FS-TST) Is a Software Package That Supports the Testing of Disk Imaging Tools
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-
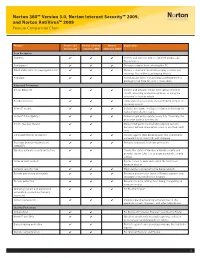
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton Antivirus™ 2009 Feature Comparison Chart
Norton 360™ Version 3.0, Norton Internet Security™ 2009, and Norton AntiVirus™ 2009 Feature Comparison Chart Feature Norton 360 Norton Internet Norton Explanation Version 3.0 Security 2009 AntiVirus 2009 Core Protection Antivirus ✔ ✔ ✔ Detects and removes viruses, Internet worms, and Trojan horses Antispyware ✔ ✔ ✔ Prevents spyware from infecting the PC Email and instant messaging protection ✔ ✔ ✔ Monitors email and instant messaging so users can exchange files without exchanging threats Antispam ✔ ✔ Automatically filters out annoying and fraudulent or phishing email from the user’s email inbox Advanced Protection Botnet detection ✔ ✔ ✔ Detects and prevents others from taking control of the PC, accessing private information, or using the computer to host an attack Rootkit detection ✔ ✔ ✔ Finds and removes threats that are hidden deep in the operating system Norton™ Insight ✔ ✔ ✔ Includes innovative, intelligence-driven technology for faster, fewer, shorter scans Norton™ Pulse Updates ✔ ✔ ✔ Delivers rapid pulse updates every 5 to 15 minutes for protection against new threats Smart, two-way firewall ✔ ✔ Makes intelligent incoming and outgoing security decisions without interrupting users to ask them each time Enhanced browser protection ✔ ✔ ✔ Secures against Web-based attacks that use browser vulnerabilities to infect PCs with malware Real-time behavioral protection ✔ ✔ ✔ Provides enhanced, real-time protection (SONAR™) Wireless network security protection ✔ ✔ Checks the status of wireless network security and provides expert advice on managing -
Norton™ Utilities Premium: User Manual
Norton™ Utilities Premium User Manual Norton Utilities Premium User Guide The software described in this book is furnished under a license agreement and may be used only in accordance with the terms of the agreement. Copyright © 2018 Symantec Corporation. All rights reserved. The product described in this document is distributed under licenses restricting its use, copying, distribution, and decompilation/reverse engineering. No part of this document may be reproduced in any form by any means without prior written authorization of Symantec Corporation and its licensors, if any. THE DOCUMENTATION IS PROVIDED "AS IS" AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. SYMANTEC CORPORATION SHALL NOT BE LIABLE FOR INCIDENTAL OR CONSEQUENTIAL DAMAGES IN CONNECTION WITH THE FURNISHING, PERFORMANCE, OR USE OF THIS DOCUMENTATION. THE INFORMATION CONTAINED IN THIS DOCUMENTATION IS SUBJECT TO CHANGE WITHOUT NOTICE. The Licensed Software and Documentation are deemed to be commercial computer software as defined in FAR 12.212 and subject to restricted rights as defined in FAR Section 52.227-19 "Commercial Computer Software - Restricted Rights" and DFARS 227.7202, et seq. "Commercial Computer Software and Commercial Computer Software Documentation," as applicable, and any successor regulations, whether delivered by Symantec as on premises or hosted services. Any use, modification, reproduction release, performance, display or disclosure of the Licensed Software and Documentation by the U.S. Government shall be solely in accordance with the terms of this Agreement. -

