Edward Wobber – Butler Lampson (MSR) - He was one of the designers of the SDS 940 time-sharing system, the Alto personal distributed computing system, the Xerox 9700 laser printer, two-phase commit protocols, the Autonet LAN, and several programming languages – Martin Abadi (Bell Labs) – Michael Burrows, Edward Wobber (DEC/Compaq/HP SRC) Oct-21-03 CSE 542: Operating Systems 1 Encryption • Properties of good encryption technique: – Relatively simple for authorized users to encrypt and decrypt data. – Encryption scheme depends not on the secrecy of the algorithm but on a parameter of the algorithm called the encryption key. – Extremely difficult for an intruder to determine the encryption key. Oct-21-03 CSE 542: Operating Systems 2 Strength • Strength of crypto system depends on the strengths of the keys • Computers get faster – keys have to become harder to keep up • If it takes more effort to break a code than is worth, it is okay – Transferring money from my bank to my credit card and Citibank transferring billions of dollars with another bank should not have the same key strength Oct-21-03 CSE 542: Operating Systems 3 Encryption methods • Symmetric cryptography – Sender and receiver know the secret key (apriori ) • Fast encryption, but key exchange should happen outside the system • Asymmetric cryptography – Each person maintains two keys, public and private • M ≡ PrivateKey(PublicKey(M)) • M ≡ PublicKey (PrivateKey(M)) – Public part is available to anyone, private part is only known to the sender – E.g. -

(Linkable) Ring Signature from Hash-Then-One-Way Signature
(Linkable) Ring Signature from Hash-Then-One-Way Signature Xingye Lu Man Ho Au ∗ Zhenfei Zhang Department of Computing Department of Computing Algorand The Hong Kong Polytechnic University The Hong Kong Polytechnic University Boston, USA Hong Kong Hong Kong [email protected] [email protected] [email protected] Abstract—In this paper, we revisit the generic construction of (such as RSA) and three-move type (Type-T) signatures ring signatures from hash-then-one-way type (Type-H) signatures (discrete log (DL) based schemes such as Schnorr). While in proposed by Abe et al. (AOS) in 2004 from the following principle similar to the concrete instantiations, security proof aspects. First, we give a proof for the generic construction, in a strengthened security model. Previously, this was only done for for the AOS generic construction is not formally presented. concrete instantiations, in a weaker model. Second, we extend AOS’s framework to generically construct one-time linkable In 1994, Shor presented a quantum algorithm [4] which can ring signatures from Type-H signatures and one-time signatures. be used to break RSA and DL type digital signatures. Since Lastly, we instantiate the generic construction with an NTRU- then, significant effort has been made to develop practical based Type-H signature: FALCON and obtain a post-quantum quantum computers. Facing the potential threat from quantum linkable ring signature scheme. Our analysis shows that the computers, post-quantum cryptography has attracted more and resulting linkable signature is more efficient than any existing lattice based solutions for small to moderate number of users. -
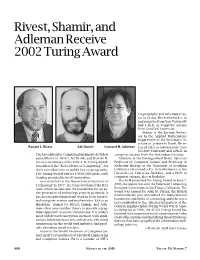
Rivest, Shamir, and Adleman Receive 2002 Turing Award, Volume 50
Rivest, Shamir, and Adleman Receive 2002 Turing Award Cryptography and Information Se- curity Group. He received a B.A. in mathematics from Yale University and a Ph.D. in computer science from Stanford University. Shamir is the Borman Profes- sor in the Applied Mathematics Department of the Weizmann In- stitute of Science in Israel. He re- Ronald L. Rivest Adi Shamir Leonard M. Adleman ceived a B.S. in mathematics from Tel Aviv University and a Ph.D. in The Association for Computing Machinery (ACM) has computer science from the Weizmann Institute. named RONALD L. RIVEST, ADI SHAMIR, and LEONARD M. Adleman is the Distinguished Henry Salvatori ADLEMAN as winners of the 2002 A. M. Turing Award, Professor of Computer Science and Professor of considered the “Nobel Prize of Computing”, for Molecular Biology at the University of Southern their contributions to public key cryptography. California. He earned a B.S. in mathematics at the The Turing Award carries a $100,000 prize, with University of California, Berkeley, and a Ph.D. in funding provided by Intel Corporation. computer science, also at Berkeley. As researchers at the Massachusetts Institute of The ACM presented the Turing Award on June 7, Technology in 1977, the team developed the RSA 2003, in conjunction with the Federated Computing code, which has become the foundation for an en- Research Conference in San Diego, California. The tire generation of technology security products. It award was named for Alan M. Turing, the British mathematician who articulated the mathematical has also inspired important work in both theoret- foundation and limits of computing and who was a ical computer science and mathematics. -

