Frank Rowlett.Pdf
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
CODEBREAKING Suggested Reading List (Can Also Be Viewed Online at Good Reads)
MARSHALL LEGACY SERIES: CODEBREAKING Suggested Reading List (Can also be viewed online at Good Reads) NON-FICTION • Aldrich, Richard. Intelligence and the War against Japan. Cambridge: Cambridge University Press, 2000. • Allen, Robert. The Cryptogram Challenge: Over 150 Codes to Crack and Ciphers to Break. Philadelphia: Running Press, 2005 • Briggs, Asa. Secret Days Code-breaking in Bletchley Park. Barnsley: Frontline Books, 2011 • Budiansky, Stephen. Battle of Wits: The Complete Story of Codebreaking in World War Two. New York: Free Press, 2000. • Churchhouse, Robert. Codes and Ciphers: Julius Caesar, the Enigma, and the Internet. Cambridge: Cambridge University Press, 2001. • Clark, Ronald W. The Man Who Broke Purple. London: Weidenfeld and Nicholson, 1977. • Drea, Edward J. MacArthur's Ultra: Codebreaking and the War Against Japan, 1942-1945. Kansas: University of Kansas Press, 1992. • Fisher-Alaniz, Karen. Breaking the Code: A Father's Secret, a Daughter's Journey, and the Question That Changed Everything. Naperville, IL: Sourcebooks, 2011. • Friedman, William and Elizebeth Friedman. The Shakespearian Ciphers Examined. Cambridge: Cambridge University Press, 1957. • Gannon, James. Stealing Secrets, Telling Lies: How Spies and Codebreakers Helped Shape the Twentieth century. Washington, D.C.: Potomac Books, 2001. • Garrett, Paul. Making, Breaking Codes: Introduction to Cryptology. London: Pearson, 2000. • Hinsley, F. H. and Alan Stripp. Codebreakers: the inside story of Bletchley Park. Oxford: Oxford University Press, 1993. • Hodges, Andrew. Alan Turing: The Enigma. New York: Walker and Company, 2000. • Kahn, David. Seizing The Enigma: The Race to Break the German U-boat Codes, 1939-1943. New York: Barnes and Noble Books, 2001. • Kahn, David. The Codebreakers: The Comprehensive History of Secret Communication from Ancient Times to the Internet. -

9 Purple 18/2
THE CONCORD REVIEW 223 A VERY PURPLE-XING CODE Michael Cohen Groups cannot work together without communication between them. In wartime, it is critical that correspondence between the groups, or nations in the case of World War II, be concealed from the eyes of the enemy. This necessity leads nations to develop codes to hide their messages’ meanings from unwanted recipients. Among the many codes used in World War II, none has achieved a higher level of fame than Japan’s Purple code, or rather the code that Japan’s Purple machine produced. The breaking of this code helped the Allied forces to defeat their enemies in World War II in the Pacific by providing them with critical information. The code was more intricate than any other coding system invented before modern computers. Using codebreaking strategy from previous war codes, the U.S. was able to crack the Purple code. Unfortunately, the U.S. could not use its newfound knowl- edge to prevent the attack at Pearl Harbor. It took a Herculean feat of American intellect to break Purple. It was dramatically intro- duced to Congress in the Congressional hearing into the Pearl Harbor disaster.1 In the ensuing years, it was discovered that the deciphering of the Purple Code affected the course of the Pacific war in more ways than one. For instance, it turned out that before the Americans had dropped nuclear bombs on Japan, Purple Michael Cohen is a Senior at the Commonwealth School in Boston, Massachusetts, where he wrote this paper for Tom Harsanyi’s United States History course in the 2006/2007 academic year. -

LGBTQ Guam and Hospitality of the Guamanian People
