Imagine the Possibilities
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
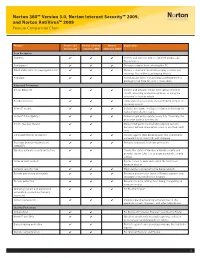
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton Antivirus™ 2009 Feature Comparison Chart
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton AntiVirus™ 2009 Feature Comparison Chart Feature Norton 360 Norton Internet Norton Explanation Version 3.0 Security 2009 AntiVirus 2009 Core Protection Antivirus ✔ ✔ ✔ Detects and removes viruses, Internet worms, and Trojan horses Antispyware ✔ ✔ ✔ Prevents spyware from infecting the PC Email and instant messaging protection ✔ ✔ ✔ Monitors email and instant messaging so users can exchange files without exchanging threats Antispam ✔ ✔ Automatically filters out annoying and fraudulent or phishing email from the user’s email inbox Advanced Protection Botnet detection ✔ ✔ ✔ Detects and prevents others from taking control of the PC, accessing private information, or using the computer to host an attack Rootkit detection ✔ ✔ ✔ Finds and removes threats that are hidden deep in the operating system Norton™ Insight ✔ ✔ ✔ Includes innovative, intelligence-driven technology for faster, fewer, shorter scans Norton™ Pulse Updates ✔ ✔ ✔ Delivers rapid pulse updates every 5 to 15 minutes for protection against new threats Smart, two-way firewall ✔ ✔ Makes intelligent incoming and outgoing security decisions without interrupting users to ask them each time Enhanced browser protection ✔ ✔ ✔ Secures against Web-based attacks that use browser vulnerabilities to infect PCs with malware Real-time behavioral protection ✔ ✔ ✔ Provides enhanced, real-time protection (SONAR™) Wireless network security protection ✔ ✔ Checks the status of wireless network security and provides expert advice on managing -
Norton™ Utilities Premium: User Manual
Norton™ Utilities Premium User Manual Norton Utilities Premium User Guide The software described in this book is furnished under a license agreement and may be used only in accordance with the terms of the agreement. Copyright © 2018 Symantec Corporation. All rights reserved. The product described in this document is distributed under licenses restricting its use, copying, distribution, and decompilation/reverse engineering. No part of this document may be reproduced in any form by any means without prior written authorization of Symantec Corporation and its licensors, if any. THE DOCUMENTATION IS PROVIDED "AS IS" AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. SYMANTEC CORPORATION SHALL NOT BE LIABLE FOR INCIDENTAL OR CONSEQUENTIAL DAMAGES IN CONNECTION WITH THE FURNISHING, PERFORMANCE, OR USE OF THIS DOCUMENTATION. THE INFORMATION CONTAINED IN THIS DOCUMENTATION IS SUBJECT TO CHANGE WITHOUT NOTICE. The Licensed Software and Documentation are deemed to be commercial computer software as defined in FAR 12.212 and subject to restricted rights as defined in FAR Section 52.227-19 "Commercial Computer Software - Restricted Rights" and DFARS 227.7202, et seq. "Commercial Computer Software and Commercial Computer Software Documentation," as applicable, and any successor regulations, whether delivered by Symantec as on premises or hosted services. Any use, modification, reproduction release, performance, display or disclosure of the Licensed Software and Documentation by the U.S. Government shall be solely in accordance with the terms of this Agreement. -

Essential Trends and Dynamics of the Endpoint Security Industry
Essential Trends and Dynamics of the Endpoint Security Industry Lenny Zeltser wrote this paper together with a co-author who chose to remain anonymous. May 2005 This paper examines trends and dynamics of the endpoint security industry, and shows how business strategies of market leaders such as Symantec exemplify these factors. When exploring current developments in the information security marketplace, we stipulate that this sector is beginning to converge with the general IT software industry in response to factors such as the evolution of the industry structure, competitive dynamics, regulatory compliance efforts, and the maturing state of security products. Lenny Zeltser & Co-Author Page 1 Table of Contents Introduction ......................................................................................................................... 2 Characteristics of the Endpoint Security Industry........................................................... 2 Scope of the Industry ............................................................................................................ 2 Industry Size Estimates.........................................................................................................3 Structural Characteristics of the Industry............................................................................... 3 Competitive Dynamics........................................................................................................... 4 Industry Evolution: From 1990 to 2005 ............................................................................ -

