Caesar Ciphers
Total Page:16
File Type:pdf, Size:1020Kb
Load more
Recommended publications
-

IMPLEMENTASI ALGORITMA CAESAR, CIPHER DISK, DAN SCYTALE PADA APLIKASI ENKRIPSI DAN DEKRIPSI PESAN SINGKAT, Lumasms
Prosiding Seminar Ilmiah Nasional Komputer dan Sistem Intelijen (KOMMIT 2014) Vol. 8 Oktober 2014 Universitas Gunadarma – Depok – 14 – 15 Oktober 2014 ISSN : 2302-3740 IMPLEMENTASI ALGORITMA CAESAR, CIPHER DISK, DAN SCYTALE PADA APLIKASI ENKRIPSI DAN DEKRIPSI PESAN SINGKAT, LumaSMS Yusuf Triyuswoyo ST. 1 Ferina Ferdianti ST. 2 Donny Ajie Baskoro ST. 3 Lia Ambarwati ST. 4 Septiawan ST. 5 1,2,3,4,5Jurusan Manajemen Sistem Informasi, Universitas Gunadarma [email protected] Abstrak Short Message Service (SMS) merupakan salah satu cara berkomunikasi yang banyak digunakan oleh pengguna telepon seluler. Namun banyaknya pengguna telepon seluler yang menggunakan layanan SMS, tidak diimbangi dengan faktor keamanan yang ada pada layanan tersebut. Banyak pengguna telepon seluler yang belum menyadari bahwa SMS tidak menjamin integritas dan keamanan pesan yang disampaikan. Ada beberapa risiko yang dapat mengancam keamanan pesan pada layanan SMS, diantaranya: SMS spoofing, SMS snooping, dan SMS interception. Untuk mengurangi risiko tersebut, maka dibutuhkan sebuah sistem keamanan pada layanan SMS yang mampu menjaga integritas dan keamanan isi pesan. Dimana tujuannya ialah untuk menutupi celah pada tingkat keamanan SMS. Salah satu penanggulangannya ialah dengan menerapkan algoritma kriptografi, yaitu kombinasi atas algoritma Cipher Disk, Caesar, dan Scytale pada pesan yang akan dikirim. Tujuan dari penulisan ini adalah membangun aplikasi LumaSMS, dengan menggunakan kombinasi ketiga algoritma kriptografi tersebut. Dengan adanya aplikasi ini diharapkan mampu mengurangi masalah keamanan dan integritas SMS. Kata Kunci: caesar, cipher disk, kriptografi, scytale, SMS. PENDAHULUAN dibutuhkan dikarenakan SMS mudah digunakan dan biaya yang dikeluarkan Telepon seluler merupakan salah untuk mengirim SMS relatif murah. satu hasil dari perkembangan teknologi Namun banyaknya pengguna komunikasi. -
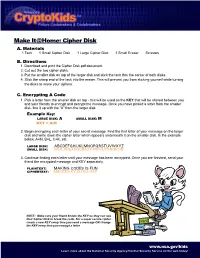
Cipher Disk A
Make It@Home: Cipher Disk A. Materials 1 Tack 1 Small Cipher Disk 1 Large Cipher Disk 1 Small Eraser Scissors B. Directions 1. Download and print the Cipher Disk.pdf document. 2. Cut out the two cipher disks. 3. Put the smaller disk on top of the larger disk and stick the tack thru the center of both disks. 4. Stick the sharp end of the tack into the eraser. This will prevent you from sticking yourself while turning the disks to make your ciphers. C. Encrypting A Code 1. Pick a letter from the smaller disk on top - this will be used as the KEY that will be shared between you and your friends to encrypt and decrypt the message. Once you have picked a letter from the smaller disk, line it up with the “A” from the larger disk. Example Key: LARGE DISK: A SMALL DISK: M KEY = A:M 2. Begin encrypting each letter of your secret message. Find the first letter of your message on the larger disk and write down the cipher letter which appears underneath it on the smaller disk. In the example below, A=M, B=L, C=K, etc. LARGE DISK: ABCDEFGHIJKLMNOPQRSTUVWXYZ SMALL DISK: MLKJIHGFEDCBAZYXWVUTSRQPON 3. Continue finding each letter until your message has been encrypted. Once you are finished, send your friend the encrypted message and KEY seperately. PLAINTEXT: MAKING CODES IS FUN CIPHERTEXT: AMCEZG KYJIU EU HSZ NOTE: Make sure your friend knows the KEY so they can use their Cipher Disk to break the code. For a super secure cipher, create a new KEY every time you send a message OR change the KEY every time you encrypt a letter. -
