Symantec {2000 }
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Manual Del Usuario De Norton Systemworks™
Manual del usuario de Norton SystemWorks™ 20% Minimum 07-30-00471-SL Manual del usuario de Norton SystemWorks™ El software que se describe en este manual se suministra con acuerdo de licencia y sólo puede utilizarse según los términos de dicho acuerdo. Información de copyright Copyright 1995-2001, Symantec Corporation. Todos los derechos reservados. Documentación, versión 5.0 Número de producto: 07-30-00471-SL SIN GARANTÍA. La presente documentación se proporciona tal cual es. Symantec Corporation no garantiza la precisión de la información en ella contenida ni se responsabiliza por el uso que de ella pueda hacerse. Cualquier utilización de la documentación técnica o de la información en ella contenida es responsabilidad del usuario. La documentación podría incluir inexactitudes técnicas o de otro tipo o errores tipográficos. Symantec se reserva el derecho de realizar cambios sin previo aviso. Queda prohibida la copia de esta publicación sin la autorización expresa por escrito de Symantec Corporation, Peter Norton Group, 20330 Stevens Creek Boulevard, Cupertino, CA 95014, EE.UU. Marcas comerciales Symantec, el logotipo de Symantec, Norton, Norton SystemWorks, Emergency Disk, LiveUpdate, Norton AntiVirus, Norton Utilities, Norton CleanSweep y Rescue Disk son marcas comerciales de Symantec Corporation. Process Viewer desarrollado en 1995-2001 por Igor Nys. GoBack y el logotipo de GoBack son marcas comerciales de Roxio, Inc. Windows es una marca comercial registrada de Microsoft Corporation. Pentium es marca comercial registrada de Intel Corporation. Otros nombres de productos mencionados en este manual pueden ser marcas comerciales de sus respectivos propietarios y se reconocen como tales. Impreso en los Estados Unidos de América. -
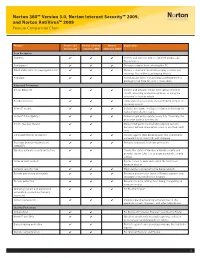
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton Antivirus™ 2009 Feature Comparison Chart
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton AntiVirus™ 2009 Feature Comparison Chart Feature Norton 360 Norton Internet Norton Explanation Version 3.0 Security 2009 AntiVirus 2009 Core Protection Antivirus ✔ ✔ ✔ Detects and removes viruses, Internet worms, and Trojan horses Antispyware ✔ ✔ ✔ Prevents spyware from infecting the PC Email and instant messaging protection ✔ ✔ ✔ Monitors email and instant messaging so users can exchange files without exchanging threats Antispam ✔ ✔ Automatically filters out annoying and fraudulent or phishing email from the user’s email inbox Advanced Protection Botnet detection ✔ ✔ ✔ Detects and prevents others from taking control of the PC, accessing private information, or using the computer to host an attack Rootkit detection ✔ ✔ ✔ Finds and removes threats that are hidden deep in the operating system Norton™ Insight ✔ ✔ ✔ Includes innovative, intelligence-driven technology for faster, fewer, shorter scans Norton™ Pulse Updates ✔ ✔ ✔ Delivers rapid pulse updates every 5 to 15 minutes for protection against new threats Smart, two-way firewall ✔ ✔ Makes intelligent incoming and outgoing security decisions without interrupting users to ask them each time Enhanced browser protection ✔ ✔ ✔ Secures against Web-based attacks that use browser vulnerabilities to infect PCs with malware Real-time behavioral protection ✔ ✔ ✔ Provides enhanced, real-time protection (SONAR™) Wireless network security protection ✔ ✔ Checks the status of wireless network security and provides expert advice on managing -
Desktop Messaging for Internet Clients
CallPilotTM Release 2.5 Desktop Messaging User Guide for Internet Clients Updates to the Desktop Messaging User Guides Internet Clients Page 7 Call the sender of a message Call the sender of a message is not supported. Page 7 Access web-based My CallPilot to view user information and change your feature settings My CallPilot is not supported. Page 8 About this guide The Internet mail clients that are supported are: • Microsoft Outlook 2000 (Internet mail mode) • Microsoft Outlook 2002 (XP) (Internet mail mode) • Microsoft Outlook 2003 (Internet mail mode) • Microsoft Outlook Express - 5.x and 6.x • Netscape Messenger (Netscape Communicator) - 6.2x • Netscape Mail - 7.0x • Qualcomm Eudora Pro - 6.1.2 Citrix (Terminal server) functionality is supported. Page 11 CallPilot Player The Call the sender button is not available. Page 11 To select your telephone or computer to play voice messages If your telephone is call forwarded to voicemail, cancel this feature before you access your messages from CallPilot Player. Page 29 Linking to My CallPilot Linking to My CallPilot is not supported. About forwarding Desktop Messaging messages Do not use the right-click menu to forward a Desktop Messaging message. To forward a message, either: • open the message and forward it from the CallPilot window or • for Outlook, select the message in the Outlook Inbox and forward it from the Outlook toolbar. Business Communications Manager & CallPilot 100/150 Outlook, Lotus Notes, GroupWise Page 7 Call the sender of a message Call the sender of a message is not supported. Page 7 Access web-based My CallPilot to view user information and change your feature settings My CallPilot is not supported. -

