Annual Report
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
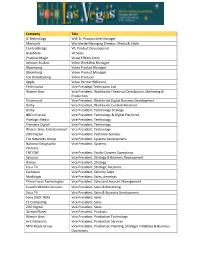
Company Title G-Technology WW Sr. Product Line Manager Microsoft
Company Title G-Technology WW Sr. Product Line Manager Microsoft Worldwide Managing Director, Media & Cable Contentbridge VP, Product Development GrayMeta VP Sales Practical Magic Visual Effects Artist Amazon Studios Video Workflow Manager Bloomberg Video Product Manager Bloomberg Video Product Manager Fox Broadcasting Video Producer Apple Video Partner Relations Technicolor Vice Presidept Technicolor Ltd Warner Bros. Vice President, Worldwide Theatrical Distribution, Marketing & Production Paramount Vice President, Worldwide Digital Business Development Dolby Vice President, Worldwide Content Relations Dolby Vice President, Technology Strategy NBCUniversal Vice President, Technology & Digital Platforms Pixelogic Media Vice President, Technology Premiere Digital Vice President, Technology Warner Bros. Entertainment Vice President, Technology ZOO Digital Vice President, Technical Services Fox Networks Group Vice President, Systems Development National Geographic Vice President, Systems Partners TNT/TBS Vice President, Studio Content Operations Synovos Vice President, Strategy & Business Development Disney Vice President, Strategy You.i TV Vice President, Strategic Accounts Cartesian Vice President, Security Sales MarkLogic Vice President, Sales, Americas Prime Focus Technologies Vice President, Sales and Account Management Crawford Media Services Vice President, Sales & Marketing You.i TV Vice President, Sales & Business Development Sony DADC NMS Vice President, Sales T2 Computing Vice President, Sales ZOO Digital Vice President, Sales -

Research on Integration of Openid Authentication Within the Gravityzoo
Research on OpenID and its integration within the GravityZoo framework Jarno van de Moosdijk [email protected] January 2008 1 Research on implementation of OpenID within GravityZoo Abstract This report covers the research on the working of OpenID and its integration into the GravityZoo framework. The GravityZoo frame- work can be used to deliver applications to a wide variety of devices. Currently, it is only possible to log in with a username and password combination. OpenID authentication eliminates the need for separate username/password combinations bound to each service. One identi- fier can be used to log in to multiple OpenID enabled services across different providers. The objective of this document is to give an in depth view on the OpenID login procedure. It covers the usability of the most popular OpenID Providers on mobile devices. None of these providers have custom pages for mobile users, which makes them less usable on mobile devices. Next to this, I have looked in to the require- ments for integrating OpenID authentication within the GravityZoo framework. c 2009 Jarno van de Moosdijk <[email protected]> Some rights reserved: This document is licensed under the Creative Com- mons Attribution 3.0 Netherlands license. You are free to use and share this document under the condition that you properly attribute the origi- nal authors. Please see the following address for the full licence conditions: http://creativecommons.org/licenses/by/3.0/nl/deed.en 2 Research on implementation of OpenID within GravityZoo Contents 1 Introduction5 1.1 Research Focus..........................5 1.2 Structure of this report.....................6 2 The GravityZoo Framework7 3 OpenID overview9 3.1 Why choose for OpenID?....................9 3.2 Basic terminology........................ -

