Norton 360 User Guide on the CD Or the USB Drive in PDF Format
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Manual Del Usuario De Norton Systemworks™
Manual del usuario de Norton SystemWorks™ 20% Minimum 07-30-00471-SL Manual del usuario de Norton SystemWorks™ El software que se describe en este manual se suministra con acuerdo de licencia y sólo puede utilizarse según los términos de dicho acuerdo. Información de copyright Copyright 1995-2001, Symantec Corporation. Todos los derechos reservados. Documentación, versión 5.0 Número de producto: 07-30-00471-SL SIN GARANTÍA. La presente documentación se proporciona tal cual es. Symantec Corporation no garantiza la precisión de la información en ella contenida ni se responsabiliza por el uso que de ella pueda hacerse. Cualquier utilización de la documentación técnica o de la información en ella contenida es responsabilidad del usuario. La documentación podría incluir inexactitudes técnicas o de otro tipo o errores tipográficos. Symantec se reserva el derecho de realizar cambios sin previo aviso. Queda prohibida la copia de esta publicación sin la autorización expresa por escrito de Symantec Corporation, Peter Norton Group, 20330 Stevens Creek Boulevard, Cupertino, CA 95014, EE.UU. Marcas comerciales Symantec, el logotipo de Symantec, Norton, Norton SystemWorks, Emergency Disk, LiveUpdate, Norton AntiVirus, Norton Utilities, Norton CleanSweep y Rescue Disk son marcas comerciales de Symantec Corporation. Process Viewer desarrollado en 1995-2001 por Igor Nys. GoBack y el logotipo de GoBack son marcas comerciales de Roxio, Inc. Windows es una marca comercial registrada de Microsoft Corporation. Pentium es marca comercial registrada de Intel Corporation. Otros nombres de productos mencionados en este manual pueden ser marcas comerciales de sus respectivos propietarios y se reconocen como tales. Impreso en los Estados Unidos de América. -
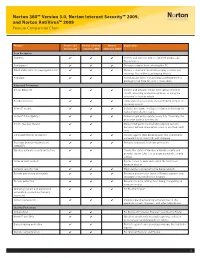
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton Antivirus™ 2009 Feature Comparison Chart
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton AntiVirus™ 2009 Feature Comparison Chart Feature Norton 360 Norton Internet Norton Explanation Version 3.0 Security 2009 AntiVirus 2009 Core Protection Antivirus ✔ ✔ ✔ Detects and removes viruses, Internet worms, and Trojan horses Antispyware ✔ ✔ ✔ Prevents spyware from infecting the PC Email and instant messaging protection ✔ ✔ ✔ Monitors email and instant messaging so users can exchange files without exchanging threats Antispam ✔ ✔ Automatically filters out annoying and fraudulent or phishing email from the user’s email inbox Advanced Protection Botnet detection ✔ ✔ ✔ Detects and prevents others from taking control of the PC, accessing private information, or using the computer to host an attack Rootkit detection ✔ ✔ ✔ Finds and removes threats that are hidden deep in the operating system Norton™ Insight ✔ ✔ ✔ Includes innovative, intelligence-driven technology for faster, fewer, shorter scans Norton™ Pulse Updates ✔ ✔ ✔ Delivers rapid pulse updates every 5 to 15 minutes for protection against new threats Smart, two-way firewall ✔ ✔ Makes intelligent incoming and outgoing security decisions without interrupting users to ask them each time Enhanced browser protection ✔ ✔ ✔ Secures against Web-based attacks that use browser vulnerabilities to infect PCs with malware Real-time behavioral protection ✔ ✔ ✔ Provides enhanced, real-time protection (SONAR™) Wireless network security protection ✔ ✔ Checks the status of wireless network security and provides expert advice on managing -
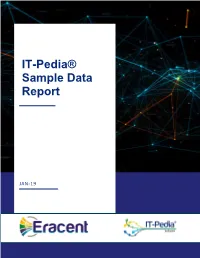
IT-Pedia® Sample Data Report
IT-Pedia® Sample Data Report JAN-19 IT-Pedia® Sample Data Report NO. Product_ID HeaderName AttributeName AttributeValue 1 97310 General Information Manufacturer Autodesk, Inc Manufacturer Part Number 05718-011408-9000 Manufacturer Website Address http://www.autodesk.com Brand Name Autodesk Product Name AutoCAD LT 2004 Marketing Information AutoCAD LT 2004 software streamlines the 2D design process with drafting and collaboration tools for efficient data creation and secure data sharing-all at an affordable price. Packaged Quantity 1 Package Type Retail Distribution Media/Method CD-ROM Product Type Software Product Information Software Main Type Design & Engineering Software Sub Type CAD Software Name AutoCAD LT 2004 Features * Software compatibility-through object enablers that read custom objects created in industry-specific Autodesk applications such as Autodesk Architectural Desktop; as well as 100 percent DWG compatibility with AutoCAD 2004 and AutoCAD 2004-based software, for trouble-free design collaboration. Min Supported Color Depth: * 24-bit (16.7M colors) Features: Here are the key AutoCAD LT 2004 features. 1\. Optimized DWG File Format: The optimized AutoCAD LT 2004 DWG file format cuts file sizes in half compared to AutoCAD LT 2002* reducing of the amount of required disk space on hard drives and servers. The new DWG file format enables drawings to be quickly transmitted via networks, email, and collaboration services such as Autodesk Language SupportedBuzzsaw. English Platform Supported PC Main Features * Complete package -

