Review on Multiple Access Techniques Used in Mobile Telecommunication Generations
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
Implementing MACA and Other Useful Improvements to Amateur Packet Radio for Throughput and Capacity
Implementing MACA and Other Useful Improvements to Amateur Packet Radio for Throughput and Capacity John Bonnett – KK6JRA / NCS820 Steven Gunderson – CMoLR Project Manager TAPR DCC – 15 Sept 2018 1 Contents • Introduction – Communication Methodology of Last Resort (CMoLR) • Speed & Throughput Tests – CONNECT & UNPROTO • UX.25 – UNPROTO AX.25 • Multiple Access with Collision Avoidance (MACA) – Hidden Terminals • Directed Packet Networks • Brevity – Directory Services • Trunked Packet • Conclusion 2 Background • Mission County – Proverbial: – Coastline, Earthquake Faults, Mountains & Hills, and Missions – Frequent Natural Disasters • Wildfires, Earthquakes, Floods, Slides & Tsunamis – Extensive Packet Networks • EOCs – Fire & Police Stations – Hospitals • Legacy 1200 Baud Packet Networks • Outpost and Winlink 2000 Messaging Software 3 Background • Mission County – Proverbial: – Coastline, Earthquake Faults, Mountains & Hills, and Missions – Frequent Natural Disasters • Wildfires, Earthquakes, Floods, Slides & Tsunamis – Extensive Packet Networks • EOCs – Fire & Police Stations – Hospitals • Legacy 1200 Baud Packet Networks • Outpost and Winlink 2000 Messaging Software • Community Emergency Response Teams: – OK Drills – Neighborhood Surveys OK – Triage Information • CERT Form #1 – Transmit CERT Triage Data to Public Safety – Situational Awareness 4 Background & Objectives (cont) • Communication Methodology of Last Resort (CMoLR): – Mission County Project: 2012 – 2016 – Enable Emergency Data Comms from CERT to Public Safety 5 Background & -
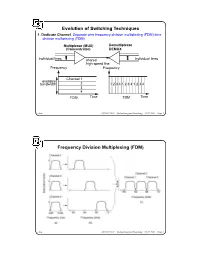
Evolution of Switching Techniques Frequency Division Multiplexing
Evolution of Switching Techniques 1. Dedicate Channel. Separate wire frequency division multiplexing (FDM) time division multiplexing (TDM) Multiplexor (MUX) Demultiplexor (Concentrator) DEMUX individual lines shared individual lines high speed line Frequency Frequency Channel 1 available bandwidth 2 1 2 3 4 1 2 3 4 1 2 3 4 3 4 FDM Time TDM Time chow CS522 F2001—Multiplexing and Switching—10/17/2001—Page 1 Frequency Division Multiplexing (FDM) chow CS522 F2001—Multiplexing and Switching—10/17/2001—Page 2 Wavelength Division Multiplexing chow CS522 F2001—Multiplexing and Switching—10/17/2001—Page 3 Impact of WDM z Many big organizations are starting projects to design WDM system or DWDN (Dense Wave Division Mutiplexing Network). We may see products appear in next three years.In Fujitsu and CCL/Taiwan, 128 different wavelengthes on the same strand of fiber was reported working in the lab. z We may have optical routers between end systems that can take one wavelenght signal, covert to different wavelenght, send it out on different links. Some are designing traditional routers that covert optical signal to electronical signal, and use time slot interchange based on high speed memory to do the switching, the convert the electronic signal back to optical signal. z With this type of optical networks, we will have a virtual circuit network, where each connection is assigned some wave length. Each connection can have 2.4 gbps tremedous bandwidth. z With inital 128 different wavelength, we can have about 10 end users. If each pair of end users needs to communicate simultaneously, it will use 10*10=100 different wavelength. -

Reservation - Time Division Multiple Access Protocols for Wireless Personal Communications
