System-On-Chip Integration of Heterogeneous Accelerators for Perceptual Computing
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

The Intro to GPGPU CPU Vs
12/12/11! The Intro to GPGPU . Dr. Chokchai (Box) Leangsuksun, PhD! Louisiana Tech University. Ruston, LA! ! CPU vs. GPU • CPU – Fast caches – Branching adaptability – High performance • GPU – Multiple ALUs – Fast onboard memory – High throughput on parallel tasks • Executes program on each fragment/vertex • CPUs are great for task parallelism • GPUs are great for data parallelism Supercomputing 20082 Education Program 1! 12/12/11! CPU vs. GPU - Hardware • More transistors devoted to data processing CUDA programming guide 3.1 3 CPU vs. GPU – Computation Power CUDA programming guide 3.1! 2! 12/12/11! CPU vs. GPU – Memory Bandwidth CUDA programming guide 3.1! What is GPGPU ? • General Purpose computation using GPU in applications other than 3D graphics – GPU accelerates critical path of application • Data parallel algorithms leverage GPU attributes – Large data arrays, streaming throughput – Fine-grain SIMD parallelism – Low-latency floating point (FP) computation © David Kirk/NVIDIA and Wen-mei W. Hwu, 2007! ECE 498AL, University of Illinois, Urbana-Champaign! 3! 12/12/11! Why is GPGPU? • Large number of cores – – 100-1000 cores in a single card • Low cost – less than $100-$1500 • Green computing – Low power consumption – 135 watts/card – 135 w vs 30000 w (300 watts * 100) • 1 card can perform > 100 desktops 12/14/09!– $750 vs 50000 ($500 * 100) 7 Two major players 4! 12/12/11! Parallel Computing on a GPU • NVIDIA GPU Computing Architecture – Via a HW device interface – In laptops, desktops, workstations, servers • Tesla T10 1070 from 1-4 TFLOPS • AMD/ATI 5970 x2 3200 cores • NVIDIA Tegra is an all-in-one (system-on-a-chip) ATI 4850! processor architecture derived from the ARM family • GPU parallelism is better than Moore’s law, more doubling every year • GPGPU is a GPU that allows user to process both graphics and non-graphics applications. -

System-On-A-Chip (Soc) & ARM Architecture
System-on-a-Chip (SoC) & ARM Architecture EE2222 Computer Interfacing and Microprocessors Partially based on System-on-Chip Design by Hao Zheng 2020 EE2222 1 Overview • A system-on-a-chip (SoC): • a computing system on a single silicon substrate that integrates both hardware and software. • Hardware packages all necessary electronics for a particular application. • which implemented by SW running on HW. • Aim for low power and low cost. • Also more reliable than multi-component systems. 2020 EE2222 2 Driven by semiconductor advances 2020 EE2222 3 Basic SoC Model 2020 EE2222 4 2020 EE2222 5 SoC vs Processors System on a chip Processors on a chip processor multiple, simple, heterogeneous few, complex, homogeneous cache one level, small 2-3 levels, extensive memory embedded, on chip very large, off chip functionality special purpose general purpose interconnect wide, high bandwidth often through cache power, cost both low both high operation largely stand-alone need other chips 2020 EE2222 6 Embedded Systems • 98% processors sold annually are used in embedded applications. 2020 EE2222 7 Embedded Systems: Design Challenges • Power/energy efficient: • mobile & battery powered • Highly reliable: • Extreme environment (e.g. temperature) • Real-time operations: • predictable performance • Highly complex • A modern automobile with 55 electronic control units • Tightly coupled Software & Hardware • Rapid development at low price 2020 EE2222 8 EECS222A: SoC Description and Modeling Lecture 1 Design Complexity Challenge Design• Productivity Complexity -