Norton Antivirus for Windows 10 Free Download Full Version Norton 360 for Windows
norton antivirus for windows 10 free download full version Norton 360 for Windows. Virus scanner, firewall, data backup, anti-theft and parental control - Norton 360 target’s all those user that like to use only one program for their digital protection. An intuitive user interface allows for easy execution of all above tasks. Hard-disks, memory cards, USB drives and other media can be scanned for viruses, trojans and spyware either ad-hoc or on a regular basis. The Anti-virus signature frequently updates automatically to ensure protection against latest malware and viruses. Backups can be stored locally or online in Symantec’s cloud storage. A browser extension warns users of web threats. This includes highlighting malicious search results on Google, Bing and Yahoo. To protect user identity, login data like usernames and passwords are encrypted and saved on Symantec’s secure servers. Technical. Windows XP, Windows 7, Windows Vista, Windows 8, Windows 10 English, German, Spanish, French, Italian, Japanese, Polish, Chinese. Norton 360 for PC. User rating User Rating. Changelog. We don't have any change log information yet for version 21.3.0.12 of Norton 360. Sometimes publishers take a little while to make this information available, so please check back in a few days to see if it has been updated. Can you help? If you have any changelog info you can share with us, we'd love to hear from you! Head over to ourContact pageand let us know. Explore Apps. Related Software. GridinSoft Anti-Malware. GridinSoft Anti-Malware (formerly Trojan Killer) is a specialised app that is designed to target numerous different types of malware, including PUPs, spyware, adware, trojans and worms etc. -

Amit a Windows 7
DVD DVD Többé nem fog akadozni az internet 11 Friss 9 GB 2009 A LEGÚJABB DRIVEREK, HASZNOS PROGRAMOK, Megmutatjuk, hogyan kell beállítani a rejtélyes Qos-t – lépésről lépésre R 90 A HÓNAP JÁTÉKAI, EXKLUZÍV CSOMAgok… 9 tipp: tökéletes TFT-képminőség Nem kell drága pénzen új monitor! Profin beállítjuk a mostanit R 98 GO DIGITAL! 2009/11_ CHIPONLINE.HU Ennyire (nem) biztonságos a vírusirtója – felfedjük! A DVD-N: Tesztünkből kiderül, hogy miért csődöl be sok víruskereső éles helyzetben R 40 es VÍRUSVADÁSZ teLJ CSOMAG Amit a Windows 7 jobban tud… 46 Gyors sikerek! Több gépre... Csak a CHIP-en! R TELJES VERZIÓ TELJES VERZIÓ TELJES VERZIÓ Egyedi, vicces, ...Szinkroni- Sytem Backup: …és, amin még javítani kell. Az összes új funkció szórakoztató zálás, mentés, vadonatúj, családi album megosztás 2010-es verzió és rejtett képesség tesztje + a Win 7 mint második rendszer Szimatolók a PC-jén? Segítünk! A legjobb eszközök az adatlopás ellen: 100% anonim szörf és levelezés R 26 Zseniális új funkciók eszközeihez T ESZ pt 20 tipp, melyekkel lenyűgöző tulajdonságokat LA TOVÁBBI DVD-TARTALOM 58 P R csalogathat elő átlagos hardvereiből 84 Radeon HD5870 Radeon teszt >> HD5870 10 tény a CPU-król >> Új technológiák: OpenID >> Mozizzunk óriástévén >> Gyorsteszt: P55-ös alaplapok >> Rés a víruspajzson >> Ennyire jó a 7 Windows >> CHIP mini PC >> 20 dolog, amit nem tudott… >> Soha többé net akadozó 1995 Ft, előfizetéssel 1395 Ft R XXI. évfolyam, 11. szám, 2009. november P55-ÖSz ALA asztali PC-k 36 Kiadja a Motor-Presse Budapest Lapkiadó Kft. A forradalma R CD CD Többé nem fog akadozni az internet 11 melléklettel 2009 EXKLUZÍV CSOMAGOK, FRISS Megmutatjuk, hogyan kell beállítani a rejtélyes Qos-t – lépésről lépésre R 90 PROGRAMOK, VÍRUSVÉDELEM.. -