Unique Ring Signatures: a Practical Construction
Unique Ring Signatures: A Practical Construction Matthew Franklin and Haibin Zhang Dept. of Computer Science, University of California, Davis, California 95616, USA {franklin,hbzhang}@cs.ucdavis.edu Abstract. We propose unique ring signatures that simplify and capture the spirit of linkable ring signatures. We use new techniques to provide an instantiation which can be tightly related to the DDH problem in the random oracle model, leading to the most efficient linkable/unique ring signature. Keywords: anonymity, authentication, e-voting system, provable secu- rity, ring signature, tight reduction, unique signature, verifiable random function. 1 Introduction Ring signatures [23] are very useful tools for many privacy-preserving applica- tions. However, they are not adequate in settings where some degree of priva- cy for users must be balanced against limited access. For example, a service provider might have the list of public keys that correspond to all users that have purchased a single access to some confidential service for that day (re- quiring anonymous authentication). For this kind of application, a number of restricted-use ring signatures are proposed. Notable examples include linkable ring signatures [1, 7, 19, 20, 25, 26] and traceable ring signatures [13, 14]. Linkable ring signature asks that if a user signs any two messages (same or different) with respect to the same ring, then an efficient public procedure can verify that the signer was the same (although the user's identity is not revealed). Traceable ring signature is a ring signature scheme where each message is signed not only with respect to a list of ring members, but also with respect to an issue (e.g., identifying label of a specific election or survey). -

Mechanics of Mobilecoin: First Edition
Mechanics of MobileCoin: First Edition exploring the foundations of a private digital currency April 6, 2021, Preview (10/11) v0.0.39 koe1,2 DRAFT INFORMATION: This is just a draft, and may not always be available wher- ever it is currently hosted. The final version will be available at https://github.com/ mobilecoinfoundation. License: `Mechanics of MobileCoin: First Edition' is released into the public domain. 1 [email protected] 2 Author `koe' worked on this document as part of a private contract with, then as an employee of, MobileCoin, Inc. Abstract Cryptography. It may seem like only mathematicians and computer scientists have access to this obscure, esoteric, powerful, elegant topic. In fact, many kinds of cryptography are simple enough that anyone can learn their fundamental concepts. It is common knowledge that cryptography is used to secure communications, whether they be coded letters or private digital interactions. Another application is in so-called cryptocurrencies. These digital moneys use cryptography to assign and transfer ownership of funds. To ensure that no piece of money can be duplicated or created at will, cryptocurrencies usually rely on `blockchains', which are public, distributed ledgers containing records of currency transactions that can be verified by third parties [115]. It might seem at first glance that transactions need to be sent and stored in plain text format to make them publicly verifiable. In truth, it is possible to conceal a transaction's participants, as well as the amounts involved, using cryptographic tools that nevertheless allow transactions to be verified and agreed upon by observers [151]. This is exemplified in the cryptocurrency MobileCoin. -

How to Leak a Secret: Theory and Applications of Ring Signatures
How to Leak a Secret: Theory and Applications of Ring Signatures Ronald L. Rivest1, Adi Shamir2, and Yael Tauman1 1 Laboratory for Computer Science, Massachusetts Institute of Technology, Cambridge, MA 02139, 2 Computer Science department, The Weizmann Institute, Rehovot 76100, Israel. Abstract. In this work we formalize the notion of a ring signature, which makes it possible to specify a set of possible signers without re- vealing which member actually produced the signature. Unlike group sig- natures, ring signatures have no group managers, no setup procedures, no revocation procedures, and no coordination: any user can choose any set of possible signers that includes himself, and sign any message by using his secret key and the others' public keys, without getting their approval or assistance. Ring signatures provide an elegant way to leak authoritative secrets in an anonymous way, to sign casual email in a way that can only be veri¯ed by its intended recipient, and to solve other problems in multiparty computations. Our main contribution lies in the presentation of e±cient constructions of ring signatures; the general concept itself (under di®erent terminology) was ¯rst introduced by Cramer et al. [CDS94]. Our constructions of such signatures are unconditionally signer-ambiguous, secure in the random oracle model, and exceptionally e±cient: adding each ring member in- creases the cost of signing or verifying by a single modular multiplication and a single symmetric encryption. We also describe a large number of extensions, modi¯cations and applications of ring signatures which were published after the original version of this work (in Asiacrypt 2001). -