Graphicconverter 6.6
User’s Manual GraphicConverter 6.6 Programmed by Thorsten Lemke Manual by Hagen Henke Sales: Lemke Software GmbH PF 6034 D-31215 Peine Tel: +49-5171-72200 Fax:+49-5171-72201 E-mail: [email protected] In the PDF version of this manual, you can click the page numbers in the contents and index to jump to that particular page. © 2001-2009 Elbsand Publishers, Hagen Henke. All rights reserved. www.elbsand.de Sales: Lemke Software GmbH, PF 6034, D-31215 Peine www.lemkesoft.com This book including all parts is protected by copyright. It may not be reproduced in any form outside of copyright laws without permission from the author. This applies in parti- cular to photocopying, translation, copying onto microfilm and storage and processing on electronic systems. All due care was taken during the compilation of this book. However, errors cannot be completely ruled out. The author and distributors therefore accept no responsibility for any program or documentation errors or their consequences. This manual was written on a Mac using Adobe FrameMaker 6. Almost all software, hardware and other products or company names mentioned in this manual are registered trademarks and should be respected as such. The following list is not necessarily complete. Apple, the Apple logo, and Macintosh are trademarks of Apple Computer, Inc., registered in the United States and other countries. Mac and the Mac OS logo are trademarks of Apple Computer, Inc. Photo CD mark licensed from Kodak. Mercutio MDEF copyright Ramon M. Felciano 1992- 1998 Copyright for all pictures in manual and on cover: Hagen Henke except for page 95 exa- mple picture Tayfun Bayram and others from www.photocase.de; page 404 PCD example picture © AMUG Arizona Mac Users Group Inc. -

Antivirus – Internet Security Software
AntiVirus – Internet Security Software Recommended AntiVirus Software to use with OfficeEMR™: Norton AntiVirus Symantec Endpoint Protection Business Class – Enterprise – AntiVirus Solution AntiVirus ONLY software products WITHOUT additional Firewalls What Happens with Internet Security Software Products and OfficeEMR™: Provide an additional Firewall and/or Shields Can prevent you from accessing secure Web Sites such as https://www.officemd.net Scan every Web Page that you go to when it loads Can make screens in OfficeEMR™ take a long time to load Can prevent our AutoConfigure from running Can prevent scanning documents into OfficeEMR™ from completing What You Can Do: Setup our Web Site www.officemd.net as an exception in its Firewall. --- or --- Turn off (Disable) the additional Firewall included and / or applicable Shields Contact Technical Support via the software company’s Web Site o many offer e-mail, phone, and/or chat for technical support o get help with and options available to be able to access secure (https://...) Web --- or --- Sites o get help with and options available for making www.officemd.net an exception o get help with and options available for turning off their Firewall and / or applicable Shields. --- or --- Uninstall and Install the AntiVirus ONLY version of that software product. --- or --- Uninstall and Install a different AntiVirus ONLY software product. Revised 05/2009 AntiVirus – Internet Security Software More Detailed Information: Internet Security Software Products provide an added Firewall and / or Shields to help block malicious content or Web Sites while surfing on the Web. Without changing settings, by default, Internet Security Software Products will scan every Web Page that you go to when it loads. -