tv '2s.\--qq T! Reservation - Time Division Multiple Access Protocols for Wireless Personal Communications Theodore V. Buot B.S.Eng (Electro&Comm), M.Eng (Telecomm) Thesis submitted for the degree of Doctor of Philosophy 1n The University of Adelaide Faculty of Engineering Department of Electrical and Electronic Engineering August 1997 Contents Abstract IY Declaration Y Acknowledgments YI List of Publications Yrt List of Abbreviations Ylu Symbols and Notations xi Preface xtv L.Introduction 1 Background, Problems and Trends in Personal Communications and description of this work 2. Literature Review t2 2.1 ALOHA and Random Access Protocols I4 2.1.1 Improvements of the ALOHA Protocol 15 2.1.2 Other RMA Algorithms t6 2.1.3 Random Access Protocols with Channel Sensing 16 2.1.4 Spread Spectrum Multiple Access I7 2.2Fixed Assignment and DAMA Protocols 18 2.3 Protocols for Future Wireless Communications I9 2.3.1 Packet Voice Communications t9 2.3.2Reservation based Protocols for Packet Switching 20 2.3.3 Voice and Data Integration in TDMA Systems 23 3. Teletraffic Source Models for R-TDMA 25 3.1 Arrival Process 26 3.2 Message Length Distribution 29 3.3 Smoothing Effect of Buffered Users 30 3.4 Speech Packet Generation 32 3.4.1 Model for Fast SAD with Hangover 35 3.4.2Bffect of Hangover to the Speech Quality 38 3.5 Video Traffic Models 40 3.5.1 Infinite State Markovian Video Source Model 41 3.5.2 AutoRegressive Video Source Model 43 3.5.3 VBR Source with Channel Load Feedback 43 3.6 Summary 46 4. -

A Survey on Aloha Protocol for Iot Based Applications
ISSN: 2277-9655 [Badgotya * et al., 7(5): May, 2018] Impact Factor: 5.164 IC™ Value: 3.00 CODEN: IJESS7 IJESRT INTERNATIONAL JOURNAL OF ENGINEERING SCIENCES & RESEARCH TECHNOLOGY A SURVEY ON ALOHA PROTOCOL FOR IOT BASED APPLICATIONS Shikha Badgotya*1 & Prof.Deepti Rai2 *1M.Tech Scholar, Department of EC, Alpine Institute of Technology,, Ujjain (India) 2H.O.D, Department of EC, Alpine Institute of Technology, Ujjain (India) DOI: 10.5281/zenodo.1246995 ABSTRACT With the emergence of IoT based applications in industries and automation, protocols for effective data transfer was the foremost need. The natural choice was a random access protocol like ALOHA which could be incorporated in the ultra narrowband ISM band framework because of its simplicity and lack of overhead. Pure ALOHA faced the limitation of greater rate of collisions among the packets of data and also there was higher level of frame delays. Slotted ALOHA overcame these limitations to some extent in which the transfer of data takes place after channel polling. Though the drawbacks of PURE ALOHA are somewhat resolved in Slotted ALOHA, still some redundant transmissions and delay of frames exist. The present proposed work puts forth an efficient mechanism for Slotted ALOHA which implements polling of channel that is non persistent in nature to reduce the probability of collisions considerably. Further it presents a channel sensing methodology also for prevention of burst errors. Interleaving serves to be useful in case of burst errors and helps in preserving useful information. The survey should pave the path for IoT based applications working on an ultra narrowband architecture. -

Spread Spectrum and Wi-Fi Basics Syed Masud Mahmud, Ph.D
Spread Spectrum and Wi-Fi Basics Syed Masud Mahmud, Ph.D. Electrical and Computer Engineering Dept. Wayne State University Detroit MI 48202 Spread Spectrum and Wi-Fi Basics by Syed M. Mahmud 1 Spread Spectrum Spread Spectrum techniques are used to deliberately spread the frequency domain of a signal from its narrow band domain. These techniques are used for a variety of reasons such as: establishment of secure communications, increasing resistance to natural interference and jamming Spread Spectrum and Wi-Fi Basics by Syed M. Mahmud 2 Spread Spectrum Techniques Frequency Hopping Spread Spectrum (FHSS) Direct -Sequence Spread Spectrum (DSSS) Orthogonal Frequency-Division Multiplexing (OFDM) Spread Spectrum and Wi-Fi Basics by Syed M. Mahmud 3 The FHSS Technology FHSS is a method of transmitting signals by rapidly switching channels, using a pseudorandom sequence known to both the transmitter and receiver. FHSS offers three main advantages over a fixed- frequency transmission: Resistant to narrowband interference. Difficult to intercept. An eavesdropper would only be able to intercept the transmission if they knew the pseudorandom sequence. Can share a frequency band with many types of conventional transmissions with minimal interference. Spread Spectrum and Wi-Fi Basics by Syed M. Mahmud 4 The FHSS Technology If the hop sequence of two transmitters are different and never transmit the same frequency at the same time, then there will be no interference among them. A hopping code determines the frequencies the radio will transmit and in which order. A set of hopping codes that never use the same frequencies at the same time are considered orthogonal . -

