A Survey on Botnets: Incentives, Evolution, Detection and Current Trends
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

Post-Mortem of a Zombie: Conficker Cleanup After Six Years Hadi Asghari, Michael Ciere, and Michel J.G
Post-Mortem of a Zombie: Conficker Cleanup After Six Years Hadi Asghari, Michael Ciere, and Michel J.G. van Eeten, Delft University of Technology https://www.usenix.org/conference/usenixsecurity15/technical-sessions/presentation/asghari This paper is included in the Proceedings of the 24th USENIX Security Symposium August 12–14, 2015 • Washington, D.C. ISBN 978-1-939133-11-3 Open access to the Proceedings of the 24th USENIX Security Symposium is sponsored by USENIX Post-Mortem of a Zombie: Conficker Cleanup After Six Years Hadi Asghari, Michael Ciere and Michel J.G. van Eeten Delft University of Technology Abstract more sophisticated C&C mechanisms that are increas- ingly resilient against takeover attempts [30]. Research on botnet mitigation has focused predomi- In pale contrast to this wealth of work stands the lim- nantly on methods to technically disrupt the command- ited research into the other side of botnet mitigation: and-control infrastructure. Much less is known about the cleanup of the infected machines of end users. Af- effectiveness of large-scale efforts to clean up infected ter a botnet is successfully sinkholed, the bots or zom- machines. We analyze longitudinal data from the sink- bies basically remain waiting for the attackers to find hole of Conficker, one the largest botnets ever seen, to as- a way to reconnect to them, update their binaries and sess the impact of what has been emerging as a best prac- move the machines out of the sinkhole. This happens tice: national anti-botnet initiatives that support large- with some regularity. The recent sinkholing attempt of scale cleanup of end user machines. -

Security Now! #664 - 05-22-18 Spectreng Revealed
Security Now! #664 - 05-22-18 SpectreNG Revealed This week on Security Now! This week we examine the recent flaws discovered in the secure Signal messaging app for desktops, the rise in DNS router hijacking, another seriously flawed consumer router family, Microsoft Spectre patches for Win10's April 2018 feature update, the threat of voice assistant spoofing attacks, the evolving security of HTTP, still more new trouble with GPON routers, Facebook's Android app mistake, BMW's 14 security flaws and some fun miscellany. Then we examine the news of the next-generation of Spectre processor speculation flaws and what they mean for us. Our Picture of the Week Security News Update your Signal Desktop Apps for Windows & Linux A few weeks ago, Argentinian security researchers discovered a severe vulnerability in the Signal messaging app for Windows and Linux desktops that allows remote attackers to execute malicious code on recipient systems simply by sending a message—without requiring any user interaction. The vulnerability was accidentally discovered while researchers–amond them Juliano Rizzo–were chatting on Signal messenger and one of them shared a link of a vulnerable site with an XSS payload in its URL. However, the XSS payload unexpectedly got executed on the Signal desktop app!! (Juliano Rizzo was on the beach when the BEAST and CRIME attacks occurred to him.) After analyzing the scope of this issue by testing multiple XSS payloads, they found that the vulnerability resides in the function responsible for handling shared links, allowing attackers to inject user-defined HTML/JavaScript code via iFrame, image, video and audio tags. -

Internet of Things Botnet Detection Approaches: Analysis and Recommendations for Future Research
applied sciences Systematic Review Internet of Things Botnet Detection Approaches: Analysis and Recommendations for Future Research Majda Wazzan 1,*, Daniyal Algazzawi 2 , Omaima Bamasaq 1, Aiiad Albeshri 1 and Li Cheng 3 1 Computer Science Department, Faculty of Computing and Information Technology, King Abdulaziz University, Jeddah 21589, Saudi Arabia; [email protected] (O.B.); [email protected] (A.A.) 2 Information Systems Department, Faculty of Computing and Information Technology, King Abdulaziz University, Jeddah 21589, Saudi Arabia; [email protected] 3 Xinjiang Technical Institute of Physics & Chemistry Chinese Academy of Sciences, Urumqi 830011, China; [email protected] * Correspondence: [email protected] Abstract: Internet of Things (IoT) is promising technology that brings tremendous benefits if used optimally. At the same time, it has resulted in an increase in cybersecurity risks due to the lack of security for IoT devices. IoT botnets, for instance, have become a critical threat; however, systematic and comprehensive studies analyzing the importance of botnet detection methods are limited in the IoT environment. Thus, this study aimed to identify, assess and provide a thoroughly review of experimental works on the research relevant to the detection of IoT botnets. To accomplish this goal, a systematic literature review (SLR), an effective method, was applied for gathering and critically reviewing research papers. This work employed three research questions on the detection methods used to detect IoT botnets, the botnet phases and the different malicious activity scenarios. The authors analyzed the nominated research and the key methods related to them. The detection Citation: Wazzan, M.; Algazzawi, D.; methods have been classified based on the techniques used, and the authors investigated the botnet Bamasaq, O.; Albeshri, A.; Cheng, L. -

