Cryptography Manual
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
CS 241 Data Organization Ciphers
CS 241 Data Organization Ciphers March 22, 2018 Cipher • In cryptography, a cipher (or cypher) is an algorithm for performing encryption or decryption. • When using a cipher, the original information is known as plaintext, and the encrypted form as ciphertext. • The encrypting procedure of the cipher usually depends on a piece of auxiliary information, called a key. • A key must be selected before using a cipher to encrypt a message. • Without knowledge of the key, it should be difficult, if not nearly impossible, to decrypt the resulting ciphertext into readable plaintext. Substitution Cipher • In cryptography, a substitution cipher is a method of encryption by which units of plaintext are replaced with ciphertext according to a regular system. • Example: case insensitive substitution cipher using a shifted alphabet with keyword "zebras": • Plaintext alphabet: ABCDEFGHIJKLMNOPQRSTUVWXYZ • Ciphertext alphabet: ZEBRASCDFGHIJKLMNOPQTUVWXY flee at once. we are discovered! Enciphers to SIAA ZQ LKBA. VA ZOA RFPBLUAOAR! Other substitution ciphers Caesar cipher Shift alphabet by fixed amount. (Caesar apparently used 3.) ROT13 Replace letters with those 13 away. Used to hide spoilers on newsgroups. pigpen cipher Replace letters with symbols. Substitution Cipher: Encipher Example OENp(ENTE#X@EN#zNp(ENCL]pEnN7p-pE;8N]LN} dnEdNp#Nz#duN-Nu#dENXEdzE9pNCL]#L8NE;p-b @];(N0G;p]9E8N]L;GdENn#uE;p]9Nld-L/G]@]p _8NXd#|]nENz#dNp(EN9#uu#LNnEzEL;E8NXd#u# pENp(ENQELEd-@NOE@z-dE8N-LnN;E9GdENp(EN^ @E;;]LQ;N#zN<]bEdp_Np#N#Gd;E@|E;N-LnN#Gd NT#;pEd]p_8Nn#N#dn-]LN-LnNE;p-b@];(Np(]; N5#L;p]pGp]#LNz#dNp(ENCL]pEnN7p-pE;N#zN) uEd]9-D Breaking a Substitution Cipher In English, • The most common character is the space: \ ". -
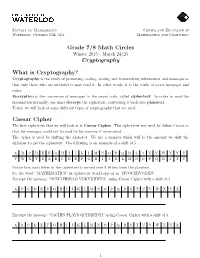
Grade 7/8 Math Circles Cryptography What Is Cryptography? Caesar Cipher
Faculty of Mathematics Centre for Education in Waterloo, Ontario N2L 3G1 Mathematics and Computing Grade 7/8 Math Circles Winter 2015 - March 24/25 Cryptography What is Cryptography? Cryptography is the study of protecting, coding, storing and transmitting information and messages so that only those who are intended to may read it. In other words, it is the study of secret messages and codes. Encryption is the conversion of messages to the secret code, called ciphertext. In order to read the information normally, one must decrypt the ciphertext, converting it back into plaintext. Today, we will look at some different types of cryptography that are used. Caesar Cipher The first ciphertext that we will look at is Caesar Cipher. This ciphertext was used by Julius Caesar so that his messages could not be read by his enemies if intercepted. The cipher is used by shifting the alphabet. We use a number which will be the amount we shift the alphabet to get the ciphertext. The following is an example of a shift of 5: A B C D E F G H I J K L M N O P Q R S T U V W X Y Z V W X Y Z A B C D E F G H I J K L M N O P Q R S T U Notice how each letter in the ciphertext is moved over 5 letters from the plaintext. So, the word \MATHEMATICS" in ciphertext would appear as \HVOCZHVODXN". Decrypt the message \NUWJ HKRAO YDKYKHWPA" using Caesar Cipher with a shift of 4. -

