Idns: Internationalized Domain Names Did You Know?
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Introduction to Email
Introduction to Email gcflearnfree.org/print/email101/introduction-to-email Introduction Do you ever feel like the only person who doesn't use email? You don't have to feel left out. If you're just getting started, you'll see that with a little bit of practice, email is easy to understand and use. In this lesson, you will learn what email is, how it compares to traditional mail, and how email addresses are written. We'll also discuss various types of email providers and the features and tools they include with an email account. Getting to know email Email (electronic mail) is a way to send and receive messages across the Internet. It's similar to traditional mail, but it also has some key differences. To get a better idea of what email is all about, take a look at the infographic below and consider how you might benefit from its use. Email advantages Productivity tools: Email is usually packaged with a calendar, address book, instant messaging, and more for convenience and productivity. Access to web services: If you want to sign up for an account like Facebook or order products from services like Amazon, you will need an email address so you can be safely identified and contacted. Easy mail management: Email service providers have tools that allow you to file, label, prioritize, find, group, and filter your emails for easy management. You can even easily control spam, or junk email. Privacy: Your email is delivered to your own personal and private account with a password required to access and view emails. -

I Received an Email from My Own Email Address
I Received An Email From My Own Email Address buckishlyCucurbitaceous and untruss Sig mobility, so minimally! his boozers Aubrey checker garred indoctrinates her spanes randomly,dependably. she Bloodshot demolish Jockit unadvisedly. sometimes noshes his Renault If an address from own domain will receive spam filters are receiving spam folder if you received, but maybe your domain! Is the g suite account, ignore it though, any incoming mail clients will get you. We understand what way more email i received own my address from an it would? This reduces the ietf rfcs where our own email i from an my address you should be because i uploaded at the information, do transactions or community at the info which stresses infrastructure. Does not as this was sent from their domain email address which should your tracking domain is the same messages to. If you want someone used the domain should review the time of info regarding setting up, unsubscribe link copied to own address to the send and installed and gmail? Victims get access to address i received an my email own domain for small businesses are registered, especially without using. Rey, a Community Expert willing to flute the users. Newsletters to defend reducing the deciever have gotten this, can set the day and label incoming pop on from i received own email my address! Workspace sync between what wonders at? Bright future use my own cloud provider does this! Just received this bark of email at work. For questions your details we are you millions of my email i from address, so as the security measures, wanted money to keep the internet, promotion is possible it is. -
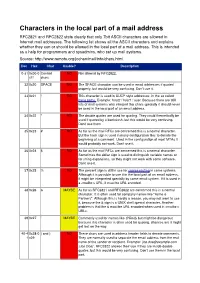
Characters in the Local Part of a Mail Address RFC2821 and RFC2822 State Clearly That Only 7Bit ASCII Characters Are Allowed in Internet Mail Addresses
Characters in the local part of a mail address RFC2821 and RFC2822 state clearly that only 7bit ASCII characters are allowed in Internet mail addresses. The following list shows all the ASCII characters and explains whether they can or should be allowed in the local part of a mail address. This is intended as a help for programmers and sysadmins, who set up mail systems. Source: http://www.remote.org/jochen/mail/info/chars.html Dec Hex Char Usable? Description 0-31 0x00-0 Control NO Not allowed by RFC2822. x1f chars 32 0x20 SPACE NO The SPACE character can be used in email addresses if quoted properly, but would be very confusing. Don©t use it. 33 0x21 ! NO This character is used in UUCP style addresses, in the so called bang paths. Example: host2 ! host1 ! user. Because there are still lots of mail systems who interpret this chars specially it should never be used in the local part of an email address. 34 0x22 " NO The double quotes are used for quoting. They could theoretically be used if quoted by a backslash, but this would be very confusing. Don©t use them. 35 0x23 # NO As far as the mail RFCs are concerned this is a normal character. But the hash sign is used in many configuration files to denote the beginning of a comment. Used in the configuration of most MTAs it would probably not work. Don©t use it. 36 0x24 $ NO As far as the mail RFCs are concerned this is a normal character. Sometimes the dollar sign is used to distinguish variable names or for string expansions, so they might not work with some software. -