The Botnet Chronicles a Journey to Infamy
The Botnet Chronicles A Journey to Infamy Trend Micro, Incorporated Rik Ferguson Senior Security Advisor A Trend Micro White Paper I November 2010 The Botnet Chronicles A Journey to Infamy CONTENTS A Prelude to Evolution ....................................................................................................................4 The Botnet Saga Begins .................................................................................................................5 The Birth of Organized Crime .........................................................................................................7 The Security War Rages On ........................................................................................................... 8 Lost in the White Noise................................................................................................................. 10 Where Do We Go from Here? .......................................................................................................... 11 References ...................................................................................................................................... 12 2 WHITE PAPER I THE BOTNET CHRONICLES: A JOURNEY TO INFAMY The Botnet Chronicles A Journey to Infamy The botnet time line below shows a rundown of the botnets discussed in this white paper. Clicking each botnet’s name in blue will bring you to the page where it is described in more detail. To go back to the time line below from each page, click the ~ at the end of the section. 3 WHITE -

Technical Brief P2P Iot Botnets Clean AC Font
Uncleanable and Unkillable: The Evolution of IoT Botnets Through P2P Networking Technical Brief By Stephen Hilt, Robert McArdle, Fernando Merces, Mayra Rosario, and David Sancho Introduction Peer-to-peer (P2P) networking is a way for computers to connect to one another without the need for a central server. It was originally invented for file sharing, with BitTorrent being the most famous P2P implementation. Decentralized file-sharing systems built on P2P networking have stood the test of time. Even though they have been used to share illegal pirated content for over 20 years, authorities have not been able to put a stop to these systems. Of course, malicious actors have used it for malware for quite a long time as well. Being able to create and manage botnets without the need for a central server is a powerful capability, mostly because law enforcement and security companies typically take down criminal servers. And since a P2P botnet does not need a central command-and-control (C&C) server, it is much more difficult to take down. From the point of view of defenders, this is the scariest problem presented by P2P botnets: If they cannot be taken down centrally, the only option available would be to disinfect each of the bot clients separately. Since computers communicate only with their own peers, the good guys would need to clean all the members one by one for a botnet to disappear. Originally, P2P botnets were implemented in Windows, but developers of internet-of-things (IoT) botnets do have a tendency to start incorporating this feature into their creations. -

Internet Infrastructure Review Vol.34
Internet Infrastructure Review Mar.2017 Vol. 34 Infrastructure Security Ursnif (Gozi) Anti-Analysis Techniques and Methods for Bypassing Them Technology Trends The Current State of Library OSes Internet Infrastructure Review March 2017 Vol.34 Executive Summary ............................................................................................................................ 3 1. Infrastructure Security .................................................................................................................. 4 1.1 Introduction ..................................................................................................................................... 4 1.2 Incident Summary ........................................................................................................................... 4 1.3 Incident Survey ...............................................................................................................................11 1.3.1 DDoS Attacks ...................................................................................................................................11 1.3.2 Malware Activities ......................................................................................................................... 13 1.3.3 SQL Injection Attacks ..................................................................................................................... 17 1.3.4 Website Alterations ....................................................................................................................... -

