Disk Encryption
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Operating System Boot from Fully Encrypted Device
Masaryk University Faculty of Informatics Operating system boot from fully encrypted device Bachelor’s Thesis Daniel Chromik Brno, Fall 2016 Replace this page with a copy of the official signed thesis assignment and the copy of the Statement of an Author. Declaration Hereby I declare that this paper is my original authorial work, which I have worked out by my own. All sources, references and literature used or excerpted during elaboration of this work are properly cited and listed in complete reference to the due source. Daniel Chromik Advisor: ing. Milan Brož i Acknowledgement I would like to thank my advisor, Ing. Milan Brož, for his guidance and his patience of a saint. Another round of thanks I would like to send towards my family and friends for their support. ii Abstract The goal of this work is description of existing solutions for boot- ing Linux and Windows from fully encrypted devices with Secure Boot. Before that, though, early boot process and bootloaders are de- scribed. A simple Linux distribution is then set up to boot from a fully encrypted device. And lastly, existing Windows encryption solutions are described. iii Keywords boot process, Linux, Windows, disk encryption, GRUB 2, LUKS iv Contents 1 Introduction ............................1 1.1 Thesis goals ..........................1 1.2 Thesis structure ........................2 2 Boot Process Description ....................3 2.1 Early Boot Process ......................3 2.2 Firmware interfaces ......................4 2.2.1 BIOS – Basic Input/Output System . .4 2.2.2 UEFI – Unified Extended Firmware Interface .5 2.3 Partitioning tables ......................5 2.3.1 MBR – Master Boot Record . -

Effective Crypto Ransomawre Detection Using Hardware
Effective Crypto Ransomawre Detection Using Hardware Performance Counters John Podolanko Department of Computer Science & Engineering The University of Texas at Arlington Supervisor Jiang Ming, PhD In partial fulfillment of the requirements for the degree of Master of Science in Computer Science May 2019 Abstract Systems affected by malware in the past 10 years has risen from 29 million to 780 million, which tells us it is a rapidly growing threat. Viruses, ransomware, worms, backdoors, botnets, etc. all come un- der malware. Ransomware alone is predicted to cost $11.5 billion in 2019. As the downtime, data loss, and financial damages are ris- ing, researchers continue to look for new ways to mitigate this threat. However, the common approaches have shown to yield high false posi- tive rates or delayed detection rates resulting in data loss. My research explores a dynamic approach for early-stage ransomware detection by modeling its behavior using hardware performance counters with low overhead. The analysis begins on a bare-metal machine running ran- somware which is profiled for hardware calls using Intel R VTuneTM Amplifier before it compromises the system. By using this approach, I am able to generate models using hardware performance counters extracted by VTuneTM on known ransomware samples collected from VirusTotal and Hybrid Analysis, and I use that data to train the de- tection system using machine learning techniques. I have shown that hardware performance counters can provide effective metrics for use in detecting and mitigating the ever-growing ransomware threat faced by the world while ensuring no data is lost. ii Acknowledgements The author thanks the supervisory committee for all their guidance, support, and patience. -

Defeating Invisible Enemies:Firmware Based
Defeating Invisible Enemies: Firmware Based Security in OpenPOWER Systems — Linux Security Summit 2017 — George Wilson IBM Linux Technology Center Linux Security Summit / Defeating Invisible Enemies / September 14, 2017 / © 2017 IBM Corporation Agenda Introduction The Case for Firmware Security What OpenPOWER Is Trusted Computing in OpenPOWER Secure Boot in OpenPOWER Current Status of Work Benefits of Open Source Software Conclusion Linux Security Summit / Defeating Invisible Enemies / September 14, 2017 / © 2017 IBM Corporation 2 Introduction Linux Security Summit / Defeating Invisible Enemies / September 14, 2017 / © 2017 IBM Corporation 3 Disclaimer These slides represent my views, not necessarily IBM’s All design points disclosed herein are subject to finalization and upstream acceptance The features described may not ultimately exist or take the described form in a product Linux Security Summit / Defeating Invisible Enemies / September 14, 2017 / © 2017 IBM Corporation 4 Background The PowerPC CPU has been around since 1990 Introduced in the RS/6000 line Usage presently spans embedded to server IBM PowerPC servers traditionally shipped with the PowerVM hypervisor and ran AIX and, later, Linux in LPARs In 2013, IBM decided to open up the server architecture: OpenPOWER OpenPOWER runs open source firmware and the KVM hypervisor with Linux guests Firmware and software designed and developed by the IBM Linux Technology Center “OpenPOWER needs secure and trusted boot!” Linux Security Summit / Defeating Invisible Enemies / September 14, 2017 / © 2017 IBM Corporation 5 The Case for Firmware Security Linux Security Summit / Defeating Invisible Enemies / September 14, 2017 / © 2017 IBM Corporation 6 Leaks Wikileaks Vault 7 Year 0 Dump NSA ANT Catalog Linux Security Summit / Defeating Invisible Enemies / September 14, 2017 / © 2017 IBM Corporation 7 Industry Surveys UEFI Firmware Rootkits: Myths and Reality – Matrosov Firmware Is the New Black – Analyzing Past Three Years of BIOS/UEFI Security Vulnerabilities – Branco et al. -

