The Case of the Uncrackable Code
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

SPYCATCHER by PETER WRIGHT with Paul Greengrass WILLIAM
SPYCATCHER by PETER WRIGHT with Paul Greengrass WILLIAM HEINEMANN: AUSTRALIA First published in 1987 by HEINEMANN PUBLISHERS AUSTRALIA (A division of Octopus Publishing Group/Australia Pty Ltd) 85 Abinger Street, Richmond, Victoria, 3121. Copyright (c) 1987 by Peter Wright ISBN 0-85561-166-9 All Rights Reserved. No part of this publication may be reproduced, stored in or introduced into a retrieval system, or transmitted, in any form or by any means (electronic, mechanical, photocopying, recording or otherwise) without the prior written permission of the publisher. TO MY WIFE LOIS Prologue For years I had wondered what the last day would be like. In January 1976 after two decades in the top echelons of the British Security Service, MI5, it was time to rejoin the real world. I emerged for the final time from Euston Road tube station. The winter sun shone brightly as I made my way down Gower Street toward Trafalgar Square. Fifty yards on I turned into the unmarked entrance to an anonymous office block. Tucked between an art college and a hospital stood the unlikely headquarters of British Counterespionage. I showed my pass to the policeman standing discreetly in the reception alcove and took one of the specially programmed lifts which carry senior officers to the sixth-floor inner sanctum. I walked silently down the corridor to my room next to the Director-General's suite. The offices were quiet. Far below I could hear the rumble of tube trains carrying commuters to the West End. I unlocked my door. In front of me stood the essential tools of the intelligence officer’s trade - a desk, two telephones, one scrambled for outside calls, and to one side a large green metal safe with an oversized combination lock on the front. -
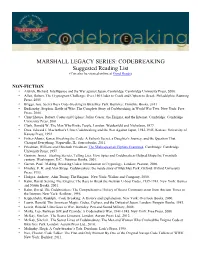
CODEBREAKING Suggested Reading List (Can Also Be Viewed Online at Good Reads)
MARSHALL LEGACY SERIES: CODEBREAKING Suggested Reading List (Can also be viewed online at Good Reads) NON-FICTION • Aldrich, Richard. Intelligence and the War against Japan. Cambridge: Cambridge University Press, 2000. • Allen, Robert. The Cryptogram Challenge: Over 150 Codes to Crack and Ciphers to Break. Philadelphia: Running Press, 2005 • Briggs, Asa. Secret Days Code-breaking in Bletchley Park. Barnsley: Frontline Books, 2011 • Budiansky, Stephen. Battle of Wits: The Complete Story of Codebreaking in World War Two. New York: Free Press, 2000. • Churchhouse, Robert. Codes and Ciphers: Julius Caesar, the Enigma, and the Internet. Cambridge: Cambridge University Press, 2001. • Clark, Ronald W. The Man Who Broke Purple. London: Weidenfeld and Nicholson, 1977. • Drea, Edward J. MacArthur's Ultra: Codebreaking and the War Against Japan, 1942-1945. Kansas: University of Kansas Press, 1992. • Fisher-Alaniz, Karen. Breaking the Code: A Father's Secret, a Daughter's Journey, and the Question That Changed Everything. Naperville, IL: Sourcebooks, 2011. • Friedman, William and Elizebeth Friedman. The Shakespearian Ciphers Examined. Cambridge: Cambridge University Press, 1957. • Gannon, James. Stealing Secrets, Telling Lies: How Spies and Codebreakers Helped Shape the Twentieth century. Washington, D.C.: Potomac Books, 2001. • Garrett, Paul. Making, Breaking Codes: Introduction to Cryptology. London: Pearson, 2000. • Hinsley, F. H. and Alan Stripp. Codebreakers: the inside story of Bletchley Park. Oxford: Oxford University Press, 1993. • Hodges, Andrew. Alan Turing: The Enigma. New York: Walker and Company, 2000. • Kahn, David. Seizing The Enigma: The Race to Break the German U-boat Codes, 1939-1943. New York: Barnes and Noble Books, 2001. • Kahn, David. The Codebreakers: The Comprehensive History of Secret Communication from Ancient Times to the Internet. -