Strike First
GET UP TO $ BACK30 THE RISE OF COBRA Via Mail-In Rebate* ONly IN Theaters STRWITH ITKHEE SPEED FIR OFS NOTRTON * Receive $30 via mail-in rebate with the purchase of Norton™ Internet Security 2009 or $20 with the purchase of Norton™ AntiVirus 2009. Offer good for purchases made between 6/21/09 and 10/19/09 at participating retailers. Rebate submissions must be postmarked within 30 days of purchase. Limit one rebate per product per customer. Read below or visit www.norton.com/gijoe for complete Terms and Conditions. To receive your rebate from Symantec, please follow these steps: Terms and Conditions 1. Purchase Norton™ Internet Security 2009 or Norton™ AntiVirus 2009 between 6/21/09 and 10/19/09 • The G.I. Joe rebate offer is valid only for stand-alone, retail (boxed or downloaded) purchases of Norton at a participating retailer (Norton Internet Security 2009 customers receive a $30 Visa® Prepaid Card. Internet Security 2009 and Norton AntiVirus 2009. Purchases must be made between 6/21/09 and Norton AntiVirus 2009 customers receive a $20 Visa Prepaid Card. Purchases made from Office Depot 10/19/09 at a participating retailer. Offer not available with site licenses, trialware, NFRs, products will receive their rebate in the form of a check.). pre-installed or supplied by a manufacturer (OEM), multi-user packs (other than Norton Internet Security 2. Read and complete this rebate request form. Or you can pre-submit your rebate at for 3-users), academic offers, auction purchases, or with any other offer except the upgrade/competitive www.symantecrebates.com. -

Computer Virus 16 Views 0 0 RELATED TITLES Virus
16 views 0 0 RELATED TITLES Virus Uploaded by Abu Naser Mohammad Saif Full description Save Embed Share Print Steve Jobs Cryptonomicon The Woman Who Smashed Codes: A True Computer Virus 16 views 0 0 RELATED TITLES Virus Uploaded by Abu Naser Mohammad Saif Full description Save Embed Share Print Steve Jobs Cryptonomicon The Woman Who Smashed Codes: A True Presentation Outline 1. Introduction: 2. VIRUS Definition and Naming: 3. Types of computer virus: 4. Example of Virus 5. To phases of virus 6. Symptom of computer attacked by virus 7. Special focus on: Trojan, & phishing site 8. Combating Viruses 9. Anti viruses & Firewall 16 views 0 0 RELATED TITLES Virus Uploaded by Abu Naser Mohammad Saif Full description Save Embed Share Print Steve Jobs Cryptonomicon The Woman Who Smashed Codes: A True Presentation Outline Symptom of computer attacked by virus Special focus on: Trojan, & phishing site Combating VirusesAnti viruses & Firewall 16 views 0 0 RELATED TITLES Virus Uploaded by Abu Naser Mohammad Saif Full description Save Embed Share Print Steve Jobs Cryptonomicon The Woman Who Smashed Codes: A True Presentation Outline 1. Introduction: 2. VIRUS Definition and Naming: 3. History of Computer Virus: 4. Types of computer virus: 5. Example of Virus 6. To phases of virus: 16 views 0 0 RELATED TITLES Virus Uploaded by Abu Naser Mohammad Saif Full description Save Embed Share Print Steve Jobs Cryptonomicon The Woman Who Smashed Codes: A True Introduction: Computer VIRUS Almost every uses has faced virus attack And loses some sort of computer resources Computer VIRUS is not a biological element rather computer program (s). -