Taxonomy for Anti-Forensics Techniques & Countermeasures
View metadata, citation and similar papers at core.ac.uk brought to you by CORE provided by St. Cloud State University St. Cloud State University theRepository at St. Cloud State Culminating Projects in Information Assurance Department of Information Systems 4-2020 Taxonomy for Anti-Forensics Techniques & Countermeasures Ziada Katamara [email protected] Follow this and additional works at: https://repository.stcloudstate.edu/msia_etds Recommended Citation Katamara, Ziada, "Taxonomy for Anti-Forensics Techniques & Countermeasures" (2020). Culminating Projects in Information Assurance. 109. https://repository.stcloudstate.edu/msia_etds/109 This Starred Paper is brought to you for free and open access by the Department of Information Systems at theRepository at St. Cloud State. It has been accepted for inclusion in Culminating Projects in Information Assurance by an authorized administrator of theRepository at St. Cloud State. For more information, please contact [email protected]. Taxonomy for Anti-Forensics Techniques and Countermeasures by Ziada Katamara A Starred Paper Submitted to the Graduate Faculty of St Cloud State University in Partial Fulfillment of the Requirements for the Degree Master of Science in Information Assurance June, 2020 Starred Paper Committee: Abdullah Abu Hussein, Chairperson Lynn A Collen Balasubramanian Kasi 2 Abstract Computer Forensic Tools are used by forensics investigators to analyze evidence from the seized devices collected at a crime scene or from a person, in such ways that the results or findings can be used in a court of law. These computer forensic tools are very important and useful as they help the law enforcement personnel to solve crimes. Computer criminals are now aware of the forensics tools used; therefore, they use countermeasure techniques to efficiently obstruct the investigation processes. -

Winter 2016 E-Newsletter
WINTER 2016 E-NEWSLETTER At Digital Mountain we assist our clients with their e-discovery, computer forensics and cybersecurity needs. With increasing encryption usage and the recent news of the government requesting Apple to provide "backdoor" access to iPhones, we chose to theme this E-Newsletter on the impact data encryption has on attorneys, litigation support professionals and investigators. THE SHIFTING LANDSCAPE OF DATA ENCRYPTION TrueCrypt, a free on-the-fly full disk encryption product, was the primary cross-platform solution for practitioners in the electronic discovery and computer forensics sector. Trusted and widely adopted, TrueCrypt’s flexibility to perform either full disk encryption or encrypt a volume on a hard drive was an attractive feature. When TrueCrypt encrypted a volume, a container was created to add files for encryption. As soon as the drive was unmounted, the data was protected. The ability to add a volume to the original container, where any files or the folder structure could be hidden within an encrypted volume, provided an additional benefit to TrueCrypt users. However, that all changed in May 2014 when the anonymous team that developed TrueCrypt decided to retire support for TrueCrypt. The timing of TrueCrypt’s retirement is most often credited to Microsoft’s ending support of Windows XP. The TrueCrypt team warned users that without support for Windows XP, TrueCrypt was vulnerable. Once support for TrueCrypt stopped, trust continued to erode as independent security audits uncovered specific security flaws. In the wake of TrueCrypt’s demise, people were forced to look for other encryption solutions. TrueCrypt’s website offered instructions for users to migrate to BitLocker, a full disk encryption program available in certain editions of Microsoft operating systems beginning with Windows Vista. -