9 Purple 18/2
THE CONCORD REVIEW 223 A VERY PURPLE-XING CODE Michael Cohen Groups cannot work together without communication between them. In wartime, it is critical that correspondence between the groups, or nations in the case of World War II, be concealed from the eyes of the enemy. This necessity leads nations to develop codes to hide their messages’ meanings from unwanted recipients. Among the many codes used in World War II, none has achieved a higher level of fame than Japan’s Purple code, or rather the code that Japan’s Purple machine produced. The breaking of this code helped the Allied forces to defeat their enemies in World War II in the Pacific by providing them with critical information. The code was more intricate than any other coding system invented before modern computers. Using codebreaking strategy from previous war codes, the U.S. was able to crack the Purple code. Unfortunately, the U.S. could not use its newfound knowl- edge to prevent the attack at Pearl Harbor. It took a Herculean feat of American intellect to break Purple. It was dramatically intro- duced to Congress in the Congressional hearing into the Pearl Harbor disaster.1 In the ensuing years, it was discovered that the deciphering of the Purple Code affected the course of the Pacific war in more ways than one. For instance, it turned out that before the Americans had dropped nuclear bombs on Japan, Purple Michael Cohen is a Senior at the Commonwealth School in Boston, Massachusetts, where he wrote this paper for Tom Harsanyi’s United States History course in the 2006/2007 academic year. -

LGBTQ Guam and Hospitality of the Guamanian People
An LGBTQ Guide to Guam Håfa Adai, Welcome! As Lieutenant Governor of Guam and proud member of the LGBTQ community, I am grateful that Guam’s residents have given me the opportunity to help direct the island’s future. Also, Guam has just elected its first female Governor, and now holds the record for the largest women majority in U.S. history. Guam’s diverse political leadership is a direct reflection JOSHUA TENORIO, of the broadening views within our island community. THE HONORABLE LT. GOVERNOR I will advocate for policy that is fair and equal for all and will positively impact LGBTQ rights. I applaud the Guam Visitors Bureau’s efforts in developing the Guam travel industry to better serve LGBTQ travelers and give my full support to their ongoing efforts. We look forward to your visit and providing you with the adventure of a lifetime! Si Yu’os Ma’åse’ 23 Håfa Adai! (Greetings!) Contents The Guam Visitors Bureau (GVB) finds great joy in welcoming LGBTQ travelers to our beautiful island. 02 Welcome As you read this guide, we hope that it inspires you to visit our home and experience the warmth 04 LGBTQ Guam and hospitality of the Guamanian people. 06 LGBTQ Resources 16 Guam strongly supports the LGBTQ community, paving 08 Visiting Guam PILAR LAGUAÑA, the way for equality, celebrating diversity, and promoting With Other LGBTQ PRESIDENT & CEO, inclusivity. The Bureau is a proud member of the Destinations 12 Things to do International Gay and Lesbian Travel Association (IGLTA), GUAM VISITORS 09 Guam + Japan 12 Outdoors BUREAU where we continue our efforts to be a reliable resource for, and to better serve the needs of, all of our visitors. -
Certain Aspects of "Magic" in the Cryptological Background of the Various Official Investigations Into the Attack on P
REF ID:A485355 OF 'l'.BE V.AltIOUS OFFICIAL INVEmGATIONS mo 'l!BE A'.t'.J!ACK ON PEA.BL MRBOR ··. •· . ' I-.- REF ID:A485355 --;-~·;-:;-.:- ... -~.... , ""'-·I';"~-""",~-·;,'~;~~~-~~.\,-::):t~<.""',. -.~\~=---:~-.,,-1f~': ------== ,,.--.., "t-,-.\;' .,-~,-. Certain As;pects of 1tMsgie 11 in the Ct;r:ttol~eaJ.. De.ck.ground of the V{'J."':touc; Offic!.&.1. Invest1@(1ons into the Atttlck on Pearl Harbor INDEX Section l. Introduction • • • • • • • • • • • • • • • • • • • 2. The Real Essence of the Problem • • • • • • • • • 11 A Ziev Look a.t the Revisionists Allegations of Conspiracy to Keep K:l.mmel and S'bort in the Da:rk • • • • • • • • • • • • • • • • • • • • • 18 4. Was MtlGIC Withheld from Kimmel and Short and, if so, ~ ••••••• ,, •••••••• • • 35 1 The tiWinds Code Message:B ' . ~ . .. 49 The Question of Sabota.g~f! • • • ti ~ • • • • • • • 53 Conclusions ....... ",., ....... 65 8. Epilogtte • • .. • • • • ' • ' It • Ill • • • • • • • • 60 11 11 APPENDIX 1: Pearl H&'bor in Pernpective1 by Dr. Louis Morton, Uni:ted States Na.val Institute Proceedi!!is,, Vo1. 81, No. 4, April 1955; P-.kl. 461'.:468 APPlitWIX 2: !lpea.rl Ra.rhor and the Revlsionists, 11 by Prof'. Robert H. Ferrc:Ll.. The Historian, Vol. XVII, No. 2, SprinS 19551 :Pl~· 215·233 REF ID:A485355 1. nmOD"OCTION More than 15 yea.rs have passed. since the Japanese, with unparalleled good luck, good luck that nov seem:s astoundinS, and vith a degree of skill unanticipated by the United, :3tates, executed their surprise attack on Pearl Harbor during the morning hours of 7 December 1941. It was an attack that constituted a. momentou::; disaster for the United States; it ma.de our Navy's Pacific Pleet, for all practica.l purposes, hors de combat for m.a.ny months. -