Trinity Broadcasting Network LPN Spectrum LLC 2442 Michelle Drive 6200 Stoneridge Mall Rd, Suite 300 Tustin, CA 92780 Pleasanton, CA 94588
Trinity Broadcasting Network LPN Spectrum LLC 2442 Michelle Drive 6200 Stoneridge Mall Rd, Suite 300 Tustin, CA 92780 Pleasanton, CA 94588 May 16, 2019 VIA ELECTRONIC FILING Ms. Marlene H. Dortch Secretary Federal Communications Commission 445 Twelfth Street, SW Washington, D.C. 20554 Re: Notice of Ex Parte Communication, Expanding Flexible Use of the 3.7 GHz to 4.2 GHz Band, GN Docket No. 18-122 Dear Ms. Dortch: Trinity Broadcasting Network (“TBN”) and LPN Spectrum LLC (“LPN”) jointly file these ex parte comments in the above-captioned proceeding in support of the Commission’s efforts to repurpose part of the C-band for 5G terrestrial use. The next generation of wireless technology promises to be a significant driver of economic growth and opportunity in a variety of industrial sectors and will change nearly every aspect of our daily lives. Repurposing part of the C-band for wireless broadband services while balancing the need to support incumbent operations is key to capturing the enormous value that 5G will bring to American businesses and consumers alike. This proceeding will help position the United States as the global leader in the race to 5G. With initial aspirations to “serve[] the interests of all stakeholders” in the C-band, Intel and Intelsat began this proceeding on the right track.1 That initial momentum has been slowed by disagreements among stakeholders, causing the proceeding to effectively stall. This is due to a basic failure of the C-Band Alliance (“CBA”) to recognize that other stakeholders have legitimate interests in what is really a “shared use” band and that any viable solution for repurposing part of the C-band must facilitate significant spectrum clearance. -

MARCH 2014 NY.Pmd
PAGE 1 MARCH 2014-NEWABLE NEWSPAPER YORK PAGE VOLUME 19 NUMBER 10 MARCH 2014 AWARD-WINNING New York THE NEWSPAPER POSITIVELY FOR, BY & ABOUT THE DISABLED READY IN THE BRONX IN THIS ISSUE Education, Kids Play and Improve Skills Schools, Camps And Recreation PAGES 7, 8, 9 CRPD 141 Countries Ratify But No U.S. Movement PAGE 2 Obama Includes PWD Minimum Wage Raised By Executive Order PAGE 3 EEOC Releases Data 2013 Highest $$ Recovery In Agency History PAGE 5 Snow, Rain, Slush Who Is Responsible For Clean-Up? PAGE 5 MTA Cuts Ribbon Dyckman #1 Station Accessible At Last PAGE 10 Sports Paralympics, Skiing And Snowboarding PAGE 11 About 100 preschoolers in the Readiness Program hockey, winter bowling, luge, ice-skating. They also VISIT at New York Institute for Special Education (NYISE), had snowball fights with crumbled paper. ABLE'S in the Bronx, recently participated in their annual Win- All activities were designed to improve gross mo- WEBSITE ter Olympics. Developmentally-delayed three- to five- tor skills such as coordination, balance, strength year-olds played Olympics-inspired games such as and agility. WWW. ABLENEWS.COM N.Y. ABLE NEWSPAPER P.O. BOX 395, OLD BETHPAGE, NY 11804 TO THE 516 939-2253 LETTERS EDITOR FAX 516 939-0540 www.ablenews.com Hi Everyone, ing home) and might have noth- siblings. Any questions please Thanks to all who have signed ing better to do, could you all contact me. our petition to save home care please mass-mail our petition Thank you. workers and the people with dis- with old-fashioned email and Philip Bennett abilities we assist. -

A Security Analysis of Openid
A Security Analysis of OpenID Bart van Delft1 and Martijn Oostdijk2 1 Comp.Sci.Dept., Radboud Univ., P.O.Box 9010, 6500 GL, Nijmegen, The Netherlands, [email protected] 2 Novay, P.O.Box 589, 7500 AN, Enschede, The Netherlands, [email protected] Abstract. OpenID, a standard for Web single sign-on, has been gaining popularity both with Identity Providers, Relying Parties, and users. This paper collects the security issues in OpenID found by others, occasionally extended by the authors, and presents them in a uniform way. It attempts to combine the shattered knowledge into a clear overview. The aim of this paper is to raise awareness about security issues surrounding OpenID and similar standards and help shape opinions on what (not) to expect from OpenID when deployed in a not-so-friendly context. 1 Introduction In 2005 Brad Fitzpatrick developed the first version of the OpenID protocol. Initially intended to save users the effort of going through a registration process on multiple social (blogging) websites they wanted to join, the protocol has by now become a very popular single sign-on method on a large number of high profile websites (JanRain claims over 30,000 OpenID enabled websites in January 2009 [5]). In fact, given an average user on the Internet, chances are high that he or she already owns a so-called `OpenID enabled login', since Google, Yahoo, Facebook, AOL and Windows Live accounts all support OpenID. The latest version of the OpenID Authentication specification, version 2.0 [20], was released in December 20073. The new version mainly enabled more flexibility and support for the possible identities to use, improved some security aspects and enabled the usage of extensions for attribute exchange. -