Full-Disk-Encryption Crash-Course
25C3: Full-Disk-Encryption Crash-Course Everything to hide Jürgen Pabel, CISSP Akkaya Consulting GmbH #0 Abstract Crash course for software based Full-Disk-Encryption. The technical architectures of full-disk-encryption solutions for Microsoft Windows and Linux are described. Technological differences between the two open-source projects TrueCrypt and DiskCryptor are explained. A wish-list with new features for these open-source Full-Disk-Encryption offerings wraps things up. Readers should be familiar with general operating system concepts and have some software development experience. #1 Introduction Software based Full-Disk-Encryption (¹FDEª) solutions are usually employed to maintain the confidentiality of data stored on mobile computer systems. The established terminology is ¹data-at-rest protectionª; it implies that data is protected against unauthorized access, even if an adversary possesses the storage media. Therefore, some of the most common risks to data confidentiality are addressed: loss and theft of mobile computer systems. The encryption and decryption of data is completely transparent to computer users, which makes Full-Disk- Encryption solutions trivial to use. The only user interaction occurs in the Pre-Boot-Authentication (¹PBAª) environment, in which the computer user provides the cryptographic key in order to allow for the operating system to be started and data to be accessed. #2 Architecture I: Pre-Boot-Authentication The Pre-Boot-Authentication environment is loaded before the operating system when the computer is powered-on. The primary purpose of the Pre-Boot-Authentication is to load the encryption key into memory and to initiate the boot process of the installed operating system. -

Advanced Notification of Cyber Threats Against Mamba Ransomware
Advanced Notification of Cyber Threats against Mamba Ransomware Security Advisory AE-Advisory 17-42 Criticality Critical Advisory Released On 13 August 2017 Impact Mamba ransomware fully encrypts the hard drive of an infected machine. Solution Adhere the advices written under the solution section. Affected Platforms Windows Operating System (OS) Summary As the leading trusted secure cyber coordination center in the region, aeCERT has researched and found about a ransomware that is new to the region currently named as “Mamba Ransomware”. Mamba ransomware uses DiskCryptor to encrypt the disks by using a very strong full disk encryption method. The hacker uses psexec utility to gain access to the network and infect the machine with the malware. The malware goes deep into the system to gain access to all services, forces the machine to restart, then starts to encrypt the disk. Advisory Details Mamba ransomware’s initial distribution is similar to other ransomware-type viruses, such as WannaCrypt and Petya. Furthermore, Mamba is used against corporations and organizations. The attacker uses Mamba ransomware to encrypt the hard drive of the victim’s machine. This ransomware uses a legitimate utility called DiskCryptor to achieve full disk encryption of the infected machine on the Master Boot Record level. In order to decrypt the machine, the victim is asked to contact the attacker for the decryption of the hard drive. This group of attackers need to gain access to the network of the company by using psexec utility to run the ransomware on the victim’s machine. The exploit generates a password for DiskCryptor utility. -