Lecture 8: Overview of Computer Networking Roadmap
Lecture 8: Overview of Computer Networking Slides adapted from those of Computer Networking: A Top Down Approach, 5th edition. Jim Kurose, Keith Ross, Addison-Wesley, April 2009. Roadmap ! what’s the Internet? ! network edge: hosts, access net ! network core: packet/circuit switching, Internet structure ! performance: loss, delay, throughput ! media distribution: UDP, TCP/IP 1 What’s the Internet: “nuts and bolts” view PC ! millions of connected Mobile network computing devices: server Global ISP hosts = end systems wireless laptop " running network apps cellular handheld Home network ! communication links Regional ISP " fiber, copper, radio, satellite access " points transmission rate = bandwidth Institutional network wired links ! routers: forward packets (chunks of router data) What’s the Internet: “nuts and bolts” view ! protocols control sending, receiving Mobile network of msgs Global ISP " e.g., TCP, IP, HTTP, Skype, Ethernet ! Internet: “network of networks” Home network " loosely hierarchical Regional ISP " public Internet versus private intranet Institutional network ! Internet standards " RFC: Request for comments " IETF: Internet Engineering Task Force 2 A closer look at network structure: ! network edge: applications and hosts ! access networks, physical media: wired, wireless communication links ! network core: " interconnected routers " network of networks The network edge: ! end systems (hosts): " run application programs " e.g. Web, email " at “edge of network” peer-peer ! client/server model " client host requests, receives -

Circuit-Switched Coherence
Circuit-Switched Coherence ‡Natalie Enright Jerger, ‡Mikko Lipasti, and ?Li-Shiuan Peh ‡Electrical and Computer Engineering Department, University of Wisconsin-Madison ?Department of Electrical Engineering, Princeton University Abstract—Circuit-switched networks can significantly lower contention, overall system performance can degrade by 20% the communication latency between processor cores, when or more. This latency sensitivity coupled with low link uti- compared to packet-switched networks, since once circuits are set up, communication latency approaches pure intercon- lization motivates our exploration of circuit-switched fabrics nect delay. However, if circuits are not frequently reused, the for CMPs. long set up time and poorer interconnect utilization can hurt Our investigations show that traditional circuit-switched overall performance. To combat this problem, we propose a hybrid router design which intermingles packet-switched networks do not perform well, as circuits are not reused suf- flits with circuit-switched flits. Additionally, we co-design a ficiently to amortize circuit setup delay. This observation prediction-based coherence protocol that leverages the exis- motivates a network with a hybrid router design that sup- tence of circuits to optimize pair-wise sharing between cores. The protocol allows pair-wise sharers to communicate di- ports both circuit and packet switching with very fast circuit rectly with each other via circuits and drives up circuit reuse. reconfiguration (setup/teardown). Our preliminary results Circuit-switched coherence provides overall system perfor- show this leading to up to 8% improvement in overall system mance improvements of up to 17% with an average improve- performance over a packet-switched fabric. ment of 10% and reduces network latency by up to 30%. -

Medium Access Control Layer
