Status of High Level Architecture Real Time Platform Reference Federation
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Chapter 1. Origins of Mac OS X
1 Chapter 1. Origins of Mac OS X "Most ideas come from previous ideas." Alan Curtis Kay The Mac OS X operating system represents a rather successful coming together of paradigms, ideologies, and technologies that have often resisted each other in the past. A good example is the cordial relationship that exists between the command-line and graphical interfaces in Mac OS X. The system is a result of the trials and tribulations of Apple and NeXT, as well as their user and developer communities. Mac OS X exemplifies how a capable system can result from the direct or indirect efforts of corporations, academic and research communities, the Open Source and Free Software movements, and, of course, individuals. Apple has been around since 1976, and many accounts of its history have been told. If the story of Apple as a company is fascinating, so is the technical history of Apple's operating systems. In this chapter,[1] we will trace the history of Mac OS X, discussing several technologies whose confluence eventually led to the modern-day Apple operating system. [1] This book's accompanying web site (www.osxbook.com) provides a more detailed technical history of all of Apple's operating systems. 1 2 2 1 1.1. Apple's Quest for the[2] Operating System [2] Whereas the word "the" is used here to designate prominence and desirability, it is an interesting coincidence that "THE" was the name of a multiprogramming system described by Edsger W. Dijkstra in a 1968 paper. It was March 1988. The Macintosh had been around for four years. -

High Speed Data Link
High Speed Data Link Vladimir Stojanovic liheng zhu Electrical Engineering and Computer Sciences University of California at Berkeley Technical Report No. UCB/EECS-2017-72 http://www2.eecs.berkeley.edu/Pubs/TechRpts/2017/EECS-2017-72.html May 12, 2017 Copyright © 2017, by the author(s). All rights reserved. Permission to make digital or hard copies of all or part of this work for personal or classroom use is granted without fee provided that copies are not made or distributed for profit or commercial advantage and that copies bear this notice and the full citation on the first page. To copy otherwise, to republish, to post on servers or to redistribute to lists, requires prior specific permission. University of California, Berkeley College of Engineering MASTER OF ENGINEERING - SPRING 2017 Electrical Engineering and Computer Science Physical Electronics and Integrated Circuits Project High Speed Data Link Liheng Zhu This Masters Project Paper fulfills the Master of Engineering degree requirement. Approved by: 1. Capstone Project Advisor: Signature: __________________________ Date ____________ Print Name/Department: Vladimir Stojanovic, EECS Department 2. Faculty Committee Member #2: Signature: __________________________ Date ____________ Print Name/Department: Elad Alon, EECS Department Capstone Report Project High Speed Data Link Liheng Zhu A report submitted in partial fulfillment of the University of California, Berkeley requirements of the degree of Master of Engineering in Electrical Engineering and Computer Science March 2017 1 Introduction For our project, High-Speed Data Link, we are trying to implement a serial communication link that can operate at ~25Gb/s through a noisy channel. We decided to build a parameterized library to allow individual user to set up his/her own parameters according to the project specifications and requirements. -

THE FUTURE of HOME NETWORKING the Impact of Wi-Fi, Remote UI and Open Source Stacks on Service Provider Network Architecture
THE FUTURE OF HOME NETWORKING The Impact of Wi-Fi, Remote UI and Open Source Stacks on Service Provider Network Architecture Business Integration with Clarity The Future of Home Networking | pureIntegration Table of Contents 1 Introduction ................................................................................................. 2 2 Proposed Evolutions .................................................................................... 3 Authentication and WebUI .............................................................................................................. 5 Self-Healing/Diagnostic ................................................................................................................... 6 Security and Content Protection ..................................................................................................... 6 3 Gateway design impact ................................................................................ 7 4 CPE and IoT devices design impact ............................................................... 8 5 Proposed development and integration approach ....................................... 9 Phase 1: Interconnection tests with RDK-B or OpenWrt on Raspberry PI ...................................... 9 Phase 2: Authentication & Remote Management development on Raspberry PI .......................... 9 Phase 3: Port on Production Gateway ............................................................................................ 9 Phase 4: End to End Integration ................................................................................................... -