Antivirus – Internet Security Software
AntiVirus – Internet Security Software Recommended AntiVirus Software to use with OfficeEMR™: Norton AntiVirus Symantec Endpoint Protection Business Class – Enterprise – AntiVirus Solution AntiVirus ONLY software products WITHOUT additional Firewalls What Happens with Internet Security Software Products and OfficeEMR™: Provide an additional Firewall and/or Shields Can prevent you from accessing secure Web Sites such as https://www.officemd.net Scan every Web Page that you go to when it loads Can make screens in OfficeEMR™ take a long time to load Can prevent our AutoConfigure from running Can prevent scanning documents into OfficeEMR™ from completing What You Can Do: Setup our Web Site www.officemd.net as an exception in its Firewall. --- or --- Turn off (Disable) the additional Firewall included and / or applicable Shields Contact Technical Support via the software company’s Web Site o many offer e-mail, phone, and/or chat for technical support o get help with and options available to be able to access secure (https://...) Web --- or --- Sites o get help with and options available for making www.officemd.net an exception o get help with and options available for turning off their Firewall and / or applicable Shields. --- or --- Uninstall and Install the AntiVirus ONLY version of that software product. --- or --- Uninstall and Install a different AntiVirus ONLY software product. Revised 05/2009 AntiVirus – Internet Security Software More Detailed Information: Internet Security Software Products provide an added Firewall and / or Shields to help block malicious content or Web Sites while surfing on the Web. Without changing settings, by default, Internet Security Software Products will scan every Web Page that you go to when it loads. -

A Glance Into the Eye Pyramid Technical Article V2
A glance into the Eye Pyramid RĂZVAN OLTEANU Security Reasercher We keep you safe and we keep it simple. 01 Introduction On January 11, 2017 Italian news agency AGI, published a court order regarding cyber-attacks against high ranking Italian government members and Italian institutions. The attacks were conducted by two Italian brothers to get financial information that would help them gain an advantage when trading on financial markets. Overview The campaign was carried out over several years starting in 2008 and continuing into 2010, 2011, 2012 and 2014. The mechanism the brothers used to distribute their malware was simple; targeted spear-phishing emails aimed at victims who had already been selected. The emails con- tained a malware attachment, which once opened harvested information from the victims’ computers. This information consisted of pictures, documents, archives, presenta- tions, email contacts, email bodies, usernames, passwords, keystrokes, web pages content and databases. Technical details The malware was written in VisualBasic.net and was obfuscated twice using common obfuscators: Dotfuscator and Skater .NET which can be easily reversed. The malware stored its sensitive data – license keys, URLs and paths – by encrypting with the Triple DES algorithm using the MD5 of a provided password as key and SHA256 of the pass- word as initialization vector. A glance into the Eye Pyramid 01 02 Figure 1 Security applications To remain unnoticed, it tried to disable any security application installed on the victim’s computer. Targeted -

Aluria Security Center Avira Antivir Personaledition Classic 7
Aluria Security Center Avira AntiVir PersonalEdition Classic 7 - 8 Avira AntiVir Personal Free Antivirus ArcaVir Antivir/Internet Security 09.03.3201.9 x64 Ashampoo FireWall Ashampoo FireWall PRO 1.14 ALWIL Software Avast 4.0 Grisoft AVG 7.x Grisoft AVG 6.x Grisoft AVG 8.x Grisoft AVG 8.x x64 Avira Premium Security Suite 2006 Avira WebProtector 2.02 Avira AntiVir Personal - Free Antivirus 8.02 Avira AntiVir PersonalEdition Premium 7.06 AntiVir Windows Workstation 7.06.00.507 Kaspersky AntiViral Toolkit Pro BitDefender Free Edition BitDefender Internet Security BullGuard BullGuard AntiVirus BullGuard AntiVirus x64 CA eTrust AntiVirus 7 CA eTrust AntiVirus 7.1.0192 eTrust AntiVirus 7.1.194 CA eTrust AntiVirus 7.1 CA eTrust Suite Personal 2008 CA Licensing 1.57.1 CA Personal Firewall 9.1.0.26 CA Personal Firewall 2008 CA eTrust InoculateIT 6.0 ClamWin Antivirus ClamWin Antivirus x64 Comodo AntiSpam 2.6 Comodo AntiSpam 2.6 x64 COMODO AntiVirus 1.1 Comodo BOClean 4.25 COMODO Firewall Pro 1.0 - 3.x Comodo Internet Security 3.8.64739.471 Comodo Internet Security 3.8.64739.471 x64 Comodo Safe Surf 1.0.0.7 Comodo Safe Surf 1.0.0.7 x64 DrVirus 3.0 DrWeb for Windows 4.30 DrWeb Antivirus for Windows 4.30 Dr.Web AntiVirus 5 Dr.Web AntiVirus 5.0.0 EarthLink Protection Center PeoplePC Internet Security 1.5 PeoplePC Internet Security Pack / EarthLink Protection Center ESET NOD32 file on-access scanner ESET Smart Security 3.0 eTrust EZ Firewall 6.1.7.0 eTrust Personal Firewall 5.5.114 CA eTrust PestPatrol Anti-Spyware Corporate Edition CA eTrust PestPatrol -