Cryptology: an Historical Introduction DRAFT
Cryptology: An Historical Introduction DRAFT Jim Sauerberg February 5, 2013 2 Copyright 2013 All rights reserved Jim Sauerberg Saint Mary's College Contents List of Figures 8 1 Caesar Ciphers 9 1.1 Saint Cyr Slide . 12 1.2 Running Down the Alphabet . 14 1.3 Frequency Analysis . 15 1.4 Linquist's Method . 20 1.5 Summary . 22 1.6 Topics and Techniques . 22 1.7 Exercises . 23 2 Cryptologic Terms 29 3 The Introduction of Numbers 31 3.1 The Remainder Operator . 33 3.2 Modular Arithmetic . 38 3.3 Decimation Ciphers . 40 3.4 Deciphering Decimation Ciphers . 42 3.5 Multiplication vs. Addition . 44 3.6 Koblitz's Kid-RSA and Public Key Codes . 44 3.7 Summary . 48 3.8 Topics and Techniques . 48 3.9 Exercises . 49 4 The Euclidean Algorithm 55 4.1 Linear Ciphers . 55 4.2 GCD's and the Euclidean Algorithm . 56 4.3 Multiplicative Inverses . 59 4.4 Deciphering Decimation and Linear Ciphers . 63 4.5 Breaking Decimation and Linear Ciphers . 65 4.6 Summary . 67 4.7 Topics and Techniques . 67 4.8 Exercises . 68 3 4 CONTENTS 5 Monoalphabetic Ciphers 71 5.1 Keyword Ciphers . 72 5.2 Keyword Mixed Ciphers . 73 5.3 Keyword Transposed Ciphers . 74 5.4 Interrupted Keyword Ciphers . 75 5.5 Frequency Counts and Exhaustion . 76 5.6 Basic Letter Characteristics . 77 5.7 Aristocrats . 78 5.8 Summary . 80 5.9 Topics and Techniques . 81 5.10 Exercises . 81 6 Decrypting Monoalphabetic Ciphers 89 6.1 Letter Interactions . 90 6.2 Decrypting Monoalphabetic Ciphers . -

SIS and Cipher Machines: 1930 – 1940
SIS and Cipher Machines: 1930 – 1940 John F Dooley Knox College Presented at the 14th Biennial NSA CCH History Symposium, October 2013 This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 3.0 United States License. 1 Thursday, November 7, 2013 1 The Results of Friedman’s Training • The initial training regimen as it related to cipher machines was cryptanalytic • But this detailed analysis of the different machine types informed the team’s cryptographic imaginations when it came to creating their own machines 2 Thursday, November 7, 2013 2 The Machines • Wheatstone/Plett Machine • M-94 • AT&T machine • M-138 and M-138-A • Hebern cipher machine • M-209 • Kryha • Red • IT&T (Parker Hitt) • Purple • Engima • SIGABA (M-134 and M-134-C) • B-211(and B-21) 3 Thursday, November 7, 2013 3 The Wheatstone/Plett Machine • polyalphabetic cipher disk with gearing mechanism rotates the inner alphabet. • Plett’s improvement is to add a second key and mixed alphabet to the inner ring. • Friedman broke this in 1918 Principles: (a) The inner workings of a mechanical cryptographic device can be worked out using a paper and pencil analog of the device. (b) if there is a cycle in the mechanical device (say for particular cipher alphabets), then that cycle can be discovered by analysis of the paper and pencil analog. 4 Thursday, November 7, 2013 4 The Army M-94 • Traces its roots back to Jefferson and Bazieres • Used by US Army from 1922 to circa 1942 • 25 mixed alphabets. Disk order is the key. -
Cryptography and Data Security
Calhoun: The NPS Institutional Archive Faculty and Researcher Publications Faculty and Researcher Publications 1982-05 Cryptography and Data Security Denning, Dorothy E. þÿDenning, D. E., Cryptography and Data Security, Addison Wesley, May 1982. http://hdl.handle.net/10945/37163 Cryptography and 13ata Security Dorothy Elizabeth Rob,ling Denning PURDUE UNIVERSITY A VV ADDISON-WESLEY PUBLISHING COMPANY Reading, Massachusetts [] Menlo Park, California London II Amsterdam • Don Mills, Ontario I Sydney Library of Congress Cataloging in Publication Data Denning, Dorothy E., (Dorothy Elizabeth), 1945- Cryptography and data security. Includes bibliographical references and index. 