Symantec Software Datasheet
Data Sheet: Endpoint Management Altiris™ Client Management Suite 7.0 Deploy, manage, secure, and troubleshoot Overview The suite delivers tools that are based on the IT The cost of a PC is only a small part of its total cost. Infrastructure Library (ITIL) to help align processes with Nearly 80 percent of the total cost of owning a client industry best practices so you can more efficiently system goes toward the support and maintenance of manage your client systems. the PC. Altiris™ Client Management Suite from Symantec automates time-consuming and redundant tasks to reduce the effort and costs associated with deploying, managing, securing, and troubleshooting client systems so organizations can gain control of their IT environments. Client Management Suite Delivers Client Management Suite ushers in a new generation of systems management by bringing end users, administrators, and key business decision makers Altiris Client Management Suite deploys, manages, secures, and together. The suite helps you align with organizational troubleshoots systems through the entire IT lifecycle. You can manage more technologies, with greater efficiency, on more objectives by providing easy-to-use self-service tools to platforms. users, powerful management tools to IT administrators, and custom dashboards to decision makers. Client Management Suite provides complete visibility into your organization's client systems so you can see Finding extra time is challenging, yet that's what Client what you have, where it's located, and what state it's in. Management Suite is designed to do. Now you can focus The suite's flexible and actionable reporting tools not on key initiatives that can help your business grow. -

Strike First
GET UP TO $ BACK30 THE RISE OF COBRA Via Mail-In Rebate* ONly IN Theaters STRWITH ITKHEE SPEED FIR OFS NOTRTON * Receive $30 via mail-in rebate with the purchase of Norton™ Internet Security 2009 or $20 with the purchase of Norton™ AntiVirus 2009. Offer good for purchases made between 6/21/09 and 10/19/09 at participating retailers. Rebate submissions must be postmarked within 30 days of purchase. Limit one rebate per product per customer. Read below or visit www.norton.com/gijoe for complete Terms and Conditions. To receive your rebate from Symantec, please follow these steps: Terms and Conditions 1. Purchase Norton™ Internet Security 2009 or Norton™ AntiVirus 2009 between 6/21/09 and 10/19/09 • The G.I. Joe rebate offer is valid only for stand-alone, retail (boxed or downloaded) purchases of Norton at a participating retailer (Norton Internet Security 2009 customers receive a $30 Visa® Prepaid Card. Internet Security 2009 and Norton AntiVirus 2009. Purchases must be made between 6/21/09 and Norton AntiVirus 2009 customers receive a $20 Visa Prepaid Card. Purchases made from Office Depot 10/19/09 at a participating retailer. Offer not available with site licenses, trialware, NFRs, products will receive their rebate in the form of a check.). pre-installed or supplied by a manufacturer (OEM), multi-user packs (other than Norton Internet Security 2. Read and complete this rebate request form. Or you can pre-submit your rebate at for 3-users), academic offers, auction purchases, or with any other offer except the upgrade/competitive www.symantecrebates.com. -

Essential Trends and Dynamics of the Endpoint Security Industry
Essential Trends and Dynamics of the Endpoint Security Industry Lenny Zeltser wrote this paper together with a co-author who chose to remain anonymous. May 2005 This paper examines trends and dynamics of the endpoint security industry, and shows how business strategies of market leaders such as Symantec exemplify these factors. When exploring current developments in the information security marketplace, we stipulate that this sector is beginning to converge with the general IT software industry in response to factors such as the evolution of the industry structure, competitive dynamics, regulatory compliance efforts, and the maturing state of security products. Lenny Zeltser & Co-Author Page 1 Table of Contents Introduction ......................................................................................................................... 2 Characteristics of the Endpoint Security Industry........................................................... 2 Scope of the Industry ............................................................................................................ 2 Industry Size Estimates.........................................................................................................3 Structural Characteristics of the Industry............................................................................... 3 Competitive Dynamics........................................................................................................... 4 Industry Evolution: From 1990 to 2005 ............................................................................ -