Norton Antivirus Product Manual
NortonTM AntiVirus Product Manual Care for our Environment; ‘It's the right thing to do.’ Symantec has removed the cover from this manual to reduce the Environmental Footprint of our products. This manual is made from recycled materials. Norton AntiVirus™ Product Manual The software described in this book is furnished under a license agreement and may be used only in accordance with the terms of the agreement. Documentation version 21.4 Copyright © 2014 Symantec Corporation. All rights reserved. Symantec, the Symantec Logo, LiveUpdate, Norton 360, and Norton are trademarks or registered trademarks of Symantec Corporation or its affiliates in the U.S. and other countries. Portions of this product Copyright 1996-2011 Glyph & Cog, LLC. Other names may be trademarks of their respective owners. The product described in this document is distributed under licenses restricting its use, copying, distribution, and decompilation/reverse engineering. No part of this document may be reproduced in any form by any means without prior written authorization of Symantec Corporation and its licensors, if any. THE DOCUMENTATION IS PROVIDED “AS IS” AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. SYMANTEC CORPORATION SHALL NOT BE LIABLE FOR INCIDENTAL OR CONSEQUENTIAL DAMAGES IN CONNECTION WITH THE FURNISHING, PERFORMANCE, OR USE OF THIS DOCUMENTATION. THE INFORMATION CONTAINED IN THIS DOCUMENTATION IS SUBJECT TO CHANGE WITHOUT NOTICE. The Licensed Software and Documentation are deemed to be commercial computer software as defined in FAR 12.212 and subject to restricted rights as defined in FAR Section 52.227-19 "Commercial Computer Software - Restricted Rights" and DFARS 227.7202, et seq. -

Zerohack Zer0pwn Youranonnews Yevgeniy Anikin Yes Men
Zerohack Zer0Pwn YourAnonNews Yevgeniy Anikin Yes Men YamaTough Xtreme x-Leader xenu xen0nymous www.oem.com.mx www.nytimes.com/pages/world/asia/index.html www.informador.com.mx www.futuregov.asia www.cronica.com.mx www.asiapacificsecuritymagazine.com Worm Wolfy Withdrawal* WillyFoReal Wikileaks IRC 88.80.16.13/9999 IRC Channel WikiLeaks WiiSpellWhy whitekidney Wells Fargo weed WallRoad w0rmware Vulnerability Vladislav Khorokhorin Visa Inc. Virus Virgin Islands "Viewpointe Archive Services, LLC" Versability Verizon Venezuela Vegas Vatican City USB US Trust US Bankcorp Uruguay Uran0n unusedcrayon United Kingdom UnicormCr3w unfittoprint unelected.org UndisclosedAnon Ukraine UGNazi ua_musti_1905 U.S. Bankcorp TYLER Turkey trosec113 Trojan Horse Trojan Trivette TriCk Tribalzer0 Transnistria transaction Traitor traffic court Tradecraft Trade Secrets "Total System Services, Inc." Topiary Top Secret Tom Stracener TibitXimer Thumb Drive Thomson Reuters TheWikiBoat thepeoplescause the_infecti0n The Unknowns The UnderTaker The Syrian electronic army The Jokerhack Thailand ThaCosmo th3j35t3r testeux1 TEST Telecomix TehWongZ Teddy Bigglesworth TeaMp0isoN TeamHav0k Team Ghost Shell Team Digi7al tdl4 taxes TARP tango down Tampa Tammy Shapiro Taiwan Tabu T0x1c t0wN T.A.R.P. Syrian Electronic Army syndiv Symantec Corporation Switzerland Swingers Club SWIFT Sweden Swan SwaggSec Swagg Security "SunGard Data Systems, Inc." Stuxnet Stringer Streamroller Stole* Sterlok SteelAnne st0rm SQLi Spyware Spying Spydevilz Spy Camera Sposed Spook Spoofing Splendide -