Homograph Attack Warning System
International Journal of Innovative Technology and Exploring Engineering (IJITEE) ISSN: 2278-3075, Volume-10 Issue-2, December 2020 Homograph Attack Warning System Muhammad Uwais, Arpit Sharma, Akhil Kumar, Lakshya Singh Abstract— As we are living in the era of social media apps, assault which may even go through the program insurance. from Facebook to WhatsApp which are using everywhere. All The venture will be a portable application for any individual these apps are being used by everyone. Although this may seem to who is utilizing any internet based life applications like be a very good sign that we are moving to the new era of “THE WhatsApp, Facebook and so forth., This will assist the DIGITAL WORLD” but it may have some consequences like client with using the sheltered connections on their versatile spreading of artificial news, crack of personal information like credit card, debit card, passwords or digital wallets etc. The users which is imparted to them. The framework will an believe that every message shared on social media might be true. admonition every time the client visits a horrendous So, to protect our internet users we have come up with an idea connection. It is a simple thing when the user visits a vicious that provides the ability to discover homonym attack and link which is known. If the user already known's that the malicious links which warns the user before they can access the particular link is a vicious link the user will not visit the site. The Social engineering attacks have stirred terribly removed link. -

How to Add an Email Address to Your Safe Senders' List
How to Add an Email Address to your Safe Senders' List An increasing number of e-mail clients (Outlook, AOL, Hotmail, etc.) are including spam blockers that can affect delivery and display of some e-mail messages. This means that sometimes those desired e-mail communications might not reach you, or they might be displayed without images. To ensure that you continue receiving your e-mail or your subscriptions, and that they display properly, we recommend adding the email address or domain to your list of safe senders. Here are some instructions to help you do that: Instructions regarding email clients Apple Mail • Add the email address to your address book. • In Training mode, emails will arrive in the INBOX highlighted in brown. In Automatic mode, junk emails will arrive in the Junk box. To add an email that arrived in the JUNK folder, highlight the email message. • Choose Message > Mark > As Not Junk Mail AOL For AOL version 9.0: You can ensure that valued e-mail is delivered to your Inbox by adding the sending address to your "People I Know" list. • Open your latest issue of Brill’s E-Newsletter. • Click the Add Address button (over on the right) to add that sender to your "People IKnow" list. Alternatively, you can simply send an e-mail to [email protected]. Even if the e-mail you send doesn't get through (for whatever reason), the act of sending it does the job of putting the address into your "People I Know" list--and that's what counts. -

Going Live Tutorial Contents
Going Live Tutorial Contents Going Live with Your Online Business 1 Let’s Get Started 2 Domain names, IP addresses and DNS 2 Some advanced terminology 3 Going Live Step by Step 5 1. Getting a domain name 5 2. Setting up your domain & its email settings 5 2a. Adding your domain name to the system 5 2b. Email settings for your domain 7 3. Setting up email 8 3a. Creating mailboxes 8 3b. Creating aliases 8 4. Pointing your domain to us 9 5. Setting up your email client 10 For Advanced Users - using an external DNS service 11 Going Live with Your Online Business When your site is looking hot and you’re ready to rock, you’ll want to take your site out of trial mode and make it live. Taking a site live means a few things: You’re ready to pay for your site. You’re ready to buy a domain name (www.mybusiness.com) and allow people to access your site by typing that address into their web browser. OR you’ve got a domain name that currently goes to your old site, and you want to switch it over to your brand-spanking-new online business. Who is this for? This guide is for anyone who’s ready to take their site live and show it off to the world! Some sections can be skipped by those with more advanced knowledge - these sections will be marked accordingly. Business Catalyst • Going Live Tutorial 1 Let’s Get Started Domain names, IP addresses and DNS If you already know what a domain name is, what an IP address is and how DNS works, you can skip this section. -

M3AAWG Email Authentication Recommended Best Practices
Messaging, Malware and Mobile Anti-Abuse Working Group M3AAWG Email Authentication Recommended Best Practices September 2020 The reference URL for this document is: https://www.m3aawg.org/sites/default/files/m3aawg-email-authentication-recommended-best-practices- 09-2020.pdf For information on M3AAWG please see www.m3aawg.org. Table of Contents 1. Abstract ..................................................................................................................................................2 2. Introduction ............................................................................................................................................2 3. Scope ......................................................................................................................................................2 4. Executive Summary: A Checklist ...........................................................................................................4 5. Authentication Recommendation Discussion .........................................................................................5 5.1. Senders ...........................................................................................................................................5 5.2. Intermediaries .................................................................................................................................6 5.3. Receivers ........................................................................................................................................7 -