Generation of an Iot Botnet Dataset in a Medium-Sized Iot Network
MedBIoT: Generation of an IoT Botnet Dataset in a Medium-sized IoT Network Alejandro Guerra-Manzanares a, Jorge Medina-Galindo, Hayretdin Bahsi b and Sven Nomm˜ c Department of Software Science, Tallinn University of Technology, Tallinn, Estonia falejandro.guerra, hayretdin.bahsi, [email protected], [email protected] Keywords: Botnet, Internet of Things, Dataset, Intrusion Detection, Anomaly Detection, IoT. Abstract: The exponential growth of the Internet of Things in conjunction with the traditional lack of security mecha- nisms and resource constraints associated with these devices have posed new risks and challenges to security in networks. IoT devices are compromised and used as amplification platforms by cyber-attackers, such as DDoS attacks. Machine learning-based intrusion detection systems aim to overcome network security lim- itations relying heavily on data quantity and quality. In the case of IoT networks these data are scarce and limited to small-sized networks. This research addresses this issue by providing a labelled behavioral IoT data set, which includes normal and actual botnet malicious network traffic, in a medium-sized IoT network infrastructure (83 IoT devices). Three prominent botnet malware are deployed and data from botnet infec- tion, propagation and communication with C&C stages are collected (Mirai, BashLite and Torii). Binary and multi-class machine learning classification models are run on the acquired data demonstrating the suitability and reliability of the generated data set for machine learning-based botnet detection IDS testing, design and deployment. The generated IoT behavioral data set is released publicly available as MedBIoT data set∗. 1 INTRODUCTION lam, 2017; Bosche et al., 2018; Pratt, 2019). -
Evolution of Iot Attacks
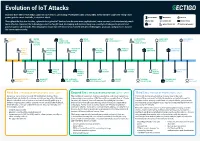
Evolution of IoT Attacks By 2025, there will be 41.6 billion connected IoT devices, generating 79 zettabytes (ZB) of data (IDC). Every Internet-connected “thing,” from power grids to smart doorbells, is at risk of attack. BLUETOOTH INDUSTRIAL MEDICAL Throughout the last few decades, cyberattacks against IoT devices have become more sophisticated, more common, and unfortunately, much BOTNET GENERIC IOT SMART HOME more effective. However, the technology sector has fought back, developing and implementing new security technologies to prevent and CAR INFRASTRUCTURE WATCH/WEARABLE protect against cyberattacks. This infographic shows how the industry has evolved with new technologies, protocols, and processes to raise the bar on cybersecurity. STUXNET WATER BMW MIRAI FITBIT SAUDI PETROL SILEX LINUX DARK NEXUS VIRUS UTILITY CONNECTED BOTNET VULNERABILITY CHEMICAL MALWARE BOTNET SYSTEM DRIVE SYSTEM PLANT ATTACK (SCADA) PUERTO UNIVERSITY UKRAINIAN HAJIME AMNESIA AMAZON PHILIPS HUE RICO OF MICHIGAN POWER VIGILANTE BOTNET RING HACK LIGHTBULB SMART TRAFFIC GRID BOTNET METERS LIGHTS MEDTRONIC GERMAN TESLA CCTV PERSIRAI FANCY SWEYNTOOTH INSULIN STEEL MODEL S BOTNET BOTNET BEAR VS. FAMILY PUMPS MILL HACK REMOTE SPORTS HACK HACKABLE HEART BASHLITE FIAT CHRYSLER NYADROP SELF- REAPER THINKPHP TWO MILLION KAIJI MONITORS BOTNET REMOTE CONTROL UPDATING MALWARE BOTNET EXPLOITATION TAKEOVER MALWARE First Era | THE AGE OF EXPLORATION | 2005 - 2009 Second Era | THE AGE OF EXPLOITATION | 2011 - 2019 Third Era | THE AGE OF PROTECTION | 2020 Security is not a priority for early IoT/embedded devices. Most The number of connected devices is exploding, and cloud connectivity Connected devices are ubiquitous in every area of life, from cyberattacks are limited to malware and viruses impacting Windows- is becoming commonplace. -

An Analysis of the Asprox Botnet
An Analysis of the Asprox Botnet Ravishankar Borgaonkar Technical University of Berlin Email: [email protected] Abstract—The presence of large pools of compromised com- motives. Exploitable vulnerabilities may exist in the Internet puters, also known as botnets, or zombie armies, represents a infrastructure, in the clients and servers, in the people, and in very serious threat to Internet security. This paper describes the way money is controlled and transferred from the Internet the architecture of a contemporary advanced bot commonly known as Asprox. Asprox is a type of malware that combines into traditional cash. Many security firms and researchers are the two threat vectors of forming a botnet and of generating working on developing new methods to fight botnets and to SQL injection attacks. The main features of the Asprox botnet mitigate against threats from botnets [7], [8], [9]. are the use of centralized command and control structure, HTTP based communication, use of advanced double fast-flux service Unfortunately, there are still many questions that need to networks, use of SQL injection attacks for recruiting new bots be addressed to find effective ways of protecting against the and social engineering tricks to spread malware binaries. The threats from botnets. In order to fight against botnets in future, objective of this paper is to contribute to a deeper understanding of Asprox in particular and a better understanding of modern it is not enough to study the botnets of past. Botnets are botnet designs in general. This knowledge can be used to develop constantly evolving, and we need to understand the design more effective methods for detecting botnets, and stopping the and structure of the emerging advanced botnets. -