An LGBTQ Guide to Guam Håfa Adai, Welcome! As Lieutenant Governor of Guam and proud member of the LGBTQ community, I am grateful that Guam’s residents have given me the opportunity to help direct the island’s future. Also, Guam has just elected its first female Governor, and now holds the record for the largest women majority in U.S. history. Guam’s diverse political leadership is a direct reflection JOSHUA TENORIO, of the broadening views within our island community. THE HONORABLE LT. GOVERNOR I will advocate for policy that is fair and equal for all and will positively impact LGBTQ rights. I applaud the Guam Visitors Bureau’s efforts in developing the Guam travel industry to better serve LGBTQ travelers and give my full support to their ongoing efforts. We look forward to your visit and providing you with the adventure of a lifetime! Si Yu’os Ma’åse’ 23 Håfa Adai! (Greetings!) Contents The Guam Visitors Bureau (GVB) finds great joy in welcoming LGBTQ travelers to our beautiful island. 02 Welcome As you read this guide, we hope that it inspires you to visit our home and experience the warmth 04 LGBTQ Guam and hospitality of the Guamanian people. 06 LGBTQ Resources 16 Guam strongly supports the LGBTQ community, paving 08 Visiting Guam PILAR LAGUAÑA, the way for equality, celebrating diversity, and promoting With Other LGBTQ PRESIDENT & CEO, inclusivity. The Bureau is a proud member of the Destinations 12 Things to do International Gay and Lesbian Travel Association (IGLTA), GUAM VISITORS 09 Guam + Japan 12 Outdoors BUREAU where we continue our efforts to be a reliable resource for, and to better serve the needs of, all of our visitors. -
Pioneers in U.S. Cryptology Ii
PIONEERS IN U.S. CRYPTOLOGY II This brochure was produced by the Center for Cryptologic History Herbert 0. Yardley 2 Herbert 0. Yardley Herbert 0 . Yardley was born in 1889 in Worthington, Indiana. After working as a railroad telegrapher and spending a year taking an English course at the University of Chicago, he became a code clerk for the Department of State. In June 1917, Yardley received a commission in the Signal Officers Reserve Corps; in July Colonel Ralph Van Deman appointed him chief of the new cryptanalytic unit, MI-8, in the Military Intelligence division. MI-8, or the Cipher Bureau, consisted of Yardley and two clerks. At MI-8's peak in November 1918, Yardley had 18 officers, 24 civilians, and 109 typists. The section had expanded to include secret inks, code and cipher compilation, communications, and shorthand. This was the first formally organized cryptanalytic unit in the history of the U.S. government. When World War I ended, the Army was considering disbanding MI-8. Yardley presented a persuasive argument for retaining it for peacetime use. His plan called for the permanent retention of a code and cipher organization funded jointly by the State and War Departments. He demonstrated that in the past eighteen months MI-8 had read almost 11,000 messages in 579 cryptographic systems. This was in addition to everything that had been examined in connection with postal censorship. On 17 May Acting Secretary of State Frank L. Polk approved the plan, and two days later the Army Chief of Staff, General Peyton C. -
Corp Bro Inside Layout
Message from the Director, NSA The National Security Agency’s rich legacy of cryptologic success serves not only as a reminder of our past triumphs, but also as an inspiration for our future. Harry Truman, the man responsible for signing the legislation that brought our Agency into existence, was once quoted as saying, “There is nothing new in the world except the history you do not know.” Like all truisms, it is only partially accurate. Each generation of Americans must at some point deal with unforeseen problems and issues that transcend the status quo. Most would agree that the challenges faced by NSA in today’s war against terrorism are far different from those of World War II, Vietnam, or Desert Storm. Even so, President Truman was correct in his assertion that there is much to be learned from the past. The history of the National Security Agency has in many respects been based on and characterized by feats of intellectual brilliance. Pioneers like William Friedman, Frank Rowlett, Dr. Louis Tordella, and Agnes Meyer Driscoll, to name but a few, were able to build on past successes and do whatever was necessary to meet the challenges of their time. We should not forget, however, that NSA’s success is due not just to the efforts of the well- known legends of the cryptologic past, but also to the dedicated work of thousands of men and women whose names will never be noted in any history book. History tells us that both genius and hard work are required to ensure success. -