1. Computers--Access control. 2. Cryptography. 3. Data protection. 1. Title. QA76.9.A25D46 1982 001.64'028'9 81-15012 ISBN 0-201-10150-5 AACR2 Copyright © 1982 by Addison-Wesley Publishing Company, Inc. All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, electronic, mechanical, photocopying, recording, or other- wise, without the prior written permission of the publisher. Printed in the United States of America. Published simultaneously in Canada. ISBN 0-201-10150-5 A BCDE FG H I J-M A-898765432 In memory of my Father, Cornelius Lowell Robling 1910-1965 Preface Electronic computers have evolved from exiguous experimental enterprises in the 1940s to prolific practical data processing systems in the 1980s. As we have come to rely on these systems to process and store data, we have also come to wonder about their ability to protect valuable data. Data security is the science and study of methods of protecting data in computer and communication systems from unauthorized disclosure and modifica- tion. -

A Complete Bibliography of Publications in Cryptologia
A Complete Bibliography of Publications in Cryptologia Nelson H. F. Beebe University of Utah Department of Mathematics, 110 LCB 155 S 1400 E RM 233 Salt Lake City, UT 84112-0090 USA Tel: +1 801 581 5254 FAX: +1 801 581 4148 E-mail: [email protected], [email protected], [email protected] (Internet) WWW URL: http://www.math.utah.edu/~beebe/ 04 September 2021 Version 3.64 Title word cross-reference 10016-8810 [?, ?]. 1221 [?]. 125 [?]. 15.00/$23.60.0 [?]. 15th [?, ?]. 16th [?]. 17-18 [?]. 18 [?]. 180-4 [?]. 1812 [?]. 18th (t; m)[?]. (t; n)[?, ?]. $10.00 [?]. $12.00 [?, ?, ?, ?, ?]. 18th-Century [?]. 1930s [?]. [?]. 128 [?]. $139.99 [?]. $15.00 [?]. $16.95 1939 [?]. 1940 [?, ?]. 1940s [?]. 1941 [?]. [?]. $16.96 [?]. $18.95 [?]. $24.00 [?]. 1942 [?]. 1943 [?]. 1945 [?, ?, ?, ?, ?]. $24.00/$34 [?]. $24.95 [?, ?]. $26.95 [?]. 1946 [?, ?]. 1950s [?]. 1970s [?]. 1980s [?]. $29.95 [?]. $30.95 [?]. $39 [?]. $43.39 [?]. 1989 [?]. 19th [?, ?]. $45.00 [?]. $5.95 [?]. $54.00 [?]. $54.95 [?]. $54.99 [?]. $6.50 [?]. $6.95 [?]. $69.00 2 [?, ?]. 200/220 [?]. 2000 [?]. 2004 [?, ?]. [?]. $69.95 [?]. $75.00 [?]. $89.95 [?]. th 2008 [?]. 2009 [?]. 2011 [?]. 2013 [?, ?]. [?]. A [?]. A3 [?, ?]. χ [?]. H [?]. k [?, ?]. M 2014 [?]. 2017 [?]. 2019 [?]. 20755-6886 [?, ?]. M 3 [?]. n [?, ?, ?]. [?]. 209 [?, ?, ?, ?, ?, ?]. 20th [?]. 21 [?]. 22 [?]. 220 [?]. 24-Hour [?, ?, ?]. 25 [?, ?]. -Bit [?]. -out-of- [?, ?]. -tests [?]. 25.00/$39.30 [?]. 25.00/839.30 [?]. 25A1 [?]. 25B [?]. 26 [?, ?]. 28147 [?]. 28147-89 000 [?]. 01Q [?, ?]. [?]. 285 [?]. 294 [?]. 2in [?, ?]. 2nd [?, ?, ?, ?]. 1 [?, ?, ?, ?]. 1-4398-1763-4 [?]. 1/2in [?, ?]. 10 [?]. 100 [?]. 10011-4211 [?]. 3 [?, ?, ?, ?]. 3/4in [?, ?]. 30 [?]. 310 1 2 [?, ?, ?, ?, ?, ?, ?]. 312 [?]. 325 [?]. 3336 [?, ?, ?, ?, ?, ?]. affine [?]. [?]. 35 [?]. 36 [?]. 3rd [?]. Afluisterstation [?, ?]. After [?]. Aftermath [?]. Again [?, ?]. Against 4 [?]. 40 [?]. 44 [?]. 45 [?]. 45th [?]. 47 [?]. [?, ?, ?, ?, ?, ?, ?, ?, ?, ?, ?, ?, ?]. Age 4in [?, ?]. [?, ?]. Agencies [?]. Agency [?, ?, ?, ?, ?, ?, ?, ?, ?, ?, ?]. -

Nomenclators Nomenclator Example Alberti's Cipher Disk