View on 5G Architecture
5G PPP Architecture Working Group View on 5G Architecture Version 3.0, June 2019 Date: 2019-06-19 Version: 3.0 Dissemination level: Public Consultation Abstract The 5G Architecture Working Group as part of the 5G PPP Initiative is looking at capturing novel trends and key technological enablers for the realization of the 5G architecture. It also targets at presenting in a harmonized way the architectural concepts developed in various projects and initiatives (not limited to 5G PPP projects only) so as to provide a consolidated view on the technical directions for the architecture design in the 5G era. The first version of the white paper was released in July 2016, which captured novel trends and key technological enablers for the realization of the 5G architecture vision along with harmonized architectural concepts from 5G PPP Phase 1 projects and initiatives. Capitalizing on the architectural vision and framework set by the first version of the white paper, the Version 2.0 of the white paper was released in January 2018 and presented the latest findings and analyses of 5G PPP Phase I projects along with the concept evaluations. The work has continued with the 5G PPP Phase II and Phase III projects with special focus on understanding the requirements from vertical industries involved in the projects and then driving the required enhancements of the 5G Architecture able to meet their requirements. The results of the Working Group are now captured in this Version 3.0, which presents the consolidated European view on the architecture design. Dissemination level: Public Consultation Table of Contents 1 Introduction........................................................................................................................ -

MURAC: a Unified Machine Model for Heterogeneous Computers
UNIVERSITY OF CAPE TOWN MURAC: A unified machine model for heterogeneous computers by Brandon Kyle Hamilton UniversityA thesis submitted of inCape fulfillment Town for the degree of Doctor of Philosophy in the Faculty of Engineering & the Built Environment Department of Electrical Engineering February 2015 The copyright of this thesis vests in the author. No quotation from it or information derived from it is to be published without full acknowledgement of the source. The thesis is to be used for private study or non- commercial research purposes only. Published by the University of Cape Town (UCT) in terms of the non-exclusive license granted to UCT by the author. University of Cape Town ABSTRACT MURAC: A unified machine model for heterogeneous computers by Brandon Kyle Hamilton February 2015 Heterogeneous computing enables the performance and energy advantages of multiple distinct processing architectures to be efficiently exploited within a single machine. These systems are capable of delivering large performance increases by matching the applications to architectures that are most suited to them. The Multiple Runtime- reconfigurable Architecture Computer (MURAC) model has been proposed to tackle the problems commonly found in the design and usage of these machines. This model presents a system-level approach that creates a clear separation of concerns between the system implementer and the application developer. The three key concepts that make up the MURAC model are a unified machine model, a unified instruction stream and a unified memory space. A simple programming model built upon these abstractions provides a consistent interface for interacting with the underlying machine to the user application. -

Mobile and Residential INEA Wi-Fi Hotspot Network Bartosz Musznicki, Karol Kowalik, Piotr Kołodziejski, and Eugeniusz Grzybek
PAPER INVITED TO 13TH INTERNATIONAL SYMPOSIUM ON WIRELESS COMMUNICATION SYSTEMS 2016, 20–23 SEPTEMBER 2016, POZNAN,´ POLAND 1 Mobile and Residential INEA Wi-Fi Hotspot Network Bartosz Musznicki, Karol Kowalik, Piotr Kołodziejski, and Eugeniusz Grzybek INEA, Poznan,´ Poland {bartosz.musznicki, karol.kowalik, piotr.kolodziejski, eugeniusz.grzybek}@inea.com.pl Abstract—Since 2012 INEA has been developing and expand- in Figure 1, which shows the changes in the number of users ing the network of IEEE 802.11 compliant Wi-Fi hotspots (access throughout an average day. Each data point corresponds to points) located across the Greater Poland region. This network a mean value obtained in the period of one month (further consists of 330 mobile (vehicular) access points carried by public buses and trams and over 20,000 fixed residential hotspots discussed in Section II-D). As in every graph in the paper, distributed throughout the homes of INEA customers to provide confidence intervals (error bars) present the standard deviation Internet access via the “community Wi-Fi” service. Therefore, of a data point. The graph for mobile network shows highest this paper is aimed at sharing the insights gathered by INEA numbers of users in the morning and in the afternoon what throughout 4 years of experience in providing hotspot-based corresponds to the busiest commuting hours. Stationary net- Internet access. The emphasis is put on daily and hourly trends in order to evaluate user experience, to determine key patterns, work, though, exhibits the highest usage in the evening what and to investigate the influences such as public transportation apparently relates to Internet activities performed at home. -