Cryptography: DH And
1 ì Key Exchange Secure Software Systems Fall 2018 2 Challenge – Exchanging Keys & & − 1 6(6 − 1) !"#ℎ%&'() = = = 15 & 2 2 The more parties in communication, ! $ the more keys that need to be securely exchanged Do we have to use out-of-band " # methods? (e.g., phone?) % Secure Software Systems Fall 2018 3 Key Exchange ì Insecure communica-ons ì Alice and Bob agree on a channel shared secret (“key”) that ì Eve can see everything! Eve doesn’t know ì Despite Eve seeing everything! ! " (alice) (bob) # (eve) Secure Software Systems Fall 2018 Whitfield Diffie and Martin Hellman, 4 “New directions in cryptography,” in IEEE Transactions on Information Theory, vol. 22, no. 6, Nov 1976. Proposed public key cryptography. Diffie-Hellman key exchange. Secure Software Systems Fall 2018 5 Diffie-Hellman Color Analogy (1) It’s easy to mix two colors: + = (2) Mixing two or more colors in a different order results in + + = the same color: + + = (3) Mixing colors is one-way (Impossible to determine which colors went in to produce final result) https://www.crypto101.io/ Secure Software Systems Fall 2018 6 Diffie-Hellman Color Analogy ! # " (alice) (eve) (bob) + + $ $ = = Mix Mix (1) Start with public color ▇ – share across network (2) Alice picks secret color ▇ and mixes it to get ▇ (3) Bob picks secret color ▇ and mixes it to get ▇ Secure Software Systems Fall 2018 7 Diffie-Hellman Color Analogy ! # " (alice) (eve) (bob) $ $ Mix Mix = = Eve can’t calculate ▇ !! (secret keys were never shared) (4) Alice and Bob exchange their mixed colors (▇,▇) (5) Eve will -

A Permissioned Blockchain Secure from Both Classical and Quantum Attacks
PQFabric: A Permissioned Blockchain Secure from Both Classical and Quantum Attacks Amelia Holcomb Geovandro Pereira Bhargav Das∗ Michele Mosca Computer Science Combinatorics & Optimization Computer Science Combinatorics & Optimization University of Waterloo University of Waterloo University of Waterloo University of Waterloo Waterloo, Canada Waterloo, Canada Waterloo, Canada Waterloo, Canada [email protected] [email protected] [email protected] [email protected] Abstract—Hyperledger Fabric is a prominent and flexible so- the end of Round 3, about an year from now. A fourth round lution for building permissioned distributed ledger platforms. is also expected in order to select alternate candidates for Access control and identity management relies on a Mem- later standardization. bership Service Provider (MSP) whose cryptographic interface only handles standard PKI methods for authentication: RSA Open source implementations of such algorithms, for and ECDSA classical signatures. Also, MSP-issued credentials instance those provided by the Open Quantum Safe (OQS) may use only one signature scheme, tying the credential- project [1], continually change in order to keep up-to- related functions to classical single-signature primitives. RSA date with both progress in cryptanalysis and per-algorithm and ECDSA are vulnerable to quantum attacks, with an ongoing parameter modifications and optimizations. However, de- post-quantum standardization process to identify quantum- safe drop-in replacements. In this paper, we propose a redesign signing, approving, and implementing post-quantum cryp- of Fabric’s credential-management procedures and related tographic standards is only the first step. There is also the specifications in order to incorporate hybrid digital signatures, gargantuan task of integrating these algorithms into the protecting against both classical and quantum attacks using wide range of existing systems that depend on and are one classical and one quantum-safe signature. -

Magnetic RSA
Magnetic RSA Rémi Géraud-Stewart1;2 and David Naccache2 1 QPSI, Qualcomm Technologies Incorporated, USA [email protected] 2 ÉNS (DI), Information Security Group CNRS, PSL Research University, 75005, Paris, France [email protected] Abstract. In a recent paper Géraud-Stewart and Naccache [GSN21] (GSN) described an non-interactive process allowing a prover P to con- vince a verifier V that a modulus n is the product of two randomly generated primes (p; q) of about the same size. A heuristic argument conjectures that P cannot control p; q to make n easy to factor. GSN’s protocol relies upon elementary number-theoretic properties and can be implemented efficiently using very few operations. This contrasts with state-of-the-art zero-knowledge protocols for RSA modulus proper generation assessment. This paper proposes an alternative process applicable in settings where P co-generates a modulus n “ p1q1p2q2 with a certification authority V. If P honestly cooperates with V, then V will only learn the sub-products n1 “ p1q1 and n2 “ p2q2. A heuristic argument conjectures that at least two of the factors of n are beyond P’s control. This makes n appropriate for cryptographic use provided that at least one party (of P and V) is honest. This heuristic argument calls for further cryptanalysis. 1 Introduction Several cryptographic protocols rely on the assumption that an integer n “ pq is hard to factor. This includes for instance RSA [RSA78], Rabin [Rab79], Paillier [Pai99] or Fiat–Shamir [FS86]. One way to ascertain that n is such a product is to generate it oneself; however, this becomes a concern when n is provided by a third-party. -