Comparative Study of Various Systems on Chips Embedded in Mobile Devices
Innovative Systems Design and Engineering www.iiste.org ISSN 2222-1727 (Paper) ISSN 2222-2871 (Online) Vol.4, No.7, 2013 - National Conference on Emerging Trends in Electrical, Instrumentation & Communication Engineering Comparative Study of Various Systems on Chips Embedded in Mobile Devices Deepti Bansal(Assistant Professor) BVCOE, New Delhi Tel N: +919711341624 Email: [email protected] ABSTRACT Systems-on-chips (SoCs) are the latest incarnation of very large scale integration (VLSI) technology. A single integrated circuit can contain over 100 million transistors. Harnessing all this computing power requires designers to move beyond logic design into computer architecture, meet real-time deadlines, ensure low-power operation, and so on. These opportunities and challenges make SoC design an important field of research. So in the paper we will try to focus on the various aspects of SOC and the applications offered by it. Also the different parameters to be checked for functional verification like integration and complexity are described in brief. We will focus mainly on the applications of system on chip in mobile devices and then we will compare various mobile vendors in terms of different parameters like cost, memory, features, weight, and battery life, audio and video applications. A brief discussion on the upcoming technologies in SoC used in smart phones as announced by Intel, Microsoft, Texas etc. is also taken up. Keywords: System on Chip, Core Frame Architecture, Arm Processors, Smartphone. 1. Introduction: What Is SoC? We first need to define system-on-chip (SoC). A SoC is a complex integrated circuit that implements most or all of the functions of a complete electronic system. -
System-On-Chip Design with Virtual Components
past designs can a huge chip be com- pleted within a reasonable time. This FEATURE solution usually entails reusing designs from previous generations of products ARTICLE and often leverages design work done by other groups in the same company. Various forms of intercompany cross licensing and technology sharing Thomas Anderson can provide access to design technol- ogy that may be reused in new ways. Many large companies have estab- lished central organizations to pro- mote design reuse and sharing, and to System-on-Chip Design look for external IP sources. One challenge faced by IP acquisi- tion teams is that many designs aren’t well suited for reuse. Designing with with Virtual Components reuse in mind requires extra time and effort, and often more logic as well— requirements likely to be at odds with the time-to-market goals of a product design team. Therefore, a merchant semiconduc- tor IP industry has arisen to provide designs that were developed specifically for reuse in a wide range of applications. These designs are backed by documen- esign reuse for tation and support similar to that d semiconductor provided by a semiconductor supplier. Here in the Recycling projects has evolved The terms “virtual component” from an interesting con- and “core” commonly denote reusable Age, designing for cept to a requirement. Today’s huge semiconductor IP that is offered for system-on-a-chip (SOC) designs rou- license as a product. The latter term is reuse may sound like tinely require millions of transistors. promoted extensively by the Virtual Silicon geometry continues to shrink Socket Interface (VSI) Alliance, a joint a great idea. -

Lecture Notes
Lecture #4-5: Computer Hardware (Overview and CPUs) CS106E Spring 2018, Young In these lectures, we begin our three-lecture exploration of Computer Hardware. We start by looking at the different types of computer components and how they interact during basic computer operations. Next, we focus specifically on the CPU (Central Processing Unit). We take a look at the Machine Language of the CPU and discover it’s really quite primitive. We explore how Compilers and Interpreters allow us to go from the High-Level Languages we are used to programming to the Low-Level machine language actually used by the CPU. Most modern CPUs are multicore. We take a look at when multicore provides big advantages and when it doesn’t. We also take a short look at Graphics Processing Units (GPUs) and what they might be used for. We end by taking a look at Reduced Instruction Set Computing (RISC) and Complex Instruction Set Computing (CISC). Stanford President John Hennessy won the Turing Award (Computer Science’s equivalent of the Nobel Prize) for his work on RISC computing. Hardware and Software: Hardware refers to the physical components of a computer. Software refers to the programs or instructions that run on the physical computer. - We can entirely change the software on a computer, without changing the hardware and it will transform how the computer works. I can take an Apple MacBook for example, remove the Apple Software and install Microsoft Windows, and I now have a Window’s computer. - In the next two lectures we will focus entirely on Hardware. -