Telematics Chapter 5: Medium Access Control Sublayer User Server watching with video Beispielbildvideo clip clips Application Layer Application Layer Presentation Layer Presentation Layer Session Layer Session Layer Transport Layer Transport Layer Network Layer Network Layer Network Layer Univ.-Prof. Dr.-Ing. Jochen H. Schiller Data Link Layer Data Link Layer Data Link Layer Computer Systems and Telematics (CST) Physical Layer Physical Layer Physical Layer Institute of Computer Science Freie Universität Berlin http://cst.mi.fu-berlin.de Contents ● Design Issues ● Metropolitan Area Networks ● Network Topologies (MAN) ● The Channel Allocation Problem ● Wide Area Networks (WAN) ● Multiple Access Protocols ● Frame Relay (historical) ● Ethernet ● ATM ● IEEE 802.2 – Logical Link Control ● SDH ● Token Bus (historical) ● Network Infrastructure ● Token Ring (historical) ● Virtual LANs ● Fiber Distributed Data Interface ● Structured Cabling Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.2 Design Issues Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.3 Design Issues ● Two kinds of connections in networks ● Point-to-point connections OSI Reference Model ● Broadcast (Multi-access channel, Application Layer Random access channel) Presentation Layer ● In a network with broadcast Session Layer connections ● Who gets the channel? Transport Layer Network Layer ● Protocols used to determine who gets next access to the channel Data Link Layer ● Medium Access Control (MAC) sublayer Physical Layer Univ.-Prof. Dr.-Ing. Jochen H. Schiller ▪ cst.mi.fu-berlin.de ▪ Telematics ▪ Chapter 5: Medium Access Control Sublayer 5.4 Network Types for the Local Range ● LLC layer: uniform interface and same frame format to upper layers ● MAC layer: defines medium access .. -
F. Circuit Switching
CSE 3461: Introduction to Computer Networking and Internet Technologies Circuit Switching Presentation F Study: 10.1, 10.2, 8 .1, 8.2 (without SONET/SDH), 8.4 10-02-2012 A Closer Look At Network Structure: • network edge: applications and hosts • network core: —routers —network of networks • access networks, physical media: communication links d. xuan 2 1 The Network Core • mesh of interconnected routers • the fundamental question: how is data transferred through net? —circuit switching: dedicated circuit per call: telephone net —packet-switching: data sent thru net in discrete “chunks” d. xuan 3 Network Layer Functions • transport packet from sending to receiving hosts application transport • network layer protocols in network data link network physical every host, router network data link network data link physical data link three important functions: physical physical network data link • path determination: route physical network data link taken by packets from source physical to dest. Routing algorithms network network data link • switching: move packets from data link physical physical router’s input to appropriate network data link application router output physical transport network data link • call setup: some network physical architectures require router call setup along path before data flows d. xuan 4 2 Network Core: Circuit Switching End-end resources reserved for “call” • link bandwidth, switch capacity • dedicated resources: no sharing • circuit-like (guaranteed) performance • call setup required d. xuan 5 Circuit Switching • Dedicated communication path between two stations • Three phases — Establish (set up connection) — Data Transfer — Disconnect • Must have switching capacity and channel capacity to establish connection • Must have intelligence to work out routing • Inefficient — Channel capacity dedicated for duration of connection — If no data, capacity wasted • Set up (connection) takes time • Once connected, transfer is transparent • Developed for voice traffic (phone) g. -
On-Demand Routing in Multi-Hop Wireless Mobile Ad Hoc Networks
Available Online at www.ijcsmc.com International Journal of Computer Science and Mobile Computing A Monthly Journal of Computer Science and Information Technology ISSN 2320–088X IJCSMC, Vol. 2, Issue. 7, July 2013, pg.317 – 321 RESEARCH ARTICLE ON-DEMAND ROUTING IN MULTI-HOP WIRELESS MOBILE AD HOC NETWORKS P. Umamaheswari 1, K. Ranjith singh 2 1Periyar University, TamilNadu, India 2Professor of PGP College, TamilNadu, India 1 [email protected]; 2 [email protected] Abstract— An ad hoc network is a collection of wireless mobile nodes dynamically forming a temporary network without the use of any preexisting network infrastructure or centralized administration. Routing protocols used in ad hoc networks must automatically adjust to environments that can vary between the extremes of high mobility with low bandwidth, and low mobility with high