Norton Antivirus Product Manual
NortonTM AntiVirus Product Manual Care for our Environment; ‘It's the right thing to do.’ Symantec has removed the cover from this manual to reduce the Environmental Footprint of our products. This manual is made from recycled materials. Norton AntiVirus™ Product Manual The software described in this book is furnished under a license agreement and may be used only in accordance with the terms of the agreement. Documentation version 21.4 Copyright © 2014 Symantec Corporation. All rights reserved. Symantec, the Symantec Logo, LiveUpdate, Norton 360, and Norton are trademarks or registered trademarks of Symantec Corporation or its affiliates in the U.S. and other countries. Portions of this product Copyright 1996-2011 Glyph & Cog, LLC. Other names may be trademarks of their respective owners. The product described in this document is distributed under licenses restricting its use, copying, distribution, and decompilation/reverse engineering. No part of this document may be reproduced in any form by any means without prior written authorization of Symantec Corporation and its licensors, if any. THE DOCUMENTATION IS PROVIDED “AS IS” AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. SYMANTEC CORPORATION SHALL NOT BE LIABLE FOR INCIDENTAL OR CONSEQUENTIAL DAMAGES IN CONNECTION WITH THE FURNISHING, PERFORMANCE, OR USE OF THIS DOCUMENTATION. THE INFORMATION CONTAINED IN THIS DOCUMENTATION IS SUBJECT TO CHANGE WITHOUT NOTICE. The Licensed Software and Documentation are deemed to be commercial computer software as defined in FAR 12.212 and subject to restricted rights as defined in FAR Section 52.227-19 "Commercial Computer Software - Restricted Rights" and DFARS 227.7202, et seq. -

Features of Norton Mobile Security
Norton Mobile Security User Guide DOWNLOAD AND INSTALL NORTON MOBILE SECURITY .................................................................. 1 ACTIVATE NORTON MOBILE SECURITY............................................................................................ 4 FEATURES OF NORTON MOBILE SECURITY ...................................................................................... 5 KEY FEATURES FOR IPHONES OR IPADS .......................................................................................... 7 SYSTEM REQUIREMENTS FOR NORTON MOBILE SECURITY ............................................................. 7 Download and install Norton Mobile Security You can directly download and install Norton Mobile Security on your mobile devices, or you can send an email with download instructions and access it on your mobile device. Select the device you are installing from: I am on a computEr and want to sEnd instructions to install Norton MobilE SEcurity to my devicE 1. Sign In to Norton. 2. If you are not signed in to Norton already, you are prompted to sign in. Type in your email address and password for Norton, and click Sign In. If you do not have a Norton account, click Create account, and complete the sign-up process. 3. In the Norton Setup window, move your mouse over Download Norton, and then click Send a Download Link. 4. Type an email address you can access on your device, and click the send icon . An email is sent to the email address with instructions to install the Norton product. Click DonE. 1 5. On the device where you want to install Norton, find and open the email that you received from "The Norton Team", and tap Download Now. The download link opens the Norton Setup page in your browser. 6. In the Norton Setup window, tap Download Now or Install. 7. You are redirected to the Norton Security and Antivirus page on the Google Play Store or App Store. -