EE Concentration: System-On-A-Chip (Soc)
EE Concentration: System-on-a-Chip (SoC) Requirements: Complete ESE350, ESE370, CIS371, ESE532 Requirement Flow: Impact: The chip at the heart of your smartphone, tablet, or mp3 player (including the Apple A11, A12) is an SoC. The chips that run almost all of your gadgets today are SoCs. These are the current culmination of miniaturization and part count reduction that allows such systems to built inexpensively and from small part counts. These chips democratize innovation, by providing a platform for the deployment of novel ideas without requiring hundreds of millions of dollars to build new custom ICs. Description: Modern computational and control chips contain billions of transistors and run software that has millions of lines of code. They integrate complete systems including multiple, potentially heterogeneous, processing elements, sophisticated memory hierarchies, communications, and rich interfaces for inputs and outputs including sensing and actuations. To design these systems, engineers must understand IC technology, digital circuits, processor and accelerator architectures, networking, and composition and interfacing and be able to manage hardware/software trade-offs. This concentration prepares students both to participate in the design of these SoC architectures and to use SoC architectures as implementation vehicles for novel embedded computing tasks. Sample industries and companies: ● Integrated Circuit Design: ARM, IBM, Intel, Nvidia, Samsung, Qualcomm, Xilinx ● Consumer Electronics: Apple, Samsung, NEST, Hewlett Packard ● Systems: Amazon, CISCO, Google, Facebook, Microsoft ● Automotive and Aerospace: Boeing, Ford, Space-X, Tesla, Waymo ● Your startup Sample Job Titles: ● Hardware Engineer, Chip Designer, Chip Architect, Architect, Verification Engineer, Software Engineering, Embedded Software Engineer, Member of Technical Staff, VP Engineering, CTO Graduate research in: computer systems and architecture . -

Threading SIMD and MIMD in the Multicore Context the Ultrasparc T2
Overview SIMD and MIMD in the Multicore Context Single Instruction Multiple Instruction ● (note: Tute 02 this Weds - handouts) ● Flynn’s Taxonomy Single Data SISD MISD ● multicore architecture concepts Multiple Data SIMD MIMD ● for SIMD, the control unit and processor state (registers) can be shared ■ hardware threading ■ SIMD vs MIMD in the multicore context ● however, SIMD is limited to data parallelism (through multiple ALUs) ■ ● T2: design features for multicore algorithms need a regular structure, e.g. dense linear algebra, graphics ■ SSE2, Altivec, Cell SPE (128-bit registers); e.g. 4×32-bit add ■ system on a chip Rx: x x x x ■ 3 2 1 0 execution: (in-order) pipeline, instruction latency + ■ thread scheduling Ry: y3 y2 y1 y0 ■ caches: associativity, coherence, prefetch = ■ memory system: crossbar, memory controller Rz: z3 z2 z1 z0 (zi = xi + yi) ■ intermission ■ design requires massive effort; requires support from a commodity environment ■ speculation; power savings ■ massive parallelism (e.g. nVidia GPGPU) but memory is still a bottleneck ■ OpenSPARC ● multicore (CMT) is MIMD; hardware threading can be regarded as MIMD ● T2 performance (why the T2 is designed as it is) ■ higher hardware costs also includes larger shared resources (caches, TLBs) ● the Rock processor (slides by Andrew Over; ref: Tremblay, IEEE Micro 2009 ) needed ⇒ less parallelism than for SIMD COMP8320 Lecture 2: Multicore Architecture and the T2 2011 ◭◭◭ • ◮◮◮ × 1 COMP8320 Lecture 2: Multicore Architecture and the T2 2011 ◭◭◭ • ◮◮◮ × 3 Hardware (Multi)threading The UltraSPARC T2: System on a Chip ● recall concurrent execution on a single CPU: switch between threads (or ● OpenSparc Slide Cast Ch 5: p79–81,89 processes) requires the saving (in memory) of thread state (register values) ● aggressively multicore: 8 cores, each with 8-way hardware threading (64 virtual ■ motivation: utilize CPU better when thread stalled for I/O (6300 Lect O1, p9–10) CPUs) ■ what are the costs? do the same for smaller stalls? (e.g. -