Washington Residential Channel Guide
Fiber TV Washington Residential Channel Lineup Effective Date August 2021 Welcome to Fiber TV Here’s your complete list of available channels to help you decide what to watch. On-Demand With Fiber TV, every night is a movie night. Choose from thousands of On Demand movies, TV shows, concerts and sports. TV On-The-Go For TV on-the-go, check out apps available from our entertainment partners featuring live and on-demand content. Browse the list of participating entertainment partners here: https://ziplyfiber.com/resources/tveverywhere. Simply sign into an entertainment partner’s app with your Ziply Fiber username and password. Have questions? We have answers … When you have a question or need help with your Fiber TV Service, simply visit Help on your TV, or visit www.ziplyfiber.com/helpcenter for a complete library of How Tos. 2 Quick Reference Channels are grouped by programming categories in the following ranges: Local Channels 1–49 SD, 501–549 HD Local Plus Channels 460–499 SD Local Public/Education/Government (varies by location) 15–47 SD Entertainment 50–69 SD, 550–569 HD Sports 70–99 & 300–319 SD, 570–599 HD News 100–119 SD, 600–619 HD Info & Education 120–139 SD, 620–639 HD Home & Leisure/Marketplace 140–179 SD, 640–679 HD Pop Culture 180–199 SD, 680–699 HD Music 210–229 SD, 710–729 HD Movies/Family 230–249 SD, 730–749 HD Kids 250–269 SD, 780–789 HD People & Culture 270–279 SD Religion 280–299 SD Premium Movies 340–449 SD, 840–949 HD Pay Per View/Subscription Sports 1000–1499 Spanish Language 1500-1749 International 1750-1799 Digital Music** 1800–1900 3 Fiber TV Select Kong TV Bounce 466 Included with all Fiber TV KSTW Grit 481 packages. -

Instructor's Edge Fall 2012
+ Fall 2012 VOLUME 35 NUMBER 1 Theo Meiner, right, Teacher. Coach. and his son, Aidan, and daughter, Guide. Alexandra. Theo died Remembering Theo Meiners in an accident September 20 while By Emma Franzeim attending the International Snow On September 20, we lost an excep- Science Workshop in Anchorage, Alaska. tional man and member of our commu- His presence will be nity when Theo Meiners fell to his death missed. in an accident in Anchorage, Alaska. Although Theo’s career as a ski In the short time since his death, easily describe him as someone whose instructor began in Colorado, we have there have been many articles pub- expectations of the people around him claimed him as one of our own in Jack- lished about the remarkable legacy that were only exceeded by his expectations son Hole since 1978. In Jackson, Theo Theo Meiners leaves behind. When you of himself. But it was more than that – it worked as an instructor, backcountry read of him in Powder Magazine, Outer was sincere belief. When Theo looked guide, and DECL. However, although Local, and JH Underground, you will you in the eye and said “You’ve got he was an integral member of our com- learn of a man of many accomplish- this.” whether you were looking into munity, it was understood by all of us ments who filled his life with excep- Corbet’s, or listening to the pulse of that Theo’s heart belonged to Alaska. tional people and experiences. helicopter pull away behind you - He had spent time in Alaska as a Although these articles do a tremen- whatever it was that you faced – when child, but it wasn’t until the World dous job of detailing Theo’s biography, he looked you in the eye and said those Extreme Skiing Competitions, when there is something they cannot fully con- words, you knew not only that he Doug Coombs made tracks on the land- vey about the hole he leaves behind. -