İSTİHBARATIN TEŞKİLATLANMA Ve YÖNETİM SORUNSALI: A.B.D. ÖRNEĞİ
T.C. İSTANBUL ÜNİVERSİTESİ SOSYAL BİLİMLER ENSTİTÜSÜ SİYASET BİLİMİ VE KAMU YÖNETİMİ ANABİLİM DALI YÜKSEK LİSANS TEZİ İSTİHBARATIN TEŞKİLATLANMA ve YÖNETİM SORUNSALI: A.B.D. ÖRNEĞİ Fatih TÜRK 2501110836 TEZ DANIŞMANI DOÇ. DR Pelin Pınar GİRİTLİOĞLU İSTANBUL - 2019 ÖZ İSTİHBARATIN TEŞKİLATLANMA ve YÖNETİM SORUNSALI: A.B.D. ÖRNEĞİ Fatih TÜRK Günümüzde teknolojinin gelişimi ve küreselleşme dünyayı uçtan uca değiştirdi. Toplumlar ve ülkeler birbiri ile etkileşime geçtikçe bireysel özgürlükler ve demokrasi konusunda hassas alanlar giderek artmaktadır. Bu etkileşim ülkelerin güvenliğini ve bireysel özgürlük alanlarınıda etkilemektedir. Bu hızlı değişime karşın ülkeler geçmişin soğuk savaş anlayışı ve güvenlik hassasiyetlerini de aynı zamanda taşımaya devam etmektedirler. Gelişmiş demokrasilere sahip ülkelerin başında gelen Amerika Birleşik Devletleri’nde (ABD) mevcut güvenlik ve istihbarat anlayışı, faaliyetleri ve denetimi işte bu çatışmanın uzun sürede meydana geldiği denge üzerine kuruludur. ABD açısından istihbarat teşkilatlanma süreci yeni problemler, hak arayışları, çatışma ve çözümler doğurmaktadır. Tüm bunların ışığında bu tezin temel amacı istihbarat problemlerini ABD istihbarat teşkilatlanma süreci üzerinden analiz edip karşılaşılan problemleri neden sonuç ilişkisi içerisinde tespit etmektir. Bu çalışmada Amerika Birleşik Devletleri’nde istihbaratın yönetim modeli, teşkilatlanması ve hukuki alt yapısı incelenmiştir. Birinci bölümde kavramsal anlamda istihbarat incelemesi literatüre önemli bir katkı olarak görülebilir. İkinci bölümde -
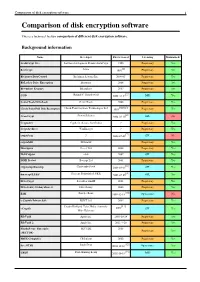
Comparison of Disk Encryption Software 1 Comparison of Disk Encryption Software
Comparison of disk encryption software 1 Comparison of disk encryption software This is a technical feature comparison of different disk encryption software. Background information Name Developer First released Licensing Maintained? ArchiCrypt Live Softwaredevelopment Remus ArchiCrypt 1998 Proprietary Yes [1] BestCrypt Jetico 1993 Proprietary Yes BitArmor DataControl BitArmor Systems Inc. 2008-05 Proprietary Yes BitLocker Drive Encryption Microsoft 2006 Proprietary Yes Bloombase Keyparc Bloombase 2007 Proprietary Yes [2] CGD Roland C. Dowdeswell 2002-10-04 BSD Yes CenterTools DriveLock CenterTools 2008 Proprietary Yes [3][4][5] Check Point Full Disk Encryption Check Point Software Technologies Ltd 1999 Proprietary Yes [6] CrossCrypt Steven Scherrer 2004-02-10 GPL No Cryptainer Cypherix (Secure-Soft India) ? Proprietary Yes CryptArchiver WinEncrypt ? Proprietary Yes [7] cryptoloop ? 2003-07-02 GPL No cryptoMill SEAhawk Proprietary Yes Discryptor Cosect Ltd. 2008 Proprietary Yes DiskCryptor ntldr 2007 GPL Yes DISK Protect Becrypt Ltd 2001 Proprietary Yes [8] cryptsetup/dmsetup Christophe Saout 2004-03-11 GPL Yes [9] dm-crypt/LUKS Clemens Fruhwirth (LUKS) 2005-02-05 GPL Yes DriveCrypt SecurStar GmbH 2001 Proprietary Yes DriveSentry GoAnywhere 2 DriveSentry 2008 Proprietary Yes [10] E4M Paul Le Roux 1998-12-18 Open source No e-Capsule Private Safe EISST Ltd. 2005 Proprietary Yes Dustin Kirkland, Tyler Hicks, (formerly [11] eCryptfs 2005 GPL Yes Mike Halcrow) FileVault Apple Inc. 2003-10-24 Proprietary Yes FileVault 2 Apple Inc. 2011-7-20 Proprietary -