Antivirus – Internet Security Software
AntiVirus – Internet Security Software Recommended AntiVirus Software to use with OfficeEMR™: Norton AntiVirus Symantec Endpoint Protection Business Class – Enterprise – AntiVirus Solution AntiVirus ONLY software products WITHOUT additional Firewalls What Happens with Internet Security Software Products and OfficeEMR™: Provide an additional Firewall and/or Shields Can prevent you from accessing secure Web Sites such as https://www.officemd.net Scan every Web Page that you go to when it loads Can make screens in OfficeEMR™ take a long time to load Can prevent our AutoConfigure from running Can prevent scanning documents into OfficeEMR™ from completing What You Can Do: Setup our Web Site www.officemd.net as an exception in its Firewall. --- or --- Turn off (Disable) the additional Firewall included and / or applicable Shields Contact Technical Support via the software company’s Web Site o many offer e-mail, phone, and/or chat for technical support o get help with and options available to be able to access secure (https://...) Web --- or --- Sites o get help with and options available for making www.officemd.net an exception o get help with and options available for turning off their Firewall and / or applicable Shields. --- or --- Uninstall and Install the AntiVirus ONLY version of that software product. --- or --- Uninstall and Install a different AntiVirus ONLY software product. Revised 05/2009 AntiVirus – Internet Security Software More Detailed Information: Internet Security Software Products provide an added Firewall and / or Shields to help block malicious content or Web Sites while surfing on the Web. Without changing settings, by default, Internet Security Software Products will scan every Web Page that you go to when it loads. -
“Global Positioning Systems” GPS Mean Never Having to Say “I’M Lost”?
APRIL 2003 VOLUME 19 NUMBER 4 PPCUGPPCUG NEWS A PUBLICATION OF THE PRINCETON PC USERS GROUP Monday April 14, 2003 “Global Positioning Systems” GPS mean never having to say “I’m Lost”? Don Arrowsmith will demonstrate the Garmin Street Pilot III Auto Navigation unit and the MapSource PC software. At Lawrence Library Meetng Rooms 1 & 2 US Route 1 South & Darrah Lane, Lawrenceville, NJ Meetings of an organization at any of the facilities of the Mercer County Library System in No Way implies endorsement of its programs In this issue About PPCUG............................................. 2 Presidents Message .................................. 2 Parcel Pick-up @TCF2003 ........................ 2 Backups-Lite .............................................. 3 New Year’s Resolutions ............................ 4 Member E-mail Directory .......................... 5 General Meeting Minutes ........ Back Cover Digital Photo by: Tom Carman Tom Digital Photo by: President Clarke Walker making his opening remarks to the group at the March general meeting. About PPCUG General Meetings Coming Events Second Monday of the month at the May 3 & 4, 2003 - Trenton Computer Festival Lawrenceville Library. Route 1 and Darrah Lane. May 12, 2003 - Lindow Operating System - Jim Russ 7:00-7:45 PM: Social Time / Tech Corner June 9, 2003 - Batch Files & Scripting - Vic Laurie 7:45 PM: Meeting Comes to Order 8 PM: Featured Presentation July 14, 2003 - Music & Video on Your PC - Don Slepian For information about upcoing meetings or joining PPCUG call 908-218-0778 to leave a message. Board Meetings Presidents Message For Meeting Location, Date and Time, call By: Clarke Walker 908-218-0778 Board meetings are open to All. I want to thank everyone who participated in last month’s “Digital Camera Show, Tell and Shoot”. -

Zerohack Zer0pwn Youranonnews Yevgeniy Anikin Yes Men
Zerohack Zer0Pwn YourAnonNews Yevgeniy Anikin Yes Men YamaTough Xtreme x-Leader xenu xen0nymous www.oem.com.mx www.nytimes.com/pages/world/asia/index.html www.informador.com.mx www.futuregov.asia www.cronica.com.mx www.asiapacificsecuritymagazine.com Worm Wolfy Withdrawal* WillyFoReal Wikileaks IRC 88.80.16.13/9999 IRC Channel WikiLeaks WiiSpellWhy whitekidney Wells Fargo weed WallRoad w0rmware Vulnerability Vladislav Khorokhorin Visa Inc. Virus Virgin Islands "Viewpointe Archive Services, LLC" Versability Verizon Venezuela Vegas Vatican City USB US Trust US Bankcorp Uruguay Uran0n unusedcrayon United Kingdom UnicormCr3w unfittoprint unelected.org UndisclosedAnon Ukraine UGNazi ua_musti_1905 U.S. Bankcorp TYLER Turkey trosec113 Trojan Horse Trojan Trivette TriCk Tribalzer0 Transnistria transaction Traitor traffic court Tradecraft Trade Secrets "Total System Services, Inc." Topiary Top Secret Tom Stracener TibitXimer Thumb Drive Thomson Reuters TheWikiBoat thepeoplescause the_infecti0n The Unknowns The UnderTaker The Syrian electronic army The Jokerhack Thailand ThaCosmo th3j35t3r testeux1 TEST Telecomix TehWongZ Teddy Bigglesworth TeaMp0isoN TeamHav0k Team Ghost Shell Team Digi7al tdl4 taxes TARP tango down Tampa Tammy Shapiro Taiwan Tabu T0x1c t0wN T.A.R.P. Syrian Electronic Army syndiv Symantec Corporation Switzerland Swingers Club SWIFT Sweden Swan SwaggSec Swagg Security "SunGard Data Systems, Inc." Stuxnet Stringer Streamroller Stole* Sterlok SteelAnne st0rm SQLi Spyware Spying Spydevilz Spy Camera Sposed Spook Spoofing Splendide -