Certain Aspects of "Magic" in the Cryptological Background of the Various Official Investigations Into the Attack on P
REF ID:A485355 OF 'l'.BE V.AltIOUS OFFICIAL INVEmGATIONS mo 'l!BE A'.t'.J!ACK ON PEA.BL MRBOR ··. •· . ' I-.- REF ID:A485355 --;-~·;-:;-.:- ... -~.... , ""'-·I';"~-""",~-·;,'~;~~~-~~.\,-::):t~<.""',. -.~\~=---:~-.,,-1f~': ------== ,,.--.., "t-,-.\;' .,-~,-. Certain As;pects of 1tMsgie 11 in the Ct;r:ttol~eaJ.. De.ck.ground of the V{'J."':touc; Offic!.&.1. Invest1@(1ons into the Atttlck on Pearl Harbor INDEX Section l. Introduction • • • • • • • • • • • • • • • • • • • 2. The Real Essence of the Problem • • • • • • • • • 11 A Ziev Look a.t the Revisionists Allegations of Conspiracy to Keep K:l.mmel and S'bort in the Da:rk • • • • • • • • • • • • • • • • • • • • • 18 4. Was MtlGIC Withheld from Kimmel and Short and, if so, ~ ••••••• ,, •••••••• • • 35 1 The tiWinds Code Message:B ' . ~ . .. 49 The Question of Sabota.g~f! • • • ti ~ • • • • • • • 53 Conclusions ....... ",., ....... 65 8. Epilogtte • • .. • • • • ' • ' It • Ill • • • • • • • • 60 11 11 APPENDIX 1: Pearl H&'bor in Pernpective1 by Dr. Louis Morton, Uni:ted States Na.val Institute Proceedi!!is,, Vo1. 81, No. 4, April 1955; P-.kl. 461'.:468 APPlitWIX 2: !lpea.rl Ra.rhor and the Revlsionists, 11 by Prof'. Robert H. Ferrc:Ll.. The Historian, Vol. XVII, No. 2, SprinS 19551 :Pl~· 215·233 REF ID:A485355 1. nmOD"OCTION More than 15 yea.rs have passed. since the Japanese, with unparalleled good luck, good luck that nov seem:s astoundinS, and vith a degree of skill unanticipated by the United, :3tates, executed their surprise attack on Pearl Harbor during the morning hours of 7 December 1941. It was an attack that constituted a. momentou::; disaster for the United States; it ma.de our Navy's Pacific Pleet, for all practica.l purposes, hors de combat for m.a.ny months. -

The First Americans the 1941 US Codebreaking Mission to Bletchley Park
United States Cryptologic History The First Americans The 1941 US Codebreaking Mission to Bletchley Park Special series | Volume 12 | 2016 Center for Cryptologic History David J. Sherman is Associate Director for Policy and Records at the National Security Agency. A graduate of Duke University, he holds a doctorate in Slavic Studies from Cornell University, where he taught for three years. He also is a graduate of the CAPSTONE General/Flag Officer Course at the National Defense University, the Intelligence Community Senior Leadership Program, and the Alexander S. Pushkin Institute of the Russian Language in Moscow. He has served as Associate Dean for Academic Programs at the National War College and while there taught courses on strategy, inter- national relations, and intelligence. Among his other government assignments include ones as NSA’s representative to the Office of the Secretary of Defense, as Director for Intelligence Programs at the National Security Council, and on the staff of the National Economic Council. This publication presents a historical perspective for informational and educational purposes, is the result of independent research, and does not necessarily reflect a position of NSA/CSS or any other US government entity. This publication is distributed free by the National Security Agency. If you would like additional copies, please email [email protected] or write to: Center for Cryptologic History National Security Agency 9800 Savage Road, Suite 6886 Fort George G. Meade, MD 20755 Cover: (Top) Navy Department building, with Washington Monument in center distance, 1918 or 1919; (bottom) Bletchley Park mansion, headquarters of UK codebreaking, 1939 UNITED STATES CRYPTOLOGIC HISTORY The First Americans The 1941 US Codebreaking Mission to Bletchley Park David Sherman National Security Agency Center for Cryptologic History 2016 Second Printing Contents Foreword ................................................................................ -

Information Theory and Entropy