COMITÉ DE TRANSPARENCIA ACTA DE LA SESIÓN ORDINARIA 17/2020 DEL 28 DE MAYO DE 2020 a Las Trece Horas Del Veintiocho De Mayo De
COMITÉ DE TRANSPARENCIA ACTA DE LA SESIÓN ORDINARIA 17/2020 DEL 28 DE MAYO DE 2020 A las trece horas del veintiocho de mayo de dos mil veinte, participan en la presente sesión a través de medios electrónicos de comunicación, Erik Mauricio Sánchez Medina, Director Jurídico; Víctor Manuel De La Luz Puebla, Director de Seguridad y Organización de la Información; y Rodrigo Villa Collins, Gerente de Análisis y Promoción de Transparencia, en su carácter de integrante suplente del Titular de la Unidad de Transparencia; todos ellos integrantes del Comité de Transparencia de este Instituto Central, así como Sergio Zambrano Herrera, Gerente de Gestión de Transparencia, en su carácter de Secretario de este órgano colegiado, de conformidad con los párrafos segundo, tercero, cuarto y quinto de la Quinta de las Reglas de Operación del Comité de Transparencia del Banco de México, publicadas en el Diario Oficial de la Federación el siete de mayo de dos mil veinte (Reglas). Acto seguido, quien ejerce en este acto las funciones de Secretariado del Comité de Transparencia manifestó que existe quórum para la celebración de la presente sesión, de conformidad con lo previsto en los artículos 43 de la Ley General de Transparencia y Acceso a la Información Pública (LGTAIP); 64, párrafos segundo y tercero, de la Ley Federal de Transparencia y Acceso a la Información Pública (LFTAIP); 83 de la Ley General de Protección de Datos Personales en Posesión de Sujetos Obligados (LGPDPPSO); 4o. del Reglamento Interior del Banco de México (RIBM); así como Quinta y Sexta de las Reglas. Por lo anterior, se procedió en los términos siguientes: ---------------------------------------------------------------------------------------------------------------------------- APROBACIÓN DEL ORDEN DEL DÍA. -

Annual Review 2013
Cert-IST annual review for 2013 regarding flaws and attacks 1) Introduction ...................................................................................................................................... 1 2) The most significant events for 2013 ............................................................................................... 2 2.1 The Snowden Affair changes the perception for « cyber-espionage » risk ............................. 2 2.2 Hardware attacks are becoming a real threat ......................................................................... 3 2.3 Offensive security is increasingly present ............................................................................... 3 3) Vulnerabilities and attacks seen in 2013 ......................................................................................... 5 3.1 Figures about Cert-IST 2013 production ................................................................................. 5 3.2 Alerts and Potential Dangers released by Cert-IST ................................................................ 6 3.3 Zoom on a few flaws and attacks ............................................................................................ 7 4) How to protect companies ............................................................................................................... 9 4.1 Advanced Persistent Threats (APT) ........................................................................................ 9 4.2 Opportunistic attacks ............................................................................................................ -

Sok: “Plug & Pray” Today – Understanding USB Insecurity In
SoK: “Plug & Pray” Today – Understanding USB Insecurity in Versions 1 through C Dave (Jing) Tian∗, Nolen Scaife∗, Deepak Kumary, Michael Baileyy, Adam Batesy, Kevin R. B. Butler∗ ∗University of Florida fdaveti, scaife, butlerg@ufl.edu yUniversity of Illinois at Urbana-Champaign fdkumar11, mdbailey, [email protected] Abstract—USB-based attacks have increased in complexity in systematizing the defenses present in the USB ecosystem, we recent years. Modern attacks now incorporate a wide range of find that most defenses often focus on protecting a single layer, attack vectors, from social engineering to signal injection. To which proves ineffective against a suite of attacks that appear address these challenges, the security community has responded with a growing set of fragmented defenses. In this work, at many communication layers. In addition, misaligned goals we survey and categorize USB attacks and defenses, unifying between industry and academia further fragment the defense observations from both peer-reviewed research and industry. space. Commercial solutions focus on the prevention of data Our systematization extracts offensive and defensive primitives loss and anti-malware without regard for emerging attack that operate across layers of communication within the USB vectors, while research prototypes vary and are hamstrung by ecosystem. Based on our taxonomy, we discover that USB attacks often abuse the trust-by-default nature of the ecosystem, and the lack of built-in security building blocks in the existing transcend different layers within a software stack; none of USB specifications. As a result, research solutions often rely the existing defenses provide a complete solution, and solutions on new host and peripheral architectures that are unlikely to expanding multiple layers are most effective.