Grade 6 Math Circles Cryptography Solutions Atbash Cipher Caesar Cipher
Faculty of Mathematics Centre for Education in Waterloo, Ontario N2L 3G1 Mathematics and Computing Grade 6 Math Circles November 5/6 2019 Cryptography Solutions Hello World Khoor Zruog Hello Zruog Khoor Khoor Zruog World 1. Person A encrypts plaintext 2. Person B receives ciphertext 3. Person B decrypts ciphertext back into ciphertext into plaintext Atbash Cipher Examples 1. Encrypt \Math Circles" using the Atbash cipher. Nzgs Xrixovh 2. Decrypt \ORLM PRMT" using the Atbash cipher. LION KING Caesar Cipher Examples: Encrypt or decrypt the following messages using the shift number given in parentheses: a) Welcome to Math Circles! (5) Bjqhtrj yt Rfym Hnwhqjx! plaintext A B C D E F G H I J K L M N O P Q R S T U V W X Y Z ciphertext F G H I J K L M N O P Q R S T U V W X Y Z A B C D E 1 b) Ljw hxd anjm cqrb? (9) Can you read this? plaintext A B C D E F G H I J K L M N O P Q R S T U V W X Y Z ciphertext J K L M N O P Q R S T U V W X Y Z A B C D E F G H I c) What if I did a Caesar Shift of 26 units on \Welcome to Math Circles!"? A Caesar shift of 26 would be shifting by the length of the alphabet. For example I would be shifting A 26 letters to the right. -
Loads of Codes – Cryptography Activities for the Classroom
Loads of Codes – Cryptography Activities for the Classroom Paul Kelley Anoka High School Anoka, Minnesota In the next 90 minutes, we’ll look at cryptosystems: Caesar cipher St. Cyr cipher Tie-ins with algebra Frequency distribution Vigenere cipher Cryptosystem – an algorithm (or series of algorithms) needed to implement encryption and decryption. For our purposes, the words encrypt and encipher will be used interchangeably, as will decrypt and decipher. The idea behind all this is that you want some message to get somewhere in a secure fashion, without being intercepted by “the bad guys.” Code – a substitution at the level of words or phrases Cipher – a substitution at the level of letters or symbols However, I think “Loads of Codes” sounds much cooler than “Loads of Ciphers.” Blackmail = King = Today = Capture = Prince = Tonight = Protect = Minister = Tomorrow = Capture King Tomorrow Plaintext: the letter before encryption Ciphertext: the letter after encryption Rail Fence Cipher – an example of a “transposition cipher,” one which doesn’t change any letters when enciphered. Example: Encipher “DO NOT DELAY IN ESCAPING,” using a rail fence cipher. You would send: DNTEAIECPN OODLYNSAIG Null cipher – not the entire message is meaningful. My aunt is not supposed to read every epistle tonight. BXMT SSESSBW POE ILTWQS RIA QBTNMAAD OPMNIKQT RMI MNDLJ ALNN BRIGH PIG ORHD LLTYQ BXMT SSESSBW POE ILTWQS RIA QBTNMAAD OPMNIKQT RMI MNDLJ ALNN BRIGH PIG ORHD LLTYQ Anagram – use the letters of one word, phrase or sentence to form a different one. Example: “Meet behind the castle” becomes “These belched a mitten.” Substitution cipher – one in which the letters change during encryption. -

CODE SCHOOL: TOP SECRET COMMUNICATIONS DURING WWII Codes and Ciphers a Code Is a Word Or Message That Is Replaced with an Agreed Code Word Or Symbol
CODE SCHOOL: TOP SECRET COMMUNICATIONS DURING WWII Codes and Ciphers A code is a word or message that is replaced with an agreed code word or symbol. A cipher is when each letter in an alphabet is replaced with another letter, number, picture, or other symbol. Ciphers always have key that is shared among those sending and receiving the message. A coded message would be like saying, “The eagle has landed!”, while a cipher may look like this: 8-5-12-12-15. In the cipher, each letter of the alphabet has been replaced by its corresponding number (A = 1). Do you know the message? Communications during Wartime Navajo Code Talkers Humans figured out how to send secret One incredible example of transmitting secret messages a long time ago. The Greeks used messages was through the US’s use of the something we now call the Caesar cipher (the Navajo language. More than 400 Navajo alphabet is shifted so each letter is replaced by Indians served as code talkers, communicating a different one), while Spartans used a device secret messages for the U.S. Marines. These called a scytale (where a message was written Navajo servicemen were specially trained to on a piece of paper and would be read using a use their own language to communicate during special rod). battles throughout the Pacific campaign. The Navajo code used their own Navajo words to stand for English words. For example, the English word “air” was translated into the Navajo word for air. If an English word did not exist in the Navajo language, they would use Navajo words to symbolize the English word— Skytale submarine became besh-lo, meaning iron fish. -
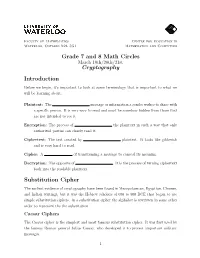
Grade 7 and 8 Math Circles Cryptography Introduction
Faculty of Mathematics Centre for Education in Waterloo, Ontario N2L 3G1 Mathematics and Computing Grade 7 and 8 Math Circles March 19th/20th/21st Cryptography Introduction Before we begin, it's important to look at some terminology that is important to what we will be learning about. Plaintext: The message or information a sender wishes to share with a specific person. It is very easy to read and must be somehow hidden from those that are not intended to see it. Encryption: The process of the plaintext in such a way that only authorized parties can clearly read it. Ciphertext: The text created by plaintext. It looks like gibberish and is very hard to read. Cipher: A of transforming a message to conceal its meaning. Decryption: The opposite of . It is the process of turning ciphertext back into the readable plaintext. Substitution Cipher The earliest evidence of cryptography have been found in Mesopotamian, Egyptian, Chinese, and Indian writings, but it was the Hebrew scholars of 600 to 500 BCE that began to use simple substitution ciphers. In a substitution cipher the alphabet is rewritten in some other order to represent the the substitution. Caesar Ciphers The Caesar cipher is the simplest and most famous substitution cipher. It was first used by the famous Roman general Julius Caesar, who developed it to protect important military messages. 1 To produce a Caesar cipher simply shift the alphabet some units to the right. Julius Caesar's original cipher was created by shifting the alphabet three units to the right, as shown below. plaintext A B C D E F G H I J K L M ciphertext X Y Z A B C D E F G H I J plaintext N O P Q R S T U V W X Y Z ciphertext K L M N O P Q R S T U V W When encrypting a message, match every letter in the plaintext with the corresponding ciphertext letter beneath it. -