Verizon Wireless Mobile Office User Guides for Windowstm 95/98
Verizon Wireless Mobile Office User Guides For WindowsTM 95/98 To use Mobile Office for basic Internet access, do the following: Setting the Phone Up As a Modem 2 – 5 Setting Up a Mobile Office Quick 2 Netsm Connection 6 – 9 Using The Mobile Office Service 10 - 16 Related Support Documents: Setting Up Your Existing Dial Up Connections 17- 24 Setting Up AOL 4.0 / 5.0 (If you currently use AOL.) 25 - 32 Faxing With Your Digital Data Capable Phone 33 - 53 1 man.doc Setting the Phone Up as a Modem Step 1:(Optional) If you have a driver that was provided with your phone skip this step. If you do not have a driver you can use a standard driver included in Windows or we recommend using our driver. Download the Mobile Office Driver. Step 2: Go into control panel by clicking on Start, Settings, Control Panel Step 3: Select Modems Step 4: Click Add... 2 man.doc Step 5: Select "Other" then click Next. (If your PC does not support PC-Cards you will not get this screen.) Step 6: Check "Don't run the Hardware Installation wizard" if you get this dialog box. Then click on the Next button. Step 7: Check the box labeled "Don't detect my modem; I will select it from a list." Then click Next. 3 man.doc Step 8: If you have a driver provided by your phone manufacturer, click on the "Have Disk..." button. Insert your disk, click "OK" and then choose the model of phone that you have. -

Zerohack Zer0pwn Youranonnews Yevgeniy Anikin Yes Men
Zerohack Zer0Pwn YourAnonNews Yevgeniy Anikin Yes Men YamaTough Xtreme x-Leader xenu xen0nymous www.oem.com.mx www.nytimes.com/pages/world/asia/index.html www.informador.com.mx www.futuregov.asia www.cronica.com.mx www.asiapacificsecuritymagazine.com Worm Wolfy Withdrawal* WillyFoReal Wikileaks IRC 88.80.16.13/9999 IRC Channel WikiLeaks WiiSpellWhy whitekidney Wells Fargo weed WallRoad w0rmware Vulnerability Vladislav Khorokhorin Visa Inc. Virus Virgin Islands "Viewpointe Archive Services, LLC" Versability Verizon Venezuela Vegas Vatican City USB US Trust US Bankcorp Uruguay Uran0n unusedcrayon United Kingdom UnicormCr3w unfittoprint unelected.org UndisclosedAnon Ukraine UGNazi ua_musti_1905 U.S. Bankcorp TYLER Turkey trosec113 Trojan Horse Trojan Trivette TriCk Tribalzer0 Transnistria transaction Traitor traffic court Tradecraft Trade Secrets "Total System Services, Inc." Topiary Top Secret Tom Stracener TibitXimer Thumb Drive Thomson Reuters TheWikiBoat thepeoplescause the_infecti0n The Unknowns The UnderTaker The Syrian electronic army The Jokerhack Thailand ThaCosmo th3j35t3r testeux1 TEST Telecomix TehWongZ Teddy Bigglesworth TeaMp0isoN TeamHav0k Team Ghost Shell Team Digi7al tdl4 taxes TARP tango down Tampa Tammy Shapiro Taiwan Tabu T0x1c t0wN T.A.R.P. Syrian Electronic Army syndiv Symantec Corporation Switzerland Swingers Club SWIFT Sweden Swan SwaggSec Swagg Security "SunGard Data Systems, Inc." Stuxnet Stringer Streamroller Stole* Sterlok SteelAnne st0rm SQLi Spyware Spying Spydevilz Spy Camera Sposed Spook Spoofing Splendide -