Third BUSINES Superbrands-2010-Final 6/1/11 12:46 PM Page 92
Third BUSINES Superbrands-2010-final 6/1/11 12:46 PM Page 92 Market safeguard and keep open cyber highways is a imminently powerful, year after year. Cyberspace is full of creepy crawlies. Consider source of abiding comfort for millions of In 2007, for instance, International Data the latest gremlins – Pillenz, Bamital, Sefrnit, internet users. Corporation (IDC) recognised Symantec in a Pylespa, Daonol, Zbot and Tidserv and add the Its success can be attributed to keeping its wide range of award categories including Data old, broad-spectrum favourites, spyware, adware, ears to the ground and developing technologies Protection and Recovery; Cross-platform worms, viruses, trojans and spam and you’ve that synchronise with the needs of customers. provider of Clustering and Availability; Email entered the world of cyber crime.These are the To accomplish this feat the company has created Archiving Applications; Security and Vulnerability pests which have made working on a PC or a unique web called the Symantec Global Management; and Policy and Compliance, and laptop a forgettable nightmare.The universal Intelligence Network.This is an extraordinary Host and Vulnerability Software; plus an award quest for a protector has thrown up several resource which provides a real-time view of for software developed for Messaging Security names but the one that has become virtually emerging digital threats almost anywhere in the and Virus Protection. synonymous with computer software, world. With more than 40,000 sensors in 180 In the same year, Gartner rated the company particularly in the realms of security and countries and more than 6200 managed security as Global Market Share Leader in Enterprise information management, is Symantec. -

Overview of Client Management Suite 7.1 Hands-On Lab
Overview of Client Management Suite 7.1 Hands-On Lab Description If you are new to Altiris Client Management Suite, this lab is an excellent place to start. This introduction lab provides a hands-on overview of the suite going through many steps of IT lifecycle management. It includes the basics on software and patch management, deployment, migration, remote assistance, and more to start you on your path to effective client management. At the end of this lab, • Create an inventory policy and run reports to view the you should be able to collected data • Describe the available methods for delivering and metering software within a real-world environment • Describe the process of staging and deploying patches to systems and applications within a network environment • Use Deployment Solution 7.1 to perform an OS Migration Notes . The lab will be directed and will provide you with step-by- step walkthroughs of key features. Feel free to follow along with the instructor, or you may optionally perform this lab at your own pace. Be sure to ask your instructor any questions you may have. Thank you for coming to our lab session. Introduction Altiris® Client Management Suite™ reduces the total cost of owning client systems by automating time-consuming and redundant tasks. By minimizing the efforts and costs associated with deploying, managing, securing and troubleshooting client systems, organizations can gain control of their environments. This easy-to-use, integrated suite of solution software for Windows, Mac and Linux is designed to address IT management needs for desktop and notebook computers throughout their entire IT lifecycle. -

India Business Volume 2 Symantec Size
Business Superbrands- 2nd edition(Main) 8/27/08 4:12 AM Page 136 Market 30% of the world’s email traffic. At the as Global Market Share Leader in Enterprise Adware, spyware, worms, viruses, trojans, company’s three security operation centres – Backup; Backup and Recovery Software; Core spam… computer users the world over are one of which is in India – employees analyse Storage Management Software; and Email Active now familiar with these gremlins that often and correlate emerging threats to help Archiving. Between 2006 and 2007, in the make working on a PC or laptop a nightmare. customers prepare for and withstand attacks. Gartner Magic Quadrants, the company was There is a universal quest for a protector.The Powerful protection – and only available from listed as a leader in PC Configuration Life Cycle one name that has become virtually Symantec – is the company credo. Its pedigree Management; Managed Security Services synonymous with computer software, is supported by other illustrious names and Providers (NA); Storage Services; Security particularly in the realms of security and includes industry leaders such as Veritas, Altiris Information and Event Management; Email information management is Symantec. and Brightmail (Source: archival data). Active Archiving; Content Monitoring and Headquartered in Cupertino, California, the Filtering for Data Loss Prevention and Email US$ 5.19 billion (Rs. 20,760 crore) company Achievements Security Boundary. operates in more than 40 countries and is part Its aptitude to successfully integrate acquired During the last two years, the accolades and of the NASDAQ and Fortune 500 listing. technologies has kept Symantec at the front of recognition have been overwhelming.