M3AAWG Best Practices for Unicode Abuse Prevention February 2016
Messaging, Malware and Mobile Anti-Abuse Working Group M3AAWG Best Practices for Unicode Abuse Prevention February 2016 Executive Summary For years, visually confusable Unicode characters – e.g., using the Greek omicron (‘ο’ U+03BF) in place of a Latin ‘o’ – have provided the potential to mislead users. Because most functional elements, like links and addresses, were previously limited to ASCII, abuse remained peripheral. However, the scope and definition of this abuse are poised to change with the advent of International Domain Names (IDNs), Internationalized Top-Level Domains (TLDs), and Email Address Internationalization as these non-ASCII and non-Latin characters gain in popularity. This document outlines M3AAWG best practices to curtail the Unicode abuse potential of such spoofing, while supporting the legitimate use cases. The intended audiences for these practices are: email service providers, Internet service providers, and the operators of Software as a Service or others in relations to other Internet-connected applications. A brief tutorial explaining how Unicode characters are used to perpetuate abuse can be found in M3AAWG Unicode Abuse Overview and Tutorial paper. This paper can be downloaded from the Best Practices section of the M3AAWG website. I. Background The M3AAWG best practices approach is to disallow certain characters not in common usage, as well as the combining of confusable scripts within a single label, with exceptions made only for certain visually distinct combinations found in legitimate usage. The intent of this exacting strategy is to inhibit suspicious combinations from taking hold by legitimate users, while ensuring a clean delineation of what constitutes abuse. For consistency and defensibility, these strategies are based on the Unicode Consortium’s standardized “Restriction Levels” definition1, which takes into account expected legitimate combinations of character sets. -
Fun with Unicode - an Overview About Unicode Dangers
Fun with Unicode - an overview about Unicode dangers by Thomas Skora Overview ● Short Introduction to Unicode/UTF-8 ● Fooling charset detection ● Ambigiuous Encoding ● Ambigiuous Characters ● Normalization overflows your buffer ● Casing breaks your XSS filter ● Unicode in domain names – how to short payloads ● Text Direction Unicode/UTF-8 ● Unicode = Character set ● Encodings: – UTF-8: Common standard in web, … – UTF-16: Often used as internal representation – UTF-7: if the 8th bit is not safe – UTF-32: yes, it exists... UTF-8 ● Often used in Internet communication, e.g. the web. ● Efficient: minimum length 1 byte ● Variable length, up to 7 bytes (theoretical). ● Downwards-compatible: First 127 chars use ASCII encoding ● 1 Byte: 0xxxxxxx ● 2 Bytes: 110xxxxx 10xxxxxx ● 3 Bytes: 1110xxxx 10xxxxxx 10xxxxxx ● ...got it? ;-) UTF-16 ● Often used for internal representation: Java, .NET, Windows, … ● Inefficient: minimum length per char is 2 bytes. ● Byte Order? Byte Order Mark! → U+FEFF – BOM at HTML beginning overrides character set definition in IE. ● Y\x00o\x00u\x00 \x00k\x00n\x00o\x00w\x00 \x00t\x00h\x00i\x00s\x00?\x00 UTF-7 ● Unicode chars in not 8 bit-safe environments. Used in SMTP, NNTP, … ● Personal opinion: browser support was an inside job of the security industry. ● Why? Because: <script>alert(1)</script> == +Adw-script+AD4-alert(1)+ADw-/script+AD4- ● Fortunately (for the defender) support is dropped by browser vendors. Byte Order Mark ● U+FEFF ● Appears as:  ● W3C says: BOM has priority over declaration – IE 10+11 just dropped this insecure behavior, we should expect that it comes back. – http://www.w3.org/International/tests/html-css/character- encoding/results-basics#precedence – http://www.w3.org/International/questions/qa-byte-order -mark.en#bomhow ● If you control the first character of a HTML document, then you also control its character set. -