Washington Residential Channel Lineup Ziply Fiber TV – Ziplyfiber.Com
Fiber TV Washington Residential Channel Lineup Effective Date December 2020 Welcome to Fiber TV Here’s your complete list of available channels to help you decide what to watch. On-Demand With Fiber TV, every night is a movie night. Choose from thousands of On Demand movies, TV shows, concerts and sports. TV On-The-Go For TV on-the-go, check out apps available from our entertainment partners featuring live and on-demand content. Browse the list of participating entertainment partners here: https://ziplyfiber.com/resources/tveverywhere. Simply sign into an entertainment partner’s app with your Ziply Fiber username and password. Have questions? We have answers … When you have a question or need help with your Fiber TV Service, simply visit Help on your TV, or visit www.ziplyfiber.com/helpcenter for a complete library of How Tos. 2 Quick Reference Channels are grouped by programming categories in the following ranges: Local Channels 1–49 SD, 501–549 HD Local Plus Channels 460–499 SD Local Public/Education/Government (varies by location) 15–47 SD Entertainment 50–69 SD, 550–569 HD Sports 70–99 & 300–319 SD, 570–599 HD News 100–119 SD, 600–619 HD Info & Education 120–139 SD, 620–639 HD Home & Leisure/Marketplace 140–179 SD, 640–679 HD Pop Culture 180–199 SD, 680–699 HD Music 210–229 SD, 710–729 HD Movies/Family 230–249 SD, 730–749 HD Kids 250–269 SD, 780–789 HD People & Culture 270–279 SD Religion 280–299 SD Premium Movies 340–449 SD, 840–949 HD Pay Per View/Subscription Sports 1000–1499 Spanish Language 1500-1749 International 1750-1799 Digital Music** 1800–1900 3 Fiber TV Select Kong TV Bounce 466 Included with all Fiber TV KSTW Grit 481 packages. -

For Immediate Release
For Immediate Release DEG: The Digital Entertainment Group Announces 12 New Member Companies Nine of 12 New Members Set to Join the D2C Alliance LOS ANGELES (March 29, 2021) | DEG: The Digital Entertainment Group is pleased to welcome 12 new companies to the organization. DEG’s newest member companies are AMC Networks, Azure, Breaker, Cinedigm, Movies Anywhere, Pixelogic, Respeecher, ScreenHits TV, SmithGeiger, Starz, Verizon Business Group and Vuulr. AMC Networks, Azure, Cinedigm, Movies Anywhere, ScreenHits TV, SmithGeiger, Starz, Verizon Business Group and Vuulr will also join DEG’s D2C Alliance Council. The D2C Alliance, a working community within DEG, represents the global direct-to-consumer media industry and supports its members to help create a robust marketplace to lead the new era of content consumption. “This diverse slate of companies reflects the expanding home entertainment landscape,” said Amy Jo Smith, President and CEO, DEG. “We welcome these 12 new members and are delighted to collaborate on their goals of delivering consumers engaging content, transformative technologies, and the highest quality entertainment experience.” AMC NETWORKS is dedicated to creating and distributing bold and inventive stories. AMC Networks owns and operates several of the most popular brands in television and film including AMC, BBC America, IFC, SundanceTV, WE tv, IFC Films, Sundance Now, Shudder, AMC Studios, and AMC Networks International. AMC Studios, the company’s in-house studio, production, and distribution operation, is behind award-winning owned series and franchises including The Walking Dead, the highest-rated series in cable history. AZURE is Microsoft’s cloud platform with more than 200 products and cloud services designed to help bring new solutions to life—to solve today’s challenges and create the future. -

Norwegian Barneblad: Flowers That Bloom in Spring American Story on Page 23
the Inside this issue: NORWEGIAN Barneblad: Flowers that bloom in Spring american story on page 23 Volume 129, #7 • April 6, 2018 Est. May 17, 1889 • Formerly Norwegian American Weekly, Western Viking & Nordisk Tidende $4 USD A student’s take on Halden Prison Drexel University students travel to Norway to compare its prisons to those in America WHAT’S INSIDE? MICHAEL KLEINER « Blir vi rørt over våren fordi Nyheter / News 2-3 den minner oss om vår egen Business 4-5 The Norwegian American engstelige og karrige, men tross Opinion 6-7 Our ideas of prisons mostly come through TV and years they discussed how to collaborate. alt naive og rørende ungdom? » Sports 8-9 movies. After moving to Drexel in 2014, Hyatt applied – Sigurd Hoel Research & Science 10 The loud clang of the iron bar doors closing. The for an Intensive Course Abroad (ICA) program to take Arts & Entertainment 11 rows of cells on each side. Guards with rings of keys students to Norway to compare American and Norwe- and billy clubs walking menacingly down the hall. gian prisons and attitudes about criminal justice. He Taste of Norway 12-13 Watching eyes during work routines. A dark cell with took five students in December 2016 and 12 in 2017. Norway near you 14-15 a dim light bulb, hard bed, sink, and toilet. A warden “There are two general goals,” said Dr. Hyatt. “The Travel 16-17 charged with keeping prisoners in line. first is practical: understanding the nuts and bolts of Norwegian Heritage 18-19 Does this work to rehabilitate inmates? Do inmates different corrections. -