June 1St Heath Robinson Operational
similar vein to Rube Goldberg in The Mark 2 supported the US). conditional branching, just as Charles Babbage’s analytical June 1st The machine consisted of a engine had done [Dec 23], frame (called the bedspread) although there’s no evidence to which supported two long suggest that the Mark 2's Heath Robinson teleprinter paper tapes on a designer, Tommy Flowers [Dec network of reels, and two other 22], was aware of Babbage's Operational racks holding counters and logic design. June 1, 1943 circuits. Ten Colossi were operating by One tape could hold 2,000 The "Heath Robinson" was a the end of the war and an characters of cipher text, while code-breaking machine used at eleventh had been the other stored patterns that Bletchley Park [Aug 15] to help commissioned. They allowed the the codebreakers believed might decrypt the Lorenz (aka Tunny) Allies to extract a vast amount of represent the Lorenz cipher. intelligence from intercepted encryption. The second tape had radio messages sent from Lorenz was a much more to be precisely one character German High Command advanced cipher than the better longer than the first, and throughout Europe. known Enigma [Feb 23]. For keeping the tapes synchronized example, Enigma machines was a major challenge. A functioning reconstruction of a initially used just three rotors Mark 2 was completed in 2008 Max Newman [Feb 7] was during their encryption process, by Tony Sale and volunteers; it's while a Lorenz device employed responsible for the Robinson's on display at The National functional specification, but twelve. -

The Magic Flute
OCTOBER 09, 2015 THE FRIDAY | 8:00 PM OCTOBER 11, 2015 MAGIC SUNDAY | 4:00 PM OCTOBER 13, 2015 FLUTE TUESDAY | 7:00 PM FLÂNEUR FOREVER Honolulu Ala Moana Center (808) 947-3789 Royal Hawaiian Center (808) 922-5780 Hermes.com AND WELCOME TO AN EXCITING NEW SEASON OF OPERAS FROM HAWAII OPERA THEATRE. We are thrilled to be opening our 2014) conducts, and Allison Grant As always we are grateful to you, season with one of Mozart’s best- (The Merry Widow, 2004) directs this our audience, for attending our loved operas: The Magic Flute. This new translation of The Magic Flute by performances and for the support colorful production comes to us Jeremy Sams. you give us in so many ways from Arizona Opera, where it was throughout the year. Without your created by Metropolitan Opera This will be another unforgettable help we simply could not continue stage director, Daniel Rigazzi. season for HOT with three to bring the world’s best opera to Inspired by the work of the French sensational operas, including Hawaii each year. surrealist painter, René Magritte, a stunning new production of the production is fi lled with portals– Benjamin Britten’s A Midsummer But now sit back and enjoy Mozart’s doorways and picture frames–that Night’s Dream, directed by Henry The Magic Flute. lead the viewer from reality to Akina, with videography by Adam dreams. With a cast that includes Larsen (Siren Song, 2015) and a MAHALO Antonio Figueroa as Tamino and So spectacular production of Verdi’s Il Young Park as the formidable Queen Trovatore designed by Peter Dean Henry G. -