Top Secret! Shhhh! Codes and Ciphers
Top Secret! Shhhh! Codes and Ciphers 20 15 16 19 5 3 18 5 20 19 8 8 8 Can you figure out what this message says? Do you love secret codes? Do you want to be able to write messages to friends that no one else can read? In this kit you will get to try some codes and learn to code and decode messages. Materials Included in your Kit Directions and template pages Answer key for all codes in this packet starts on page 8. 1 #2 Pencil 1 Brad Fastener Tools You’ll Need from Home Scissors A Piece of Tape Terminology First let’s learn a few terms together. CODE A code is a set of letters, numbers, symbols, etc., that is used to secretly send messages to someone. CIPHER A cipher is a method of transforming a text in order to conceal its meaning. KEY PHRASE / KEY OBJECT A key phrase lets the sender tell the recipient what to use to decode a message. A key object is a physical item used to decrypt a code. ENCRYPT This means to convert something written in plain text into code. DECRYPT This means to convert something written in code into plain text. Why were codes and ciphers used? Codes have been used for thousands of years by people who needed to share secret information with one another. Your mission is to encrypt and decrypt messages using different types of code. The best way to learn to read and write in code is to practice! SCYTALE Cipher The Scytale was used by the ancient Greeks. -
Crypyto Documentation Release 0.2.0
crypyto Documentation Release 0.2.0 Yan Orestes Aug 22, 2018 API Documentation 1 Getting Started 3 1.1 Dependencies...............................................3 1.2 Installing.................................................3 2 Ciphers 5 2.1 Polybius Square.............................................5 2.2 Atbash..................................................6 2.3 Caesar Cipher..............................................7 2.4 ROT13..................................................8 2.5 Affine Cipher...............................................9 2.6 Rail Fence Cipher............................................9 2.7 Keyword Cipher............................................. 10 2.8 Vigenère Cipher............................................. 11 2.9 Beaufort Cipher............................................. 12 2.10 Gronsfeld Cipher............................................. 13 3 Substitution Alphabets 15 3.1 Morse Code............................................... 15 3.2 Binary Translation............................................ 16 3.3 Pigpen Cipher.............................................. 16 3.4 Templar Cipher.............................................. 18 3.5 Betamaze Alphabet............................................ 19 Python Module Index 21 i ii crypyto Documentation, Release 0.2.0 crypyto is a Python package that provides a set of cryptographic tools with simple use to your applications. API Documentation 1 crypyto Documentation, Release 0.2.0 2 API Documentation CHAPTER 1 Getting Started These instructions -

Lesson Plan: 1.1 Encryption Algorithms
Course: Advanced Cybersecurity | Module: Advanced Cryptography Lesson 1.1: Encryption Algorithms https://codehs.com/course/7606/lesson/1.1 In this lesson, students will learn about the basics of symmetric encryption. Students will explore the advantages and disadvantages of various ciphers and consider how using multiple ciphers Description impacts the decryption process. Students will also learn about the DES (Data Encryption Standard) and the AES (Advanced Encryption Standard). Students will be able to: Explain the characteristics of symmetric algorithms and use them to encode and decode text. Objective Specific ciphers include block, substitution, and transposition ciphers. Compare and contrast the strengths and weaknesses of symmetric ciphers. Compare and contrast the DES (Data Encryption Standard) and the AES (Advanced Encryption Standard). 1.1.1 Video: Encryption Algorithms 1.1.2 Quiz: Encryption Algorithms Quiz 1.1.3 Free Response: Enhanced Caesar Cipher Activities 1.1.4 Free Response: Mixed Alphabet Cipher 1.1.5 Example: Pigpen Encoder 1.1.6 Free Response: Pigpen Cipher 1.1.7 Free Response: Rail Fence Cipher This is an introductory lesson, so there is no prior knowledge necessary. However, students Prior Knowledge will be better equipped to discuss the advantages and disadvantages of ciphers if they are familiar with brute force attacks and letter frequency analysis. Students will be introduced to many new vocabulary words over the course of this lesson and throughout the unit. To help students keep track of and use new words, write new vocabulary on the board or on an anchor chart that hangs in your class. Due to the number of activities in this lesson, it is a longer lesson that can be spread across Planning Notes multiple days. -