Chapter 5: Asics Vs. Plds
Chapter 5: ASICs Vs. PLDs 5.1 Introduction A general definition of the term Application Specific Integrated Circuit (ASIC) is virtually every type of chip that is designed to perform a dedicated task. ASICS, more specifically, are designed by the end user to perform some proprietary application. Semi- custom and full-custom Application Specific Integrated Circuits are very useful in integrating digital, analog, mixed signal or system-on-a-chip (SOC) designs but are very costly and not schedule friendly. Depending on the design application, there are many advantages in using ASICs rather than Field Programmable Gate Arrays (FPGAs) or Complex Programmable Logic devices (CPLDs). Some advantages include higher performance, increased densities and decreased space requirements. Some disadvantages include lacking flexibility for changes and difficulty to test and debug. There are some design applications best suited for ASIC technology and others suited for PLDs. Logic designs done in FPGA occupy more space and have decreased performance and may need to be migrated to an ASIC methodology. The migration process introduces issues such as architectural difference and logic mapping to vendor specified functions. 5.2 ASIC Industry The ASIC industry is very volatile with new companies, products and methodologies emerging daily. In the mid-1980s the prediction was that ASIC designs would be taking over 50% of the electronic design market by 1990. When 1990 came the ASIC market turned out to be approximately 10%. Most of the focus for ASICS is providing a technology capable of handling 100,000 or more gates with very high performance. Most of the new ASIC designs do not require high density and 79 performance. -
AI Chips: What They Are and Why They Matter
APRIL 2020 AI Chips: What They Are and Why They Matter An AI Chips Reference AUTHORS Saif M. Khan Alexander Mann Table of Contents Introduction and Summary 3 The Laws of Chip Innovation 7 Transistor Shrinkage: Moore’s Law 7 Efficiency and Speed Improvements 8 Increasing Transistor Density Unlocks Improved Designs for Efficiency and Speed 9 Transistor Design is Reaching Fundamental Size Limits 10 The Slowing of Moore’s Law and the Decline of General-Purpose Chips 10 The Economies of Scale of General-Purpose Chips 10 Costs are Increasing Faster than the Semiconductor Market 11 The Semiconductor Industry’s Growth Rate is Unlikely to Increase 14 Chip Improvements as Moore’s Law Slows 15 Transistor Improvements Continue, but are Slowing 16 Improved Transistor Density Enables Specialization 18 The AI Chip Zoo 19 AI Chip Types 20 AI Chip Benchmarks 22 The Value of State-of-the-Art AI Chips 23 The Efficiency of State-of-the-Art AI Chips Translates into Cost-Effectiveness 23 Compute-Intensive AI Algorithms are Bottlenecked by Chip Costs and Speed 26 U.S. and Chinese AI Chips and Implications for National Competitiveness 27 Appendix A: Basics of Semiconductors and Chips 31 Appendix B: How AI Chips Work 33 Parallel Computing 33 Low-Precision Computing 34 Memory Optimization 35 Domain-Specific Languages 36 Appendix C: AI Chip Benchmarking Studies 37 Appendix D: Chip Economics Model 39 Chip Transistor Density, Design Costs, and Energy Costs 40 Foundry, Assembly, Test and Packaging Costs 41 Acknowledgments 44 Center for Security and Emerging Technology | 2 Introduction and Summary Artificial intelligence will play an important role in national and international security in the years to come. -

ARM Processor Architecture Embedded Systems with ARM Cortext-M Updated: Monday, February 5, 2018 a Little About ARM – the Company
Chapters 1 and 3 ARM Processor Architecture Embedded Systems with ARM Cortext-M Updated: Monday, February 5, 2018 A Little about ARM – The company • Originally Acorn RISC Machine (ARM) • Later Advanced RISC Machine • Then it became ARM Ltd owned by ARM Holdings (parent company) • In 2016 SoftBank bought ARM for $31 billion • ARM: • Develops the architecture and licenses it to other companies • Other companies design their own products that implement one of those architectures— including systems- on-chips (SoC) and systems-on-modules (SoM) that incorporate memory, interfaces, radios, etc. • It also designs cores that implement this instruction set and licenses these designs to a number of companies that incorporate those core designs into their own products. • ARM Processors • RISC based processors • In 2010 alone, 6.1 billion ARM-based processor, representing 95% of smartphones, 35% of digital televisions and set-top boxes and 10% of mobile computers • over 100 billion ARM processors produced as of 2017 • The most widely used instruction set architecture in terms of quantity produced https://en.wikipedia.org/wiki/ARM_architecture M R https://en.wikipedia.org/wiki/ARM_architecture ARM Family and Architecture CPU ARM FAMILY TREE CORTEX- CORTEX- CORTEX- ARM Cortex Processors • ARM Cortex-A family: • Applications processors • Support OS and high- performance applications • Such as Smartphones, Smart TV • ARM Cortex-R family: • Real-time processors with high performance and high reliability • Support real-time processing and mission-critical control • ARM Cortex-M family: • Microcontroller • Cost-sensitive, support SoC 6 CORTEX- • Cortex-M is a great trade-off between performance, cost, efficiency; used for IoT, various applications. -