Gate-Level Leakage Assessment and Mitigation
Gate-level Leakage Assessment and Mitigation Tarun Kathuria Thesis submitted to the Faculty of the Virginia Polytechnic Institute and State University in partial fulfillment of the requirements for the degree of Master of Science in Computer Engineering Patrick R. Schaumont, Chair Cameron D. Patterson Xun Jian June 26, 2019 Blacksburg, Virginia Keywords: Side-channel leakage, Countermeasures, Power analysis attacks Copyright 2019, Tarun Kathuria Gate-level Leakage Assessment and Mitigation Tarun Kathuria (ABSTRACT) Side-channel leakage, caused by imperfect implementation of cryptographic algorithms in hardware, has become a serious security threat for connected devices that generate and process sensitive data. This side-channel leakage can divulge secret information in the form of power consumption or electromagnetic emissions. The side-channel leakage of a crytographic device is commonly assessed after tape-out on a physical prototype. This thesis presents a methodology called Gate-level Leakage Assessment (GLA), which evaluates the power-based side-channel leakage of an integrated circuit at design time. By combining side-channel leakage assessment with power simulations on the gate-level netlist, GLA is able to pinpoint the leakiest cells in the netlist in addition to assessing the overall side-channel vulnerability to side-channel leakage. As the power traces obtained from power simulations are noiseless, GLA is able to precisely locate the sources of side-channel leakage with fewer measurements than on a physical prototype. The thesis applies the methodology on the design of a encryption co-processor to analyze sources of side-channel leakage. Once the gate-level leakage sources are identified, this thesis presents a logic level replacement strategy for the leakage sources that can thwart side-channel leakage. -
Integrating E Verification IP in a VMM Testbench
Integrating e Verification IP in a VMM Testbench JL Gray Verilab [email protected] Adiel Khan Synopsys [email protected] 30 March 2010 ABSTRACT Modern testbenches often consist of components drawn from multiple languages. In many of these cases, multi-language and multi-methodology interaction is not well defined. In this paper, we will demonstrate the use of e verification components (eVCs) in a SystemVerilog/VMM testbench. Several complex issues arise when using SystemVerilog as the “primary” language. Initial simulator engine synchronization, random generation ordering, timing problems caused by program blocks, and methodology synchronization between the VMM and eRM will all be discussed. Copyright © 2010 Verilab, Inc. All rights reserved. Integrating e Verification IP in a VMM Testbench Contents 1 Overview ................................................................................................................... 3 1.1 Background .......................................................................................................... 3 1.2 Terminology ......................................................................................................... 4 1.3 Other Useful Terminology ................................................................................... 4 2 Challenges ................................................................................................................. 4 2.1 Method Ports ....................................................................................................... 4 2.2 -

The Journal for the International Ada Community
TThehe journaljournal forfor thethe internationalinternational AdaAda communitycommunity AdaAda UserUser Volume 41 Journal Number 1 Journal March 2020 Editorial 3 Quarterly News Digest 4 Conference Calendar 21 Forthcoming Events 29 Anniversary Articles J. Barnes From Byron to the Ada Language 31 C. Brandon CubeSat, the Experience 36 B.M. Brosgol How to Succeed in the Software Business while Giving Away the Source Code: The AdaCore Experience 43 Special Contribution J. Cousins ARG Work in Progress IV 47 Proceedings of the Workshop on Challenges and New Approaches for Dependable and Cyber-Physical Systems of Ada-Europe 2019 L. Nogueira, A. Barros, C. Zubia, D. Faura, D. Gracia Pérez, L.M. Pinho Non-functional Requirements in the ELASTIC Architecture 51 Puzzle J. Barnes Forty Years On and Going Strong 57 Produced by Ada-Europe Editor in Chief António Casimiro University of Lisbon, Portugal [email protected] Ada User Journal Editorial Board Luís Miguel Pinho Polytechnic Institute of Porto, Portugal Associate Editor [email protected] Jorge Real Universitat Politècnica de València, Spain Deputy Editor [email protected] Patricia López Martínez Universidad de Cantabria, Spain Assistant Editor [email protected] Kristoffer N. Gregertsen SINTEF, Norway Assistant Editor [email protected] Dirk Craeynest KU Leuven, Belgium Events Editor [email protected] Alejandro R. Mosteo Centro Universitario de la Defensa, Zaragoza, Spain News Editor [email protected] Ada-Europe Board Tullio Vardanega (President) Italy University -

Model-Driven Distributed Simulation Engineering
Proceedings of the 2019 Winter Simulation Conference N. Mustafee, K.-H.G. Bae, S. Lazarova-Molnar, M. Rabe, C. Szabo, P. Haas, and Y.-J. Son, eds. MODEL-DRIVEN DISTRIBUTED SIMULATION ENGINEERING Paolo Bocciarelli Andrea D’Ambrogio Andrea Giglio Emiliano Paglia Department of Enterprise Engineering University of Rome Tor Vergata Rome, Italy ABSTRACT Simulation-based analysis is widely recognized as an effective technique to support verification and validation of complex systems throughout their lifecycle. The inherently distributed nature of complex systems makes the use of distributed simulation approaches a natural fit. However, the development of a distributed simulation is by itself a challenging task in terms of effort and required know-how. This tutorial introduces an approach that applies highly automated model-driven engineering principles and standards to ease the development of distributed simulations. The proposed approach is framed around the development process defined by the DSEEP (Distributed Simulation Engineering and Execution Process) standard, as applied to distributed simulations based on the HLA (High Level Architecture), and is focused on a chain of automated model transformations. A case study is used in the tutorial to illustrate an example application of the proposed model-driven approach to the development of an HLA-based distributed simulation of a space system. 1 INTRODUCTION The development of complex systems strongly benefits from the adoption of quantitative analysis techniques that enable an early evaluation of the system behavior, so to assess, before starting implementation or maintenance activities, whether or not the to-be system is going to satisfy the stakeholder requirements and constraints. In this context, simulation-based techniques may be effectively introduced to enact the design-time evaluation of various structural and/or behavioral properties of the system under study. -