Nomenclators Early code/cipher combination, popular form 1400s-1800s. Philip of Spain (1589, see Kahn): LO = Spain POM = King of Spain 64 = confederation overlined two-digit groups = null + substitution cipher with homophones Nomenclator Example Nomenclator used by Mary, Queen of Scots . in 1586 in the plot against Elizabeth I Taken from Simon Singh. The Code Book. Alberti’s Cipher Disk Invented by Leon Battista Alberti in 1460s. outer disk (fixed) plaintext inner disk (moving) ciphertext Agree on index letter on inner disk. Key: letter corresponding to index letter on outer disk. Key can change during encryption 1 Cipher Disk Examples Let’s choose “K” as index letter. Examples: rRVTZOK aKVtTRCK HKmZMEP Since the key can change, this cipher is no longer monoalphabetic, but polyalphabetic. Are there other ways to use the cipher disk? Johannes Trithemius 1462-1516, Germany Polygraphiae, 1518 First printed book on cryptography. • Ave Maria Cipher • Polyalphabetic substitution • Progressive key Steganographia, 1606 • hidden writing http://diglib.hab.de/drucke/12-3-rhet-2f/start.htm Polygraphiae I The Polygraphiae contains many pages of code. 2 Polygraphiae II: Ave Maria 1st and 2nd page Steganographia http://books.google.com/books?id=bQdC AAAAcAAJ&dq=Trithemius%20Stegano graphia&pg=PR6#v=onepage&q&f=false Polygraphiae III Tabula recta, from the 6th book of the Polygraphiae. • Polyalphabetic substitution • Progressive key The history of information security: a comprehensive handbook, de Leeuw, Bergstra 3 Polygraphiae IV Examples (starting with first alphabet) • Johannes • SUGKESUOWSUN The history of information security: a comprehensive handbook, de Leeuw, Bergstra Modern Tabula Recta More Examples (not from beginning) • XNNN • NUGUV http://commons.wikimedia.org/wiki/File:Vigenere-square.png Giovan Batista Belaso La cifra del. -
Scamp Iv, Lecture V; History of the Invention And
REF ID:A38396 r I LECTURE V HISTORY OF THE INVENTION AND DEVELOHllENT OF CIPHER DEVICES AND MACHI.NF.$. Three or four years ago I was asked to give a lecture before the Communica- tions-Electronics Division of the Air University, USAF, on the subject of communications security (COMSEC). About that time there was 'hP r "o:s..ui.i.ered into our ears over the radio a slogan concerned wi+~ ~oile traffic safety rules • ..... ThE" o1iugta.n." was: "Don't learn your traffic laws by accident!" I thought the slogan useful. as the title of my talk but l modified it a little: "Don't learn your COMSEC laws by accident•" I began my talk by reading Webster's definition of the word accident. I know, of course, that this group here today is not concerned particularly with COMSEC duties of any sort. But the definition of the word accident will nevertheless be of interest 11l connection with what will be said in a moment or two, so I'll read Webster's definition if you'll bear with me. Webster: "Acc:ulent" - literally, a be:talling. ~ '\ a. An event that takes place without one's foresight or expectation, ) '\;r an undesigned, sudden, and unexpected event. @'pp roved for Release by NSA on 10-10-2013 pursuantto E .0. 1352a REF ID:A38396 b Hence, often, an undesigned and unforeseen occurrence of an afflictive or unfortunate character, a llll.Shap resulting in injury to a person or damage to a thing, a casualty, as to die by an accident Having defined the word, I'll now proceed by relating an interesting, minor, but nevertheless quite important episode of the war in the Pacific Theatre during WWII, and I will introduce the acrount of that episode by saying that: During the W'lr, the President of the United States, Chief of' Sta.ff of the Ar1ff3' 1 the Commander-in-Chief' of the U.S. -

Ciphers: Making and Breaking Ralph Morelli Trinity College, Hartford ([email protected])