bandwidth. This thesis argues that such protocols must operate in an on-demand fashion and that they must carefully limit the number of nodes required to react to a given topology change in the network. I have embodied these two principles in a routing protocol called Dynamic Source Routing (DSR). As a result of its unique design, the protocol adapts quickly to routing changes when node movement is frequent, yet requires little or no overhead during periods in which nodes move less frequently. By presenting a detailed analysis of DSR’s behavior in a variety of situations, this thesis generalizes the lessons learned from DSR so that they can be applied to the many other new routing protocols that have adopted the basic DSR framework. The thesis proves the practicality of the DSR protocol through performance results collected from a full-scale 8 node tested, and it demonstrates several methodologies for experimenting with protocols and applications in an ad hoc network environment, including the emulation of ad hoc networks. -

Application Note: 2-Cell Test Environment
Application Note 2-cell Test Environment MD8475A Signalling Tester 1. Background to LTE Rollout Mobile phones appearing in the late 1980s soon experienced rapid evolution of functions from 1990 to 2000 and also spread worldwide as key communications infrastructure. The mobile phone is not limited to just two-way communications between two people but also supports sending and receiving of Short Message Services (SMS), web browsing using the Internet, application and video download, etc., and has become a popular and key cultural tool supporting a fuller lifestyle for many people. Figure 1. Evolution on UE According to one research company, total mobile phone (terminal) shipments at the end of 2010 were valued at $38 billion split between 45% for 2G phones and 49% for 3G. Table 1. Mobile Terminal Shipments Mobile Terminal Shipments ($38 billion total) LTE 1.3% WiMAX 4.0% W-CDMA 40.0% CDMA 9.3% GSM 45.4% 1 MD8475A-E-F-1 The purpose of the shift from 2G to 3G systems was to make more efficient use of frequency bandwidths and was closely related to the explosive growth of the Internet. While still maintaining the easy portability of a mobile phone, users were able to access the information they needed easily at any time and place using the Internet. Similarly to growth of 3G technology, the requirements of LTE systems, which is are positioned in the market as 3.9G to maintain competitiveness with coming 4G systems, are being examined. Connectivity with IP-based core networks must be maintained to support multimedia applications and ubiquitous networks using the packet domain. -
ECE 158A: Lecture 13
ECE 158A: Lecture 13 Fall 2015 Random Access and Ethernet! Random Access! Basic idea: Exploit statistical multiplexing Do not avoid collisions, just recover from them When a node has packet to send Transmit at full channel data rate No a priori coordination among nodes Two or more transmitting nodes ⇒ collision Random access MAC protocol specifies: How to detect collisions How to recover from collisions Key Ideas of Random Access Carrier sense Listen before speaking, and don’t interrupt Check if someone else is already sending data and wait till the other node is done Collision detection If someone else starts talking at the same time, stop Realize when two nodes are transmitting at once by detecting that the data on the wire is garbled Randomness Don’t start talking again right away Wait for a random time before trying again Aloha net (70’s) First random access network Setup by Norm Abramson at the University of Hawaii First data communication system for Hawaiian islands Hub at University of Hawaii, Oahu Alohanet had two radio channels: Random access: Sites sending data Broadcast: Hub rebroadcasting data Aloha Signaling Two channels: random access, broadcast Sites send packets to hub (random) If received, hub sends ACK (random) If not received (collision), site resends Hub sends packets to all sites (broadcast) Sites can receive even if they are also sending Questions: When do you resend? Resend with probability p How does this perform? Will analyze in class, stay tuned…. Slot-by-slot Aloha Example