Software Maintenance Maturity Model (Smmm): the Software Maintenance Process Model
Software Maintenance Maturity Model (SMmm): The software maintenance process model Alain April1, Jane Huffman Hayes* ,†,2, Alain Abran1, and Reiner Dumke3 1Department of Software Engineering, Université du Québec, École de Technologie Supérieure, Canada 2Department of Computer Science, University of Kentucky, U.S.A. 3Department of Informatik, Otto von Guericke Universtity of Magdeburg, Germany. SUMMARY We address the assessment and improvement of the software maintenance function by proposing improvements to the software maintenance standards and introducing a proposed maturity model for daily software maintenance activities: Software Maintenance Maturity Model (SMmm). The software maintenance function suffers from a scarcity of management models to facilitate its evaluation, management, and continuous improvement. The SMmm addresses the unique activities of software maintenance while preserving a structure similar to that of the CMMi©4 maturity model. It is designed to be used as a complement to this model. The SMmm is based on practitioners’ experience, international standards, and the seminal literature on software maintenance. We present the model’s purpose, scope, foundation, and architecture, followed by its initial validation. Copyright © 2004 John Wiley & Sons, Ltd. J. Softw. Maint. And Evolution 2004; No. of Figures: 4. No. of Tables: 7. No. of References: 117. KEY WORDS: software maintenance; process improvement; process model; maturity model *Correspondence to: Jane Hayes, Computer Science, Laboratory for Advanced Networking, University of Kentucky, 301 Rose Street, Hardymon Building, Lexington, Kentucky 40506-0495 USA. †E-mail: [email protected] Contract/grant sponsor: none 1. INTRODUCTION Corporations that rely on revenues from developing and maintaining software now face a new, globally competitive market with increasingly demanding customers. -
Verilog HDL. a Guide to Digital Design and Synthesis
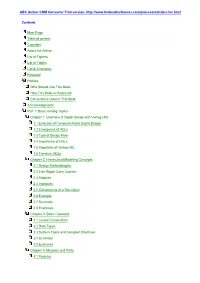
ABC Amber CHM Converter Trial version, http://www.thebeatlesforever.com/processtext/abcchm.html Contents Main Page Table of content Copyright About the Author List of Figures List of Tables List of Examples Foreword Preface Who Should Use This Book How This Book Is Organized Conventions Used in This Book Acknowledgments Part 1: Basic Verilog Topics Chapter 1. Overview of Digital Design with Verilog HDL 1.1 Evolution of Computer-Aided Digital Design 1.2 Emergence of HDLs 1.3 Typical Design Flow 1.4 Importance of HDLs 1.5 Popularity of Verilog HDL 1.6 Trends in HDLs Chapter 2. Hierarchical Modeling Concepts 2.1 Design Methodologies 2.2 4-bit Ripple Carry Counter 2.3 Modules 2.4 Instances 2.5 Components of a Simulation 2.6 Example 2.7 Summary 2.8 Exercises Chapter 3. Basic Concepts 3.1 Lexical Conventions 3.2 Data Types 3.3 System Tasks and Compiler Directives 3.4 Summary 3.5 Exercises Chapter 4. Modules and Ports 4.1 Modules ABC Amber CHM Converter Trial version, http://www.thebeatlesforever.com/processtext/abcchm.html 4.2 Ports 4.3 Hierarchical Names 4.4 Summary 4.5 Exercises Chapter 5. Gate-Level Modeling 5.1 Gate Types 5.2 Gate Delays 5.3 Summary 5.4 Exercises Chapter 6. Dataflow Modeling 6.1 Continuous Assignments 6.2 Delays 6.3 Expressions, Operators, and Operands 6.4 Operator Types 6.5 Examples 6.6 Summary 6.7 Exercises Chapter 7. Behavioral Modeling 7.1 Structured Procedures 7.2 Procedural Assignments 7.3 Timing Controls 7.4 Conditional Statements 7.5 Multiway Branching 7.6 Loops 7.7 Sequential and Parallel Blocks 7.8 Generate Blocks 7.9 Examples 7.10 Summary 7.11 Exercises Chapter 8.