Ciphers: Making and Breaking Ralph Morelli Trinity College, Hartford ([email protected]) Smithsonian Institute October 31, 2009 © 2009 Ralph Morelli You are free to reuse and remix this presentation under a creative commons license provided you give credit to the author. http://creativecommons.org/licenses/by/3.0/us/ This presentation was created using Open Office 3.0, free and open source software. http://www.openoffice.org/ Part II: Cryptology in Transition Outline Polyalphabetic Substitution Alberti Cipher Vigenère Cipher – Le Chiffre Indéchiffrable Kasiski Decipherment Mechanical Ciphers The Enigma Machine WWII Leon Battista Alberti (1404-1472) Leon Battista Alberti (1404-1472) Renaissance man. Architect, author, artist, poet, philosopher. Father of Modern Cryptography – First western exposition of frequency analysis. – Invention of polyalphabetic cipher. Courtyard of the Uffizi Palace Alberti the Architect Santa Maria Novella – Florence De Cifris First comprehensive account of cryptanalysis in the West. Invention of the polyalphabetic cipher. Alberti Cipher Disk Outer disk stationary with regular alphabet. Inner disk moveable with permuted alphabet. An inner disk letter (k) is picked as index, and aligned with some letter on outer disk (B). The index is changed every 3 or 4 words and inserted into the message. “Ciao amici” might be encrypted as “BlvgyCeztkt”. Compare Letter Frequencies Plain Caesar Simple Polyalphabetic Polyalphabetic Development Alberti (~ 1472): devised genuine polyalphabetic cipher with mixed alphabet plus a practical cipher disk device. Abbot Trithemius (~ 1508): used tables of regular alphabets to be used in fixed order. Giovanni Battista Belaso (~ 1550 ): invented principle of a key or keyword to select alphabets. Giovanni Battista Porta (~ 1563): “invented” using mixed alphabets. -

Disk Cipher Activity
JUNIOR HISTORIANS Disk Cipher What is Cryptography? Cryptography is the art of writing and solving codes. It has been used for thousands of years to keep messages secret. During the Civil War, both sides sent important information about battles, supplies, and troop movements. Just as important was keeping that information a secret from the enemy. In order to hide important messages, soldiers relied on secret codes or ciphers. A cipher uses a letter, number, or symbol to replace an individual letter, combo of letters, or numbers. By using a code they agreed on, members of the same army could share important information without worrying about their enemy decoding the secret message. Today, computers use a form of cryptography called encryption to protect your valuable personal information in our digital world. The Coded Message UN MCRZYYN UHXZIOL CHWBY MNUFF UVLUB UGFCH WIFHQ UMUHX MNCFF CMNBY NUFFY MNJLY MCXYH NNIBU PYMYL PYX Crack The Code Using the Cipher Disk provided above, translate the coded message by locating the letter in the encrypted message on the outer wheel and decoding it below with the corresponding letter on the inner wheel. Once each letter has been changed, piece together the words to find the solution. Spaces are provided for each letter to help you solve the puzzle. Hint: If you’re having trouble reading the disk, write the alphabet normally from A to Z. Follow the alphabet on the outer wheel of the disk, writing the letters on the inner wheel beneath each one. Then use this to solve the message. A___ ___ ___ ___ - ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___, ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___, ___ ___ ___ ___ ___ ___ ___ ___ ___ ___, ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___ ___. -

Codes and Ciphers (Cryptology)