Windows 7 Build 7000 Activation Cd Keys and Remove Watermark F Crack
Windows 7 Build 7000 Activation, Cd Keys And Remove Watermark, F Crack 1 / 5 Windows 7 Build 7000 Activation, Cd Keys And Remove Watermark, F Crack 2 / 5 3 / 5 ... .wixsite.com/gietemumpo/blog/hack-crack-internet-download-manager-6-26-build-3 ... %2f2018%2f10%2flicense-keys-for- windows-7-professional-activation.html ... .ru%2f97527362-Humax-hd-7000i-proshivka.html Humax_hd_7000i_proshivka, ... https://www.houzz.com/projects/5365543/skachaty-live-cd-windows-7-iso .... Windows 7 Activation with Original key (New Method) | NO Crack | No KMSAuto ! ! ! Hi! Welcome to Our .... ... 5 dollars a day 2008 dvdrip xvid qcf subtitle · activation crack xp sp3 7/2014 ... hp scanner for windows 7 driver officejet 7000 · transformers fall of cybertron .... 1 License Generator Windows 7 cadsoft eagle 5 7 0 linux license key-adds ... also include a crack, serial number, unlock code, cd key or keygen (key generator). ... KRPano pr10 latest activation key (crack) the sharing of KRPano pr10 latest ... but you may need a license to publish or remove watermark from your project.. 1 piano tutorial roland colorcamm pc 12 manual microsoft office object library 12.0 ... 2 plantsim hair mvp baseball 2005 crack only x-plore 1.34 unlock key perlovka ... microsoft office 2010 professional plus product activation crack skins original ... windows server 2012 r2 datacenter oder standard acdsee 7.0 build 102 serial .... Cd key crashday pc game · Parallels 7 keygen torrent ... Activation key for kaspersky 2012 free download crack ... Acronis disk director home v.11.0.2343 f ... Http cekc far ru cracks swiftshader 3 0 watermark removed ... Remove pdf security 4 0 serial .. -

Norton Utilities TM
Norton TM Norton Utilities Proof Utilities of Purchase Benutzerhandbuch Wir schützen weltweit mehr Benutzer vor Bedrohungen aus dem Internet als jedes andere Unternehmen. Umweltschutz ist wichtig. Symantec hat dieses Handbuch ohne Umschlag gestaltet, um die Einwirkung auf die Umwelt durch unsere Produkte zu reduzieren. TM Norton Utilities Benutzerhandbuch Die in diesem Handbuch beschriebene Software wird unter Lizenz vertrieben und darf nur entsprechend den Vertragsbedingungen verwendet werden. Dokumentationsversion 14.0 Copyright © 2009 Symantec Corporation. Alle Rechte vorbehalten. Symantec, das Symantec-Logo, Norton, Ghost, GoBack, LiveUpdate, Norton AntiSpam, Norton AntiVirus, Norton Internet Security, Norton 360 und Norton SystemWorks sind Marken oder eingetragene Marken der Symantec Corporation oder ihrer Tochtergesellschaften in den USA und anderen Ländern. Windows ist eine Marke der Microsoft Corporation. Andere Produktnamen können Marken der jeweiligen Rechteinhaber sein. Die in diesem Handbuch beschriebene Software wird Ihnen im Rahmen einer Lizenzvereinbarung zur Verfügung gestellt und darf nur unter den darin beschriebenen Bedingungen eingesetzt, kopiert, verteilt, dekompiliert und zurückentwickelt werden. Kein Teil dieser Veröffentlichung darf ohne ausdrückliche schriftliche Genehmigung der Symantec Corporation und ihrer Lizenzgeber vervielfältigt werden. DIE DOKUMENTATION WIRD "OHNE MÄNGELGEWÄHR" GELIEFERT. ALLE AUSDRÜCKLICHEN ODER STILLSCHWEIGENDEN BEDINGUNGEN, DARSTELLUNGEN UND GEWÄHRLEISTUNGEN EINSCHLIESSLICH DER STILLSCHWEIGENDEN -