Diffie and Hellman Receive 2015 Turing Award Rod Searcey/Stanford University
Diffie and Hellman Receive 2015 Turing Award Rod Searcey/Stanford University. Linda A. Cicero/Stanford News Service. Whitfield Diffie Martin E. Hellman ernment–private sector relations, and attracts billions of Whitfield Diffie, former chief security officer of Sun Mi- dollars in research and development,” said ACM President crosystems, and Martin E. Hellman, professor emeritus Alexander L. Wolf. “In 1976, Diffie and Hellman imagined of electrical engineering at Stanford University, have been a future where people would regularly communicate awarded the 2015 A. M. Turing Award of the Association through electronic networks and be vulnerable to having for Computing Machinery for their critical contributions their communications stolen or altered. Now, after nearly to modern cryptography. forty years, we see that their forecasts were remarkably Citation prescient.” The ability for two parties to use encryption to commu- “Public-key cryptography is fundamental for our indus- nicate privately over an otherwise insecure channel is try,” said Andrei Broder, Google Distinguished Scientist. fundamental for billions of people around the world. On “The ability to protect private data rests on protocols for a daily basis, individuals establish secure online connec- confirming an owner’s identity and for ensuring the integ- tions with banks, e-commerce sites, email servers, and the rity and confidentiality of communications. These widely cloud. Diffie and Hellman’s groundbreaking 1976 paper, used protocols were made possible through the ideas and “New Directions in Cryptography,” introduced the ideas of methods pioneered by Diffie and Hellman.” public-key cryptography and digital signatures, which are Cryptography is a practice that facilitates communi- the foundation for most regularly used security protocols cation between two parties so that the communication on the Internet today. -

The Best Nurturers in Computer Science Research
The Best Nurturers in Computer Science Research Bharath Kumar M. Y. N. Srikant IISc-CSA-TR-2004-10 http://archive.csa.iisc.ernet.in/TR/2004/10/ Computer Science and Automation Indian Institute of Science, India October 2004 The Best Nurturers in Computer Science Research Bharath Kumar M.∗ Y. N. Srikant† Abstract The paper presents a heuristic for mining nurturers in temporally organized collaboration networks: people who facilitate the growth and success of the young ones. Specifically, this heuristic is applied to the computer science bibliographic data to find the best nurturers in computer science research. The measure of success is parameterized, and the paper demonstrates experiments and results with publication count and citations as success metrics. Rather than just the nurturer’s success, the heuristic captures the influence he has had in the indepen- dent success of the relatively young in the network. These results can hence be a useful resource to graduate students and post-doctoral can- didates. The heuristic is extended to accurately yield ranked nurturers inside a particular time period. Interestingly, there is a recognizable deviation between the rankings of the most successful researchers and the best nurturers, which although is obvious from a social perspective has not been statistically demonstrated. Keywords: Social Network Analysis, Bibliometrics, Temporal Data Mining. 1 Introduction Consider a student Arjun, who has finished his under-graduate degree in Computer Science, and is seeking a PhD degree followed by a successful career in Computer Science research. How does he choose his research advisor? He has the following options with him: 1. Look up the rankings of various universities [1], and apply to any “rea- sonably good” professor in any of the top universities. -

The RSA Algorithm
The RSA Algorithm Evgeny Milanov 3 June 2009 In 1978, Ron Rivest, Adi Shamir, and Leonard Adleman introduced a cryptographic algorithm, which was essentially to replace the less secure National Bureau of Standards (NBS) algorithm. Most impor- tantly, RSA implements a public-key cryptosystem, as well as digital signatures. RSA is motivated by the published works of Diffie and Hellman from several years before, who described the idea of such an algorithm, but never truly developed it. Introduced at the time when the era of electronic email was expected to soon arise, RSA implemented two important ideas: 1. Public-key encryption. This idea omits the need for a \courier" to deliver keys to recipients over another secure channel before transmitting the originally-intended message. In RSA, encryption keys are public, while the decryption keys are not, so only the person with the correct decryption key can decipher an encrypted message. Everyone has their own encryption and decryption keys. The keys must be made in such a way that the decryption key may not be easily deduced from the public encryption key. 2. Digital signatures. The receiver may need to verify that a transmitted message actually origi- nated from the sender (signature), and didn't just come from there (authentication). This is done using the sender's decryption key, and the signature can later be verified by anyone, using the corresponding public encryption key. Signatures therefore cannot be forged. Also, no signer can later deny having signed the message. This is not only useful for electronic mail, but for other electronic transactions and transmissions, such as fund transfers.