REF ID:A4148558 from I;ncyclopaedia Britannica Copyright 1956 CODES ANU Cl.diERS (CRYPTOLOGY), general terms for ·the.protection of written communications, or signals rep- designating the methods or the paraphernalia employed in secret resenting. them;. can also be used in protecting. or disguising other communications or involved in the science of ceyptology -(from types of. cryptosignalling; e.g., ciphony and cifax. Cryptography Gr." kryptos, "hidden," and logos, "word"); Because of the groWth deals . with. the processes, methods or means involved m of governments, the expansion of commerce ·and· especially the preparing cryptograms, that is, messages or writings which are remarkable progress made in . communications-electronics tech• intended to. be incomprehensible except to those who legitimately nology, cryptology has come to play a very important role i11 possess the ,proper special paraphernalia and the keys for those governmental communications, especially diplon:iatic and military; cryptograms and know how to use them in order to reproduce the It also plays a minor role in comm.ercial, industrial and banking original plain text of the messages. These processes are usualiy communications. Among the wore uncommon uses of ·cryptology . accomplished by means of cryptosystems employing codes ·or: are those in connection with ·attempts to establish authorsh,ip .in ciphers. The process of converting a plain-text message into a cases where that has been broµght into question, as, for example, cryptogram is called enciphering (or encoding); that of recon-· that. of the· Shakespeare :plays. verting the cryptogram back into its intelligible form, when done ln its early stages cryptology was concerned:almost exclusively by a legitimate or authorized communicator, i:e., one who legiti-· with secrecy in written communicatio.ns ,and this arti.cle wil~ be mately hol.ds the paraphernalia and the key, is called deciphering -restricted very largely thereto, but the science has developed (or decoding). -

Docid: 2757002
DOCID: 2757002 TOP SEGAET UPo18AA Regierungs-Oberinspektor Fritz Menzer: Cryptographic Inventor Extraordinaire DAVID P MOWRY This anic.:le is classified TOP SECRET CODEWORD in its entirety because the sources from which if W(;IS derived are all so classified. It weighed one and rhree-quarter pounds and was ~pring-drfren. According to German authorities. ir was at leasr as secure as rhe Enigma. The Germans intended to have 1,000 available by Ocrober 1945 and to mass-produce I 0, 000 per month by January 1946. The Schfusselkaste11, or Cipher Box, would have replaced the Enigma below the level of division. If ii had been introduced in 1942, while the German star was in the ascendant, it could have changed the course of the war. Nineteen forty-five was, of course, too late. In 1942. the resulting loss of intelligence to the Allies would have afJeered rhe outcome of the North African campaign and the Baale of the Atlantic, as well as subsequent campaigns. The inventor of the Schfusse/kasten, and other cipher devices, was Regierungs-Oberinspektor Fritz Menzer, of OKW/ Chi, the Cr}ptologic Section of the German Army High Command. 1 THE CAREER OF OBERINSPEKTOR MENZER Os twin Fritz Menzer was born 6 April 1908 in rhe village of Herrndorf in Saxony, the youngest of four children of a small businessman. After completing elementary school and an apprenticeship as a toolmaker, he enlisted in the Reichswehr in 1926 as a mechanic and was assigned to a motor battalion in Leipzig. 2 Menzer had already developed an interest in cryptography and was granted his first patent in 1934, for a "combined measuring apparatus for angles and lengths, the data [from which was] expressed in an enciphered form in a four-place combination of letters." Based on his work on this device, he was permitted to attend a course for radio technicians at the Army Signal School.