3 Information Theory and Entropy Solomon Kullback (1907–1994) was born in Brooklyn, New York, USA, and graduated from the City College of New York in 1927, received an M.A. degree in mathematics in 1929, and completed a Ph.D. in mathematics from the George Washington University in 1934. Kully as he was known to all who knew him, had two major careers: one in the Defense Department (1930–1962) and the other in the Department of Statistics at George Washington University (1962–1972). He was chairman of the Statistics Department from 1964–1972. Much of his pro- fessional life was spent in the National Security Agency and most of his work during this time is still classified. Most of his studies on information theory were done during this time. Many of his results up to 1958 were published in his 1959 book, “Information Theory and Statistics.” Additional details on Kullback may be found in Greenhouse (1994) and Anonymous (1997). When we receive something that decreases our uncertainty about the state of the world, it is called information. Information is like “news,” it informs. Informa- tion is not directly related to physical quantities. Information is not material and is not a form of energy, but it can be stored and communicated using material or energy means. It cannot be measured with instruments but can be defined in terms of a probability distribution. Information is a decrease in uncertainty. 52 3. Information Theory and Entropy This textbook is about a relatively new approach to empirical science called “information-theoretic.” The name comes from the fact that the foundation originates in “information theory”; a set of fundamental discoveries made largely during World War II with many important extensions since that time. -

The Magic Flute
OCTOBER 09, 2015 THE FRIDAY | 8:00 PM OCTOBER 11, 2015 MAGIC SUNDAY | 4:00 PM OCTOBER 13, 2015 FLUTE TUESDAY | 7:00 PM FLÂNEUR FOREVER Honolulu Ala Moana Center (808) 947-3789 Royal Hawaiian Center (808) 922-5780 Hermes.com AND WELCOME TO AN EXCITING NEW SEASON OF OPERAS FROM HAWAII OPERA THEATRE. We are thrilled to be opening our 2014) conducts, and Allison Grant As always we are grateful to you, season with one of Mozart’s best- (The Merry Widow, 2004) directs this our audience, for attending our loved operas: The Magic Flute. This new translation of The Magic Flute by performances and for the support colorful production comes to us Jeremy Sams. you give us in so many ways from Arizona Opera, where it was throughout the year. Without your created by Metropolitan Opera This will be another unforgettable help we simply could not continue stage director, Daniel Rigazzi. season for HOT with three to bring the world’s best opera to Inspired by the work of the French sensational operas, including Hawaii each year. surrealist painter, René Magritte, a stunning new production of the production is fi lled with portals– Benjamin Britten’s A Midsummer But now sit back and enjoy Mozart’s doorways and picture frames–that Night’s Dream, directed by Henry The Magic Flute. lead the viewer from reality to Akina, with videography by Adam dreams. With a cast that includes Larsen (Siren Song, 2015) and a MAHALO Antonio Figueroa as Tamino and So spectacular production of Verdi’s Il Young Park as the formidable Queen Trovatore designed by Peter Dean Henry G. -

An Introduction to a Historic Computer Document: Betting on the Future - the 1946 Pendergrass Report Cryptanalysis and the Digital Computer
UNCLASSIFIED An Introduction to a Historic Computer Document: Betting on the Future - The 1946 Pendergrass Report Cryptanalysis and the Digital Computer COLIN BURKE The codebreakers of the American navy's OP-20-G had struggled since the early 1930s to obtain the funds needed to design and build high-speed electronic analytic machines. [11,21 Unfortunately, their mid-1930's project, which was led by Vannevar Bush of MIT, did not produce a truly successful device. The developmental funds and the institutional supports provided by the navy were insufficient for the challenging move into digital electronics. The relatively special-purpose, optical-electronic Comparator that Bush constructed for the navy in 1938 was unreliable. OP-20-G began World War II with only a handful of IBM electromechanical tabulators and the hope that massive funding of electronics research would finally allow the creation of the more powerful Rapid Analytic machines Bush had suggested to the navy's S.C. Hooper and Joseph Wenger in 1936. [211 Hooper and Wenger hoped that such machines, distant cousins of the programmed digital electronic computer, would allow OP-20-G to create and apply advanced mathematical and statistical cryptanalytic techniques. A stable, long-term program to develop the Rapid Machines might have led OP-20-G to be among the very first to conceive of and build a modern electronic computer, but the chance for such a program had been lost in the 1930s. It could not be reborn during the war. The demands created by Pearl Harbor and the Battle of the Atlantic turned OP-20-G away from speculative projects. -