2005 Annual Report
SYMANTEC 2005 ANNUAL REPORT BE FEARLESS LEAD THREE YEAR SUMMARY Fiscal Year Ended (in millions, except per share amounts) 2005 2004 2003 Reconciliation of Non-GAAP to GAAP Results*: Revenues $ 2,583 $ 1,870 $ 1,407 Non-GAAP Gross Margin $ 2,180 $ 1,584 $ 1,186 Cost of revenues: amortization of acquired product rights $ (49) $ (41) $ (29) GAAP Gross Margin $ 2,131 $ 1,543 $ 1,157 Non-GAAP Operating Expenses $ 1,292 $ 1,007 $ 796 Amortization of other intangibles from acquisitions $ 5 $ 3 $ 3 Amortization of deferred stock-based compensation $ 5 – – Acquired in-process research and development $ 3 $ 4 $ 5 Restructuring $ 3 $ 1 $ 11 Patent settlement – $ 14 – Integration costs $ 3 – – GAAP Operating Expenses $ 1,311 $ 1,029 $ 815 Non-GAAP Net Income $ 634 $ 411 $ 280 Cost of revenues $ (49) $ (41) $ (29) Operating expenses $ (20) $ (21) $ (19) Income tax benefit $ 25 $ 22 $ 16 Tax charge on cash repatriation $ (54) – – GAAP Net Income $ 536 $ 371 $ 248 GAAP Net Income per Share – Diluted $ 0.74 $ 0.54 $ 0.38 Non-GAAP Net Income per Share – Diluted $ 0.87 $ 0.59 $ 0.43 Other Information: Cash Flow from Operating Activities $ 1,207 $ 903 $ 599 Total Assets $ 5,614 $ 4,456 $ 3,266 Stockholders’ Equity $ 3,705 $ 2,426 $ 1,764 Total Employees 6,395 5,300 4,344 *In addition to reporting financial results in accordance with generally accepted accounting principles, or GAAP, Symantec reports non-GAAP financial results. Non-GAAP net income per share exclude amortization of acquisition-related intangibles, amortization of deferred stock-based compensation, in-process research and development, and certain other identified charges, such as restructuring, patent settlement, and integration planning expenses associated with the VERITAS merger, as well as the tax ef- fect of these items, and the one-time tax effect associated with the company’s cash repatriation under the American Jobs Creation Act. -

Norton Utilities TM
Norton TM Norton Utilities Proof Utilities of Purchase Benutzerhandbuch Wir schützen weltweit mehr Benutzer vor Bedrohungen aus dem Internet als jedes andere Unternehmen. Umweltschutz ist wichtig. Symantec hat dieses Handbuch ohne Umschlag gestaltet, um die Einwirkung auf die Umwelt durch unsere Produkte zu reduzieren. TM Norton Utilities Benutzerhandbuch Die in diesem Handbuch beschriebene Software wird unter Lizenz vertrieben und darf nur entsprechend den Vertragsbedingungen verwendet werden. Dokumentationsversion 14.0 Copyright © 2009 Symantec Corporation. Alle Rechte vorbehalten. Symantec, das Symantec-Logo, Norton, Ghost, GoBack, LiveUpdate, Norton AntiSpam, Norton AntiVirus, Norton Internet Security, Norton 360 und Norton SystemWorks sind Marken oder eingetragene Marken der Symantec Corporation oder ihrer Tochtergesellschaften in den USA und anderen Ländern. Windows ist eine Marke der Microsoft Corporation. Andere Produktnamen können Marken der jeweiligen Rechteinhaber sein. Die in diesem Handbuch beschriebene Software wird Ihnen im Rahmen einer Lizenzvereinbarung zur Verfügung gestellt und darf nur unter den darin beschriebenen Bedingungen eingesetzt, kopiert, verteilt, dekompiliert und zurückentwickelt werden. Kein Teil dieser Veröffentlichung darf ohne ausdrückliche schriftliche Genehmigung der Symantec Corporation und ihrer Lizenzgeber vervielfältigt werden. DIE DOKUMENTATION WIRD "OHNE MÄNGELGEWÄHR" GELIEFERT. ALLE AUSDRÜCKLICHEN ODER STILLSCHWEIGENDEN BEDINGUNGEN, DARSTELLUNGEN UND GEWÄHRLEISTUNGEN EINSCHLIESSLICH DER STILLSCHWEIGENDEN -
Norton-360.Pdf
Norton™ 360 Product Manual Norton™ 360 Product Manual The software described in this book is furnished under a license agreement and may be used only in accordance with the terms of the agreement. Documentation version 22.21.3 Copyright © 2021 NortonLifeLock Inc. All rights reserved. NortonLifeLock, the NortonLifeLock Logo, the Checkmark Logo, Norton, Norton Secured Logo, LifeLock, and the LockMan Logo are trademarks or registered trademarks of NortonLifeLock Inc. or its affiliates in the U. S. and other countries. Other names may be trademarks of their respective owners. The product described in this document is distributed under licenses restricting its use, copying, distribution, and decompilation/reverse engineering. No part of this document may be reproduced in any form by any means without prior written authorization of NortonLifeLock Inc. and its licensors, if any. THE DOCUMENTATION IS PROVIDED "AS IS" AND ALL EXPRESS OR IMPLIED CONDITIONS, REPRESENTATIONS AND WARRANTIES, INCLUDING ANY IMPLIED WARRANTY OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE OR NON-INFRINGEMENT, ARE DISCLAIMED, EXCEPT TO THE EXTENT THAT SUCH DISCLAIMERS ARE HELD TO BE LEGALLY INVALID. NORTONLIFELOCK INC. SHALL NOT BE LIABLE FOR INCIDENTAL OR CONSEQUENTIAL DAMAGES IN CONNECTION WITH THE FURNISHING, PERFORMANCE, OR USE OF THIS DOCUMENTATION. THE INFORMATION CONTAINED IN THIS DOCUMENTATION IS SUBJECT TO CHANGE WITHOUT NOTICE. The Licensed Software and Documentation are deemed to be commercial computer software as defined in FAR 12.212 and subject to restricted rights as defined in FAR Section 52.227-19 "Commercial Computer Software - Restricted Rights" and DFARS 227.7202, et seq. "Commercial Computer Software and Commercial Computer Software Documentation," as applicable, and any successor regulations, whether delivered by NortonLifeLock as on premises or hosted services. -