Opinnäytetyön Mallipohja
Integrating external authentication service in Viope Solutions Oy’s web platform Malla Pradhananga, Rabi Raj 2015 Leppävaara Laurea University of Applied Sciences Laurea Leppävaara Integrating external authentication service in Viope So- lutions Oy’s web platform Rabi Raj Malla Pradhananga Degree Program in Business Information Technology Bachelor’s Thesis April, 2015 Laurea University of Applied Sciences Abstract Laurea Leppävaara Degree Program in Business Information Technology Rabi Raj Malla Pradhananga Integrating external authentication service in Viope Solutions Oy’s web platform Year 2015 Pages 53 In today’s world, surfing the internet and using various web services has become common- place. Most of the web services require users to create an account in order to use their ser- vices. Studies show that an average internet user has at least 25 different web accounts. This means the user has 25 different set of username and password combinations to remember in order to access those accounts. This could lead to the problems like forgetting username or password or both and password mismatch. External authentication service, EAS, solve this problem at certain extent by letting users to use their existing set of username and password for more than one web accounts. This thesis work has aimed to integrate EAS in the case company, Viope Solutions Oy’s web platform. There are different types of EAS providers available from social networking sites to payment solution services. It was essential to choose the most suitable EAS provider with which Viope’s potential users already have account and they feel comfortable using it. Differ- ent existing researches and survey reports were analyzed and Facebook was chosen as the most suitable EAS provider. -

Q1 2018 Earnings Call Transcript
Client Id: 77 THOMSON REUTERS STREETEVENTS EDITED TRANSCRIPT DOX - Q1 2018 Amdocs Ltd Earnings Call EVENT DATE/TIME: JANUARY 30, 2018 / 10:00PM GMT OVERVIEW: Co. reported 1Q18 revenue of $978m, diluted GAAP EPS of $0.80 and non-GAAP dluted EPS of $1.06. Expects FY18 reported revenue growth to be roughly 0-4% and diluted non-GAAP EPS growth to be 4-8%, also expects 2Q18 revenue to be $960-1,000m and diluted non-GAAP EPS to be $0.91-0.97. THOMSON REUTERS STREETEVENTS | www.streetevents.com | Contact Us ©2018 Thomson Reuters. All rights reserved. Republication or redistribution of Thomson Reuters content, including by framing or similar means, is prohibited without the prior written consent of Thomson Reuters. 'Thomson Reuters' and the Thomson Reuters logo are registered trademarks of Thomson Reuters and its affiliated companies. Client Id: 77 JANUARY 30, 2018 / 10:00PM, DOX - Q1 2018 Amdocs Ltd Earnings Call CORPORATE PARTICIPANTS Eli Gelman Amdocs Limited - Director Matthew E. Smith Amdocs Limited - Secretary Tamar Rapaport-Dagim Amdocs Limited - CFO & Senior VP of Amdocs Management Ltd CONFERENCE CALL PARTICIPANTS Ashwin Vassant Shirvaikar Citigroup Inc, Research Division - Director and U.S. Computer and Business Services Analyst Jackson Edmund Ader JP Morgan Chase & Co, Research Division - Analyst Matthew David Van Vliet Stifel, Nicolaus & Company, Incorporated, Research Division - Associate Ramsey Clark El-Assal Jefferies LLC, Research Division - Equity Analyst Shaul Eyal Oppenheimer & Co. Inc., Research Division - MD and Senior Analyst William Verity Power Robert W. Baird & Co. Incorporated, Research Division - Senior Research Analyst PRESENTATION Operator Good day, ladies and gentlemen, and welcome to the First Quarter 2018 Amdocs Earnings Conference Call.