Iptrust Botnet / Malware Dictionary This List Shows the Most Common Botnet and Malware Variants Tracked by Iptrust
ipTrust Botnet / Malware Dictionary This list shows the most common botnet and malware variants tracked by ipTrust. This is not intended to be an exhaustive list, since new threat intelligence is always being added into our global Reputation Engine. NAME DESCRIPTION Conficker A/B Conficker A/B is a downloader worm that is used to propagate additional malware. The original malware it was after was rogue AV - but the army's current focus is undefined. At this point it has no other purpose but to spread. Propagation methods include a Microsoft server service vulnerability (MS08-067) - weakly protected network shares - and removable devices like USB keys. Once on a machine, it will attach itself to current processes such as explorer.exe and search for other vulnerable machines across the network. Using a list of passwords and actively searching for legitimate usernames - the ... Mariposa Mariposa was first observed in May 2009 as an emerging botnet. Since then it has infected an ever- growing number of systems; currently, in the millions. Mariposa works by installing itself in a hidden location on the compromised system and injecting code into the critical process ͞ĞdžƉůŽƌĞƌ͘ĞdžĞ͘͟/ƚŝƐknown to affect all modern Windows versions, editing the registry to allow it to automatically start upon login. Additionally, there is a guard that prevents deletion while running, and it automatically restarts upon crash/restart of explorer.exe. In essence, Mariposa opens a backdoor on the compromised computer, which grants full shell access to ... Unknown A botnet is designated 'unknown' when it is first being tracked, or before it is given a publicly- known common name. -

A PRACTICAL METHOD of IDENTIFYING CYBERATTACKS February 2018 INDEX
In Collaboration With A PRACTICAL METHOD OF IDENTIFYING CYBERATTACKS February 2018 INDEX TOPICS EXECUTIVE SUMMARY 4 OVERVIEW 5 THE RESPONSES TO A GROWING THREAT 7 DIFFERENT TYPES OF PERPETRATORS 10 THE SCOURGE OF CYBERCRIME 11 THE EVOLUTION OF CYBERWARFARE 12 CYBERACTIVISM: ACTIVE AS EVER 13 THE ATTRIBUTION PROBLEM 14 TRACKING THE ORIGINS OF CYBERATTACKS 17 CONCLUSION 20 APPENDIX: TIMELINE OF CYBERSECURITY 21 INCIDENTS 2 A Practical Method of Identifying Cyberattacks EXECUTIVE OVERVIEW SUMMARY The frequency and scope of cyberattacks Cyberattacks carried out by a range of entities are continue to grow, and yet despite the seriousness a growing threat to the security of governments of the problem, it remains extremely difficult to and their citizens. There are three main sources differentiate between the various sources of an of attacks; activists, criminals and governments, attack. This paper aims to shed light on the main and - based on the evidence - it is sometimes types of cyberattacks and provides examples hard to differentiate them. Indeed, they may of each. In particular, a high level framework sometimes work together when their interests for investigation is presented, aimed at helping are aligned. The increasing frequency and severity analysts in gaining a better understanding of the of the attacks makes it more important than ever origins of threats, the motive of the attacker, the to understand the source. Knowing who planned technical origin of the attack, the information an attack might make it easier to capture the contained in the coding of the malware and culprits or frame an appropriate response. the attacker’s modus operandi. -

C&C Botnet Detection Over
C&C Botnet Detection over SSL Riccardo Bortolameotti University of Twente - EIT ICT Labs masterschool [email protected] Dedicated to my parents Remo and Chiara, and to my sister Anna 2 Abstract Nowadays botnets are playing an important role in the panorama of cyber- crime. These cyber weapons are used to perform malicious activities such fi- nancial frauds, cyber-espionage, etc... using infected computers. This threat can be mitigated by detecting C&C channels on the network. In literature many solutions have been proposed. However, botnet are becoming more and more complex, and currently they are trying to move towards encrypted solutions. In this work, we have designed, implemented and validated a method to detect botnet C&C communication channels over SSL, the se- curity protocol standard de-facto. We provide a set of SSL features that can be used to detect malicious connections. Using our features, the results indicate that we are able to detect, what we believe to be, a botnet and ma- licious connections. Our system can also be considered privacy-preserving and lightweight, because the payload is not analyzed and the portion of an- alyzed traffic is very small. Our analysis also indicates that 0.6% of the SSL connections were broken. Limitations of the system, its applications and possible future works are also discussed. 3 4 Contents 1 Introduction 7 1.1 Problem Statement . .9 1.2 Research questions . 10 1.2.1 Layout of the thesis . 11 2 State of the Art 13 2.1 Preliminary concepts . 13 2.1.1 FFSN .