Norton 360 for Gamers Game Optimization Testing Windows 10
Norton 360 for Gamers Game Optimization Testing Windows 10 June 2021 Document: Norton 360 for Gamers Game Optimization Testing (Edition 1) Authors: J. Han, D. Wren Company: PassMark Software Date: 22 June 2021 Edition: 1 File: Norton_Game_Optimization_Testing_2021_Ed1.docx Norton 360 for Gamers Game Optimization Testing PassMark Software Table of Contents REVISION HISTORY ............................................................................................................................................ 3 EXECUTIVE SUMMARY ...................................................................................................................................... 4 OVERALL SCORE ................................................................................................................................................ 5 PRODUCTS LIST ................................................................................................................................................. 6 TEST RESULTS.................................................................................................................................................... 7 PHASE 1 ......................................................................................................................................................... 7 PHASE 2 ....................................................................................................................................................... 15 CONCLUSION ................................................................................................................................................. -

Product Support Bulletin
Product Support Bulletin Subject: Apex Plus Hardware and Software Compatibility Lists Date: 4/19/89 PSB No: S-007 Page: 1 of 8 Originator: REM The purpose of this bulletin is to provide a current listing of tested hardware and software for the Apex Plus. All testing was performed by Seiko Epson Japan and the results were supplied to Epson America. This is not an all - inclusive list; there are many hardware options and applications that will work correctly that are not listed. Unless otherwise noted, all tests were conducted with the latest release of the Apex Plus MS - DOS operating system software and ROM BIOS. The products tested were certified in one of three ways: OK - Product works with full functionality NG - Product does not work - see compatibility note * Product works with partial functionality - see compatibility note The information provided does not constitute a guarantee or endorsement of any particular product or any specific use or application. Some of the products on the list may have software or hardware requirements which are not met by the Apex Plus personal computer. Therefore, while EPSON believes the information supplied is accurate, EPSON does not assume any responsibility for use of any of the products on the attached list. EPSON MAKES NO REPRESENTATIONS OR WARRANTIES, EITHER EXPRESS OR’ IMPLIED, WITH RESPECT TO THIS LISTING OR THE PRODUCTS REFERENCED IN THE LIST. EPSON SHALL NOT BE LIABLE FOR ANY LOSS, INCONVENIENCE OR DAMAGE, INCLUDING DIRECT, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES, RESULTING FROM THE USE OR INABILITY TO USE ANY OF THE PRODUCTS LISTED.