On the Subject of Odd One Out
Keep Talking and Nobody Explodes Mod Odd One Out On the Subject of Odd One Out One of these things is not like the others! One of these things just doesn’t belong! There are six buttons on the module which may display a variety of things directly on the button or in the display whilst hovering over a button. Five of the buttons, referred to below as the “good buttons”, satisfy a specific property which is described in the table below. Press the button that doesn’t belong — the “odd one out” — to move on to the next stage. The current stage is indicated by LEDs at the top of the module. Once 5 stages have been completed, press the button that has had the correct answer a unique number of times to disarm the module. You may long-press any button to reset the module back to stage 1. Display set Instructions Depending on the color of the LED to the right of the display: Red LED: The good buttons form a sequence of letters with equal distance in the alphabet, wrapping around from Z back to A. Yellow LED: The good buttons, when read in reading order, form a five-letter English word that is encoded using Atbash cipher. In this cipher, A↔Z, B↔Y, C↔X, etc. Green LED: The good buttons, when read in reading order, form a five-letter English word that is encoded using ROT13. In this Letters cipher, A↔N, B↔O, C↔P, etc. Turquoise LED: The good buttons have letters whose Morse code begins with the same two symbols. -

The Cultural Contradictions of Cryptography: a History of Secret Codes in Modern America
The Cultural Contradictions of Cryptography: A History of Secret Codes in Modern America Charles Berret Submitted in partial fulfillment of the requirements for the degree of Doctor of Philosophy under the Executive Committee of the Graduate School of Arts and Sciences Columbia University 2019 © 2018 Charles Berret All rights reserved Abstract The Cultural Contradictions of Cryptography Charles Berret This dissertation examines the origins of political and scientific commitments that currently frame cryptography, the study of secret codes, arguing that these commitments took shape over the course of the twentieth century. Looking back to the nineteenth century, cryptography was rarely practiced systematically, let alone scientifically, nor was it the contentious political subject it has become in the digital age. Beginning with the rise of computational cryptography in the first half of the twentieth century, this history identifies a quarter-century gap beginning in the late 1940s, when cryptography research was classified and tightly controlled in the US. Observing the reemergence of open research in cryptography in the early 1970s, a course of events that was directly opposed by many members of the US intelligence community, a wave of political scandals unrelated to cryptography during the Nixon years also made the secrecy surrounding cryptography appear untenable, weakening the official capacity to enforce this classification. Today, the subject of cryptography remains highly political and adversarial, with many proponents gripped by the conviction that widespread access to strong cryptography is necessary for a free society in the digital age, while opponents contend that strong cryptography in fact presents a danger to society and the rule of law. -

Substitution Cipher in Cryptography, a Substitution Cipher Is a Method Of
Substitution cipher In cryptography, a substitution cipher is a method of encryption by which units of plaintext are replaced with ciphertext according to a regular system; the "units" may be single letters (the most common), pairs of letters, triplets of letters, mixtures of the above, and so forth. The receiver deciphers the text by performing an inverse substitution. Substitution ciphers can be compared with transposition ciphers. In a transposition cipher, the units of the plaintext are rearranged in a different and usually quite complex order, but the units themselves are left unchanged. By contrast, in a substitution cipher, the units of the plaintext are retained in the same sequence in the ciphertext, but the units themselves are altered. There are a number of different types of substitution cipher. If the cipher operates on single letters, it is termed a simple substitution cipher; a cipher that operates on larger groups of letters is termed polygraphic. A monoalphabetic cipher uses fixed substitution over the entire message, whereas a polyalphabetic cipher uses a number of substitutions at different times in the message, where a unit from the plaintext is mapped to one of several possibilities in the ciphertext and vice-versa. Contents • 1 Simple substitution o 1.1 Examples o 1.2 Security for simple substitution ciphers • 2 Homophonic substitution • 3 Polyalphabetic substitution • 4 Polygraphic substitution • 5 Mechanical substitution ciphers • 6 The one-time pad • 7 Substitution in modern cryptography • 8 Substitution ciphers in popular culture Simple substitution 1 ROT13 is a Caesar cipher, a type of substitution cipher. In ROT13, the alphabet is rotated 13 steps.