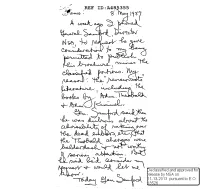
The Legendary William F. Friedman
'\ •' THE LEGENDARY WILLIAM F. FRH:DMAN By L~mbros D. C~llimPhos February 1974 "------- @'pp roved for Release bv NSA on 05-12-2014 Pursuant to E .0. 1352\3 REF ID:A4045961 "To my disciple, colles:igue, end friend, LPmbros Demetrios Cl3llim::>hos- who, hr:iving at an early ?ge become one of the gre?t fl1=1utists of the world, deserted the profession of musician, in favor of another in which he is making noteworthy contributions-- From r:illif'm F. Friedm?.n- - who, having ?t 8n early ege aspired to become noted in the field of biology, deserted the profession of geneticist, in favor of ~nother, upon which he hopes he hes left some impression by his contributions. In short: From deserter to deserter, with affectionate greetings! W.F.F. Washington, 21 November 1958" (Facing pege J-) REF ID:A4045961 ~ THE LEGENDARY WILLIAM F. FRIEDMAN By Lambros D. Callimahos Unclassified PROLOGUE When I joined the U.S. Army to enter the cryptologic service of my adopted country on February 11, 1941, William F. Friedman was already e legendRry figure in my eyes. I had read two efffly papers of his, "L'indice de coincidence et ses a-pplications en cryptographie" end "Application des methodes de la statistioue a la cryptogre~hie, when I was living in Feris in 1934, concertizing as a flute soloist throughout Europe while privately pursuing en active hobby of cryptology, which I felt would be my niche when the time CPme for me to enter the army. (Be sides the U.S. Army, I was also liable for service in the Greek, Egy-ptian, and Turkish armies, P.nd barely missed being in one of the letter.) As a member of the original group of 28 students in the Cryptogr8phic School at Fort Monmouth: N. -

Cryptologic Quarterly, 2019-01
Cryptologic Quarterly NSA’s Friedman Conference Center PLUS: Vint Hill Farms Station • STONEHOUSE of East Africa The Evolution of Signals Security • Mysteries of Linguistics 2019-01 • Vol. 38 Center for Cryptologic History Cryptologic Quarterly Contacts. Please feel free to address questions or comments to Editor, CQ, at [email protected]. Disclaimer. All opinions expressed in Cryptologic PUBLISHER: Center for Cryptologic History Quarterly are those of the authors. Th ey do not neces- CHIEF: John A. Tokar sarily refl ect the offi cial views of the National Security EXECUTIVE EDITOR: Pamela F. Murray Agency/Central Security Service. MANAGING EDITOR: Laura Redcay Copies of Cryptologic Quarterly can be obtained by ASSOCIATE EDITOR: Jennie Reinhardt sending an email to [email protected]. Editorial Policy. Cryptologic Quarterly is the pro- fessional journal for the National Security Agency/ Central Security Service. Its mission is to advance knowledge of all aspects of cryptology by serving as a forum for issues related to cryptologic theory, doc- trine, operations, management, and history. Th e pri- mary audience for Cryptologic Quarterly is NSA/CSS professionals, but CQ is also distributed to personnel in other United States intelligence organizations as well as cleared personnel in other federal agencies and departments. Cryptologic Quarterly is published by the Center for Cryptologic History, NSA/CSS. Th e publication is de- signed as a working aid and is not subject to receipt, control, or accountability. Cover: “Father of American cryptology” William Friedman’s retirement ceremony in the Arlington Hall Post Theater, Arlington, VA, 1955. Lieutenant General Ralph Canine is at left, Solomon Kullback is seated left, Friedman is second from right, and Director of Central Intelligence Allen Dulles is at far right.