Norton 360 Guide De L'utilisateur
Guide de l'utilisateur Pour une installation rapide, voir au verso. Prenons soin de notre environnement. Nous avons décidé de supprimer la couverture de ce manuel afin de réduire l'empreinte écologique de nos produits. Ce manuel est constitué à partir de matériaux recyclés. Norton 360™ Guide de l'utilisateur Le logiciel décrit dans ce manuel est fourni dans le cadre d'un contrat de licence et ne peut être utilisé qu'en accord avec les termes de ce contrat. Documentation version 6.0 Copyright © 2011 Symantec Corporation. Tous droits réservés. Symantec, le logo Symantec, LiveUpdate, Norton 360 et Norton sont des marques commerciales ou déposées de Symantec Corporation ou de ses sociétés affiliées aux Etats-Unis et dans d'autres pays. Copyright sur les parties de ce produit 1996-2011 Glyph & Cog, LLC. Les autres noms peuvent être des marques de leurs détenteurs respectifs. Le produit décrit dans ce document est distribué aux termes d'une licence limitant son utilisation, sa copie, sa distribution et sa décompilation/ingénierie inverse. Ce document ne peut, en tout ou partie, être reproduit sous aucune forme et par aucun moyen sans l'autorisation préalable écrite de Symantec Corporation et de ses concédants éventuels. LA DOCUMENTATION EST FOURNIE "EN L'ETAT" ET TOUTE GARANTIE OU CONDITION D'AUCUNE SORTE, EXPRESSE OU IMPLICITE, Y COMPRIS, SANS QUE CELA SOIT LIMITATIF, LES GARANTIES OU CONDITIONS IMPLICITES DE QUALITE MARCHANDE, D'ADEQUATION A UN USAGE PARTICULIER OU DE RESPECT DES DROITS DE PROPRIETE INTELLECTUELLE EST REFUTEE, EXCEPTÉ DANS LA MESURE OÙ DE TELLES EXCLUSIONS SERAIENT TENUES POUR LEGALEMENT NON VALIDES. -

Wsn, COURT STAFF) (Filed on 8/23/2013
Haskins v. Symantec Corporation Doc. 32 1 2 3 4 UNITED STATES DISTRICT COURT 5 NORTHERN DISTRICT OF CALIFORNIA 6 KATHLEEN HASKINS, 7 Case No. 13-cv-01834-JST Plaintiff, 8 v. ORDER GRANTING MOTION TO 9 DISMISS SYMANTEC CORPORATION, 10 ECF No. 22 Defendant. 11 12 13 Before the Court is Defendant Symantec Corporation’s (“Symantec”) Motion to Dismiss 14 Plaintiff’s First Amended Complaint (“Motion”). ECF No. 22. The Court has carefully 15 considered the papers filed in support of the motion and finds the matter appropriate for resolution 16 without oral argument. See Civil L.R. 7-1(b). The hearing scheduled for August 29, 2013 is 17 therefore VACATED. United States District United Court District States Northern District of California Northern California of District 18 I. BACKGROUND 19 A. Factual Background 20 The Court accepts the following allegations as true for the purpose of resolving 21 Defendant’s motion to dismiss. Cahill v. Liberty Mutual Ins. Co., 80 F.3d 336, 337–38 (9th Cir. 22 1996). 23 Symantec provides security, storage, and systems management to consumers, small 24 businesses, and large global organizations through its antivirus, data management utility and 25 enterprise software products. First Amended Complaint (“FAC”), ECF No. 17, ¶ 3. In 2006, 26 hackers infiltrated Symantec’s network and stole the source code for the 2006 versions of 27 pcAnywhere, Norton SystemWorks, Norton Antivirus Corporate Edition and Norton Internet 28 Dockets.Justia.com 1 Security (which Plaintiff identifies in the FAC the “Compromised Symantec Products”1). Id. ¶ 18. 2 The stolen Symantec source code includes instructions written in various computer programming 3 languages, and comments made by engineers to explain the design of the software. -

Yes, Virginia, There Really Is a Norton
05_579932 bk01ch01.qxd 2/24/05 10:44 PM Page 9 Chapter 1: Getting to Know Norton Products In This Chapter ߜ Appreciating Norton’s long history in the PC help biz ߜ Figuring out exactly who Norton is ߜ Getting to know Norton products by type ven if you’re brand-spankin’-new to computers, and before you pur- Echased your Norton software, you probably heard or read the name Norton many times. In fact, Norton is one of the relatively few PC-industry names that has been with us since early on in the history of personal com- puters. If you only knew how many companies have gone bust or been bought up by bigger firms over the last two-plus decades, you would be astounded! This chapter introduces you to the various tools that are available under the Norton name (plenty!). Here, I focus in on the type of software, because you have so many different ones to choose from. Just as finding and using the right tool in your household tool chest is important when you’re want- ing to do a specific repair, choosing the right Norton product for the PC protection, repair, or maintenance job you face is important — and in this chapter, I help you do just that. Norton: A Name Long Associated with PC Care IBM’s name is still associated with the original PC-class computer that rolled out in 1981. This is true even though so many other manufacturers have joined theCOPYRIGHTED PC design and rollout industry. MATERIAL Not very long after the debut of the IBM PC, the name IBM was joined by the name Norton for some of the first utilities created to help consumers work with those PCs.