An Introduction to a Historic Computer Document: Betting on the Future - the 1946 Pendergrass Report Cryptanalysis and the Digital Computer
UNCLASSIFIED An Introduction to a Historic Computer Document: Betting on the Future - The 1946 Pendergrass Report Cryptanalysis and the Digital Computer COLIN BURKE The codebreakers of the American navy's OP-20-G had struggled since the early 1930s to obtain the funds needed to design and build high-speed electronic analytic machines. [11,21 Unfortunately, their mid-1930's project, which was led by Vannevar Bush of MIT, did not produce a truly successful device. The developmental funds and the institutional supports provided by the navy were insufficient for the challenging move into digital electronics. The relatively special-purpose, optical-electronic Comparator that Bush constructed for the navy in 1938 was unreliable. OP-20-G began World War II with only a handful of IBM electromechanical tabulators and the hope that massive funding of electronics research would finally allow the creation of the more powerful Rapid Analytic machines Bush had suggested to the navy's S.C. Hooper and Joseph Wenger in 1936. [211 Hooper and Wenger hoped that such machines, distant cousins of the programmed digital electronic computer, would allow OP-20-G to create and apply advanced mathematical and statistical cryptanalytic techniques. A stable, long-term program to develop the Rapid Machines might have led OP-20-G to be among the very first to conceive of and build a modern electronic computer, but the chance for such a program had been lost in the 1930s. It could not be reborn during the war. The demands created by Pearl Harbor and the Battle of the Atlantic turned OP-20-G away from speculative projects. -

MTAT.07.006 Research Seminar in Cryptography the Enigma Cipher Machine
MTAT.07.006 Research Seminar in Cryptography The Enigma Cipher Machine Kadri Hendla November 28, 2005 Abstract 3.1 The Rotors The aim of this survey is to give a brief overview on Rotors are the most important part of an Enigma Enigma cipher machine and its cryptanalysis before machine. A rotor is a disc about 10 cm in diameter and during the Second World War. The survey is and it’s usually made of hard rubber or bakelite. mostly based on the articles [1] and [7] on Enigma On one face are 26 brass pins forming a circle; on from Wikipedia. the other side are corresponding electrical contacts. Each pin represents a letter in the alphabet. Inside the rotor are 26 wires connecting the pins on one 1 Introduction side to the contacts on the other side; the wiring is different for each rotor. The rotor also has a finger Enigma is a portable cipher machine, famous for wheel for turning the rotor by hand and an alpha- the role it played in World War II. The breaking of bet ring, so the operator can see the rotor position. Enigma codes is considered to be one of the reasons In the earlier versions of Enigma the alphabet ring for the Allies victory. was fixed; the later versions allowed adjusting the alphabet ring relative to the core wiring. This po- sition of the ring is known as the ring settings. The 2 History of Enigma rotors are placed in the machine side by side, which causes the pins and contacts of the neighbouring In 1918 German engineer Arthur Scherbius applied rotors to form an electrical connection. -

Colossus – NZZ Artikel – Dominik Landwehr – März 2007 1/17
Colossus – NZZ Artikel – Dominik Landwehr – März 2007 1/17 Colossus: 15 000 Röhren knacken den Nazi-Code Bletchley Park rekonstruiert einen frühen Computer Mit einem beispiellosen Aufwand gelang es den Briten im Zweiten Weltkrieg die deutsche Chiffriermaschine Enigma zu knacken. Weniger bekannt ist die Tatsache, dass sie dank einer Maschine namens 'Colossus' auch einen weit komplexeren deutschen Fernschreiber-Code brechen konnten. 'Colossus' nimmt in der Ahnengalerie der Computergeschichte einen Ehrenplatz ein und ist seit kurzem in Bletchley Park als funktionsfähiger Nachbau zu besichtigen. Von Dominik Landwehr 14 Jahre akribischer Arbeit stecken hinter dem Projekt der Colossus-Rekonstruktion. Damit konnte der britische Ingenieur und Nachrichtendienst-Spezialist Tony Sale eine seiner Visionen wahr machen.(Foto Dominik Landwehr) Colossus – NZZ Artikel – Dominik Landwehr – März 2007 2/17 Gewiss, es gibt grössere Museen zur Technik und besonders der Computergeschichte als jenes von Bletchley Park: Zu nennen wäre das Science Museum in London, das Deutsche Museum in München, das Heinz Nixdorf MuseumsForum in Paderborn oder das Computer History Museum im kalifornischen Mountain View. Bletchley Park – eine Zugstunde nördlich von London genau in der Mitte zwischen Oxford und Cambridge gelegen – ist dennoch etwas einzigartiges und das hängt vor allem mit seinem ’genius loci’ zusammen. Die goldenen Eier von Bletchley Park Im Rahmen einer geheimen Operation wurde hier im Zweiten Weltkrieg ein wesentlicher Teil des Nachrichtenverkehrs von Hitler Deutschland entschlüsselt. Die wichtigsten hier dekodierten Nachrichten wurden unter dem Aktenvermerk 'Ultra' nur höchsten Entscheidungsträgern zugänglich gemacht. Die Entschlüsselung geschah gewissermassen auf industrieller Basis: Bis zu zehntausend Menschen – die meisten davon Frauen – arbeiteten in Bletchley Park rund um die Uhr. -