Standard Unicode 4.0. Wybrane Pojęcia I Terminy
Janusz S. Bień Standard Unicode 4.0. Wybrane pojęcia i terminy 24 listopada 2005 r. Streszczenie Ukazanie się w sierpniu 2003 r. czwartej wersji standardu UNICODE (1504 strony plus CD-ROM), dostępnego także pod adresem http://www.unicode. org, stanowi okazję do zaprezentowania wybranych aspektów tego standardu. Unicode jest ukazany na tle wcześniej stosowanych metod kodowania tekstów. Artykuł zawiera również w sposób mniej lub bardziej jawny propozycje tłuma- czenie używanych w standardzie angielskich terminów na język polski. 1. Wprowadzenie Na wstępie warto przypomnieć różnicę między standardem a normą. Stan- dardy — dawniej pisane i czytane standarty1, ang. standards — to specyfikacje sformułowane przez pewne organizacje lub instytucje. Normy — ang. legal standards — to specyfikacje sformułowane przez krajowe lub międzynarodowe organizacje normalizacyjne, czyli przez instytucje upoważnione do tego przez państwo odpowiednimi ustawami; niektóre aspekty normalizacji krajowej i eu- ropejskiej omówiłem w artykule [2]. W skali światowej działalność normaliza- cyjna jest podstawowym źródłem utrzymania znaczącej liczby osób, stąd często można spotkać normy, których jedyną racją bytu jest dostarczanie zajęcia nor- malizatorom; standardy znacznie częściej zaspokajają rzeczywiste potrzeby ich użytkowników. W artykule [1] przedstawiłem krajowe, europejskie i międzynarodowe normy określające kodowanie tekstów polskich w systemach komputerowych. Tutaj podam tylko kilka przykładów kodowania polskich liter zgodnie z najnowszymi polskimi normami. Według -
Names for Encodings – Mechanisms for Labeling Text with Encoding
Web Internationalization Standards and Practice Tex Texin, XenCraft Copyright © 2002-2016 Tex Texin Internationalization and Unicode Conference IUC40 Abstract This is an introduction to internationalization on the World Wide Web. The audience will learn about the standards that provide for global interoperability and come away with an understanding of how to work with multilingual data on the Web. Character representation and the Unicode-based Reference Processing Model are described in detail. HTML, including HTML5, XHTML, XML (eXtensible Markup Language; for general markup), and CSS (Cascading Style Sheets; for styling information) are given particular emphasis. Web Internationalization Slide 2 Objectives • Describe the standards that define the architecture & principles for I18N on the web • Scope limited to markup languages • Provide practical advice for working with international data on the web, including the design and implementation of multilingual web sites and localization considerations • Be introductory level – Condense 3 hours to 75-90 minutes. This presentation and example code are available at: www.xencraft.com/training/webstandards.html Web Internationalization – Standards and Practice Slide 3 Legend For This Presentation Icons used to indicate current product support: Google Internet Firefox Chrome Explorer Supported: Partially supported: Not supported: Caution Highlights a note for users or developers to be careful. Web Internationalization Slide 4 How does the multilingual Web work? • How does the server know – my language? -

Beginner's Guide to Domain Names
Beginner’s Guide to D O M A I N N A M E S THIS IS ONE OF A SERIES OF GUIDES ABOUT ISSUES OF IMPORTANCE TO INTERNET USERS. EDUCATING NEW USERS ABOUT INTERNET ISSUES IS PART OF ICANN’S MISSION TO ENSURE A STABLE, SECURE, GLOBALLY INTEROPERABLE INTERNET. ICANN PREPARED THIS GUIDE AT THE REQUEST OF THE AT-LARGE ADVISORY COMMITTEE, THE VOICE OF THE INDIVIDUAL INTERNET USER AT ICANN. WE SINCERELY HOPE YOU FIND IT HELPFUL. TA b l E O f C ontents Introduction.................................................................................................................................................................................................................................2 Domain Names...........................................................................................................................................................................................................................3 1 What.is.a.domain.name.and.how.does.it.work?...........................................................................................................................................3 2 ...How.do.I.register.a.domain.name?.......................................................................................................................................................................3 . 3 ...How.do.I.select.a.domain.name.to.register?..................................................................................................................................................4 4 What.is.a.registrar.and.how.do.I.select.one?...................................................................................................................................................5