Verification Methodology for a Complex System-On-A-Chip
UDC 621.3.049.771.14.001.63 Verification Methodology for a Complex System-on-a-Chip VAkihiro Higashi VKazuhide Tamaki VTakayuki Sasaki (Manuscript received December 1, 1999) Semiconductor technology has progressed to the point where it is now possible to implement system-level functions on a single LSI chip. However, traditional LSI verifi- cation becomes less and less powerful as the scale and complexity increase. In fact, more than half of the time required to develop a System-on-a-Chip (SOC) is used for function verification. A new verification methodology for SOCs should therefore be established. We developed a system-level simulation technology to verify the specification and architecture of an SOC and a logic emulation technology to verify the logic function of an entire SOC. By combining these technologies, we established a powerful verifica- tion methodology for an SOC. We applied the verification methodology to develop a high-definition MPEG2 decoder LSI for a digital TV broadcasting system. The LSI was successfully developed on schedule and worked in the first silicon implementation completely according to the specifications. 1. Introduction because of this difficulty. In the era of the System-on-a-Chip (SOC), we We therefore examined the bugs that occur are now able to integrate the functions needed for during LSI development and identified the follow- consumer products such as digital home electron- ing causes: ic appliances and advanced mobile devices on a • Specification problems (insufficient definition, single LSI chip. An SOC LSI includes complex lack of necessary conditions, and misunder- functions with millions of logic gates. -
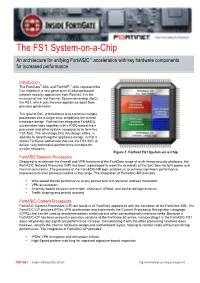
Inside Fortigate: the Fortinet FS1 System-On-A-Chip
The FS1 System-on-a-Chip An architecture for unifying FortiASIC™ acceleration with key hardware components for increased performance Introduction ® ™ The FortiGate -60C and FortiWiFi -60C represent the first models in a new generation of desktop-based network security appliances from Fortinet. It is the inclusion of the first Fortinet System-on-a-chip (SoC), the FS1, which sets the new appliances apart from previous generations. The goal of SoC architectures is to combine multiple processors into a single chip, simplifying the overall hardware design. Fortinet has integrated FortiASIC acceleration logic together with a RISC-based main processor and other system components to form the FS1 SoC. The advantage that this design offers, in addition to simplifying the appliance design, is that it allows FortiGate appliances that use the FS1 SoC to deliver very impressive performance numbers for smaller networks. Figure 1. Fortinet FS1 System-on-a-Chip FortiASIC Network Processors Designed to accelerate the firewall and VPN functions of the FortiGate range of multi-threat security platforms, the FortiASIC Network Processor (NP) has been repackaged to meet the demands of the SoC form factor’s power and thermal constraints. The presence of the FortiASIC-NP logic enables us to achieve significant performance improvements over previous models in the range. The integration of FortiASIC-NP provides: . Wire-speed firewall performance at any packet size with dynamic address translation . VPN acceleration . Anomaly-based intrusion prevention, checksum offload, and packet defragmentation . Traffic shaping and priority queuing FortiASIC Content Processors FortiASIC Content Processors (CP) are found in all FortiGate appliances with the exception of the FortiGate-30B.