Teaching the Conflicts Neal Stephenson's Cryptonomicon And
Teaching the Conflicts Neal Stephenson’s Cryptonomicon and The Baroque Cycle Lee Barbrook Doctor of Philosophy Newcastle University May 2012 Abstract I read Neal Town Stephenson’s Cryptonomicon and The Baroque Cycle to interrogate what types of links they make to US countercultural writing, postmodern discourse in American culture, and perceived uninterrogated links to the term America itself in images of modern progressive liberalism. Postmodernist readings of literary texts came under increasing public scrutiny in intellectual debates of the 80s and 90s. My analysis is to situate and reconsider these fictions within debates happening in the North American academy at this time and the more recent one concerning the demise of poststructuralism in the humanities. Linking together works of Sean McCann, Michael Szalay, John Guillory and Mark McGurl I locate Cryptonomicon as constitutive of the postwar drift from the modernist aesthetic yet simultaneously developing within Sacvan Bercovitch’s model of dissensus. Through reference to McGurl’s work in particular, my thesis will offer the first sustained critical reading of Cryptonomicon relevant to the University’s new teaching standards of diversity and research excellence . Through Lauren Berlant’s concept of an intimate public I argue The Baroque Cycle develops a richly aesthetic form of criticism that challenges the consensus view of culturally affirming alternatives to American sociopolitical and economic life. In addition, each chapter charts specific aspects of the impact of European critical theories that presided over the marriage of intellectualism and professionalism in the North American academy. More specifically, and throwing particular focus on resistances to theory and canon change, I discuss how the politics of the classroom developed within the literary culture wars brought with it a renewed emphasis on what postwar professors taught in the classroom. -

Colossus and the Origins of Programmability
Colossus and the Origins of Programmability Draft for discussion at the 2016 SIGCIS Workshop. Do not quote or cite without permission of the authors. Thomas Haigh ([email protected]) and Mark Priestley ([email protected]) This is an initial draft of some material from our ongoing project to explore the history of Tommy Flowers, the ways in which Colossus was used and configured, and its place in the history of information technology. This work is sponsored by Mrs. L.D. Rope’s Second Charitable Trust. The current draft is very preliminary, so please do not quote, cite, or distribute without our permission. If names and references are confusing to you our apologies! Fortunately the basics of Colossus and Bletchley Park are well covered in Wikipedia. Colossus was a codebreaking device built by the British General Post Office at the end of 1943, under the direction of career telecommunications engineer Tommy Flowers. It entered use at Bletchley Park in 1944 to speed the work of codebreakers targeting what was then codenamed “fish,” a family of Lorenz teleprinter codes used for high level German military communication. Colossus was not a one‐off machine, like most early electronic computers, but the prototype for a family of ten “colossi,” in which later models incorporated some significant improvements. The machines were used by the Newmanry, a group under mathematician Max Newman, where ingenious codebreaking users discovered new applications for them which, in turn, shaped the provision of additional controls and capabilities in the later models. Unlike ENIAC, which began in modest secrecy but soon graced the front page of the New York Times, Colossus was highly classified and remained unknown to the public until the 1970s.