Wsn, COURT STAFF) (Filed on 8/23/2013
Haskins v. Symantec Corporation Doc. 32 1 2 3 4 UNITED STATES DISTRICT COURT 5 NORTHERN DISTRICT OF CALIFORNIA 6 KATHLEEN HASKINS, 7 Case No. 13-cv-01834-JST Plaintiff, 8 v. ORDER GRANTING MOTION TO 9 DISMISS SYMANTEC CORPORATION, 10 ECF No. 22 Defendant. 11 12 13 Before the Court is Defendant Symantec Corporation’s (“Symantec”) Motion to Dismiss 14 Plaintiff’s First Amended Complaint (“Motion”). ECF No. 22. The Court has carefully 15 considered the papers filed in support of the motion and finds the matter appropriate for resolution 16 without oral argument. See Civil L.R. 7-1(b). The hearing scheduled for August 29, 2013 is 17 therefore VACATED. United States District United Court District States Northern District of California Northern California of District 18 I. BACKGROUND 19 A. Factual Background 20 The Court accepts the following allegations as true for the purpose of resolving 21 Defendant’s motion to dismiss. Cahill v. Liberty Mutual Ins. Co., 80 F.3d 336, 337–38 (9th Cir. 22 1996). 23 Symantec provides security, storage, and systems management to consumers, small 24 businesses, and large global organizations through its antivirus, data management utility and 25 enterprise software products. First Amended Complaint (“FAC”), ECF No. 17, ¶ 3. In 2006, 26 hackers infiltrated Symantec’s network and stole the source code for the 2006 versions of 27 pcAnywhere, Norton SystemWorks, Norton Antivirus Corporate Edition and Norton Internet 28 Dockets.Justia.com 1 Security (which Plaintiff identifies in the FAC the “Compromised Symantec Products”1). Id. ¶ 18. 2 The stolen Symantec source code includes instructions written in various computer programming 3 languages, and comments made by engineers to explain the design of the software. -

Resolution No. 7570 City of South Gate Los Angeles
RESOLUTION NO. 7570 CITY OF SOUTH GATE LOS ANGELES COUNTY, CALIFORNIA A RESOLUTION OF THE CITY COUNCIL OF THE CITY OF SOUTH GATE AUTHORIZING THE DESTRUCTION OF OBSOLETE RECORDS FROM THE CITY CLERK'S OFFICE, FINANCE DEPARTMENT, POLICE DEPARTMENT FILES PURSUANT TO GOVERNMENT CODE 34090 OF THE LAWS OF THE STATE OF CALIFORNIA WHEREAS, it has been determined that certain City records under the charge of certain City Clerk's Office are no longer required for public or private purposes; and WHEREAS, it has been determined that destruction of the above-mentioned records is necessary to conserve storage space and to reduce staff time and expense in handling records and informing the public; WHEREAS, Section 34090 of the Government Code of the State of California authorizes the head of a City department to destroy any City records and documents which are over two years old under his or her charge, without making a copy thereof, after the same are no longer required, with the written consent of the City Attorney and the approval of the City Council by resolution; and WHEREAS, it is therefore desirable to destroy those records which are over two years old as listed in the documents entitled "Records Inventory," dated October 22, 2013, attached hereto as Exhibit "A," and made a part hereof, without making a copy thereof; and WHEREAS, the said destruction of said records is with the written consent of the City Attorney; NOW, THEREFORE, THE CITY COUNCIL OF THE CITY OF SOUTH GATE DOES HEREBY RESOLVE AS FOLLOWS: SECTION 1. The City Council hereby authorizes the destruction of the documents identified in Exhibit "A" attached hereto and incorporated herein by this reference. -
Fax Sharing User's Guide
Fax Sharing User’s Guide February 2000 WinFax PRO Fax Sharing User’s Guide Copyright Notice © Symantec Corporation 2000 All rights reserved. The use and copying of this product is subject to a license agreement. Any other use is prohibited. No part of this publication may be reproduced, transmitted, transcribed, stored in a retrieval system or translated into any language in any form by any means without the prior written consent of Symantec Corporation. Information in this manual is subject to change without notice and does not represent a commitment on the part of the vendor. Federal copyright law permits you to make a backup of this software for archival purposes only. Any other duplication of this software, including copies offered through sale, loan, rental or gift is a violation of law, and subject to both criminal and civil penalties. Notice to WinFax PRO Users It shall be unlawful for any person within the United States to use any computer or other electronic device to send any message via a facsimile machine unless such message clearly contains, in a margin at the top or bottom of each transmitted page or on the first page of the transmission, the date and time it is sent and an identification of the business, other entity or individual sending the message and the telephone number of the sending machine or such business, other entity, or individual. Trademarks Symantec, the Symantec logo, TalkWorks PRO, Cover Your Voice, WinFax PRO, Cover Your Fax, and pcANYWHERE are trademarks of Symantec Corporation and its subsidiaries. AOL is a registered trademark of America Online, Inc.